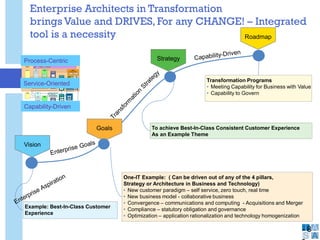
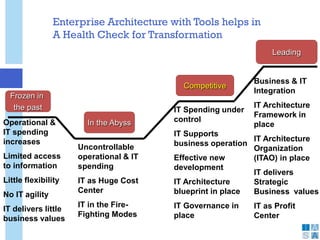
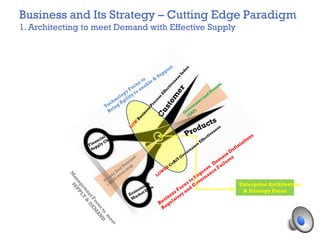
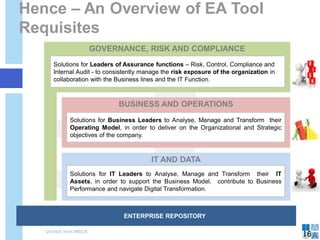
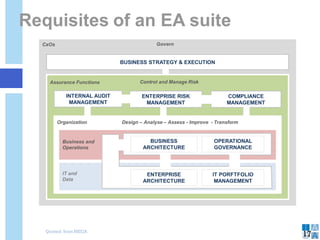
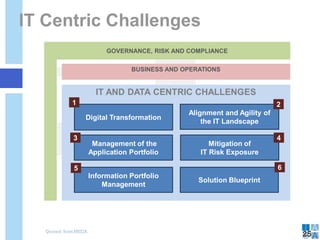
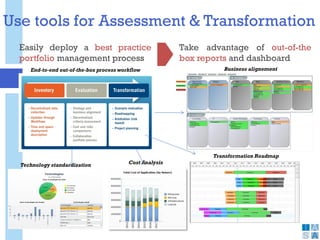
Enterprise architecture tools help organizations transform by capturing essential business and IT information. The tools must:
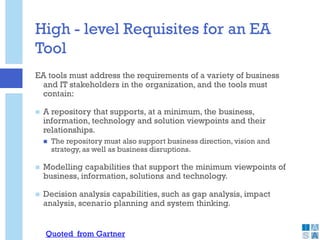
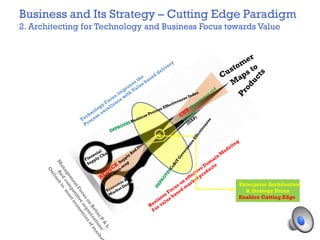
1. Include repositories for business, information, technology, and solutions viewpoints and their relationships.
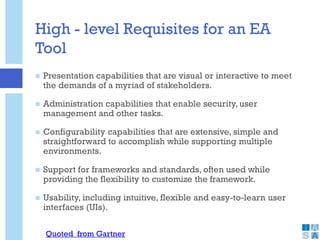
2. Support modeling, decision analysis, visualization, and administration capabilities.
3. Integrate with project and portfolio management to ensure investments align with business strategy and vision.
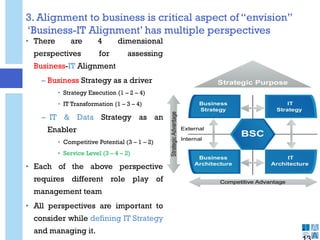
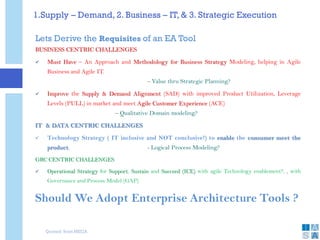
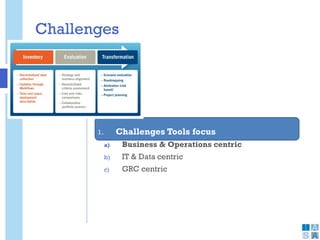
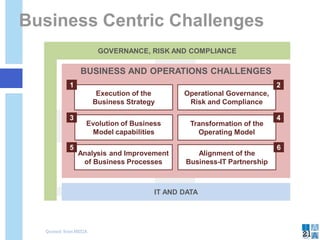
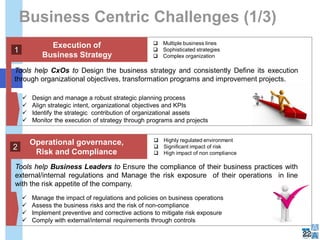
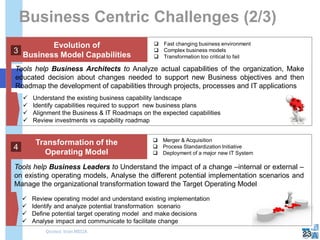
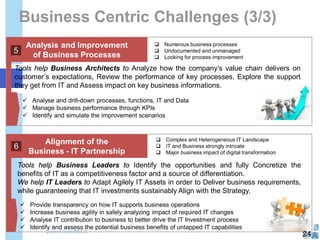
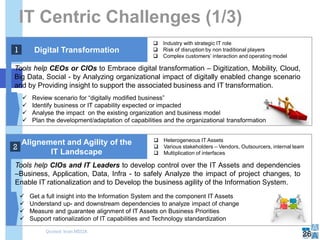
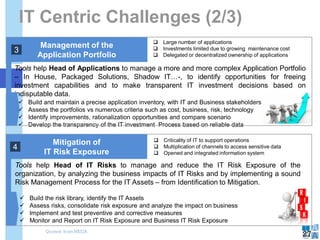
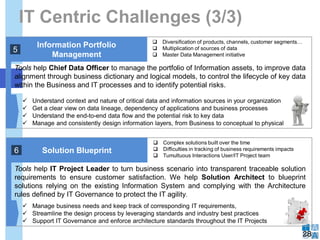
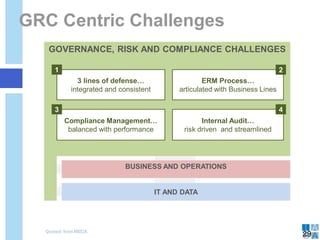
The document discusses how enterprise architecture tools can help organizations address challenges like aligning supply and demand, integrating business and IT strategies, and executing business strategies. It outlines requisites for tools to support business strategy modeling, domain modeling, process modeling, and governance. Overall, the document argues that enterprise architecture tools are necessary to drive organizational change and