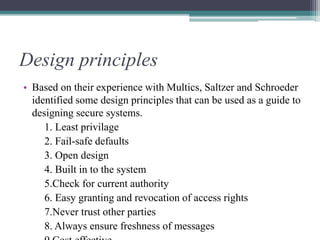
The document discusses computer security, outlining its necessity for protecting sensitive information and defining key goals such as secrecy, privacy, authenticity, and integrity. It categorizes threats into passive and active attacks, detailing methods like browsing, leaking, viruses, and logic bombs. It further covers cryptography, authentication, access control, and essential design principles for creating secure systems.