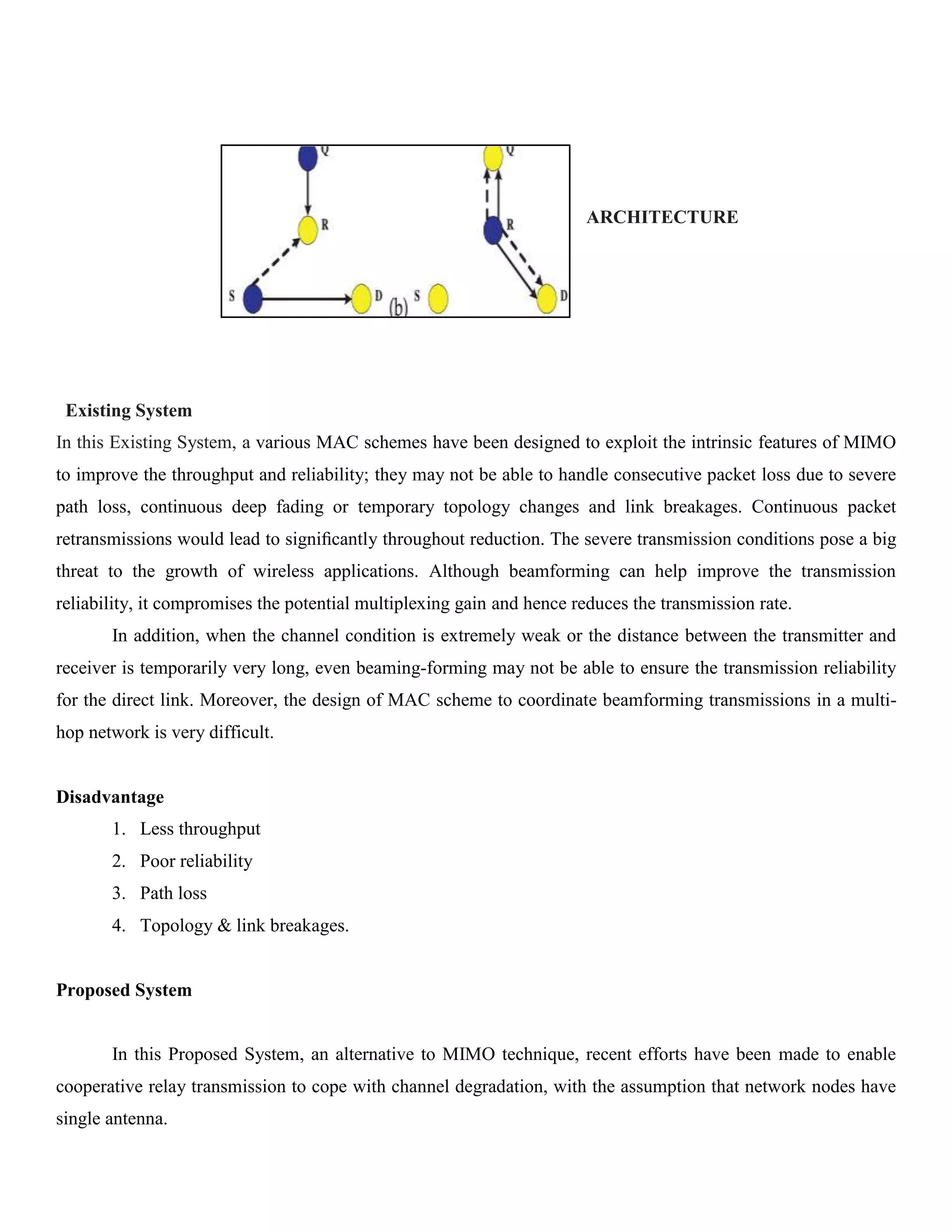
The document discusses a proposed system utilizing cooperative relay transmission in MIMO-based ad hoc networks to enhance communication performance amidst challenging channel conditions. It outlines the development of centralized and distributed scheduling algorithms that efficiently integrate relay transmissions with MIMO technology, achieving improvements in throughput and reliability. Additionally, the performance results indicate significant throughput enhancements across various scenarios, addressing issues such as packet loss and link breakages.

![current elapsed time since its initial transmission, so that candidate relays can record this stamp and update it as
the queuing time increases.
ALGORITHM: - CENTRALIZED AND DISTRIBUTED ALGORITHM
<param name=”filetext”>
</param>
Public IEnumreable<string> producewordblocks(string filetext)
{
int blocksize=250;
int startpos=0;
int len=0;
for(int i=0;i<filetext.Length;i++)
{
i = i + blocksize > filetext.Length – 1 ? filetext.Length – 1 : i + blocksize;
while(i >= startpos && filetext[i] != “ “)
{
i--;
}
if(i == startpos)
{
i = i + blocksize > (filetext.Length – 1) ? filetext.Length – 1 : i + blocksize;
len = (i – startpos) + 1;
}
else
{
len = i – startpos;
}
yield return filetext.Substring(startpos, len).Trim();
startpos = i;
}
}](https://image.slidesharecdn.com/exploitingcooperativerelayforhighperformancecommunicationsinmimoadhocnetworks-131007081819-phpapp01/75/Exploiting-cooperative-relay-for-high-performance-communications-in-mimo-ad-hoc-networks-6-2048.jpg)