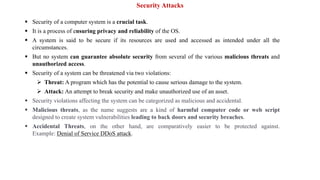
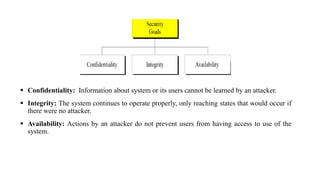
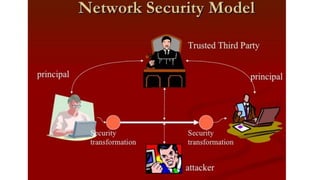
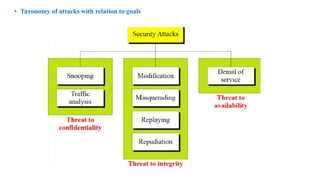
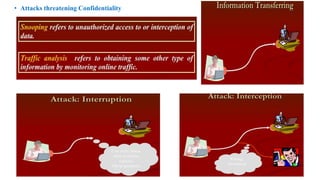
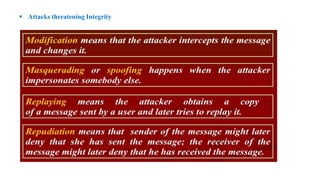
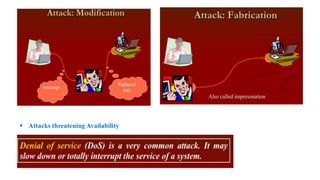
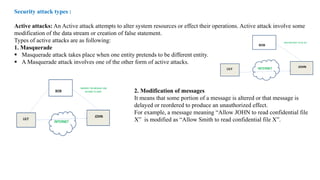
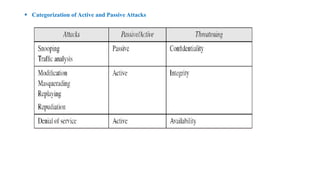
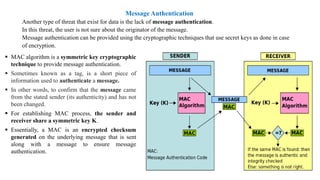
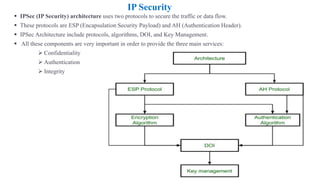
The document outlines various computer security concepts including active and passive attacks, message authentication, email security, IP security, cryptographic suites, and firewalls. It highlights the importance of protecting computer systems from various threats, both malicious and accidental, and provides details on the mechanisms used for securing data, such as message authentication codes, firewalls, and email protection measures. Additionally, it reviews different types of attacks and security measures, detailing the architecture and protocols involved in securing network communications.