Data Sheet: Corporate Overview
•
1 like•276 views
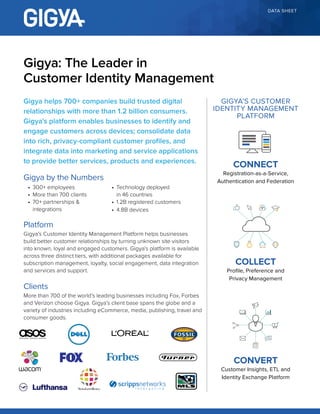
Gigya helps over 700 companies build relationships with over 1.2 billion consumers through its customer identity management platform. The platform enables businesses to identify customers across devices, consolidate user data into privacy-compliant profiles, and integrate that data into marketing applications to improve customer service, products, and experiences. Gigya has over 300 employees, 700 clients spanning many industries, and has raised over $100 million from investors including Benchmark Capital and Intel Capital.
Report
Share
Report
Share
Download to read offline
Recommended
Gigya and Marketo

Get Better Results with Identity-Driven Marketing Automation
Gigya’s pre-built integration fuels Marketo's marketing automation software with rich first-party identity data. With Gigya and Marketo, brands can:
*Sync any data points between Gigya’s Profile Management and Marketo
*Set updates to ensure that you’re always working with accurate user data
*Build timely and relevant campaigns that foster valuable, lifetime relationships with your customers
Connect, Collect, Convert

To be successful today, businesses must leverage consumer data to enable great customer experiences. Doing this in a seamless and compliant way is not easy, with a shifting regulatory landscape, numerous identity providers and front-end technologies to support. Gigya's end-to-end Customer Identity Management platform helps businesses succeed by providing:
*Flexible registration and authentication to connect you with your customers
*Profile and preference management to collect all data types into unified and compliant profiles
*Powerful customer insights tools and easy integration with virtually any third-party technology
Data Sheet: Why CPG Companies Need CIAM

A true customer identity and access management (CIAM)
solution allows CPG companies to easily manage multiple
brands in various countries, providing the ability to identify
customers and reconcile all data types into complete user
profiles across channels and brands. This data can be
leveraged to build relevant campaigns and experiences that
create value beyond cost savings to maximize acquisition,
conversions and loyalty.
Case Study: Frontier Communications

Gigya’s Registration-as-a-Service (RaaS) provides Frontier Communications with the flexibility to quickly deploy custom registration forms and flows across its web and mobile properties, complete with identity validation and verification policies. All data collected through registration and known users’ on-site actions is organized into unified profiles in Gigya’s Profile Management database, which serves as a single source of truth across properties. Profile Management automatically maintains data privacy compliance, protection and quality.
Data Sheet: IAM vs. CIAM: A Simple Choice

Managing self-provisioned profiles and customer-generated
data within legacy IAM has proven overwhelming and costly. A cloud-based Customer Identity and Access Management (cIAM) platform can meet this challenge while helping your business extract maximum value from customer data.
CIS 2015 Modernize IAM with UnboundID and Ping Identity - Terry Sigle & B. Al...

UnboundID and Ping Identity are partnering to bring together
their solutions for Federated Single Sign-On, high performance LDAP directory servers, and customer identity
and preference management into an integrated solution for enterprise customers. Obtain a joint product briefing and demo of these solutions to modernize legacy IAM systems.
Data Sheet: Why Your eCommerce Platform Needs CIAM

A specialized customer identity and access management (CIAM) solution can maximize the potential of your eCommerce platform, allowing you to deliver more relevant experiences across every touchpoint by enabling:
- Flexible registration and social login
- Customer-focused profile management
- Pre-built integrations with today's top revenue-driving technologies
Recommended
Gigya and Marketo

Get Better Results with Identity-Driven Marketing Automation
Gigya’s pre-built integration fuels Marketo's marketing automation software with rich first-party identity data. With Gigya and Marketo, brands can:
*Sync any data points between Gigya’s Profile Management and Marketo
*Set updates to ensure that you’re always working with accurate user data
*Build timely and relevant campaigns that foster valuable, lifetime relationships with your customers
Connect, Collect, Convert

To be successful today, businesses must leverage consumer data to enable great customer experiences. Doing this in a seamless and compliant way is not easy, with a shifting regulatory landscape, numerous identity providers and front-end technologies to support. Gigya's end-to-end Customer Identity Management platform helps businesses succeed by providing:
*Flexible registration and authentication to connect you with your customers
*Profile and preference management to collect all data types into unified and compliant profiles
*Powerful customer insights tools and easy integration with virtually any third-party technology
Data Sheet: Why CPG Companies Need CIAM

A true customer identity and access management (CIAM)
solution allows CPG companies to easily manage multiple
brands in various countries, providing the ability to identify
customers and reconcile all data types into complete user
profiles across channels and brands. This data can be
leveraged to build relevant campaigns and experiences that
create value beyond cost savings to maximize acquisition,
conversions and loyalty.
Case Study: Frontier Communications

Gigya’s Registration-as-a-Service (RaaS) provides Frontier Communications with the flexibility to quickly deploy custom registration forms and flows across its web and mobile properties, complete with identity validation and verification policies. All data collected through registration and known users’ on-site actions is organized into unified profiles in Gigya’s Profile Management database, which serves as a single source of truth across properties. Profile Management automatically maintains data privacy compliance, protection and quality.
Data Sheet: IAM vs. CIAM: A Simple Choice

Managing self-provisioned profiles and customer-generated
data within legacy IAM has proven overwhelming and costly. A cloud-based Customer Identity and Access Management (cIAM) platform can meet this challenge while helping your business extract maximum value from customer data.
CIS 2015 Modernize IAM with UnboundID and Ping Identity - Terry Sigle & B. Al...

UnboundID and Ping Identity are partnering to bring together
their solutions for Federated Single Sign-On, high performance LDAP directory servers, and customer identity
and preference management into an integrated solution for enterprise customers. Obtain a joint product briefing and demo of these solutions to modernize legacy IAM systems.
Data Sheet: Why Your eCommerce Platform Needs CIAM

A specialized customer identity and access management (CIAM) solution can maximize the potential of your eCommerce platform, allowing you to deliver more relevant experiences across every touchpoint by enabling:
- Flexible registration and social login
- Customer-focused profile management
- Pre-built integrations with today's top revenue-driving technologies
Winning with GDPR: How to Win Customer Loyalty and Trust

New research by ForgeRock and MyCustomer has revealed that customer trust, and their willingness to share data, is being harmed by the poor quality of digital experiences. So how can your organisation break this cycle? Customer Insights Expert, Paul Laughlin and Doug Norton-Bilsby, Global VP of Retail and Consumer Products at ForgeRock discuss.
2016 04-26 webinar - consumer-focused identity management

identity and cloud cybersecurity today mean a lot more than has traditionally been understood in these technology disciplines. we will see how the technological and legal shifts that have taken place have major implications not just for IAM and cybersecurity, but also for the discipline traditionally known as customer relationship management, or CRM.
Ping Identity: Corporate Overview Financial Services

From Denver based identity and access management vendor Ping Identity comes this presentation explaining how financial services can benefit from identity management solutions.
Rent-a-DPO for IT Vendors

GDPR offers chances to enhance trust in your organisation, by showing that data is safe with you. Chances to show you take social responsibility, transparency and privacy seriously. Chances to minimise the risks of identity fraud and data leaks.
We can help you with our pragmatic approach from our expertise in information security, processes and privacy law.
Do you want to be ready for GDPR on May 25th, 2018? Call or mail me.
r.kranendonk@rent-a-dpo.nl
+31 (0) 30 227 0960
+31 (0) 6 286 388 46
Healthcare Patient Experiences Matter

Join your patient's journey and see critical touch points that impact revenue. These stats prove superb patient experiences move business forward.
Data Sheet: Gigya Customer Identity Management Platform Tiers

Gigya’s Customer Identity Management Platform
Case Study: Multi-Billion Dollar Enterprise - Managing Millions of Identities...

With dozens of different web properties spread across a number of international territories, a multi-billion dollar company was in need of a solution to better manage its customer identities and data at a global scale. The solution had to be scalable and flexible, offer robust administrative roles and permissions and keep the brand compliant with regional data privacy regulations.
Data Sheet: Why Loyalty

Gigya’s Loyalty package offers a suite of gamification tools that make it easy to develop custom gamification strategies, recognize and reward users and track and measure results.
Data Sheet: Gigya for the IT Buyer

Gigya’s Customer Identity Management Platform offers a more intelligent and efficient way to collect and organize your customer data, so you can make better informed decisions and maximize the value of your data.
Case Study: Nutricia-Danone

In light of high demands for its formula product, Nutricia-Danone realized that the only way to effectively retain and service its customers and protect its market share was to properly identify buyers.
Nutricia-Danone implemented Gigya’s Registration-as-a-Service (RaaS) and Social Login across Nutricia web properties, including formula vending machines located throughout the Netherlands, bringing legacy technology into the world of connected devices and the Internet of Things.
More Related Content
What's hot
Winning with GDPR: How to Win Customer Loyalty and Trust

New research by ForgeRock and MyCustomer has revealed that customer trust, and their willingness to share data, is being harmed by the poor quality of digital experiences. So how can your organisation break this cycle? Customer Insights Expert, Paul Laughlin and Doug Norton-Bilsby, Global VP of Retail and Consumer Products at ForgeRock discuss.
2016 04-26 webinar - consumer-focused identity management

identity and cloud cybersecurity today mean a lot more than has traditionally been understood in these technology disciplines. we will see how the technological and legal shifts that have taken place have major implications not just for IAM and cybersecurity, but also for the discipline traditionally known as customer relationship management, or CRM.
Ping Identity: Corporate Overview Financial Services

From Denver based identity and access management vendor Ping Identity comes this presentation explaining how financial services can benefit from identity management solutions.
Rent-a-DPO for IT Vendors

GDPR offers chances to enhance trust in your organisation, by showing that data is safe with you. Chances to show you take social responsibility, transparency and privacy seriously. Chances to minimise the risks of identity fraud and data leaks.
We can help you with our pragmatic approach from our expertise in information security, processes and privacy law.
Do you want to be ready for GDPR on May 25th, 2018? Call or mail me.
r.kranendonk@rent-a-dpo.nl
+31 (0) 30 227 0960
+31 (0) 6 286 388 46
Healthcare Patient Experiences Matter

Join your patient's journey and see critical touch points that impact revenue. These stats prove superb patient experiences move business forward.
What's hot (9)
Winning with GDPR: How to Win Customer Loyalty and Trust

Winning with GDPR: How to Win Customer Loyalty and Trust
2016 04-26 webinar - consumer-focused identity management

2016 04-26 webinar - consumer-focused identity management
Ping Identity: Corporate Overview Financial Services

Ping Identity: Corporate Overview Financial Services
Similar to Data Sheet: Corporate Overview
Data Sheet: Gigya Customer Identity Management Platform Tiers

Gigya’s Customer Identity Management Platform
Case Study: Multi-Billion Dollar Enterprise - Managing Millions of Identities...

With dozens of different web properties spread across a number of international territories, a multi-billion dollar company was in need of a solution to better manage its customer identities and data at a global scale. The solution had to be scalable and flexible, offer robust administrative roles and permissions and keep the brand compliant with regional data privacy regulations.
Data Sheet: Why Loyalty

Gigya’s Loyalty package offers a suite of gamification tools that make it easy to develop custom gamification strategies, recognize and reward users and track and measure results.
Data Sheet: Gigya for the IT Buyer

Gigya’s Customer Identity Management Platform offers a more intelligent and efficient way to collect and organize your customer data, so you can make better informed decisions and maximize the value of your data.
Case Study: Nutricia-Danone

In light of high demands for its formula product, Nutricia-Danone realized that the only way to effectively retain and service its customers and protect its market share was to properly identify buyers.
Nutricia-Danone implemented Gigya’s Registration-as-a-Service (RaaS) and Social Login across Nutricia web properties, including formula vending machines located throughout the Netherlands, bringing legacy technology into the world of connected devices and the Internet of Things.
Case Study: ESI Uses First-Party Data to Drive Ad Revenue with Gigya

As digital ad inventory increased in volume and decreased in value, ESI Media saw the opportunity to grow ad revenue and gain a competitive advantage by offering segmented audience targeting. Using Gigya's RaaS and Profile Management, ESI was able to capture rich first-party user data to effectively understand and segment its users, resulting in:
- 30% increase in registrations
- 300% increase in CTR
- 2X campaign yields
Case Study: DC Thomson Media Creates a Single Customer View Across Multiple D...

DC Thomson Media, or DCT Media, chose Gigya as their customer identity provider, resulting in a 5X increase in new registrations and a 16% increase in pageviews.
Data Sheet: Why Your DMP Needs CIAM

A specialized customer identity and access management (CIAM) solution can maximize the potential of your DMP platform. Enable more relevant experiences across every touchpoint by implementing:
- Flexible registration and social login
- Customer-focused profile management
- Pre-built integrations with today's top revenue-driving technologies
Similar to Data Sheet: Corporate Overview (20)
Data Sheet: Gigya Customer Identity Management Platform Tiers

Data Sheet: Gigya Customer Identity Management Platform Tiers
Case Study: Multi-Billion Dollar Enterprise - Managing Millions of Identities...

Case Study: Multi-Billion Dollar Enterprise - Managing Millions of Identities...
Case Study: ESI Uses First-Party Data to Drive Ad Revenue with Gigya

Case Study: ESI Uses First-Party Data to Drive Ad Revenue with Gigya
Case Study: DC Thomson Media Creates a Single Customer View Across Multiple D...

Case Study: DC Thomson Media Creates a Single Customer View Across Multiple D...
More from Gigya
Case Study: STV Boosts Viewer Engagement and Campaign Yields with Gigya

Scottish Television, or STV, implemented Gigya's Customer Identity Management platform to enable viewers to register for accounts with minimal information, resulting in increased open and click-through rates, as well as better ad retargeting performance.
Some highlights include:
- Improved open rates by 14.5%
- Improved Click-through rates by 21.4%
- Went live in less than 6 months
White Paper: Gigya's Information Security and Data Privacy Practices

As the leading SaaS Customer Identity and Access Management provider for enterprises, Gigya is committed to maintaining a high level of performance and security Our platform is optimized for maximum e ciency and scalability while protecting our clients’ data by adhering to strict security and compliance standards This document provides an overview of Gigya’s standards for the following four categories: Infrastructure, Data Security, Compliance, and Privacy Policies.
Gigya und die Erfüllung globaler behördlicher Auflagen (Global Regulatory Com...

In unserer modernen datengesteuerten Welt wird es für Unternehmen immer schwieriger, die richtige Balance zwischen Personalisierung und Datenschutz zu verwirklichen.
Gigya's China Data Center - Data Sheet

New China Data Center Helps Gigya’s Clients Manage Compliance with New Chinese Cybersecurity Law.
As businesses expand into new markets to grow their customer bases through digital initiatives, compliance with widely variable data protection and privacy regulations is now one of the key competitive differentiators between industry leaders
and losers.
The Chutes and Ladders of Customer Identity

Cross-channel digital marketing today can feel like a game of chutes and ladders, with opportunities and risk at every turn. To win, businesses should build customer profiles progressively, leveraging a mature customer identity management solution to ensure that they can:
- Ask for and manage customers’ consent throughout their entire lifecycle
- Take advantage of features such as lite registration and subscription management to seamlessly engage customers earlier in the buyer journey
- Offer customers real value in exchange for their information
Build transparency into the framework of their digital strategy to build trust with customers
- Reward customers by offering continual value and incentivizing them to engage more often to drive long-term loyalty and advocacy
White Paper: DIY vs CIAM

Digital innovation being demanded by every business unit is transforming IT’s role to that of the main driver of new growth initiatives, prompting a shift in perspective and strategy for CIOs that begins with a well-planned and executed approach to managing customer identities. While legacy IAM might seem like a natural starting point for meeting this challenge, customer identity and access management (CIAM) has significantly different requirements and outcomes when compared to employee-facing IAM.
Data Sheet: Gigya and Global Regulatory Compliance

Gigya’s Customer Identity Management platform offers features that provide maximum flexibility for building
customer consent and control into every step of the customer journey, as well as support for meeting a wide
range of regional privacy requirements. Notably, the European Union’s General Data Protection Regulation
(GDPR) comes into effect on May 25, 2018, carrying potential penalties of up to the greater of €20,000,000 or
4% of total annual global turnover.
The following data sheet illustrates how Gigya’s platform enables data privacy and compliance for our 700 clients.
White Paper: 2017 Predictions - French

2016 a été une année décisive en
matière de Gestion des identités clients
(CIM - Customer Identity Management)
et les entreprises, la presse et les
analystes se sont accordés à dire que
la technologie CIM n’était plus une «
bonne chose » au sein des entreprises
actuelles, mais un impératif.
White Paper: 2017 Predictions - German

Als die Identität der Verbraucher in vollem Gange ist, hat Gigya fünf Vorhersagen für die wichtigsten Trends, die wir sehen, wachsen im Jahr 2017 gelegt, und wie wir sehen, dass Organisationen reagieren.
Case study - American Kennel Club

American Kennel Club (AKC) understood they needed a registration system, but after attempting to build their own, and some significant challenges in time and effort, AKC effectively sought to implement Gigya's Customer Identity Management Platform.
In this case study, Steve Pessah, Sr. Product Manager at American Kennel Club, discusses how Gigya has helped AKC:
- Improve registration conversion rates by 75%
- Increase value per user by 35%
- Saved 12 months of development time for AKC
Gigya Infographic - Death Of A Password

Consumers now expect more trusted and personalized experiences in exchange for their personal information, but businesses are struggling to protect user privacy in light of growing global security and privacy concerns. Since tolerance is diminishing for username and password processes, today’s businesses must find new ways to secure users' data while delivering better customer experiences.
GDPR Implications Customer Identity Management - German

The upcoming General Data Protection Regulation (EU GDPR) will change the requirements for managing consumers’ personal data across the globe. The regulation’s scope is broad and also affects organizations outside of the EU. Striking a balance between meeting the new regulatory requirements and effectively serving customers in the age of Digital Transformation mandates a shift from siloed consumer data management to centralized Customer Identity Management platforms that support the balance between compliance, user consent, and optimizing the customer experience.
In this white paper — commissioned by Gigya from European analyst firm KuppingerCole and prepared by Fellow Analyst Dr. Karsten Kinast and Lead Analyst Ivan Niccolai — you will learn about:
*The history, framework, implementation and scope of the EU GDPR
*Key compliance elements of the EU GDPR
*The implications of the EU GDPR on Customer Identity Management and best-practice recommendations for strategy and implementation
White Paper: Managing consumer data privacy with Gigya (French)

White Paper: Managing consumer data privacy with Gigya French
Managing Consumer Data Privacy

For today’s digital businesses, being prepared to meet new compliance requirements when storing and managing consumer data will not only minimize risk, but also enable more valued and trusted customer experiences that drive increased loyalty, engagement and revenue. To gain better perspective on this important issue, it’s important to understand:
- The trends driving governmental regulatory shifts and the basic tenets of these new laws
- The challenges faced by executives across the enterprise when managing privacy compliance for consumer data
- The emergence of cloud-based solutions that help businesses manage privacy compliance by acting as end-to-end customer data storage and management solutions that are far more scalable and flexible than legacy systems
Information Security and Data Privacy Practices

Gigya’s enterprise class Customer Identity & Access Management platform delivers maximum efficiency and scalability while protecting consumer data with strict security and compliance standards. The four pillars of Gigya’s security and privacy promise are:
- Infrastructure: State-of-the-art data centers for optimized performance and scalability.
- Data Security: ISO 27001 certification and multiple levels of security protect data with both physical and virtual safeguards.
- Compliance: Regional privacy compliance and built in social network terms of service functionality ensure responsible data management.
- Privacy Policies: Increased transparency of data practices fosters consumer trust and relationships.
Russian Data Center

Russia’s new Personal Data Protection Act stipulates that companies with Russian customers must store those users’ personal data within Russian borders. To ensure that all of our clients doing business in Russia can continue to do so safely, Gigya has opened a new primary data center in Russia.
White Paper: 5 Ways Airports Can Drive Non-Aviation Revenue

With airlines now accounting for just 38% of airport revenues, maximizing non-aviation earnings has never been more necessary. This white paper takes a look at how airports can drive non-aviation revenue by leveraging customer identities to create personal experiences across five key areas:
- Parking
- Retail and concessions
- Food and beverage
- Loyalty programs
- Advertising
Case Study: Unibail-Rodamco Creates a Connected, Personalized Shopping Experi...

After conducting a customer survey, Unibail-Rodamco determined that providing shoppers with personalized experiences across malls was key to its future success. By leveraging a Customer Identity Management solution to understand its shoppers' tastes and preferences, Unibail-Rodamco was able to see:
- 26% increase in registration rates
- 92% growth in loyalty card subscriptions
- 76% of registrants connecting socially
- 35x increase in mobile registrations
More from Gigya (20)
Case Study: STV Boosts Viewer Engagement and Campaign Yields with Gigya

Case Study: STV Boosts Viewer Engagement and Campaign Yields with Gigya
White Paper: Gigya's Information Security and Data Privacy Practices

White Paper: Gigya's Information Security and Data Privacy Practices
Gigya und die Erfüllung globaler behördlicher Auflagen (Global Regulatory Com...

Gigya und die Erfüllung globaler behördlicher Auflagen (Global Regulatory Com...
Data Sheet: Gigya and Global Regulatory Compliance

Data Sheet: Gigya and Global Regulatory Compliance
GDPR Implications Customer Identity Management - German

GDPR Implications Customer Identity Management - German
White Paper: Managing consumer data privacy with Gigya (German)

White Paper: Managing consumer data privacy with Gigya (German)
White Paper: Managing consumer data privacy with Gigya (French)

White Paper: Managing consumer data privacy with Gigya (French)
White Paper: 5 Ways Airports Can Drive Non-Aviation Revenue

White Paper: 5 Ways Airports Can Drive Non-Aviation Revenue
Case Study: Unibail-Rodamco Creates a Connected, Personalized Shopping Experi...

Case Study: Unibail-Rodamco Creates a Connected, Personalized Shopping Experi...
Recently uploaded
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Recently uploaded (20)
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Data Sheet: Corporate Overview
- 1. DATA SHEET Gigya helps 700+ companies build trusted digital relationships with more than 1.2 billion consumers. Gigya’s platform enables businesses to identify and engage customers across devices; consolidate data into rich, privacy-compliant customer profiles, and integrate data into marketing and service applications to provide better services, products and experiences. Gigya by the Numbers Platform Gigya’s Customer Identity Management Platform helps businesses build better customer relationships by turning unknown site visitors into known, loyal and engaged customers. Gigya’s platform is available across three distinct tiers, with additional packages available for subscription management, loyalty, social engagement, data integration and services and support. Clients More than 700 of the world’s leading businesses including Fox, Forbes and Verizon choose Gigya. Gigya’s client base spans the globe and a variety of industries including eCommerce, media, publishing, travel and consumer goods. Gigya: The Leader in Customer Identity Management GIGYA’S CUSTOMER IDENTITY MANAGEMENT PLATFORM • 300+ employees • More than 700 clients • 70+ partnerships & integrations • Technology deployed in 46 countries • 1.2B registered customers • 4.8B devices COLLECT Profile, Preference and Privacy Management CONNECT Registration-as-a-Service, Authentication and Federation CONVERT Customer Insights, ETL and Identity Exchange Platform
- 2. © 2017 Gigya, Inc. | 2513 Charleston Road #200, Mountain View, CA 94043 | T : (650) 353.7230 | www.gigya.com Gigya, the Gigya logo, and Customer Identity Management Platform are either registered trademarks or trademarks of Gigya Incorporated in the United States and/or other countries. All other trademarks are the property of their respective owners. Gigya does not own any end user data or maintain any other rights to this data, other than utilizing it to make Gigya’s services available to our clients and their end users. Gigya acts as an agent or back-end vendor of its client’s website or mobile application, to which the end user of our client granted permissions (if applicable). Gigya facilitates the collection, transfer and storage of end user data solely on behalf of its clients and at its clients’ direction. For more information, please see Gigya’s Privacy Policy, available at http://www.gigya.com/privacy-policy/. Gigya_Data_Sheet_Corporate Overview_201701 Partners Composed of more than 70 industry-leading companies, the Gigya Partner Program is designed to help joint clients deliver better products, better services, and better marketing by integrating customer identity information into sales, service and marketing applications. Investors Gigya has raised more than $100M in capital from several leading firms including Benchmark Capital, DAG Ventures, First Round Capital, Greenspring Associates, Intel Capital, Mayfield, Adobe and Vintage Investment Partners. Leadership Gigya’s executive team brings over 200 years of collective experience innovating in the areas of digital marketing, privacy and security. • Patrick Salyer, CEO • Rooly Eliezerov, Co-founder and President • Eyal Magen, Co-founder and Chief Strategy Officer • Eran Kutner, Co-founder and CTO • J.F. Hervy, CFO • Gilad Sofer, CISO • Ben Jackson, SVP, Worldwide Sales • Marc Troyan, SVP, Customer Success • Patrick McCue, SVP, Global Channels & Alliances • Jason Rose, SVP, Marketing WITH MORE THAN 2.5 MILLION VOLUNTEERS AND MILLIONS OF DONORS, WE SAW GIGYA AS THE LOGICAL CHOICE FOR A STABLE AND EFFECTIVE IDENTITY MANAGEMENT SOLUTION. Jay Ferro Chief Information Officer American Cancer Society Offices Mountain View (Headquarters) 2513 E. Charleston Road Mountain View, CA 94043 Tel Aviv 132 Begin Road Azrieli Towers (Triangle) 43rd Floor Tel Aviv, Israel 67021 London 6 Ramillies Street Soho London W1F 7TY
