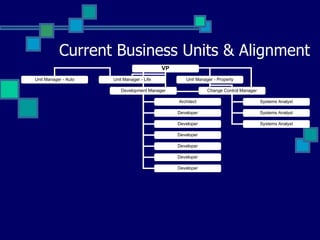
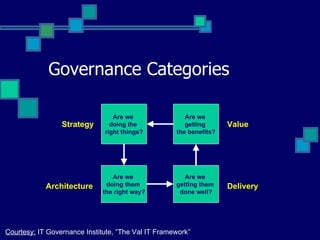
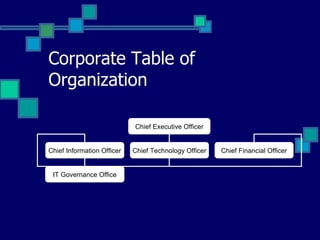
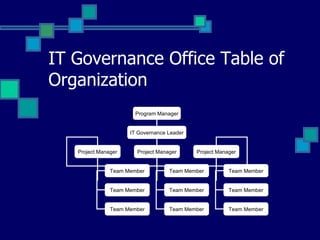
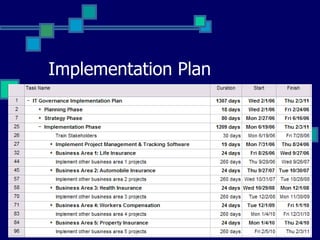
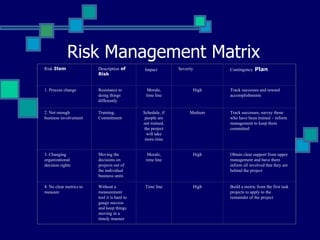
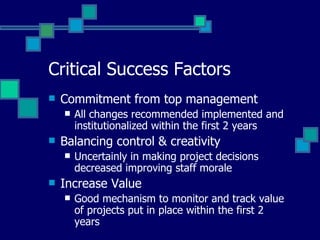
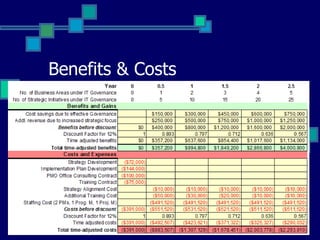
The document outlines an implementation model for effective IT governance at Kig Insurance Company, addressing significant challenges such as low project success rates and lack of alignment between business units and IT. It defines goals, a technical plan, and a management plan aimed at enhancing IT decision rights, aligning IT projects with business strategy, and measuring the success of these projects using clearly defined metrics. Additionally, it details a risk management plan and critical success factors, highlighting the importance of top management commitment and effective communication.