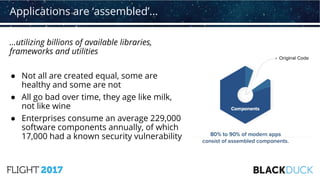
The document discusses the integration of security within DevOps practices, emphasizing the rise of DevSecOps as a response to inadequate security measures in traditional DevOps. It highlights the increasing complexity of software development, the need for better security automation, and the importance of using secure libraries and components. The document also points out the growing trend of enterprises incorporating automated security vulnerability scanning into their DevOps initiatives.