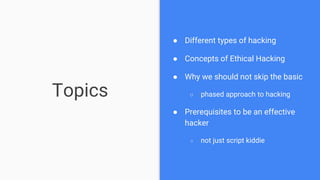
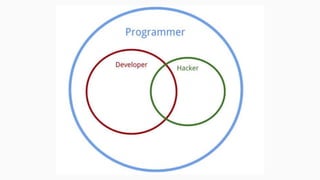
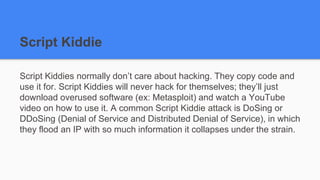
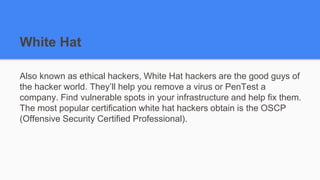
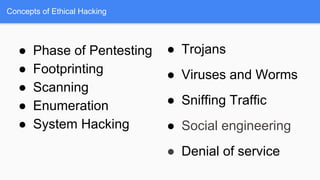
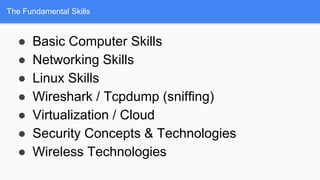
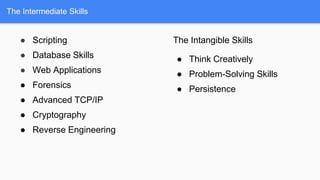
The document provides an introductory overview of offensive security, targeting beginners interested in ethical hacking. It covers different hacking types, the phases of penetration testing, and the prerequisites needed to be an effective hacker. Key concepts include reconnaissance, scanning, gaining access, and maintaining access, while emphasizing the importance of documentation for success in hacking endeavors.