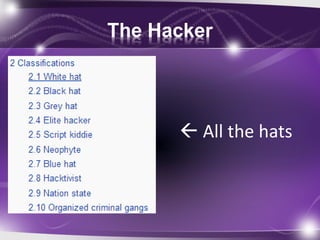
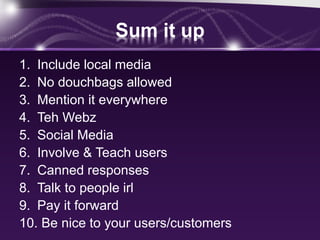
This document summarizes Amanda Berlin's talk on hackers and the information security community in 5 parts. It discusses that while there are "black hat" and "grey hat" hackers, there are also positive aspects like "white hat" hackers who work to improve security, conferences that raise money for charity, and communities that help with substance abuse and mentoring. It provides 10 steps anyone can take to help improve public perception of hackers and information security, such as using social media to spread awareness, being respectful to others, and educating the public on basic computer security practices. The document encourages involvement in local media and computer user groups to differentiate ethical from unethical hacking activities and help more users protect themselves.