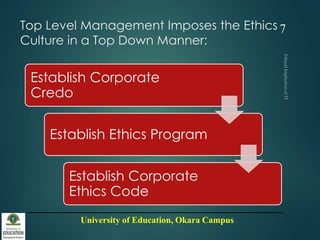
This document discusses the ethical implications of information technology. It begins by stating that firms have an obligation to establish an ethical culture through a corporate credo and ethics programs. It also notes that computer ethics are important because society has perceptions and fears related to computer use. The document then defines the differences between morals, ethics, and laws. It discusses reasons for computer ethics, including the logical malleability of computers, their ability to transform processes, and the invisibility of their internal operations. The document also outlines four basic social rights related to information: privacy, accuracy, property, and accessibility. It concludes by discussing how companies can establish ethics in IT through codes of ethics and educational programs.