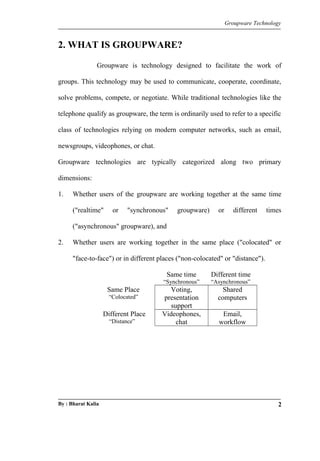
Groupware technology facilitates group work through applications that enable communication, collaboration, and coordination among users, often utilizing modern computer networks. It includes both asynchronous applications like email and workflow systems, as well as synchronous solutions like shared whiteboards and chat systems. The advantages of groupware include improved communication, enhanced problem-solving, and reduced costs, making it increasingly popular in organizations.