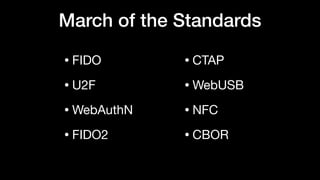
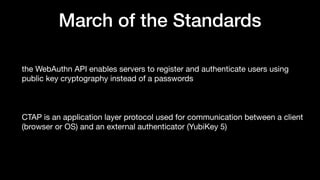
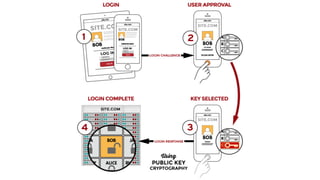
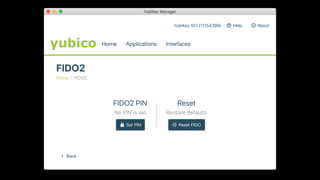
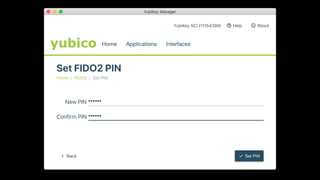
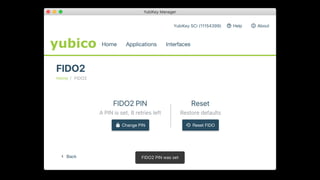
- FIDO2 is a passwordless authentication standard that uses public key cryptography instead of passwords
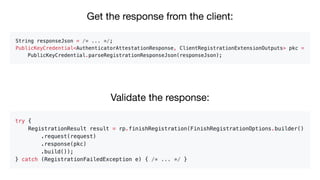
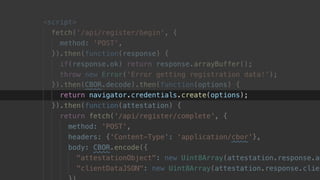
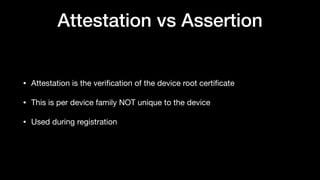
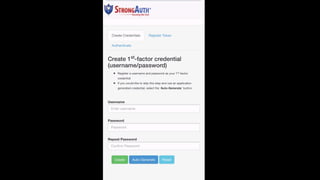
- It involves an initial registration process where a public/private key pair is created and the public key is associated with the user's account
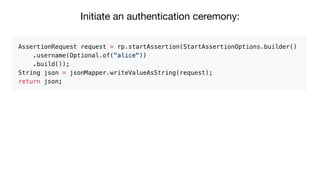
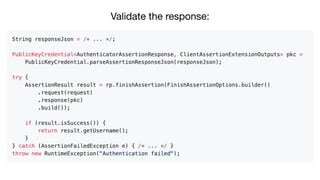
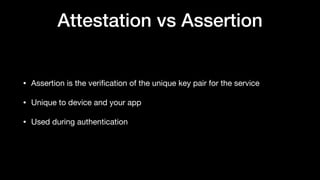
- Authentication then involves validating the signature from the private key without exposing any secrets
- FIDO2 supports various form factors beyond USB keys like mobile devices and provides stronger security than passwords