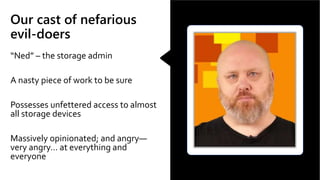
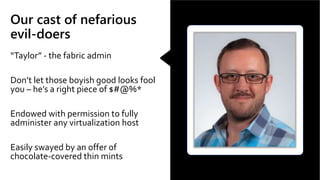
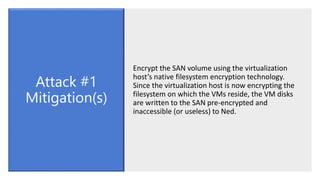
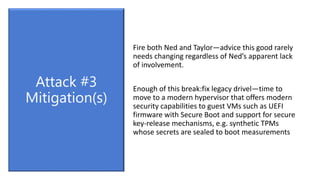
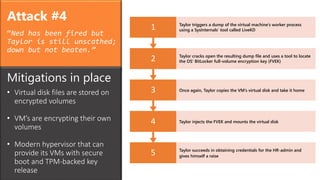
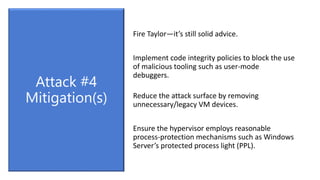
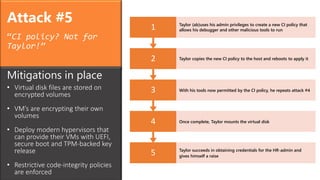
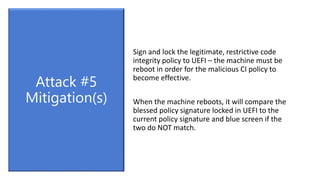
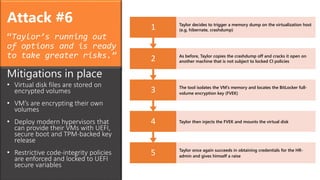
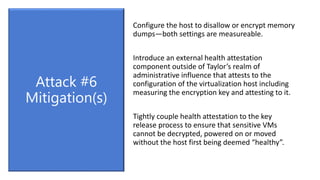
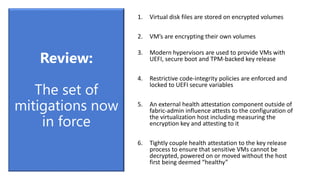
The document outlines attacks on a virtualization fabric by compromised administrators. It describes 6 attacks by the storage admin "Ned" and fabric admin "Taylor" to gain unauthorized access and privileges. Each attack is followed by mitigation strategies to harden the fabric, such as encrypting storage, using secure boot, enforcing code integrity policies, and implementing an external attestation service to verify host configuration and policies before allowing sensitive VM access. The review lists the layered security measures now in place to protect against insider threats.