Recommended
PDF
PDF
Pythonの理解を試みる 〜バイトコードインタプリタを作成する〜
PDF
SQLアンチパターン - 開発者を待ち受ける25の落とし穴
PDF
PPTX
PDF
PDF
PDF
PDF
PDF
Elasticsearch勉強会#44 20210624
PDF
PDF
PPTX
Swin Transformer (ICCV'21 Best Paper) を完璧に理解する資料
PDF
PDF
PDF
Dockerfile を書くためのベストプラクティス解説編
PDF
【DL輪読会】"Masked Siamese Networks for Label-Efficient Learning"
PPTX
PDF
[DL輪読会]data2vec: A General Framework for Self-supervised Learning in Speech,...
PDF
PWNの超入門 大和セキュリティ神戸 2018-03-25
PDF
High performance python computing for data science
PDF
PPTX
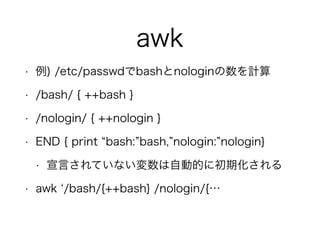
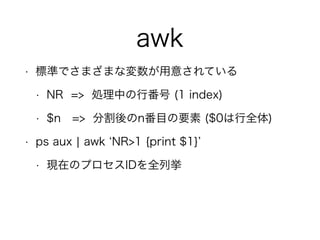
Effective Modern C++ 勉強会 Item 22
PDF
PDF
ChatGPT 人間のフィードバックから強化学習した対話AI
PDF
PDF
PPTX
GraphQLのsubscriptionで出来ること
PDF
Summary of "Hacking", 0x351-0x354
ODP
More Related Content
PDF
PDF
Pythonの理解を試みる 〜バイトコードインタプリタを作成する〜
PDF
SQLアンチパターン - 開発者を待ち受ける25の落とし穴
PDF
PPTX
PDF
PDF
PDF
What's hot
PDF
PDF
Elasticsearch勉強会#44 20210624
PDF
PDF
PPTX
Swin Transformer (ICCV'21 Best Paper) を完璧に理解する資料
PDF
PDF
PDF
Dockerfile を書くためのベストプラクティス解説編
PDF
【DL輪読会】"Masked Siamese Networks for Label-Efficient Learning"
PPTX
PDF
[DL輪読会]data2vec: A General Framework for Self-supervised Learning in Speech,...
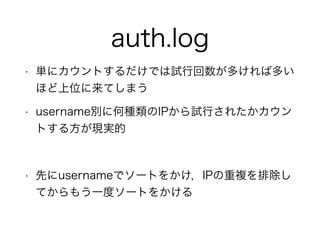
PDF
PWNの超入門 大和セキュリティ神戸 2018-03-25
PDF
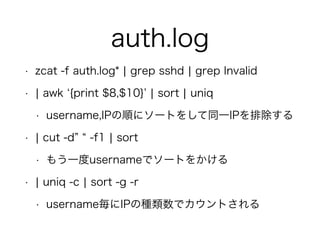
High performance python computing for data science
PDF
PPTX
Effective Modern C++ 勉強会 Item 22
PDF
PDF
ChatGPT 人間のフィードバックから強化学習した対話AI
PDF
PDF
PPTX
GraphQLのsubscriptionで出来ること
Viewers also liked
PDF
Summary of "Hacking", 0x351-0x354
ODP
PDF
PDF
PPT
PDF
固定長レコード形式行順ファイルでもAwkがしたい!
PDF
PPTX
PPTX
ODP
Format string vunerability
PDF
PDF
ODP
Scalability, Fidelity and Stealth in the DRAKVUF Dynamic Malware Analysis System
PDF
20130824 第六回チャンピオンシップシェル芸ランナー勉強会 in LLまつり
PDF
Similar to シェル芸初心者によるシェル芸入門 (修正版)
PDF
PDF
PDF
PDF
「はじめよう、シェル芸」オープンキャンプin南島原2020/OpenCamp in Minami-shimabara online
PDF
PDF
20160618 第23回シェル芸勉強会LT コマンドプロンプト芸
PDF
PPTX
PDF
PDF
スクリプト言語入門 - シェル芸のすすめ - 第2回クラウド勉強会
PDF
ODP
PDF
NGS速習コース:UNIXの基礎の理解/Linux導入
PPTX
シェルスクリプトワークショップ資料 - 初心者向け「シェル芸」
PPTX
シェルスクリプトワークショップ資料 - 上級者向け「シェル芸」
PDF
20130223 OSC Tokyo/Spring
PPTX
PDF
jus & USP友の会共催 シェルワンライナー勉強会@関西(第11回シェル芸勉強会)
PDF
PDF
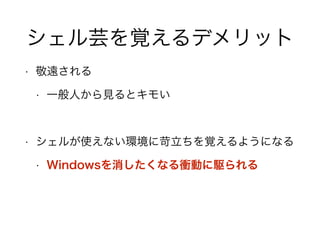
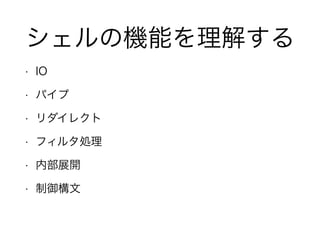
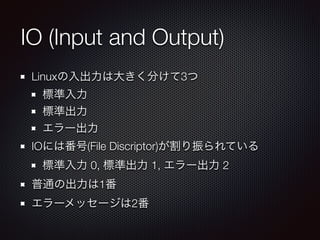
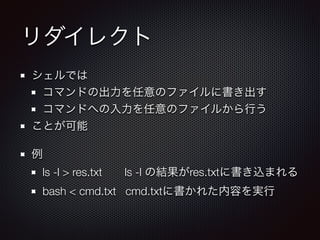
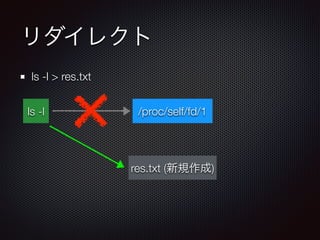
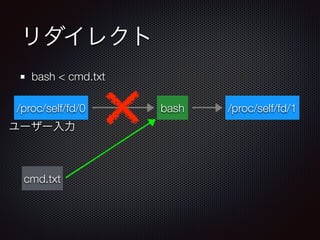
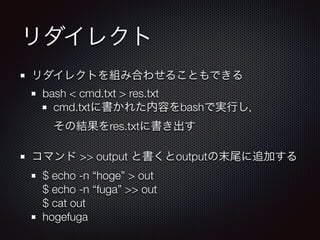
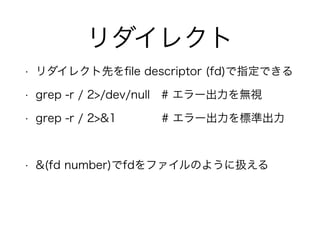
シェル芸初心者によるシェル芸入門 (修正版) 1. 2. 3. 4. 5. 6. 7. 8. 9. IO (Input and Output)
Linuxの入出力は大きく分けて3つ
標準入力
標準出力
エラー出力
IOには番号(File Discriptor)が割り振られている
標準入力 0, 標準出力 1, エラー出力 2
普通の出力は1番
エラーメッセージは2番
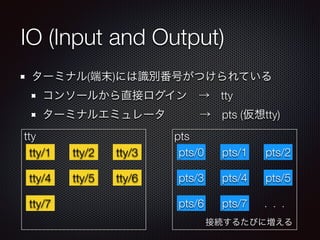
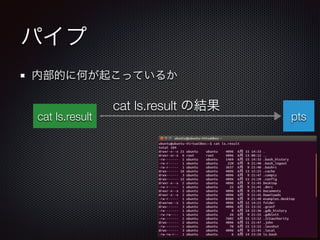
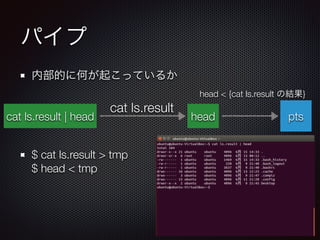
10. IO (Input and Output)
ターミナル(端末)には識別番号がつけられている
コンソールから直接ログイン → tty
ターミナルエミュレータ → pts (仮想tty)
tty pts
tty/1 tty/2 tty/3
tty/4 tty/5 tty/6
tty/7
pts/0 pts/1 pts/2
pts/3 pts/4 pts/5
pts/6 pts/7
接続するたびに増える
...
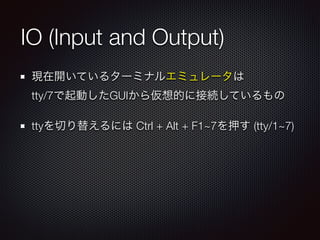
11. IO (Input and Output)
現在開いているターミナルエミュレータは
tty/7で起動したGUIから仮想的に接続しているもの
ttyを切り替えるには Ctrl + Alt + F1~7を押す (tty/1~7)
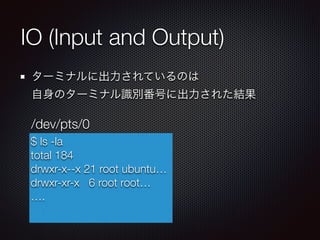
12. IO (Input and Output)
ターミナルに出力されているのは
自身のターミナル識別番号に出力された結果
$ ls -la
total 184
drwxr-x--x 21 root ubuntu…
drwxr-xr-x 6 root root…
….
/dev/pts/0
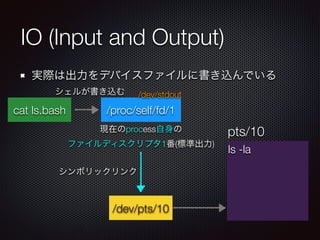
13. IO (Input and Output)
実際は出力をデバイスファイルに書き込んでいる
cat ls.bash
/dev/pts/10
/proc/self/fd/1
現在のprocess自身の
ファイルディスクリプタ1番(標準出力)
シンボリックリンク
ls -la
pts/10
シェルが書き込む /dev/stdout
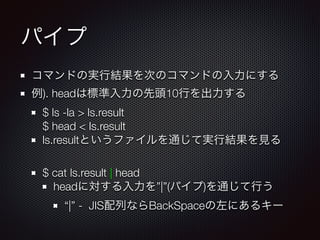
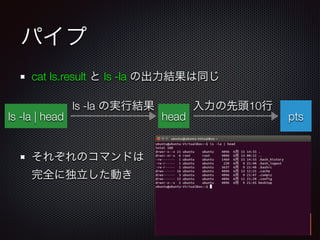
14. 15. 16. 17. 18. 19. 20. 21. 22. パイプ
cat ls.result と ls -la の出力結果は同じ
!
!
それぞれのコマンドは
完全に独立した動き
ptsls -la | head head
ls -la の実行結果 入力の先頭10行
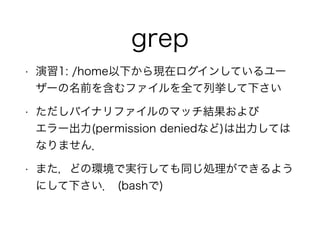
23. 24. 25. 26. grep
• grep expr [input]
• exprにマッチする行を出力する
• grep -v expr [input]
• exprにマッチしない行を出力する
• grep -r expr /some/path
• /some/path配下からexprにマッチするファイル
およびその箇所を出力する
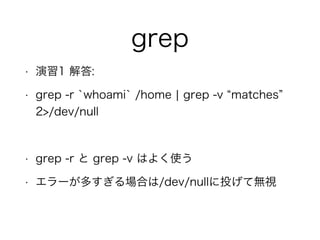
27. 28. grep
• 演習1 解答:
• grep -r `whoami` /home ¦ grep -v matches
2>/dev/null
!
• grep -r と grep -v はよく使う
• エラーが多すぎる場合は/dev/nullに投げて無視
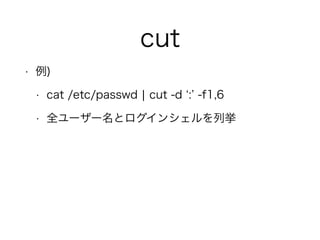
29. cut
• cut -d <delim> -f num [input]
• <delim>を区切り文字として,num番目の列を
出力する
• numには 1,3-5 (1と3-5行目)のように範囲を指
定できる
30. 31. sed
• sed expr [input]
• 入力を行ごとにexprに従って処理する
• expr
• s/[pat1]/[pat2]/g # pat1をpat2に置換する
• patに / が含まれる場合はエスケープが必要
• 区切り文字は別のものでも良い (@,#,%など)
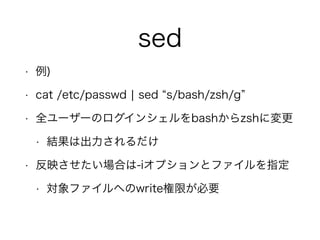
32. sed
• 例)
• cat /etc/passwd ¦ sed s/bash/zsh/g
• 全ユーザーのログインシェルをbashからzshに変更
• 結果は出力されるだけ
• 反映させたい場合は-iオプションとファイルを指定
• 対象ファイルへのwrite権限が必要
33. awk
• awk expr [input]
• テキスト処理のために作られたスクリプト言語
• 行単位で処理を行う
• デフォルトで空白をいい感じに扱ってくれる
• 空白とタブが混じっていても大丈夫
• cutで崩れるような場合に便利
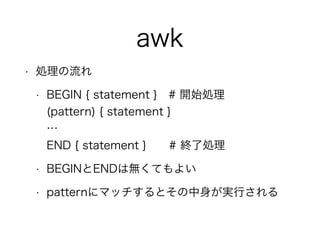
34. awk
• 処理の流れ
• BEGIN { statement } # 開始処理
(pattern) { statement }
…
END { statement } # 終了処理
• BEGINとENDは無くてもよい
• patternにマッチするとその中身が実行される
35. 36. 37. sort
• sort [input]
• 入力をソートする (ソートキーを変更可能)
• -t <delim> # 区切り文字をdelimにする
• -k <key1> # key1から行末をソートキーにする
• -b # 行頭のスペースを無視
• -r # 降順
• -i # ignore case
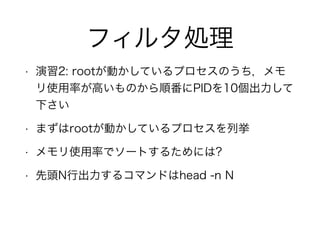
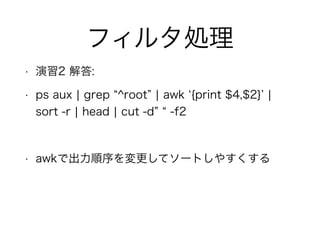
38. 39. 40. フィルタ処理
• 演習2 解答:
• ps aux ¦ grep ^root ¦ awk {print $4,$2} ¦
sort -r ¦ head ¦ cut -d -f2
!
• awkで出力順序を変更してソートしやすくする
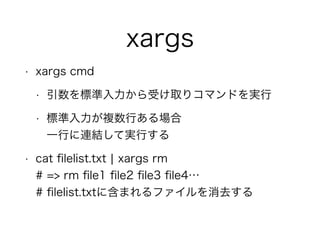
41. xargs
• xargs cmd
• 引数を標準入力から受け取りコマンドを実行
• 標準入力が複数行ある場合
一行に連結して実行する
• cat filelist.txt ¦ xargs rm
# => rm file1 file2 file3 file4…
# filelist.txtに含まれるファイルを消去する
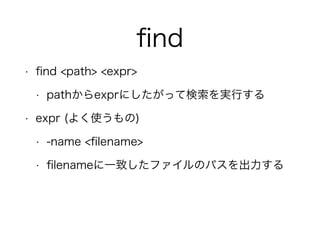
42. find
• find <path> <expr>
• pathからexprにしたがって検索を実行する
• expr (よく使うもの)
• -name <filename>
• filenameに一致したファイルのパスを出力する
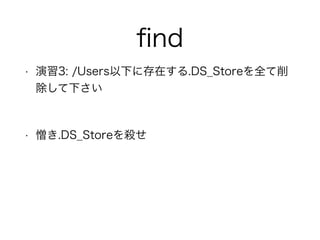
43. 44. find
• 演習3 解答:
• find /Users -name .DS_Store ¦ xargs rm -f
!
• find /Users -name .DS_Store
• /Users以下に含まれる.DS_Storeを検索
• xargs rm -f
• rm -f [.DS_Store1] [.DS_Store2]…
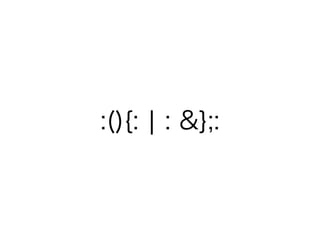
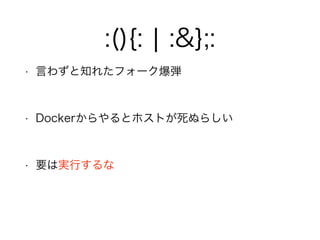
45. 46. 47. 48. 49. :(){: ¦ :&};:
• :()
• : という関数を定義
• {: ¦ :&}; :
• :を:にパイプで繋ぐのをバックグラウンドで実行
!
• 無限にプロセスが増殖する
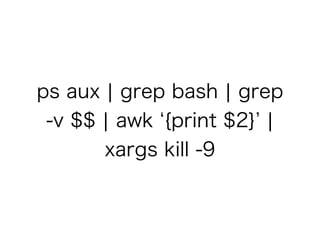
50. 51. ps aux ¦ grep bash ¦ grep
-v $$ ¦ awk {print $2} ¦
xargs kill -9
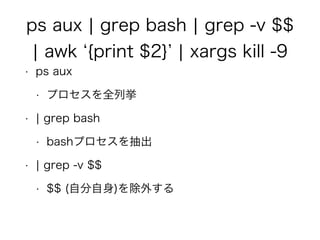
52. ps aux ¦ grep bash ¦ grep -v $$
¦ awk {print $2} ¦ xargs kill -9
• ps aux
• プロセスを全列挙
• ¦ grep bash
• bashプロセスを抽出
• ¦ grep -v $$
• $$ (自分自身)を除外する
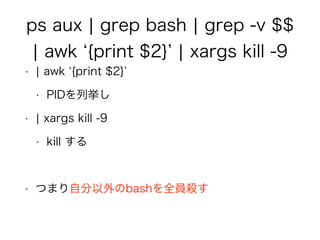
53. ps aux ¦ grep bash ¦ grep -v $$
¦ awk {print $2} ¦ xargs kill -9
• ¦ awk {print $2}
• PIDを列挙し
• ¦ xargs kill -9
• kill する
!
• つまり自分以外のbashを全員殺す
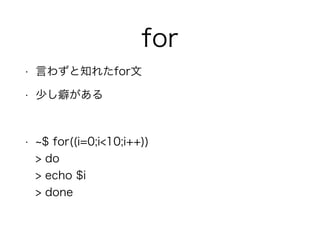
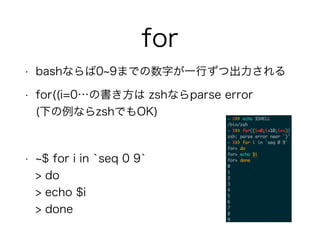
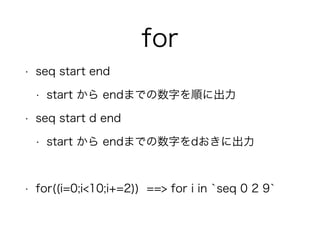
54. 55. 56. 57. 58. 59. for
• seq start end
• start から endまでの数字を順に出力
• seq start d end
• start から endまでの数字をdおきに出力
!
• for((i=0;i<10;i+=2)) ==> for i in `seq 0 2 9`
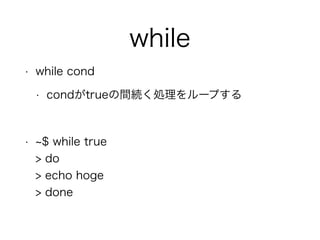
60. 61. while
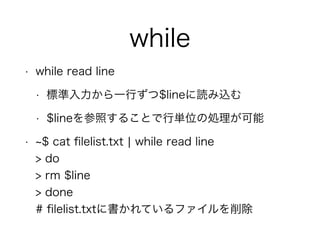
• while read line
• 標準入力から一行ずつ$lineに読み込む
• $lineを参照することで行単位の処理が可能
• $ cat filelist.txt ¦ while read line
> do
> rm $line
> done
# filelist.txtに書かれているファイルを削除
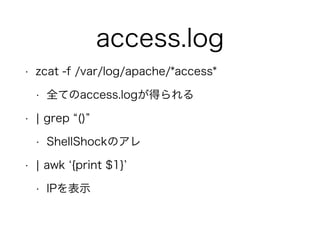
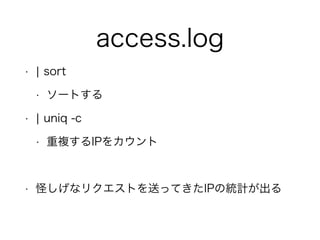
62. 63. 64. 65. 66. 67. 68. 69. access.log
• zcat -f /var/log/apache/*access*
• 全てのaccess.logが得られる
• ¦ grep ()
• ShellShockのアレ
• ¦ awk {print $1}
• IPを表示
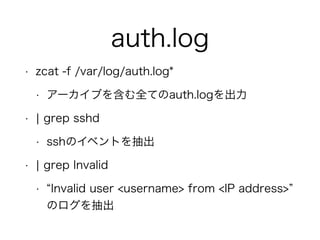
70. 71. 72. auth.log
• zcat -f /var/log/auth.log*
• アーカイブを含む全てのauth.logを出力
• ¦ grep sshd
• sshのイベントを抽出
• ¦ grep Invalid
• Invalid user <username> from <IP address>
のログを抽出
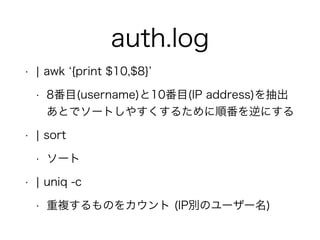
73. auth.log
• ¦ awk {print $10,$8}
• 8番目(username)と10番目(IP address)を抽出
あとでソートしやすくするために順番を逆にする
• ¦ sort
• ソート
• ¦ uniq -c
• 重複するものをカウント (IP別のユーザー名)
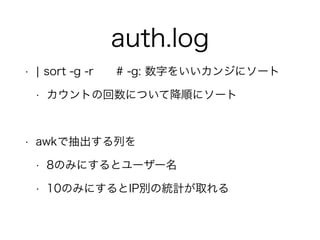
74. auth.log
• ¦ sort -g -r # -g: 数字をいいカンジにソート
• カウントの回数について降順にソート
!
• awkで抽出する列を
• 8のみにするとユーザー名
• 10のみにするとIP別の統計が取れる
75. 76. 77. 78. auth.log
• zcat -f auth.log* ¦ grep sshd ¦ grep Invalid
• ¦ awk {print $8,$10} ¦ sort ¦ uniq
• username,IPの順にソートをして同一IPを排除する
• ¦ cut -d -f1 ¦ sort
• もう一度usernameでソートをかける
• ¦ uniq -c ¦ sort -g -r
• username毎にIPの種類数でカウントされる
79. 80.

![フィルタ処理
• 引数に与えられたファイルまたは
標準入力に対して特定のテキスト処理を行う
• grep, cut, sed, awk, sort, uniq
!
• 以降では,cmd [input] と表記した場合
[input]にはファイル名が入るが,省略した場合は
標準入力を使用する](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-25-320.jpg)
![grep
• grep expr [input]
• exprにマッチする行を出力する
• grep -v expr [input]
• exprにマッチしない行を出力する
• grep -r expr /some/path
• /some/path配下からexprにマッチするファイル
およびその箇所を出力する](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-26-320.jpg)
![cut
• cut -d <delim> -f num [input]
• <delim>を区切り文字として,num番目の列を
出力する
• numには 1,3-5 (1と3-5行目)のように範囲を指
定できる](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-29-320.jpg)
![sed
• sed expr [input]
• 入力を行ごとにexprに従って処理する
• expr
• s/[pat1]/[pat2]/g # pat1をpat2に置換する
• patに / が含まれる場合はエスケープが必要
• 区切り文字は別のものでも良い (@,#,%など)](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-31-320.jpg)
![awk
• awk expr [input]
• テキスト処理のために作られたスクリプト言語
• 行単位で処理を行う
• デフォルトで空白をいい感じに扱ってくれる
• 空白とタブが混じっていても大丈夫
• cutで崩れるような場合に便利](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-33-320.jpg)
![sort
• sort [input]
• 入力をソートする (ソートキーを変更可能)
• -t <delim> # 区切り文字をdelimにする
• -k <key1> # key1から行末をソートキーにする
• -b # 行頭のスペースを無視
• -r # 降順
• -i # ignore case](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-37-320.jpg)
![uniq
• uniq [input]
• 重複する行を消して出力
• -c # 消した行数をカウントする
!
• sort と組み合わせて使うことが多い](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-38-320.jpg)
![find
• 演習3 解答:
• find /Users -name .DS_Store ¦ xargs rm -f
!
• find /Users -name .DS_Store
• /Users以下に含まれる.DS_Storeを検索
• xargs rm -f
• rm -f [.DS_Store1] [.DS_Store2]…](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-44-320.jpg)


![access.log
• gzipで圧縮されているものを読むには
• gunzip -c [files]
• zcat [files]
• zcatの方がタイプ数が少なくコマンド名が直感的
(個人の主観)](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-66-320.jpg)
![access.log
• gzipで圧縮されているものを読むには
• gunzip -c [files]
• zcat [files]
• zcatの方がタイプ数が少なくコマンド名が直感的
(個人の主観)](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-67-320.jpg)
![auth.log
• ログインなど資格情報の使用記録
• /var/log/auth.log
• アーカイブはauth.log.<number>[.gz] の形
!
• 不正ログインしようとしたIPとそのユーザー名につ
いて調べてみる](https://image.slidesharecdn.com/rnccshell-150903123759-lva1-app6892/85/slide-71-320.jpg)