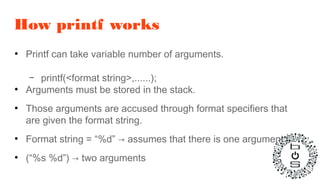
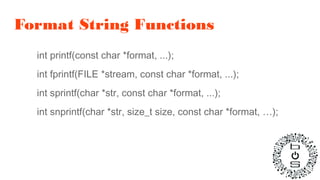
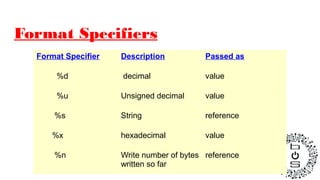
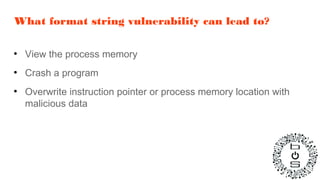
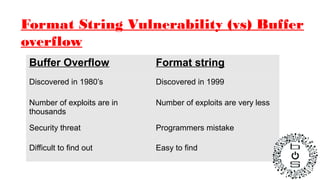
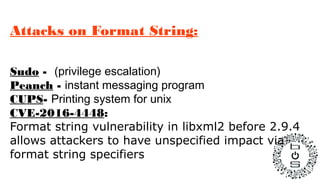
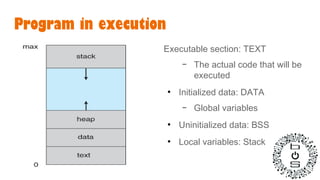
The document discusses format string vulnerabilities, which occur when user-supplied input containing format specifiers is used without validation in functions like printf(). Format strings allow viewing process memory, crashing programs, or overwriting memory locations like the instruction pointer. While buffer overflows have thousands of exploits, format string vulnerabilities are less common but easier to find due to programmer mistakes. Exploiting format strings can lead to privilege escalation, crashes, or arbitrary code execution. Examples of past vulnerabilities are discussed.
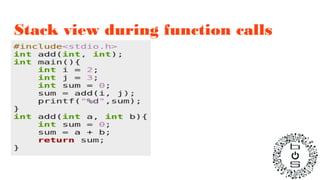
![Stack
…....
10. push j
11. push i
12. call add
13. add esp, 0x8
……
20. add:
21. mov eax, [esp+0x4]
22. mov ebx, [esp+0x8]
23. add eax, ebx
24. ret
Stack
0XDEADCAFE
Higher address
Lower address](https://image.slidesharecdn.com/formatstringvunerability-161122173200/85/Format-string-vunerability-7-320.jpg)