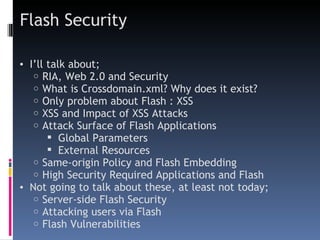
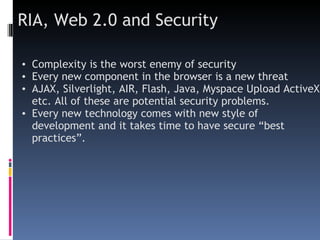
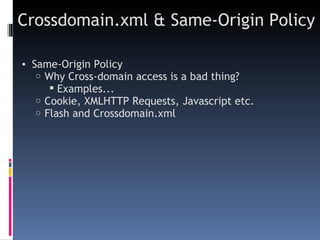
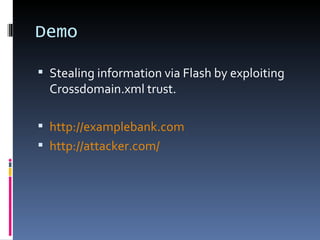
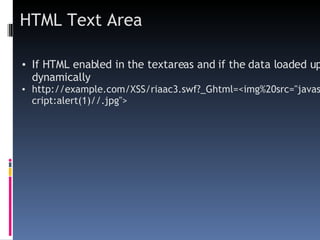
This document discusses security issues related to Flash applications and cross-domain access. It covers how the crossdomain.xml file controls cross-domain access and demonstrates how this can be exploited. Attack surfaces like global parameters, external resources, and HTML text areas are described. The document recommends limiting JavaScript access in embedded Flash, ensuring configurations and external resources come from trusted domains, and sanitizing data in HTML text areas.