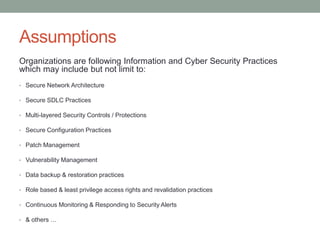
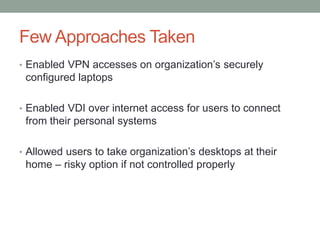
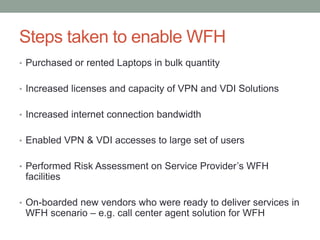
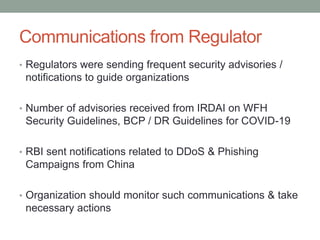
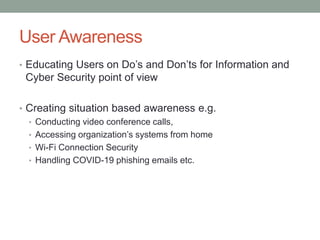
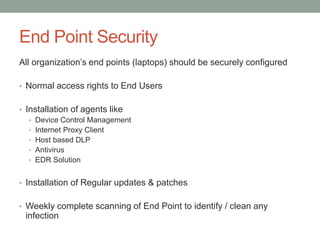
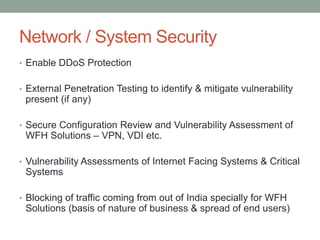
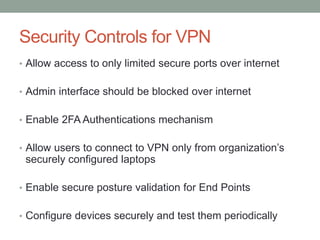
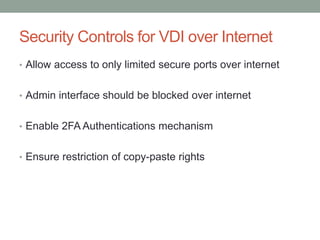
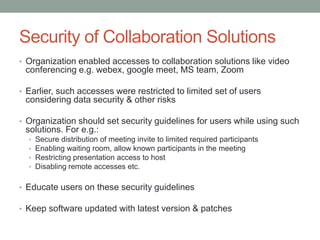
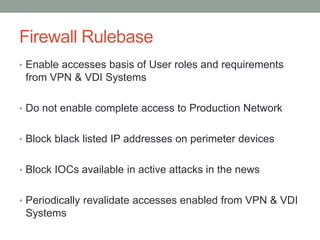
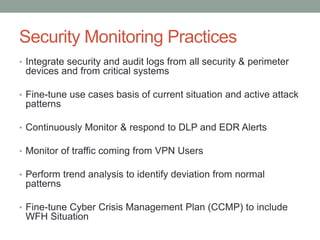
This document summarizes a webinar presentation about IT security practices during the COVID-19 pandemic. The presentation discusses how organizations transitioned to work from home, the security challenges they faced, and best practices for securing remote access and collaboration tools. It provides an overview of steps taken such as enabling VPN and VDI access, educating users, implementing endpoint security controls, and adjusting security monitoring practices for the new normal of remote work.