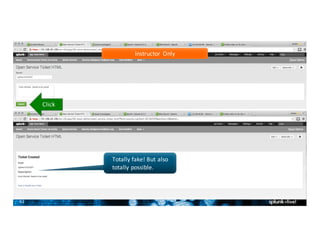
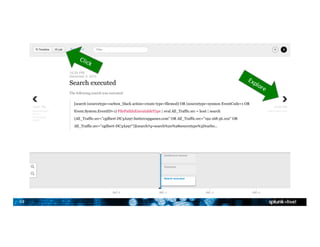
The document is a presentation overview of the Splunk App for Enterprise Security, detailing its functionalities including data ingest, the Common Information Model (CIM), risk analysis, threat intelligence, and incident response workflows. It highlights the app's capabilities for analyzing machine data, generating reports, and customizing searches, along with a guided tour for users. Additionally, it mentions the upcoming Splunk conference, providing details on sessions and networking opportunities.