Embed presentation
Download to read offline

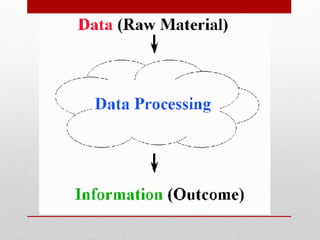
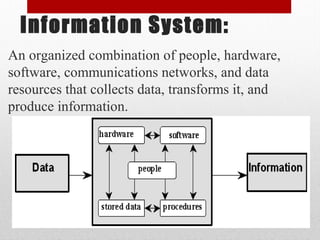
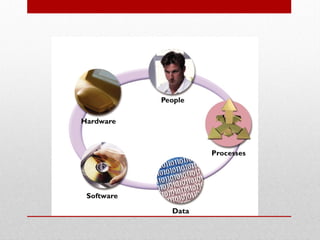


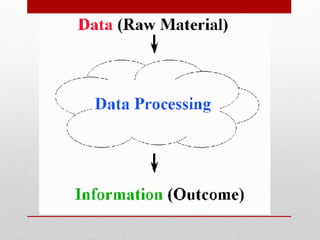
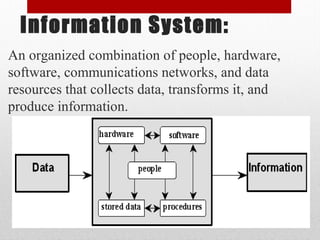
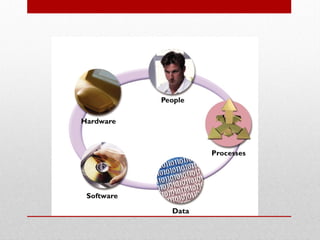
The document outlines the components of an information system, which consists of hardware, software, data, people, and procedures. It differentiates between system software (operating systems and utility programs) and application software (like word processors and web browsers). Additionally, it emphasizes the role of people in the success of an information system and describes procedures as essential strategies for utilizing computer-based information systems.