This document provides an overview of distributed denial of service (DDoS) attacks including:
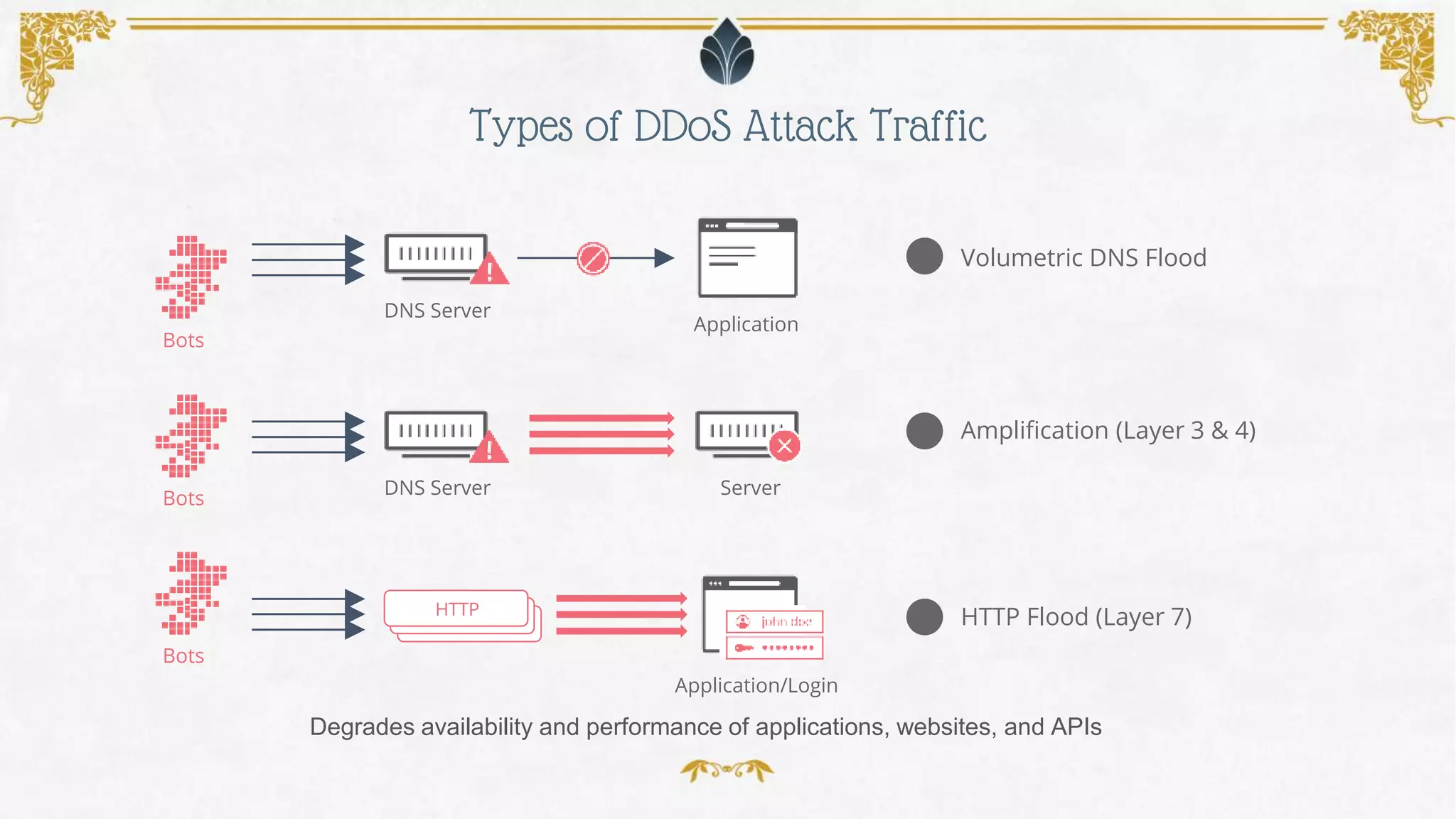
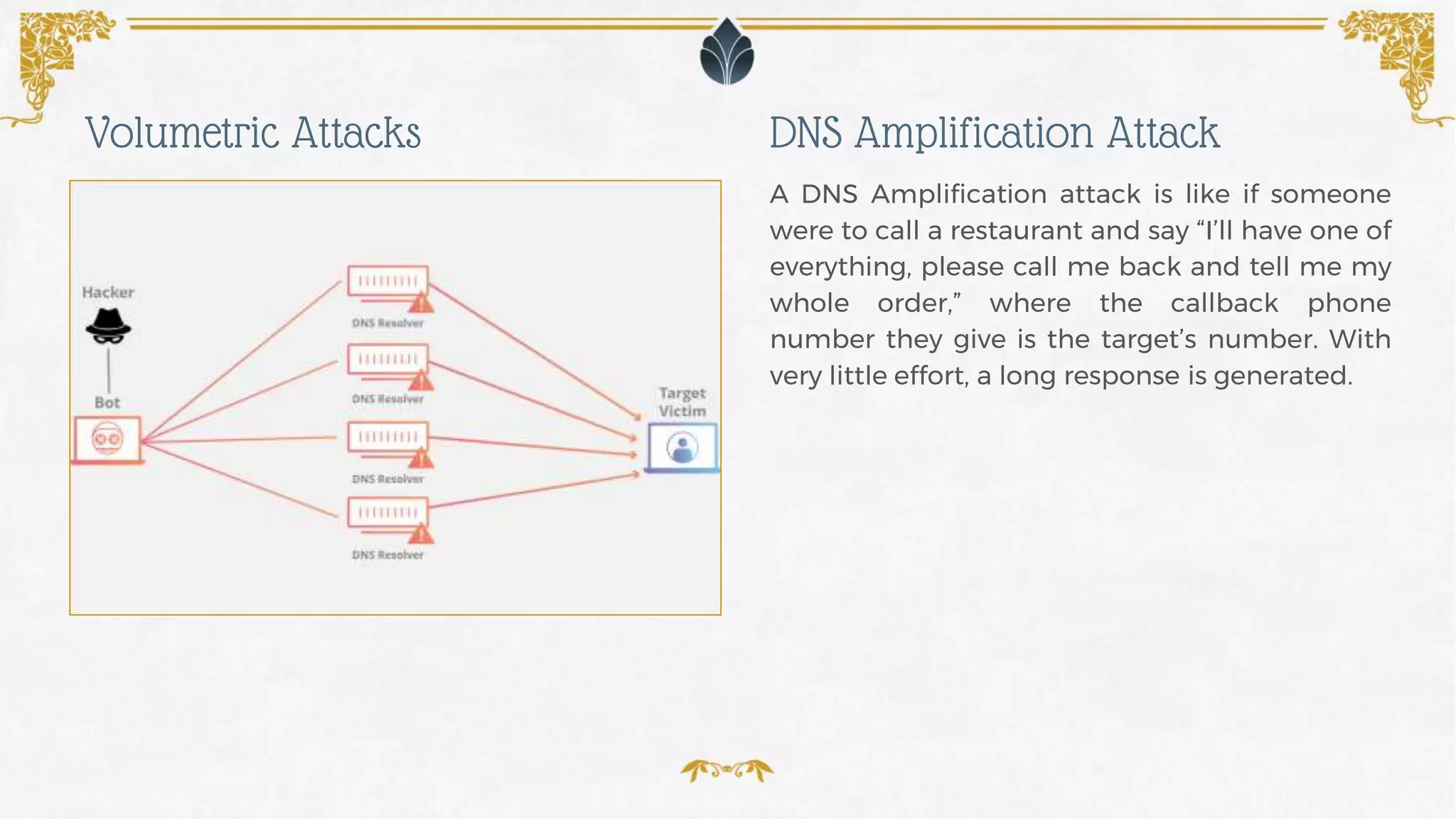
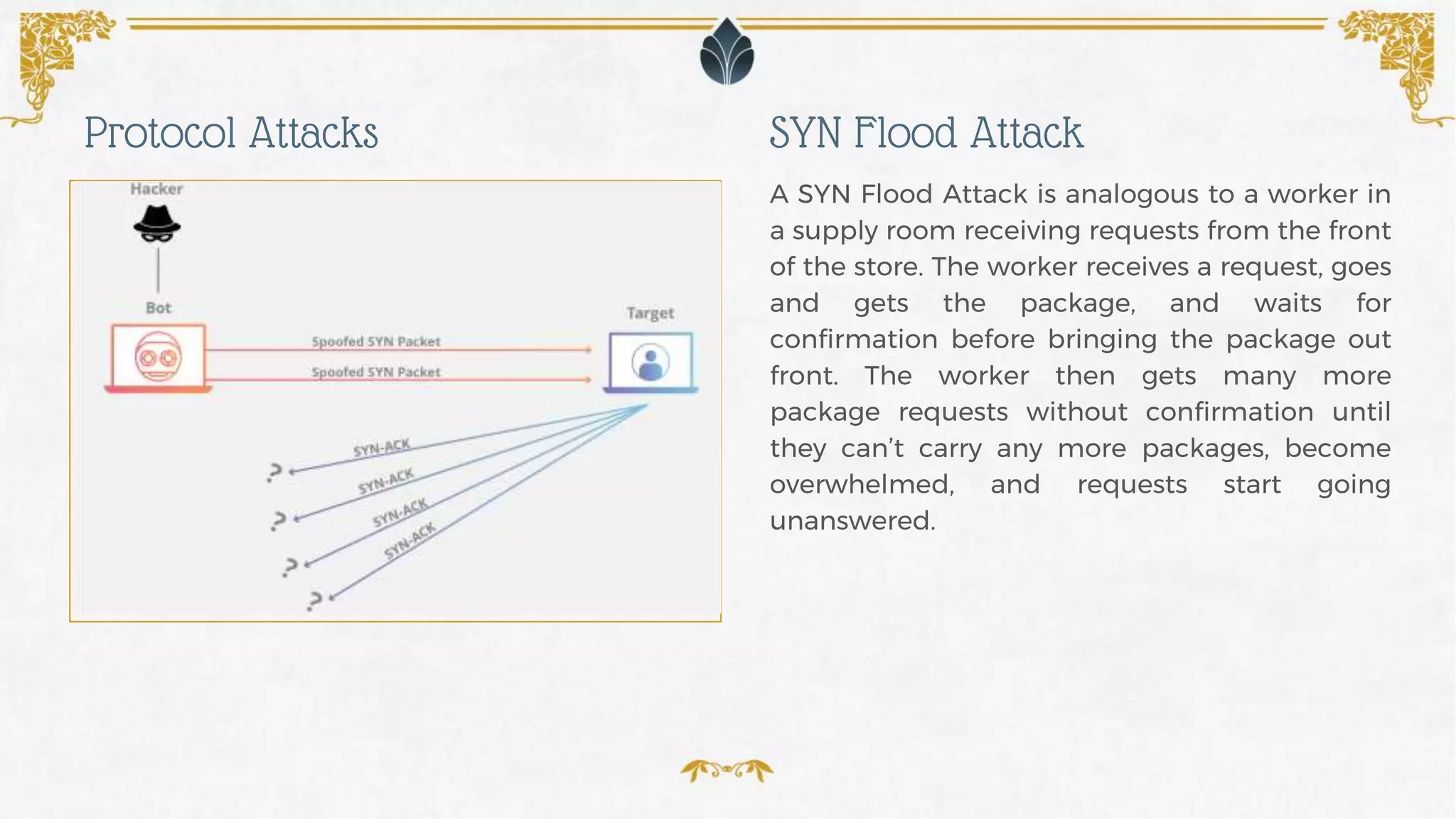
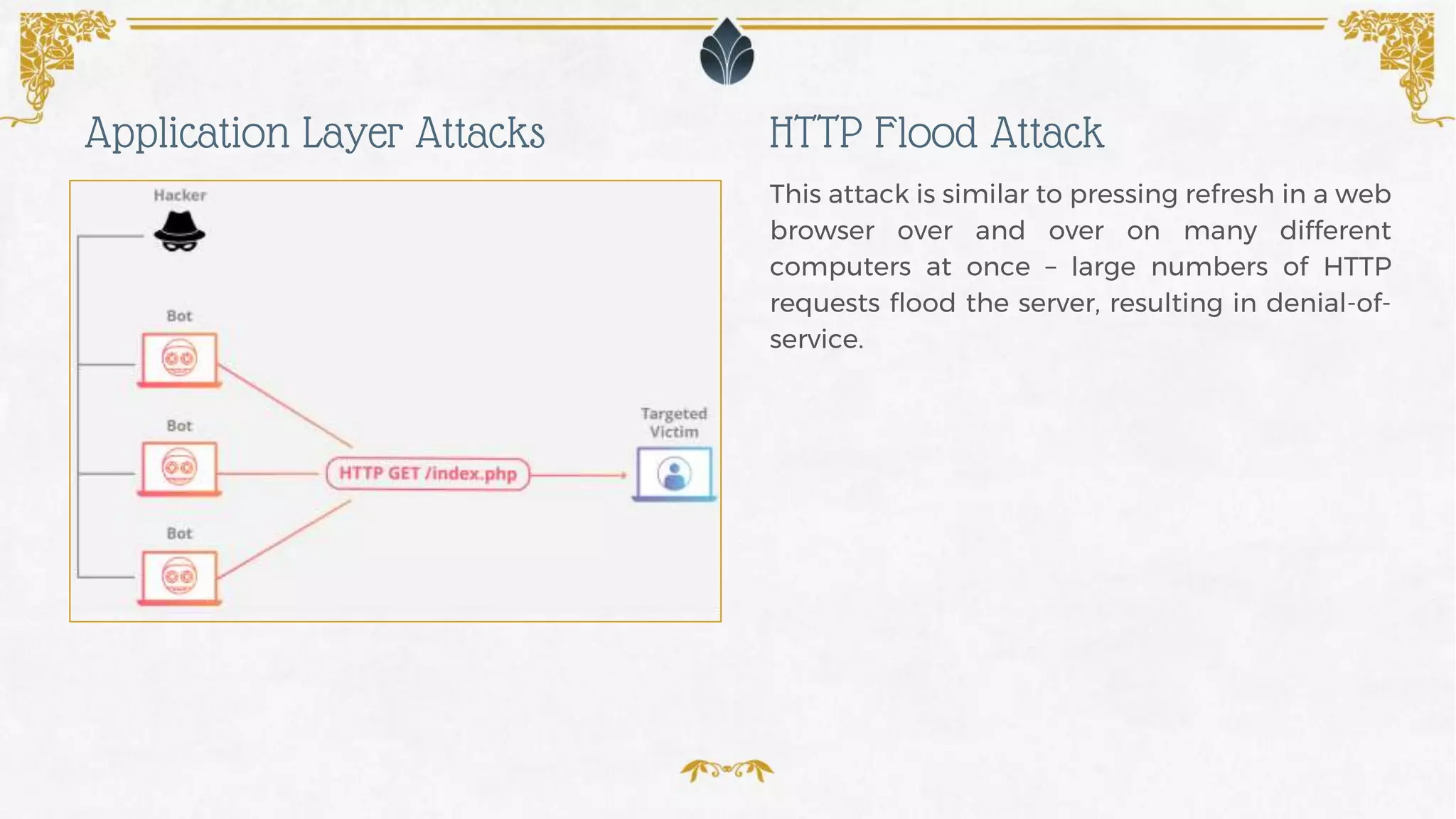
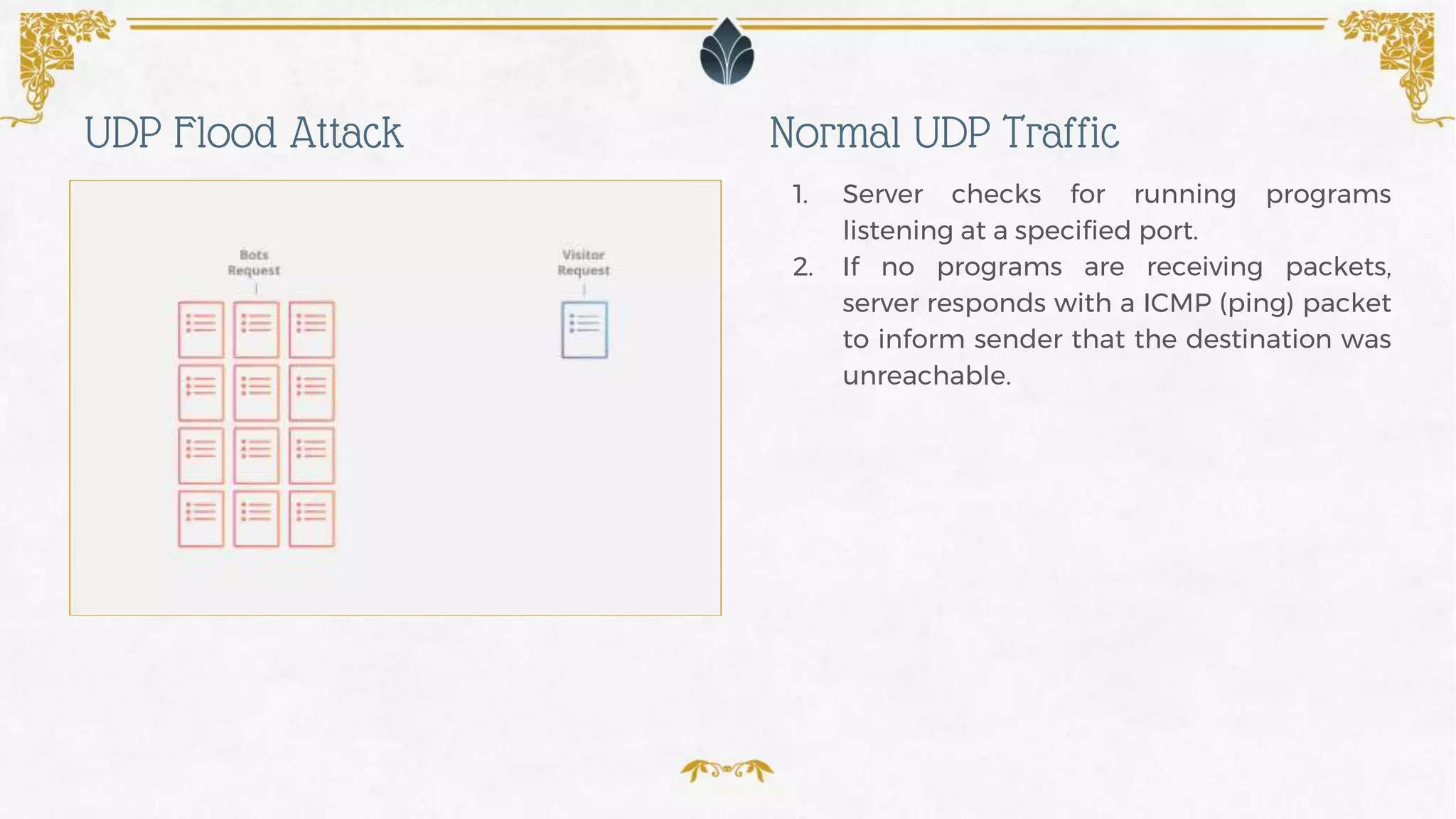
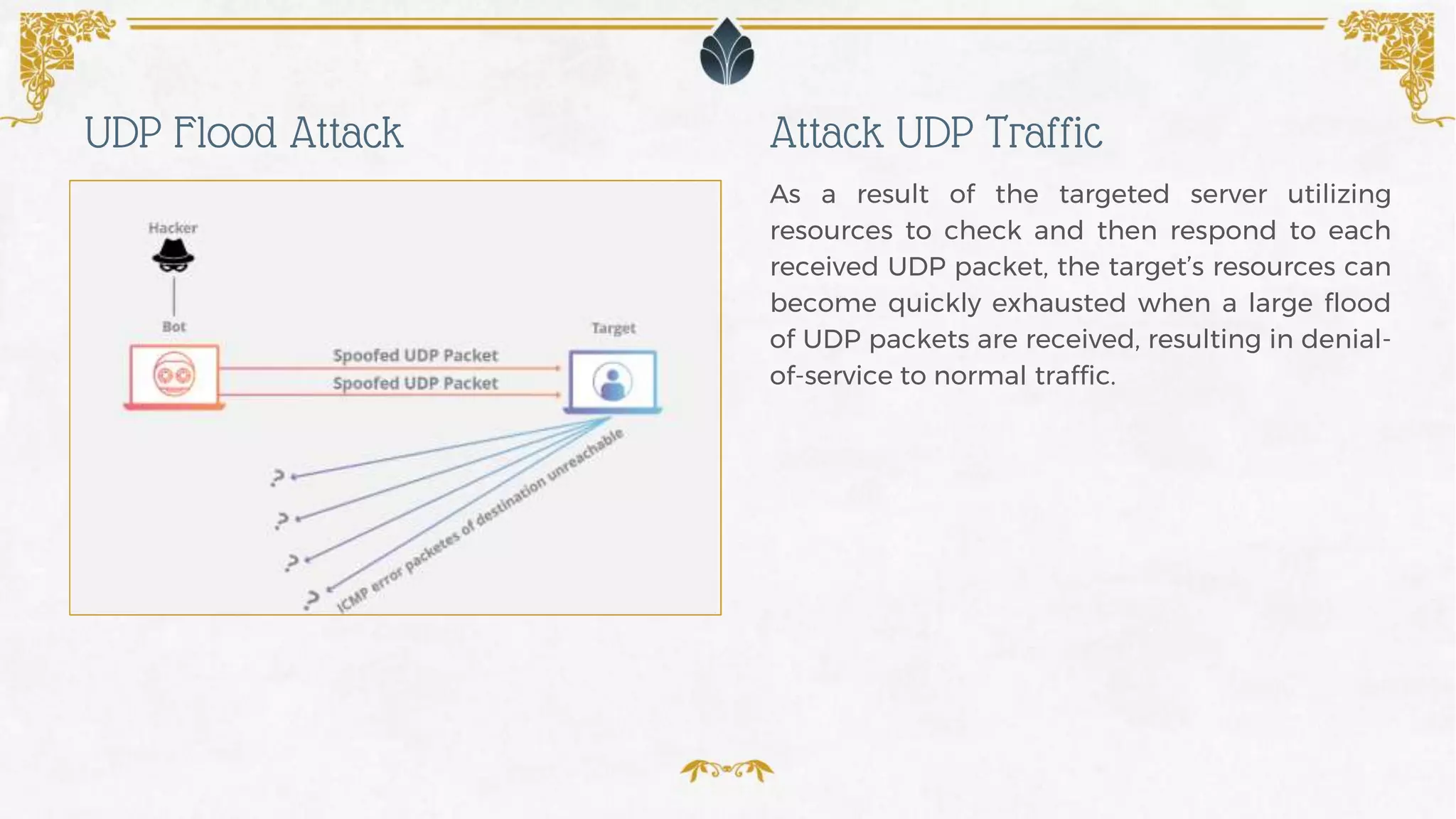
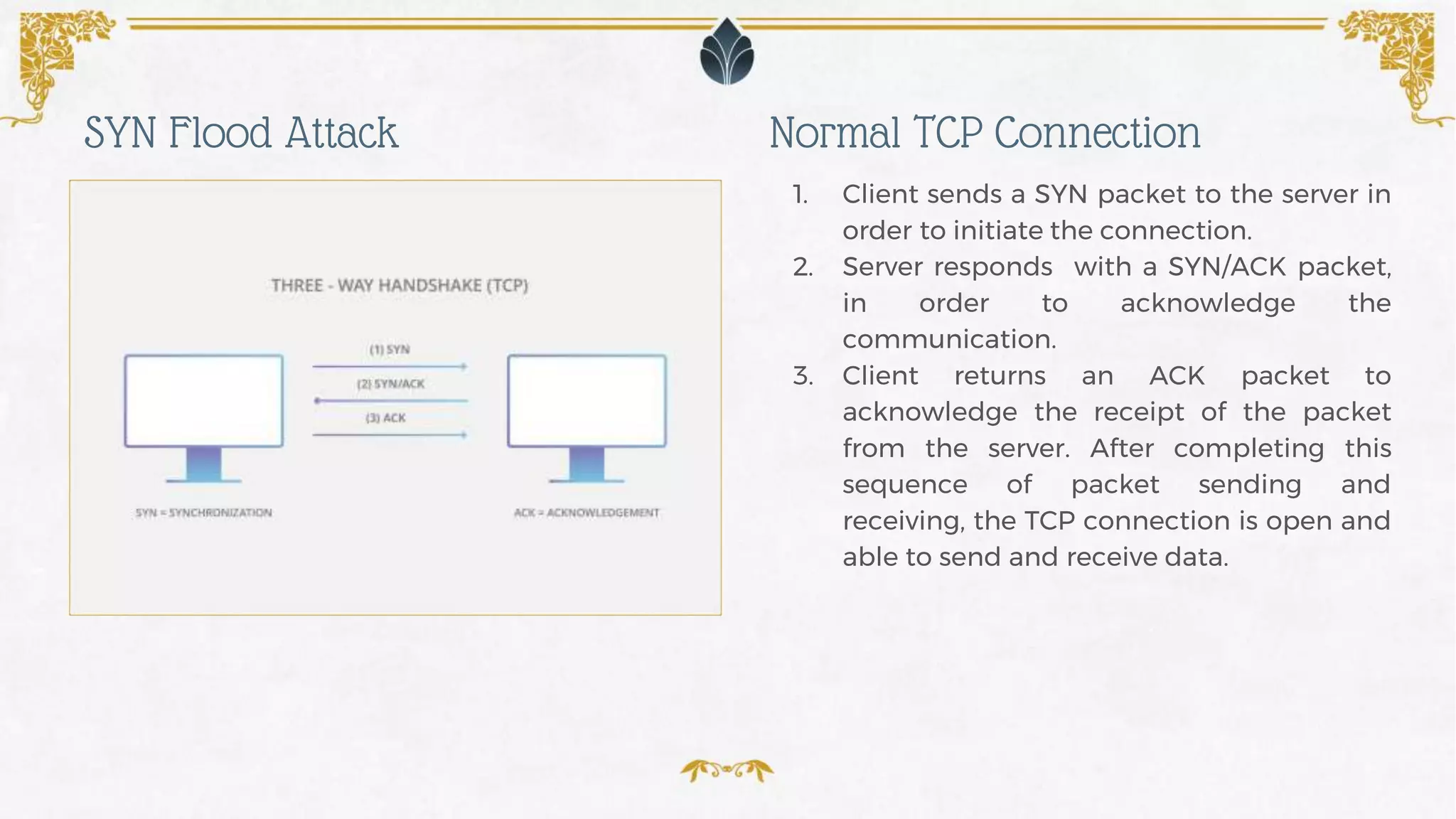
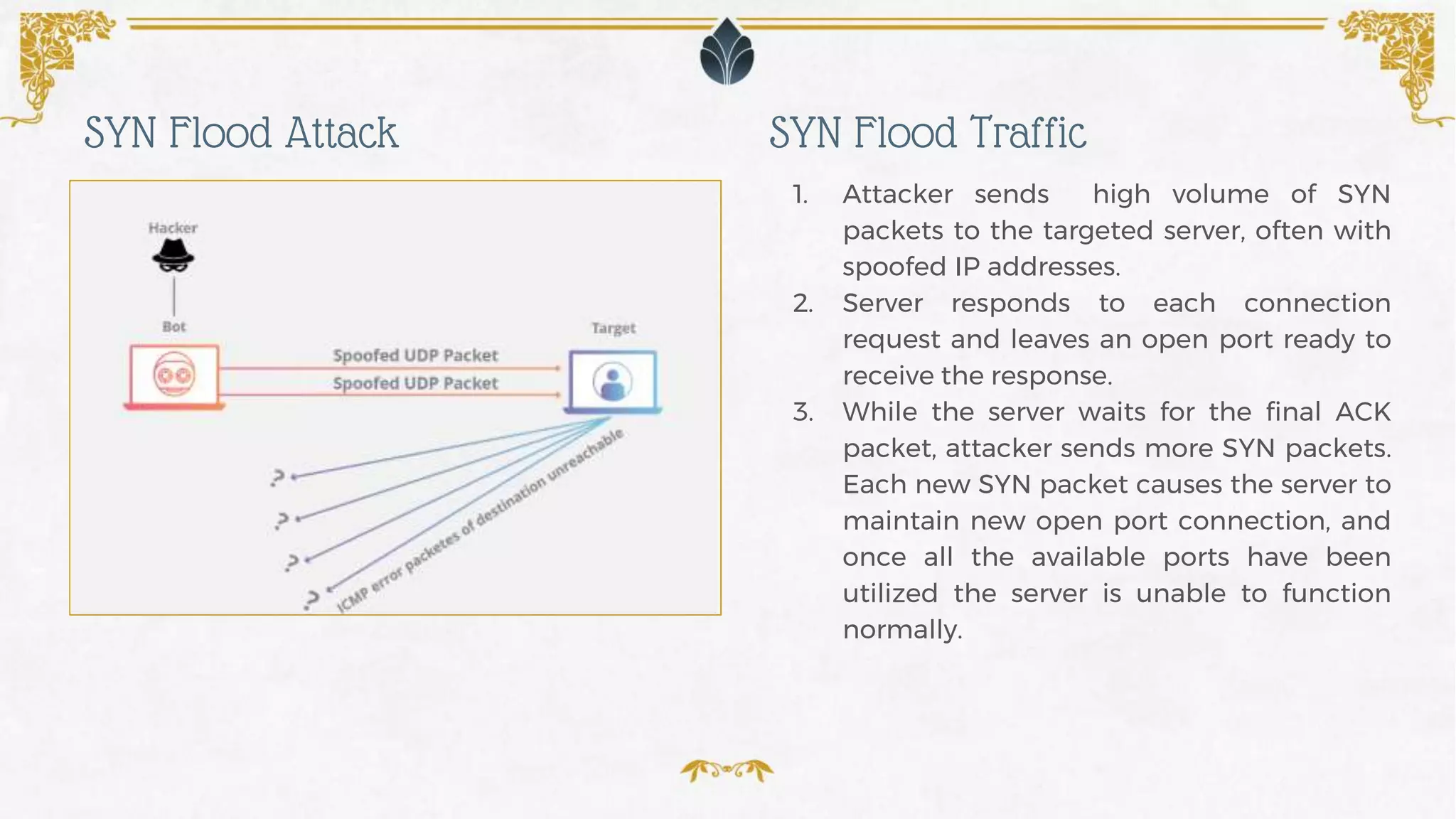
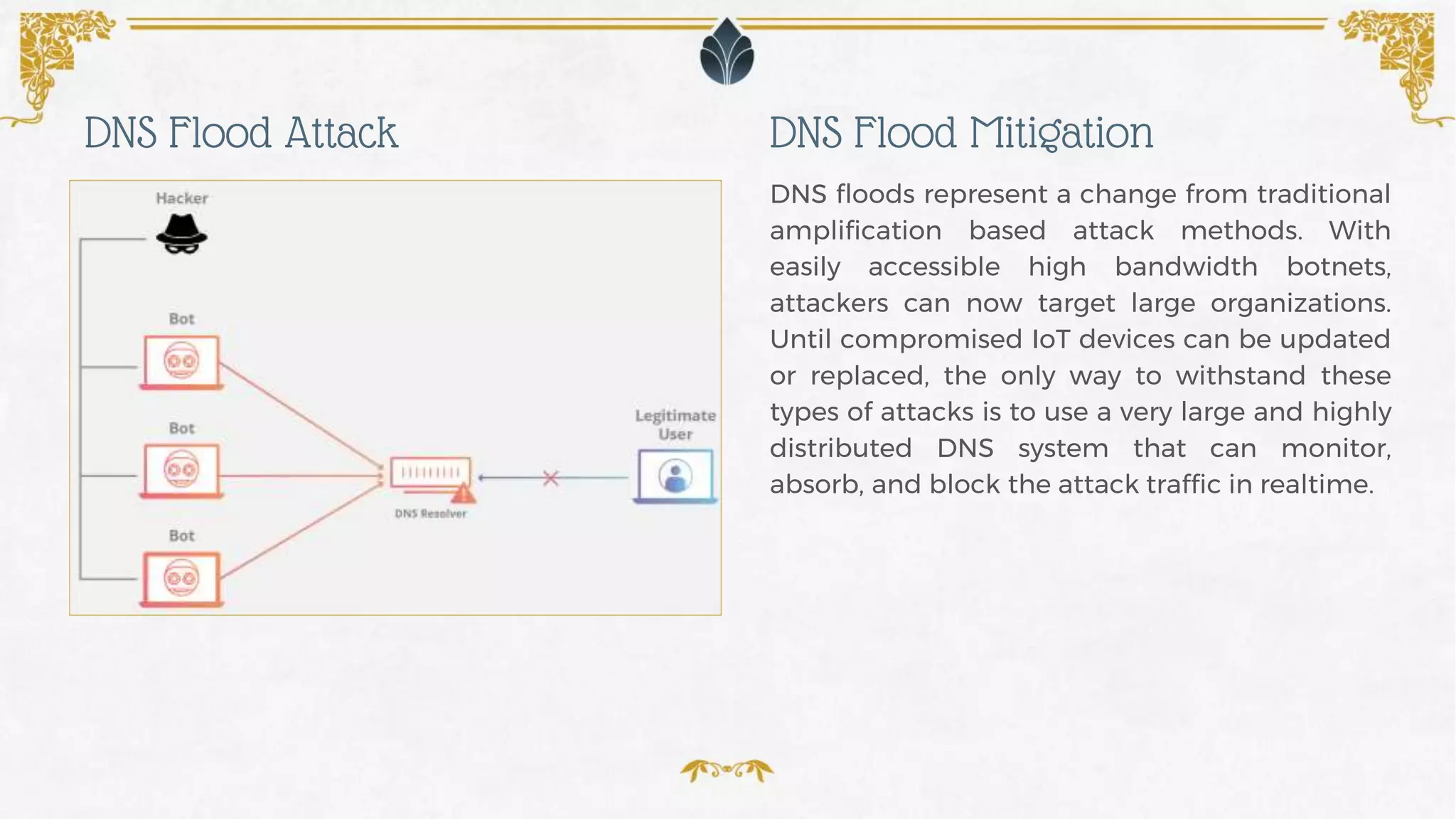
- Common types of DDoS attacks like UDP floods, SYN floods, DNS floods and HTTP floods and how they work to overwhelm servers.
- How DDoS attacks are evolving to larger sizes and more complex botnets.
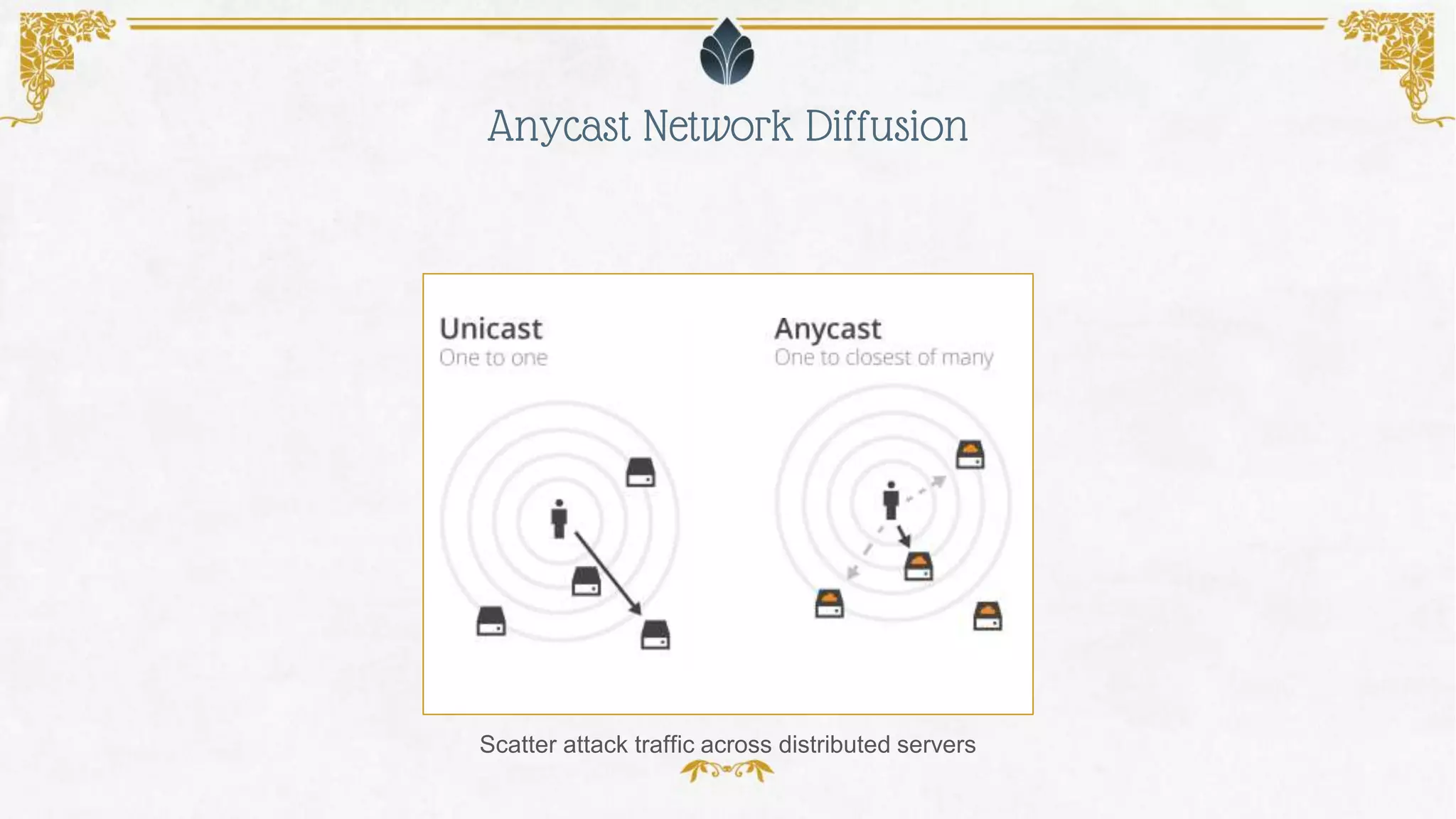
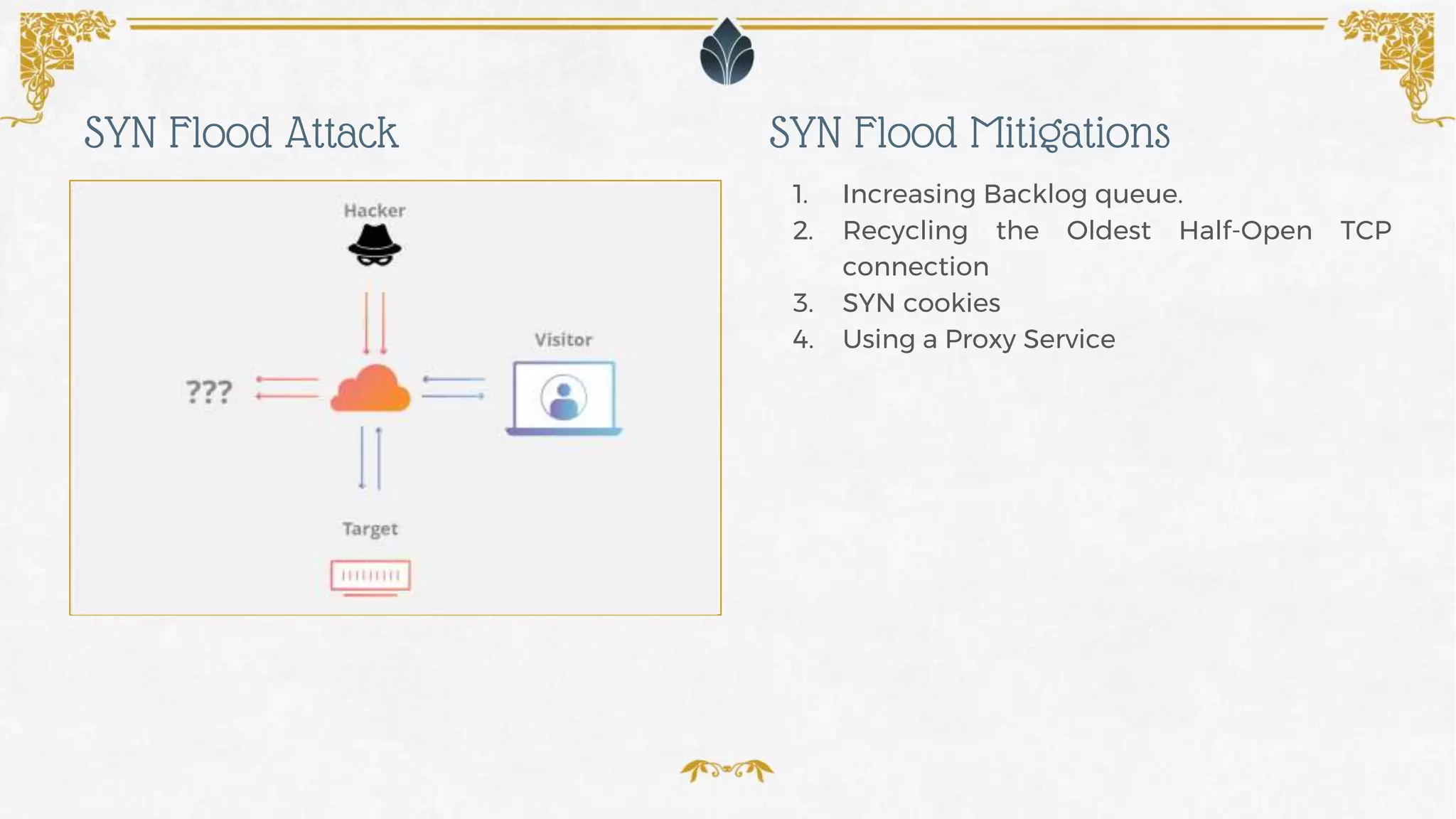
- Methods for mitigating DDoS attacks including black hole routing, rate limiting, web application firewalls, anycast networks and cloud-based DDoS protection services.
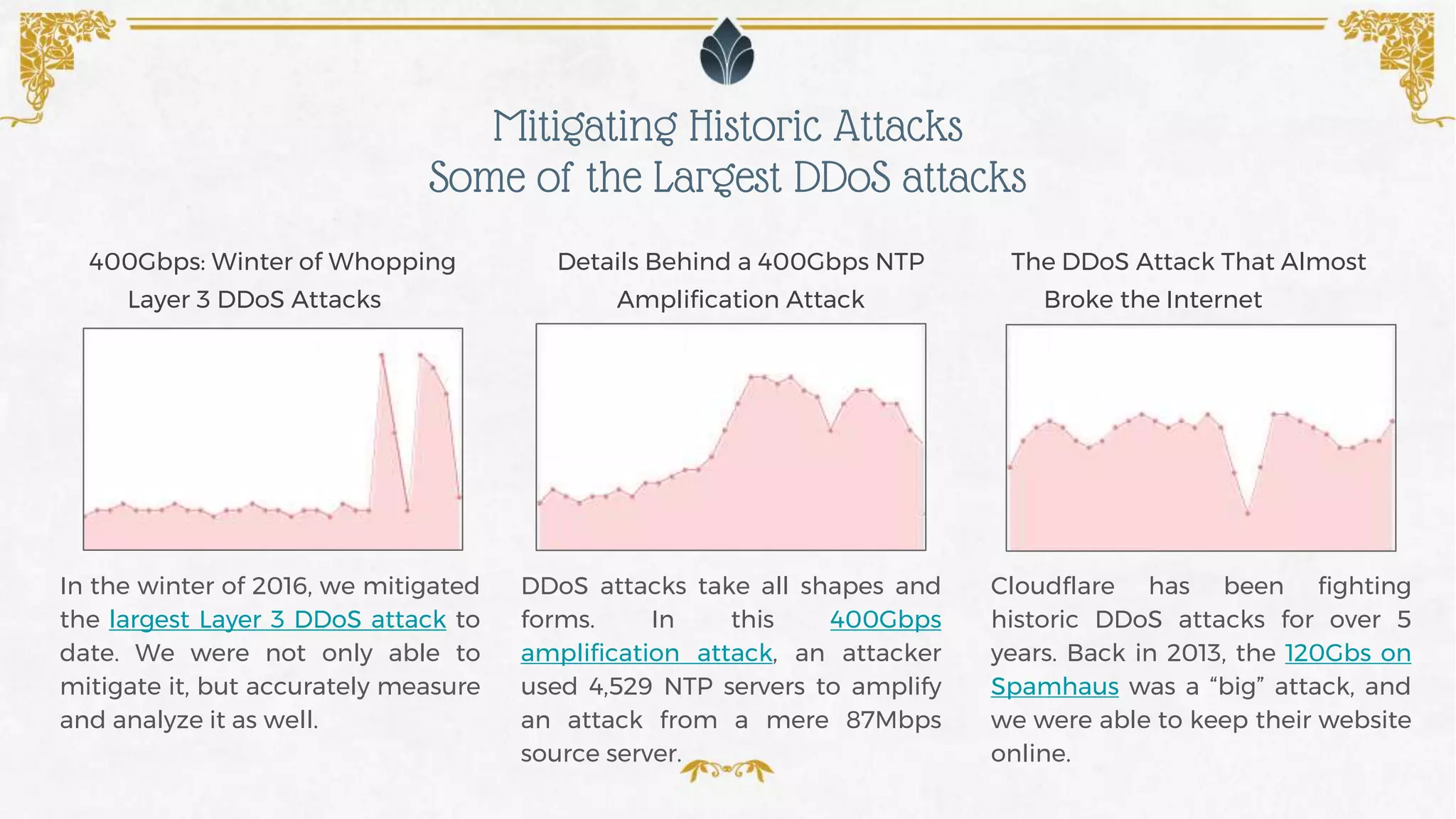
- A real example of mitigating a massive 400Gbps DDoS attack and the largest attacks seen to date.
![❖ Malicious attempt to disrupt
normal traffic
❖ Overwhelm target with flood
❖ Utilize multiple compromised
systems
❖ Motive can be political, social,
or financial
❖ Targets in every industry
Subject: ddos attack
Hi!
If you dont pay 8 bitcoin until 17. january your network will be
hardly ddosed! Our attacks are super powerfull. And if you dont pay
until 17.
january ddos attack will start and price to stop will double!
We are not kidding and we will do small demo now on [XXXXXXXX] to
show we are serious.
Pay and you are safe from us forever.
OUR BITCOIN ADDRESS: [XXXXXXXX]
Dont reply, we will ignore! Pay and we will be notify you payed and
you are safe.
Cheers!
Elements of a DDoS Attack
An Example DDoS Ransom Note](https://image.slidesharecdn.com/drupalconvienna2017-anatomyofddos-170927090705/75/DrupalCon-Vienna-2017-Anatomy-of-DDoS-4-2048.jpg)