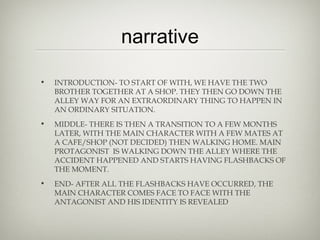
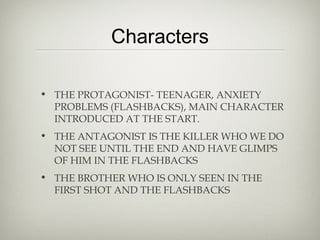
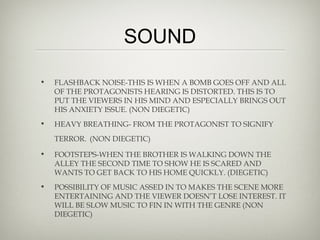
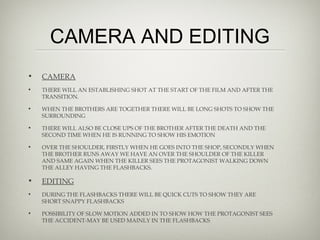
The document provides an initial narrative and production plan for a thriller short film. It outlines that the film will follow a teenage protagonist who begins having flashbacks down an alleyway where his brother was killed a few months prior. The narrative will be set up through establishing shots of the brothers at a shop and cafe, and conclude with the protagonist confronting his brother's killer in the alleyway. The document discusses incorporating common thriller conventions like low key lighting in the alleyway, narrative enigmas around the brother's death and killer's identity, and depicting the protagonist's anxiety through flashbacks. It provides details on the characters, locations, props, sound design, camera shots, and editing techniques planned to develop the thriller genre and narrative.