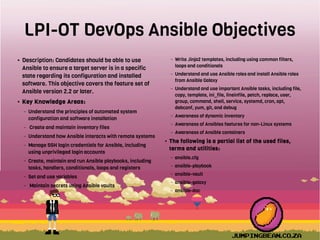
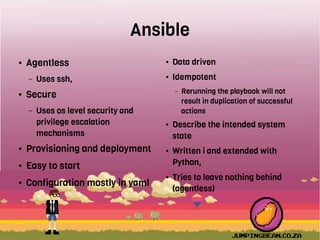
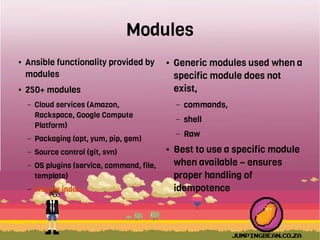
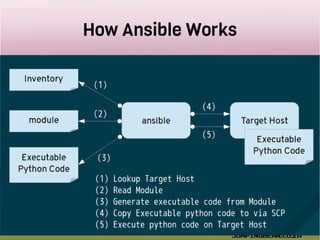
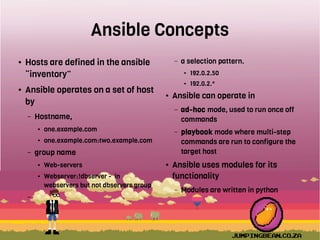
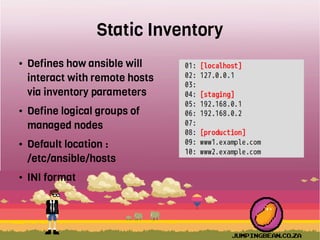
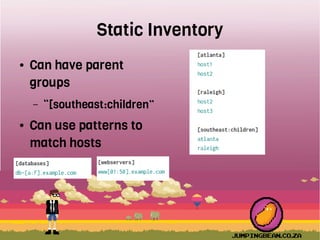
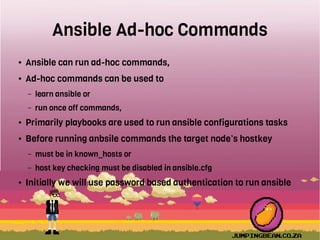
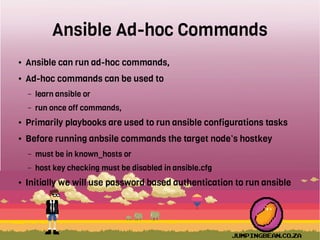
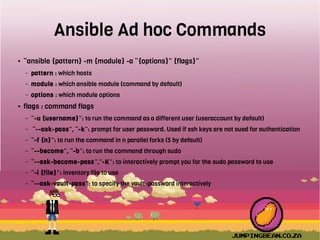
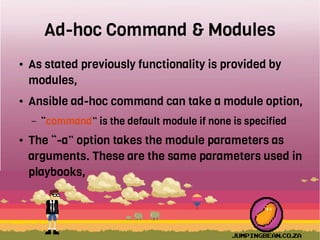
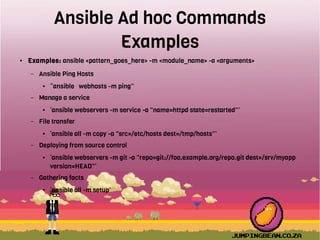
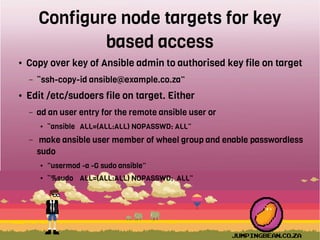
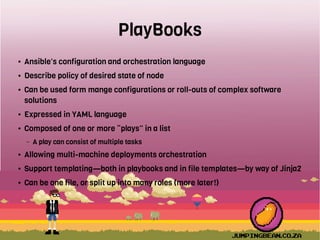
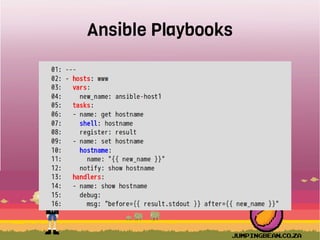
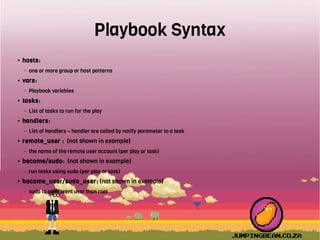
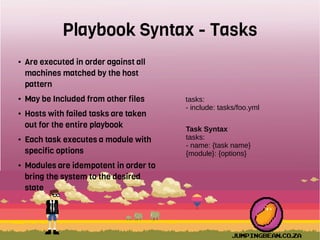
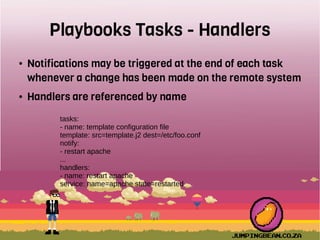
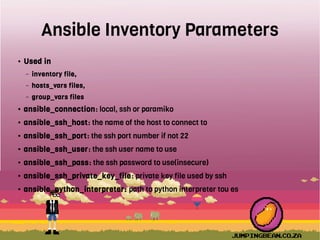
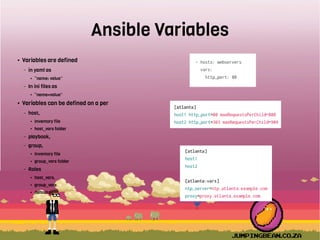
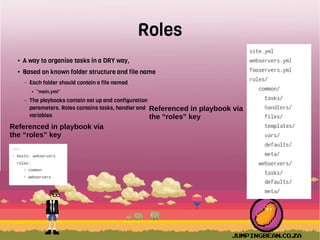
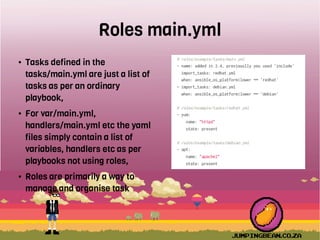
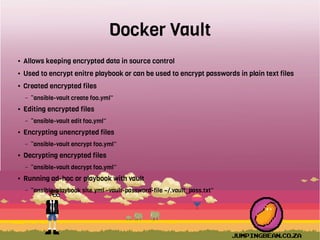
The document outlines the objectives and key knowledge areas for Ansible DevOps training, focusing on automated system configuration, software installation, and usage of Ansible version 2.2 or later. It details how to create and manage inventory files, utilize SSH for remote systems, write playbooks, and understand roles and modules, emphasizing the idempotent nature of actions performed. Additionally, it covers the prerequisites for labs, command syntax for ad-hoc commands, and how to handle secrets with Ansible Vault.