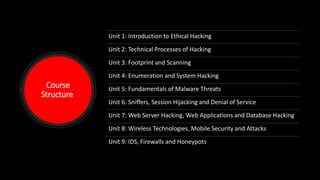
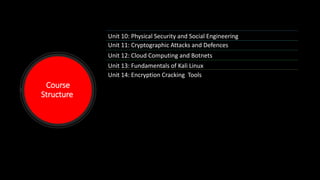
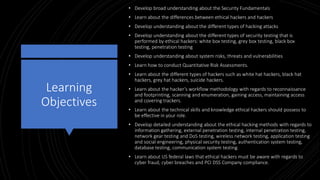
The document outlines a comprehensive training diploma course in ethical hacking provided by the UK Cyber Defence Academy. The course covers various units that include topics such as techniques for hacking, malware threats, and security testing methodologies, alongside practical tools and laws relevant to the industry. Each module is designed to equip participants with knowledge and skills essential for effectively conducting ethical hacking and ensuring cybersecurity.