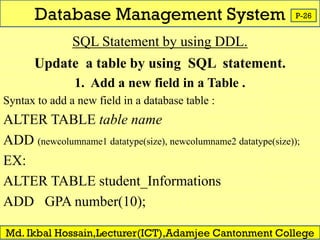
This document discusses database management systems and related concepts. It defines what a database and DBMS are, and describes some common DBMS software. It also explains key database concepts like data types, fields, records, files, and data hierarchy. SQL is introduced as the most common query language for databases. The document outlines the different types of SQL statements for defining, manipulating, and querying data in a database. Database relationships like one-to-one, one-to-many, many-to-one, and many-to-many are also summarized.