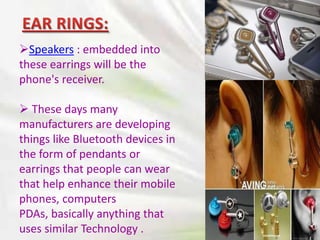
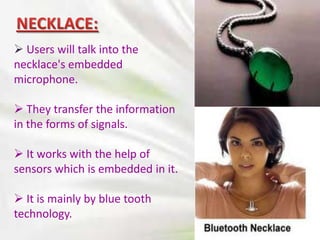
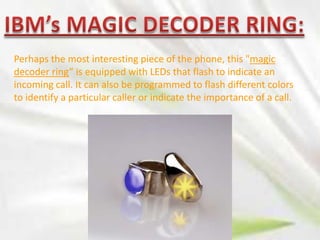
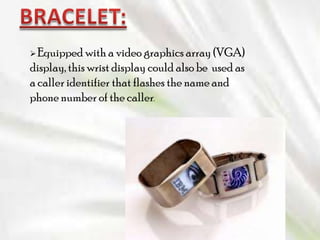
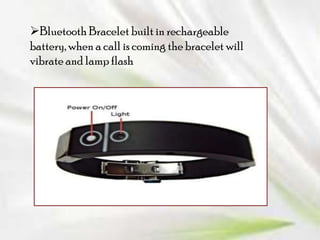
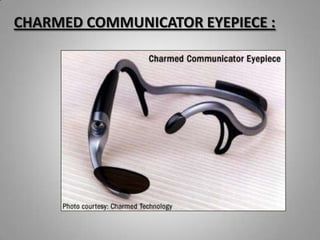
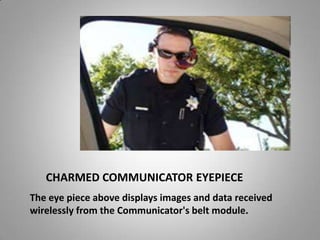
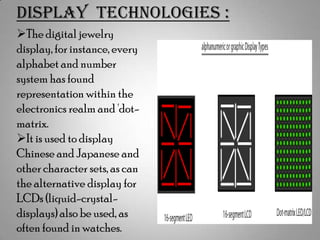
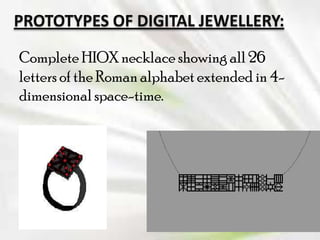
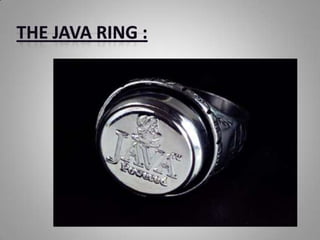
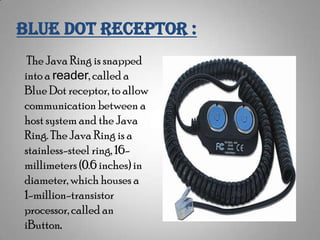
The document discusses the concept of digital jewelry, which embeds computing capabilities into jewelry items like earrings, necklaces, bracelets, and rings. It describes prototypes created by IBM and other companies that could replace items like phones, keys, and ID cards. Functions like calls, data display, passwords, and wireless controls might be integrated. While the idea combines fashion and technology, challenges remain around technical specifications, powering and programming the devices, and commercializing the concept.