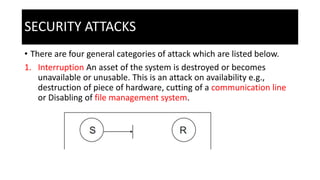
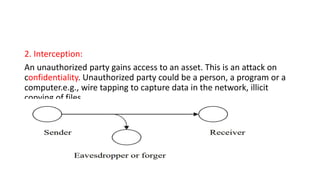
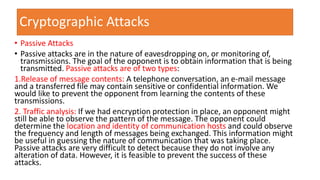
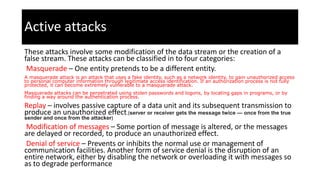
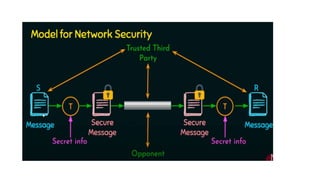
Computer data can be vulnerable when traveling between computers. Cryptography transforms data using secret codes and modern mathematics, making it safer during transmission. It provides security by encrypting data to protect confidentiality and ensuring integrity and authentication of messages. Common security threats include passive attacks like eavesdropping and traffic analysis, as well as active attacks like masquerading, message modification, denial of service, and replays. Cryptography addresses these using techniques like symmetric and public key encryption.