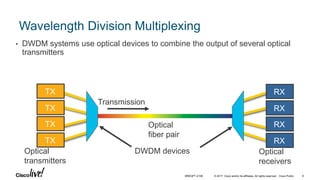
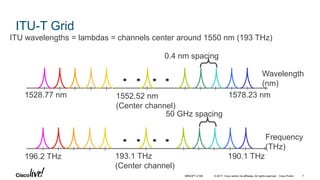
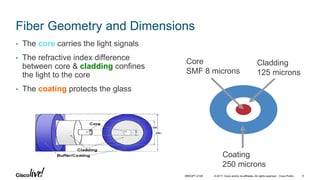
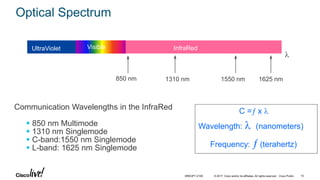
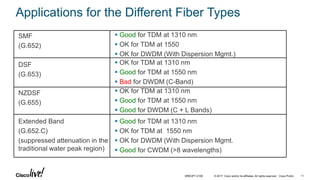
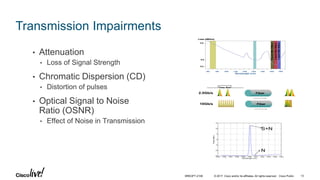
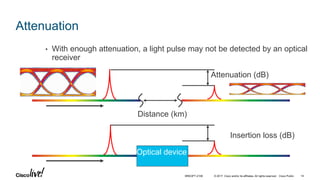
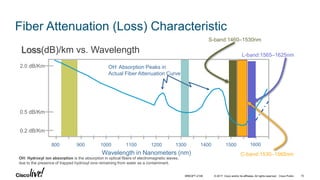
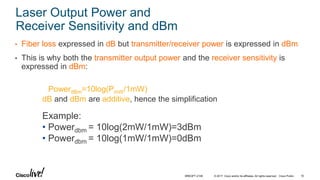
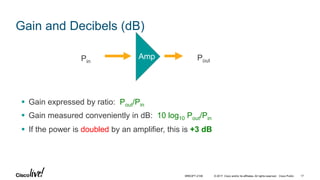
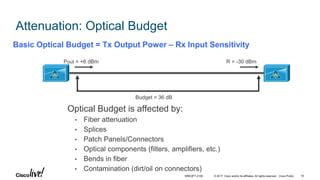
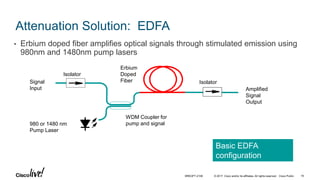
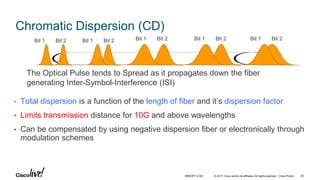
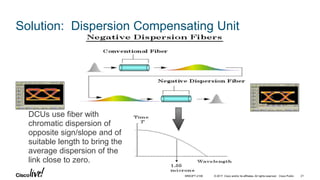
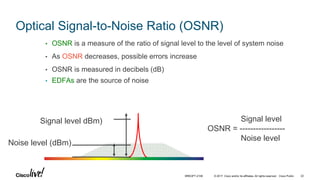
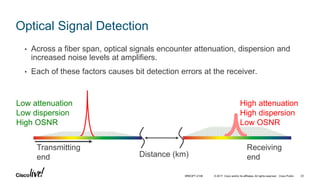
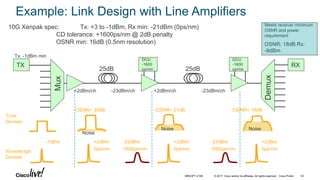
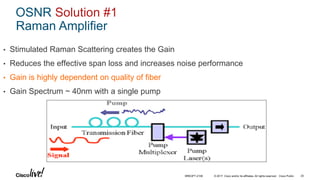
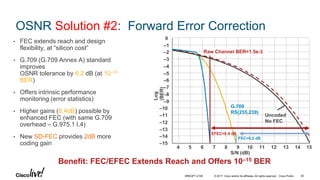
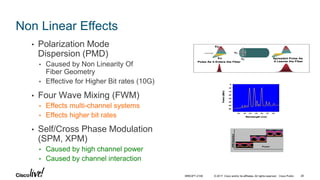
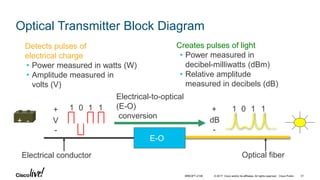
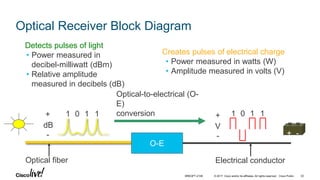
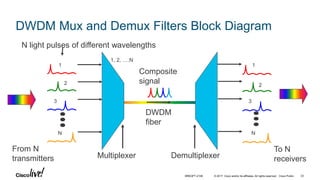
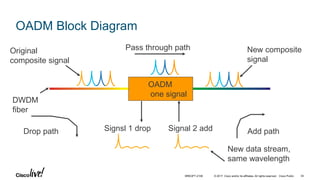
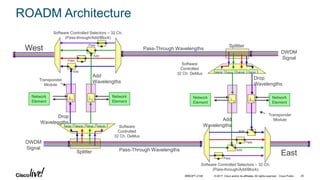
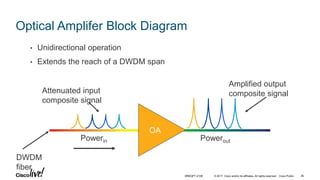
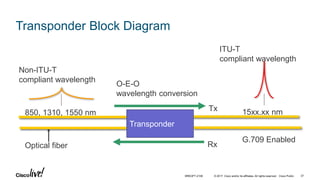
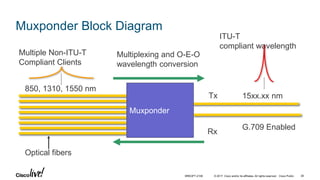
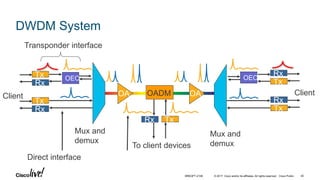
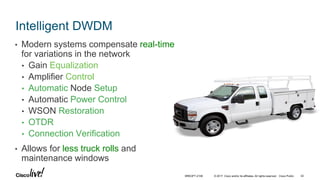
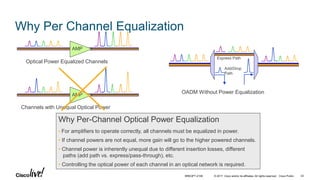
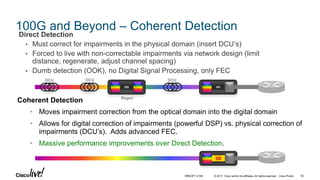
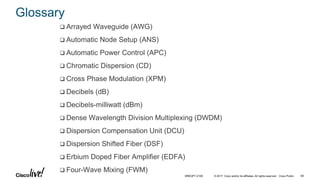
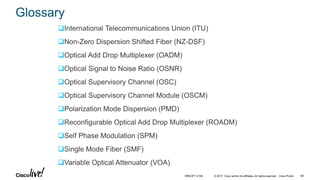
The document provides an overview and agenda for a presentation on advances in Dense Wavelength Division Multiplexing (DWDM). It begins with definitions of DWDM and how it works by combining multiple optical transmitters onto an optical fiber using different wavelengths. It then covers optical fiber types and properties, linear and non-linear effects that impact transmission over fiber including attenuation, chromatic dispersion, optical signal-to-noise ratio, and solutions to mitigate these effects like amplifiers, dispersion compensation, and forward error correction. Finally, it reviews common DWDM components like transmitters, receivers, mux/demux filters, optical add/drop multiplexers, and reconfigurable optical add/drop multiplexers.