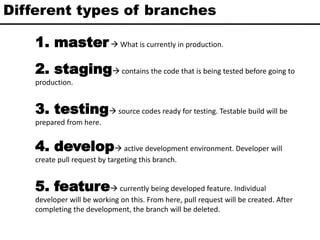
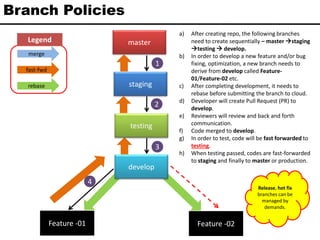
The document outlines the process of git branching and code review including different types of branches such as master, staging, developing, feature, and testing. It describes branch policies for creating and merging branches as well as a structured system for code review comments using specific prefixes like 'imo', 'must', 'nit', and 'q'. The overall process ensures code quality through collaboration and testing before deployment to production.
![Code review comment & prefix
1. IMO In my opinion . If reviewer has a different opinion on a statement,
he/she will put this prefix. Like-
• [IMO] This statement will never be executed.
2. MUST Must have to change the statement to maintain code quality
according to defined code convention.
• [MUST] Access modifier of the variable is private.
• [MUST] Variable name start with underscore(_).
3. NIT Nit pick. That is, a small change that may not be very important,
but is technically correct. Can be treated as a suggestion.
• [NIT] Rather than long data type, integer type will satisfy the
requirement.
4. Q If there is any question on an statement, user can put this Q
comment.
• Like- [Q] Why the function is returning null even though return type
is string?](https://image.slidesharecdn.com/gitbranchingandreviewpolicies-210416175901/85/Git-branching-policy-and-review-comment-s-prefix-5-320.jpg)
