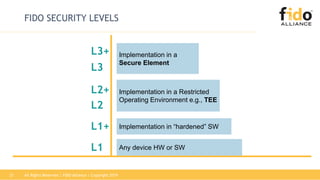
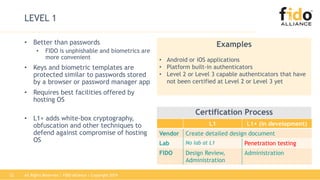
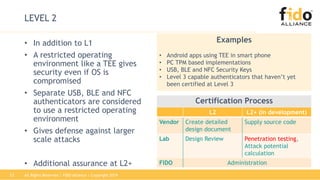
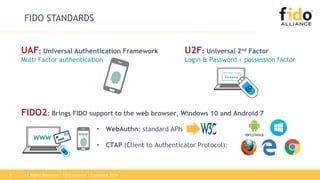
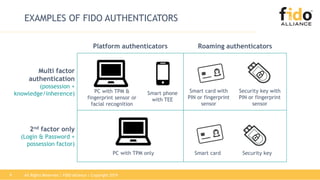
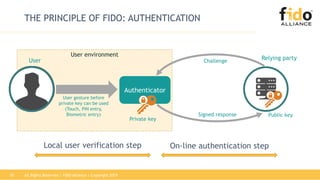
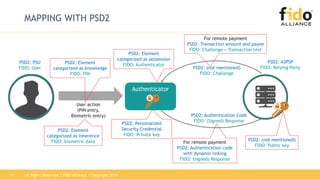
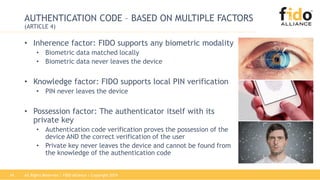
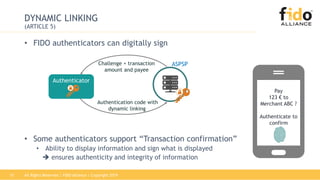
The document discusses the FIDO Alliance's role in achieving strong customer authentication compliance, highlighting its authentication standards and certification program. It outlines how FIDO aligns with RTS requirements under PSD2, emphasizing the importance of security measures, user verification, and the protection of sensitive data. Additionally, it covers FIDO security levels and the necessity of independent testing and evaluation for compliance assurance.









![All Rights Reserved | FIDO Alliance | Copyright 201918
EVALUATION: WHAT THE REGULATOR SAYS
[RTS] RECITAL 2, ARTICLE 3.1
The security measures for the application of strong customer
authentication, the measures to protect confidentiality and integrity of
the personalised security credentials must be:
• Documented
• Periodically tested, evaluated and audited by auditors
• Auditors must have expertise in IT security and payments and be
operationally independent](https://image.slidesharecdn.com/webinar-fido-psd2compliance-final-190409175414/85/FIDO-PSD2-Achieving-Strong-Customer-Authentication-Compliance-18-320.jpg)