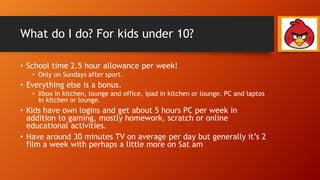
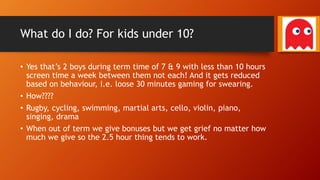
The document discusses the complexities of video gaming, including its history, market dominance, interfaces, and the psychological and social hooks that can lead to addiction. It addresses the benefits of gaming, such as improving social skills and cognitive abilities, while also highlighting the need for a balanced approach and safe play strategies, especially for children. The author, a gaming enthusiast and chairman of a local IT institute, shares personal insights on managing gaming habits in both children and adult gamers.