Case Study: DC Thomson Media Creates a Single Customer View Across Multiple Domains
•
2 likes•892 views
DC Thomson Media, or DCT Media, chose Gigya as their customer identity provider, resulting in a 5X increase in new registrations and a 16% increase in pageviews.
Report
Share
Report
Share
Download to read offline
Recommended
Case Study: STV Boosts Viewer Engagement and Campaign Yields with Gigya

Scottish Television, or STV, implemented Gigya's Customer Identity Management platform to enable viewers to register for accounts with minimal information, resulting in increased open and click-through rates, as well as better ad retargeting performance.
Some highlights include:
- Improved open rates by 14.5%
- Improved Click-through rates by 21.4%
- Went live in less than 6 months
White Paper: The Evolution of Consumer Identity - Five Predictions for 2016

2016 promises to be a year of enhanced development in the customer identity and access management (CIAM) space, with customer experience, data privacy and personalization proving to be increasingly critical components of business success. This white paper reveals five identity-related trends we foresee taking hold in the new year, including:
- The death of traditional usernames and passwords
- The decline of data broker revenues
- The convergence of security and customer experience
White Paper: Bridging the Gap between Marketing & IT with Customer Identity &...

As customer data and digital experiences become the linchpins of business success, there is an unprecedented need for marketing and IT to come together. Bridging this gap requires a solution that addresses the needs and concerns of both marketing and IT while presenting opportunities for joint departmental and business growth. We'll take a look at three marketing and IT conflicts and how customer identity and access management (CIAM) provides a highly collaborative and effective solution.
White Paper: The 2015 State of Consumer Privacy & Personalization

This year’s survey results illustrate increased growth and intensity in consumer desire for data privacy and personalized user experiences. While social login usage continues to skyrocket, consumers are also showing a marked interest in next-generation authentication methods, including payment providers and biometrics, indicating a clear evolution of the concept of digital identity: Identity 3.0.
White Paper: Internal vs. External Identity Access Management 

Customer identity and access management (CIAM)
White Paper: Don't Let Your Corporate Strategy be Hostage to Your IT Strategy

Digital innovation being demanded by every business unit is transforming IT’s role to that of the main driver of new growth initiatives, prompting a shift in perspective and strategy for CIOs that begins with a well-planned and executed approach to managing customer identities. While legacy IAM might seem like a natural starting point for meeting this challenge, customer identity and access management (CIAM) has significantly different requirements and outcomes when compared to employee-facing IAM.
Recommended
Case Study: STV Boosts Viewer Engagement and Campaign Yields with Gigya

Scottish Television, or STV, implemented Gigya's Customer Identity Management platform to enable viewers to register for accounts with minimal information, resulting in increased open and click-through rates, as well as better ad retargeting performance.
Some highlights include:
- Improved open rates by 14.5%
- Improved Click-through rates by 21.4%
- Went live in less than 6 months
White Paper: The Evolution of Consumer Identity - Five Predictions for 2016

2016 promises to be a year of enhanced development in the customer identity and access management (CIAM) space, with customer experience, data privacy and personalization proving to be increasingly critical components of business success. This white paper reveals five identity-related trends we foresee taking hold in the new year, including:
- The death of traditional usernames and passwords
- The decline of data broker revenues
- The convergence of security and customer experience
White Paper: Bridging the Gap between Marketing & IT with Customer Identity &...

As customer data and digital experiences become the linchpins of business success, there is an unprecedented need for marketing and IT to come together. Bridging this gap requires a solution that addresses the needs and concerns of both marketing and IT while presenting opportunities for joint departmental and business growth. We'll take a look at three marketing and IT conflicts and how customer identity and access management (CIAM) provides a highly collaborative and effective solution.
White Paper: The 2015 State of Consumer Privacy & Personalization

This year’s survey results illustrate increased growth and intensity in consumer desire for data privacy and personalized user experiences. While social login usage continues to skyrocket, consumers are also showing a marked interest in next-generation authentication methods, including payment providers and biometrics, indicating a clear evolution of the concept of digital identity: Identity 3.0.
White Paper: Internal vs. External Identity Access Management 

Customer identity and access management (CIAM)
White Paper: Don't Let Your Corporate Strategy be Hostage to Your IT Strategy

Digital innovation being demanded by every business unit is transforming IT’s role to that of the main driver of new growth initiatives, prompting a shift in perspective and strategy for CIOs that begins with a well-planned and executed approach to managing customer identities. While legacy IAM might seem like a natural starting point for meeting this challenge, customer identity and access management (CIAM) has significantly different requirements and outcomes when compared to employee-facing IAM.
White Paper: Achieving A Single Customer View: The Holy Grail for Marketers

This guide provides actionable strategies for how your business can achieve a single customer view to better understand your audience and build meaningful, identity-driven customer relationships.
Privacy 2.0: Building a Winning Mobile Strategy in a Privacy-first World

In this webinar, our privacy experts partner with marketing analytics and attribution experts, Singular, to talk about channel diversification and building a trove of first-party data to create a winning mobile channel strategy in the age of privacy.
Mobile and Loyalty Programs - The Hyper Digital Age: Accelerating customer bo...

Thanks to the fast-paced growth of connected devices such as smartphones and tablets, brands have never before had so much data available to define an individual customer's feelings, needs and emotions. By capturing this behavioural data, brands can build useful intelligence. For loyalty programs, the opportunity is in making truly contextually relevant approaches, driving real value to customers.
Chatbots are Changing Customer Service

Businesses are starting to see the benefits of using chatbots for their customer-facing services.
Data Sheet: Why CPG Companies Need CIAM

A true customer identity and access management (CIAM)
solution allows CPG companies to easily manage multiple
brands in various countries, providing the ability to identify
customers and reconcile all data types into complete user
profiles across channels and brands. This data can be
leveraged to build relevant campaigns and experiences that
create value beyond cost savings to maximize acquisition,
conversions and loyalty.
Connect, Collect, Convert

To be successful today, businesses must leverage consumer data to enable great customer experiences. Doing this in a seamless and compliant way is not easy, with a shifting regulatory landscape, numerous identity providers and front-end technologies to support. Gigya's end-to-end Customer Identity Management platform helps businesses succeed by providing:
*Flexible registration and authentication to connect you with your customers
*Profile and preference management to collect all data types into unified and compliant profiles
*Powerful customer insights tools and easy integration with virtually any third-party technology
Innovative Internet & Digital marketing 

This presentation was given on 24th Aug at MCCIA Pune event. It discusses how search engine works, SEO and SMO. How one can engage with web site visitors.
What's Next: Social Media Trends 2020 

Despite the debates around privacy, disinformation and influencer authenticity; social media continues to fuel our digital lives. The biggest change is how. With ever evolving platforms, trends, and even content types, social is growing increasingly complex and discerning fact from fiction is becoming progressively more difficult. What will be the biggest trends for marketers in 2020? Chris Walts, Social Strategy Lead at Ogilvy UK, and Kanika Bali, Social Strategist at Ogilvy Hong Kong share their insights.
Apple Vs. Facebook – Who Will Win The Data Privacy War?

Apple and Facebook are taking very different approaches towards user privacy and transparency. In this article, we discuss these and explore which approach will more likely to win in the long run.
Video Advertising Services

3Di offer two distinct video advertising options. A pre-roll video ad network and a "direct response" video adverting product.
The Data Dilemma: How Can Consumers Trust Brands with Personal Information

As brands collect more data, consumers are understandably concerned about how their personal information will be used. In this POV, we discuss how brands can deliver real value in exchange for data, and the keys to increasing trust.
Why entertainment companies get into Bollywood Quiz based gaming

Future of Bollywood based gaming for a entertainment company having web/wap/app on Bollywood stories.
Impact of Bollywood Gaming in Entertainment Media

Entertainment industry stats, Bollywood Gaming Future and game rules.
Me Data - The Rising Opportunity for Self Optimization Apps 

A new research study from creative digital agency Beyond, shows that the lack of concern over the privacy of Me Data - open, freely available, personal data - and the popularity of personal tracking apps is leading to a demand in self-optimization services like Google Now. These products and services will break out of the niches created by personal tracking apps, instead offering overall lifestyle self-optimization services based on several different strands of Me Data.
What are Emerging Mobile Data Platforms

Data is going to be central to the way a company markets its products in the future. This presentation describes the different categories of Mobile data platforms and their advantages.
2019 trends

By all accounts, 2019 will be the year marketers (finally!) get serious about customer experience (CX). Defined by BusinessDictionary.com as “the entirety of the interactions a
customer has with a company and its products,” CX has long been a hot topic, and in our age of endless distractions, an aspect of customer relationship management (or CRM)
that businesses can’t afford to get wrong. Armed with intelligent technologies capable of delivering the highest levels of customization and personalization, brands and their
partners will place big bets on CX – and its impact on driving conversions – in the year to
come.
Now onto a handful of the trends we’ve been tracking, in no particular order
How Will Blockchain Transform Digital Signage Advertising?

Read the full blog here: https://bit.ly/3nEPaOO
Connect with us through:
Contact us : https://bit.ly/2IpPX7w
Facebook : https://www.facebook.com/PixelCrayons
Twitter : https://twitter.com/pixelcrayons
LinkedIn : https://www.linkedin.com/company/pixelcrayons
Instagram : https://www.instagram.com/pixelcrayons/
Pinterest : https://in.pinterest.com/pixelcrayons/
Tomorrow's Data Heros

Telecom companies are struggling to find a profitable identity in today’s digital sphere. What about helping customers control their information?
Data Sheet: Why Your DMP Needs CIAM

A specialized customer identity and access management (CIAM) solution can maximize the potential of your DMP platform. Enable more relevant experiences across every touchpoint by implementing:
- Flexible registration and social login
- Customer-focused profile management
- Pre-built integrations with today's top revenue-driving technologies
More Related Content
What's hot
White Paper: Achieving A Single Customer View: The Holy Grail for Marketers

This guide provides actionable strategies for how your business can achieve a single customer view to better understand your audience and build meaningful, identity-driven customer relationships.
Privacy 2.0: Building a Winning Mobile Strategy in a Privacy-first World

In this webinar, our privacy experts partner with marketing analytics and attribution experts, Singular, to talk about channel diversification and building a trove of first-party data to create a winning mobile channel strategy in the age of privacy.
Mobile and Loyalty Programs - The Hyper Digital Age: Accelerating customer bo...

Thanks to the fast-paced growth of connected devices such as smartphones and tablets, brands have never before had so much data available to define an individual customer's feelings, needs and emotions. By capturing this behavioural data, brands can build useful intelligence. For loyalty programs, the opportunity is in making truly contextually relevant approaches, driving real value to customers.
Chatbots are Changing Customer Service

Businesses are starting to see the benefits of using chatbots for their customer-facing services.
Data Sheet: Why CPG Companies Need CIAM

A true customer identity and access management (CIAM)
solution allows CPG companies to easily manage multiple
brands in various countries, providing the ability to identify
customers and reconcile all data types into complete user
profiles across channels and brands. This data can be
leveraged to build relevant campaigns and experiences that
create value beyond cost savings to maximize acquisition,
conversions and loyalty.
Connect, Collect, Convert

To be successful today, businesses must leverage consumer data to enable great customer experiences. Doing this in a seamless and compliant way is not easy, with a shifting regulatory landscape, numerous identity providers and front-end technologies to support. Gigya's end-to-end Customer Identity Management platform helps businesses succeed by providing:
*Flexible registration and authentication to connect you with your customers
*Profile and preference management to collect all data types into unified and compliant profiles
*Powerful customer insights tools and easy integration with virtually any third-party technology
Innovative Internet & Digital marketing 

This presentation was given on 24th Aug at MCCIA Pune event. It discusses how search engine works, SEO and SMO. How one can engage with web site visitors.
What's Next: Social Media Trends 2020 

Despite the debates around privacy, disinformation and influencer authenticity; social media continues to fuel our digital lives. The biggest change is how. With ever evolving platforms, trends, and even content types, social is growing increasingly complex and discerning fact from fiction is becoming progressively more difficult. What will be the biggest trends for marketers in 2020? Chris Walts, Social Strategy Lead at Ogilvy UK, and Kanika Bali, Social Strategist at Ogilvy Hong Kong share their insights.
Apple Vs. Facebook – Who Will Win The Data Privacy War?

Apple and Facebook are taking very different approaches towards user privacy and transparency. In this article, we discuss these and explore which approach will more likely to win in the long run.
Video Advertising Services

3Di offer two distinct video advertising options. A pre-roll video ad network and a "direct response" video adverting product.
The Data Dilemma: How Can Consumers Trust Brands with Personal Information

As brands collect more data, consumers are understandably concerned about how their personal information will be used. In this POV, we discuss how brands can deliver real value in exchange for data, and the keys to increasing trust.
Why entertainment companies get into Bollywood Quiz based gaming

Future of Bollywood based gaming for a entertainment company having web/wap/app on Bollywood stories.
Impact of Bollywood Gaming in Entertainment Media

Entertainment industry stats, Bollywood Gaming Future and game rules.
Me Data - The Rising Opportunity for Self Optimization Apps 

A new research study from creative digital agency Beyond, shows that the lack of concern over the privacy of Me Data - open, freely available, personal data - and the popularity of personal tracking apps is leading to a demand in self-optimization services like Google Now. These products and services will break out of the niches created by personal tracking apps, instead offering overall lifestyle self-optimization services based on several different strands of Me Data.
What are Emerging Mobile Data Platforms

Data is going to be central to the way a company markets its products in the future. This presentation describes the different categories of Mobile data platforms and their advantages.
2019 trends

By all accounts, 2019 will be the year marketers (finally!) get serious about customer experience (CX). Defined by BusinessDictionary.com as “the entirety of the interactions a
customer has with a company and its products,” CX has long been a hot topic, and in our age of endless distractions, an aspect of customer relationship management (or CRM)
that businesses can’t afford to get wrong. Armed with intelligent technologies capable of delivering the highest levels of customization and personalization, brands and their
partners will place big bets on CX – and its impact on driving conversions – in the year to
come.
Now onto a handful of the trends we’ve been tracking, in no particular order
How Will Blockchain Transform Digital Signage Advertising?

Read the full blog here: https://bit.ly/3nEPaOO
Connect with us through:
Contact us : https://bit.ly/2IpPX7w
Facebook : https://www.facebook.com/PixelCrayons
Twitter : https://twitter.com/pixelcrayons
LinkedIn : https://www.linkedin.com/company/pixelcrayons
Instagram : https://www.instagram.com/pixelcrayons/
Pinterest : https://in.pinterest.com/pixelcrayons/
Tomorrow's Data Heros

Telecom companies are struggling to find a profitable identity in today’s digital sphere. What about helping customers control their information?
What's hot (20)
White Paper: Achieving A Single Customer View: The Holy Grail for Marketers

White Paper: Achieving A Single Customer View: The Holy Grail for Marketers
Privacy 2.0: Building a Winning Mobile Strategy in a Privacy-first World

Privacy 2.0: Building a Winning Mobile Strategy in a Privacy-first World
Mobile and Loyalty Programs - The Hyper Digital Age: Accelerating customer bo...

Mobile and Loyalty Programs - The Hyper Digital Age: Accelerating customer bo...
Apple Vs. Facebook – Who Will Win The Data Privacy War?

Apple Vs. Facebook – Who Will Win The Data Privacy War?
The Data Dilemma: How Can Consumers Trust Brands with Personal Information

The Data Dilemma: How Can Consumers Trust Brands with Personal Information
Why entertainment companies get into Bollywood Quiz based gaming

Why entertainment companies get into Bollywood Quiz based gaming
Me Data - The Rising Opportunity for Self Optimization Apps 

Me Data - The Rising Opportunity for Self Optimization Apps
How Will Blockchain Transform Digital Signage Advertising?

How Will Blockchain Transform Digital Signage Advertising?
Similar to Case Study: DC Thomson Media Creates a Single Customer View Across Multiple Domains
Data Sheet: Why Your DMP Needs CIAM

A specialized customer identity and access management (CIAM) solution can maximize the potential of your DMP platform. Enable more relevant experiences across every touchpoint by implementing:
- Flexible registration and social login
- Customer-focused profile management
- Pre-built integrations with today's top revenue-driving technologies
Internal vs. external identity access management

Strategies to develop an end-to-end customer data management framework.
Data Sheet: Why Your eCommerce Platform Needs CIAM

A specialized customer identity and access management (CIAM) solution can maximize the potential of your eCommerce platform, allowing you to deliver more relevant experiences across every touchpoint by enabling:
- Flexible registration and social login
- Customer-focused profile management
- Pre-built integrations with today's top revenue-driving technologies
Case Study: ESI Uses First-Party Data to Drive Ad Revenue with Gigya

As digital ad inventory increased in volume and decreased in value, ESI Media saw the opportunity to grow ad revenue and gain a competitive advantage by offering segmented audience targeting. Using Gigya's RaaS and Profile Management, ESI was able to capture rich first-party user data to effectively understand and segment its users, resulting in:
- 30% increase in registrations
- 300% increase in CTR
- 2X campaign yields
Case Study: Multi-Billion Dollar Enterprise - Managing Millions of Identities...

With dozens of different web properties spread across a number of international territories, a multi-billion dollar company was in need of a solution to better manage its customer identities and data at a global scale. The solution had to be scalable and flexible, offer robust administrative roles and permissions and keep the brand compliant with regional data privacy regulations.
Data Sheet: Gigya Customer Identity Management Platform Tiers

Gigya’s Customer Identity Management Platform
Data Sheet: IAM vs. CIAM: A Simple Choice

Managing self-provisioned profiles and customer-generated
data within legacy IAM has proven overwhelming and costly. A cloud-based Customer Identity and Access Management (cIAM) platform can meet this challenge while helping your business extract maximum value from customer data.
Gigya and Marketo

Get Better Results with Identity-Driven Marketing Automation
Gigya’s pre-built integration fuels Marketo's marketing automation software with rich first-party identity data. With Gigya and Marketo, brands can:
*Sync any data points between Gigya’s Profile Management and Marketo
*Set updates to ensure that you’re always working with accurate user data
*Build timely and relevant campaigns that foster valuable, lifetime relationships with your customers
Keynote: Data Strategy: Starts with First-Party Data

May 3, 2019 - 09:00 AM: Learn how Dell shifted its focus back to their most valuable marketing asset, first-party CRM data, to enable personalized cross-channel customer experiences and deliver business results. Keynote Jeremy Parker, Global DMP Audience Manager, Dell
Data Sheet: Corporate Overview

An overview of Gigya's platform, history and leadership, clients, partners and investors.
Case Study: Frontier Communications

Gigya’s Registration-as-a-Service (RaaS) provides Frontier Communications with the flexibility to quickly deploy custom registration forms and flows across its web and mobile properties, complete with identity validation and verification policies. All data collected through registration and known users’ on-site actions is organized into unified profiles in Gigya’s Profile Management database, which serves as a single source of truth across properties. Profile Management automatically maintains data privacy compliance, protection and quality.
Similar to Case Study: DC Thomson Media Creates a Single Customer View Across Multiple Domains (20)
Data Sheet: Why Your eCommerce Platform Needs CIAM

Data Sheet: Why Your eCommerce Platform Needs CIAM
Case Study: ESI Uses First-Party Data to Drive Ad Revenue with Gigya

Case Study: ESI Uses First-Party Data to Drive Ad Revenue with Gigya
Case Study: Multi-Billion Dollar Enterprise - Managing Millions of Identities...

Case Study: Multi-Billion Dollar Enterprise - Managing Millions of Identities...
Data Sheet: Gigya Customer Identity Management Platform Tiers

Data Sheet: Gigya Customer Identity Management Platform Tiers
Keynote: Data Strategy: Starts with First-Party Data

Keynote: Data Strategy: Starts with First-Party Data
More from Gigya
White Paper: Gigya's Information Security and Data Privacy Practices

As the leading SaaS Customer Identity and Access Management provider for enterprises, Gigya is committed to maintaining a high level of performance and security Our platform is optimized for maximum e ciency and scalability while protecting our clients’ data by adhering to strict security and compliance standards This document provides an overview of Gigya’s standards for the following four categories: Infrastructure, Data Security, Compliance, and Privacy Policies.
Gigya und die Erfüllung globaler behördlicher Auflagen (Global Regulatory Com...

In unserer modernen datengesteuerten Welt wird es für Unternehmen immer schwieriger, die richtige Balance zwischen Personalisierung und Datenschutz zu verwirklichen.
Gigya's China Data Center - Data Sheet

New China Data Center Helps Gigya’s Clients Manage Compliance with New Chinese Cybersecurity Law.
As businesses expand into new markets to grow their customer bases through digital initiatives, compliance with widely variable data protection and privacy regulations is now one of the key competitive differentiators between industry leaders
and losers.
The Chutes and Ladders of Customer Identity

Cross-channel digital marketing today can feel like a game of chutes and ladders, with opportunities and risk at every turn. To win, businesses should build customer profiles progressively, leveraging a mature customer identity management solution to ensure that they can:
- Ask for and manage customers’ consent throughout their entire lifecycle
- Take advantage of features such as lite registration and subscription management to seamlessly engage customers earlier in the buyer journey
- Offer customers real value in exchange for their information
Build transparency into the framework of their digital strategy to build trust with customers
- Reward customers by offering continual value and incentivizing them to engage more often to drive long-term loyalty and advocacy
White Paper: DIY vs CIAM

Digital innovation being demanded by every business unit is transforming IT’s role to that of the main driver of new growth initiatives, prompting a shift in perspective and strategy for CIOs that begins with a well-planned and executed approach to managing customer identities. While legacy IAM might seem like a natural starting point for meeting this challenge, customer identity and access management (CIAM) has significantly different requirements and outcomes when compared to employee-facing IAM.
Data Sheet: Gigya and Global Regulatory Compliance

Gigya’s Customer Identity Management platform offers features that provide maximum flexibility for building
customer consent and control into every step of the customer journey, as well as support for meeting a wide
range of regional privacy requirements. Notably, the European Union’s General Data Protection Regulation
(GDPR) comes into effect on May 25, 2018, carrying potential penalties of up to the greater of €20,000,000 or
4% of total annual global turnover.
The following data sheet illustrates how Gigya’s platform enables data privacy and compliance for our 700 clients.
White Paper: 2017 Predictions - French

2016 a été une année décisive en
matière de Gestion des identités clients
(CIM - Customer Identity Management)
et les entreprises, la presse et les
analystes se sont accordés à dire que
la technologie CIM n’était plus une «
bonne chose » au sein des entreprises
actuelles, mais un impératif.
White Paper: 2017 Predictions - German

Als die Identität der Verbraucher in vollem Gange ist, hat Gigya fünf Vorhersagen für die wichtigsten Trends, die wir sehen, wachsen im Jahr 2017 gelegt, und wie wir sehen, dass Organisationen reagieren.
Case study - American Kennel Club

American Kennel Club (AKC) understood they needed a registration system, but after attempting to build their own, and some significant challenges in time and effort, AKC effectively sought to implement Gigya's Customer Identity Management Platform.
In this case study, Steve Pessah, Sr. Product Manager at American Kennel Club, discusses how Gigya has helped AKC:
- Improve registration conversion rates by 75%
- Increase value per user by 35%
- Saved 12 months of development time for AKC
Gigya Infographic - Death Of A Password

Consumers now expect more trusted and personalized experiences in exchange for their personal information, but businesses are struggling to protect user privacy in light of growing global security and privacy concerns. Since tolerance is diminishing for username and password processes, today’s businesses must find new ways to secure users' data while delivering better customer experiences.
GDPR Implications Customer Identity Management - German

The upcoming General Data Protection Regulation (EU GDPR) will change the requirements for managing consumers’ personal data across the globe. The regulation’s scope is broad and also affects organizations outside of the EU. Striking a balance between meeting the new regulatory requirements and effectively serving customers in the age of Digital Transformation mandates a shift from siloed consumer data management to centralized Customer Identity Management platforms that support the balance between compliance, user consent, and optimizing the customer experience.
In this white paper — commissioned by Gigya from European analyst firm KuppingerCole and prepared by Fellow Analyst Dr. Karsten Kinast and Lead Analyst Ivan Niccolai — you will learn about:
*The history, framework, implementation and scope of the EU GDPR
*Key compliance elements of the EU GDPR
*The implications of the EU GDPR on Customer Identity Management and best-practice recommendations for strategy and implementation
White Paper: Managing consumer data privacy with Gigya (French)

White Paper: Managing consumer data privacy with Gigya French
Managing Consumer Data Privacy

For today’s digital businesses, being prepared to meet new compliance requirements when storing and managing consumer data will not only minimize risk, but also enable more valued and trusted customer experiences that drive increased loyalty, engagement and revenue. To gain better perspective on this important issue, it’s important to understand:
- The trends driving governmental regulatory shifts and the basic tenets of these new laws
- The challenges faced by executives across the enterprise when managing privacy compliance for consumer data
- The emergence of cloud-based solutions that help businesses manage privacy compliance by acting as end-to-end customer data storage and management solutions that are far more scalable and flexible than legacy systems
Information Security and Data Privacy Practices

Gigya’s enterprise class Customer Identity & Access Management platform delivers maximum efficiency and scalability while protecting consumer data with strict security and compliance standards. The four pillars of Gigya’s security and privacy promise are:
- Infrastructure: State-of-the-art data centers for optimized performance and scalability.
- Data Security: ISO 27001 certification and multiple levels of security protect data with both physical and virtual safeguards.
- Compliance: Regional privacy compliance and built in social network terms of service functionality ensure responsible data management.
- Privacy Policies: Increased transparency of data practices fosters consumer trust and relationships.
Russian Data Center

Russia’s new Personal Data Protection Act stipulates that companies with Russian customers must store those users’ personal data within Russian borders. To ensure that all of our clients doing business in Russia can continue to do so safely, Gigya has opened a new primary data center in Russia.
White Paper: 5 Ways Airports Can Drive Non-Aviation Revenue

With airlines now accounting for just 38% of airport revenues, maximizing non-aviation earnings has never been more necessary. This white paper takes a look at how airports can drive non-aviation revenue by leveraging customer identities to create personal experiences across five key areas:
- Parking
- Retail and concessions
- Food and beverage
- Loyalty programs
- Advertising
Case Study: Unibail-Rodamco Creates a Connected, Personalized Shopping Experi...

After conducting a customer survey, Unibail-Rodamco determined that providing shoppers with personalized experiences across malls was key to its future success. By leveraging a Customer Identity Management solution to understand its shoppers' tastes and preferences, Unibail-Rodamco was able to see:
- 26% increase in registration rates
- 92% growth in loyalty card subscriptions
- 76% of registrants connecting socially
- 35x increase in mobile registrations
More from Gigya (20)
White Paper: Gigya's Information Security and Data Privacy Practices

White Paper: Gigya's Information Security and Data Privacy Practices
Gigya und die Erfüllung globaler behördlicher Auflagen (Global Regulatory Com...

Gigya und die Erfüllung globaler behördlicher Auflagen (Global Regulatory Com...
Data Sheet: Gigya and Global Regulatory Compliance

Data Sheet: Gigya and Global Regulatory Compliance
GDPR Implications Customer Identity Management - German

GDPR Implications Customer Identity Management - German
White Paper: Managing consumer data privacy with Gigya (German)

White Paper: Managing consumer data privacy with Gigya (German)
White Paper: Managing consumer data privacy with Gigya (French)

White Paper: Managing consumer data privacy with Gigya (French)
White Paper: 5 Ways Airports Can Drive Non-Aviation Revenue

White Paper: 5 Ways Airports Can Drive Non-Aviation Revenue
Case Study: Unibail-Rodamco Creates a Connected, Personalized Shopping Experi...

Case Study: Unibail-Rodamco Creates a Connected, Personalized Shopping Experi...
Recently uploaded
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Have you ever wanted a Ruby client API to communicate with your web service? Smithy is a protocol-agnostic language for defining services and SDKs. Smithy Ruby is an implementation of Smithy that generates a Ruby SDK using a Smithy model. In this talk, we will explore Smithy and Smithy Ruby to learn how to generate custom feature-rich SDKs that can communicate with any web service, such as a Rails JSON API.
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Recently uploaded (20)
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Generating a custom Ruby SDK for your web service or Rails API using Smithy
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Case Study: DC Thomson Media Creates a Single Customer View Across Multiple Domains
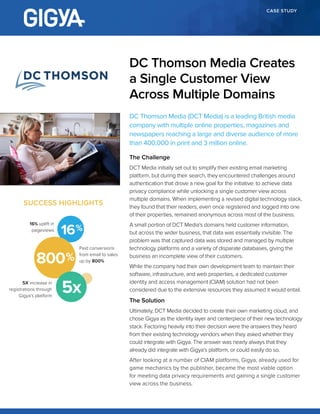
- 1. CASE STUDY DC Thomson Media (DCT Media) is a leading British media company with multiple online properties, magazines and newspapers reaching a large and diverse audience of more than 400,000 in print and 3 million online. The Challenge DCT Media initially set out to simplify their existing email marketing platform, but during their search, they encountered challenges around authentication that drove a new goal for the initiative: to achieve data privacy compliance while unlocking a single customer view across multiple domains. When implementing a revised digital technology stack, they found that their readers, even once registered and logged into one of their properties, remained anonymous across most of the business. A small portion of DCT Media’s domains held customer information, but across the wider business, that data was essentially invisible. The problem was that captured data was stored and managed by multiple technology platforms and a variety of disparate databases, giving the business an incomplete view of their customers. While the company had their own development team to maintain their software, infrastructure, and web properties, a dedicated customer identity and access management (CIAM) solution had not been considered due to the extensive resources they assumed it would entail. The Solution Ultimately, DCT Media decided to create their own marketing cloud, and chose Gigya as the identity layer and centerpiece of their new technology stack. Factoring heavily into their decision were the answers they heard from their existing technology vendors when they asked whether they could integrate with Gigya. The answer was nearly always that they already did integrate with Gigya’s platform, or could easily do so. After looking at a number of CIAM platforms, Gigya, already used for game mechanics by the publisher, became the most viable option for meeting data privacy requirements and gaining a single customer view across the business. DC Thomson Media Creates a Single Customer View Across Multiple Domains SUCCESS HIGHLIGHTS 16 Paid conversions from email to sales up by 800% 16% uplift in pageviews 5X increase in registrations through Gigya’s platform 800 5x
- 2. © 2017 Gigya, Inc. | 2513 East Charleston Road #200, Mountain View, CA 94043 | T: (650) 353.7230 | www.gigya.com Gigya, the Gigya logo, and Customer Identity Management Platform are either registered trademarks or trademarks of Gigya Incorporated in the United States and/or other countries. All other trademarks are the property of their respective owners. Gigya does not own any end user data or maintain any other rights to this data, other than utilizing it to make Gigya’s services available to our clients and their end users. Gigya acts as an agent or back-end vendor of its client’s website or mobile application, to which the end user of our client granted permissions (if applicable). Gigya facilitates the collection, transfer and storage of end user data solely on behalf of its clients and at its clients’ direction. For more information, please see Gigya’s Privacy Policy, available at http://www.gigya.com/privacy-policy/. Gigya_CS_DC_Thomson_201710 Kirsten Morrison, Head of Digital, said, “Gigya was the ‘silver bullet’ that resolved this issue and allowed us to build out our own mini-network, creating in effect a multi-site environment of shops and websites with a single login and preference centre.” Gigya’s Registration-as-a-Service (RaaS) solution now essentially serves as the gatekeeper for the majority of DCT Media’’s digital properties, controlling all new sign ups and email preferences. With this single login and preference center, users are able to seamlessly access other domains in DCT Media’’s portfolio via Gigya’s Single Sign-on (SSO) features. In addition, Gigya directly or indirectly integrates first-party data collected by the publisher with technologies such as Magento, Wordpress, Permutive, Sailthru, and more. The Benefits Currently, Gigya is live on 15 of DCT Media’’s digital properties, with the goal of being live on 20 by the end of 2017. Gigya is the single point of entry for these properties, so a reader or viewer cannot sign up to manage preferences, buy a subscription, access content behind a paywall or receive newsletters without a Gigya ID. As a result, DCT Media has found that a registered reader or viewer is 5 times more valuable than an anonymous visitor, consuming significantly more content. Also, registered readers are 12 times more likely to buy a subscription to their titles. DCT Media even saw an increase of 800% on e-commerce campaigns from e-mails using Sailthru and their newfound personalisation capabilities. As far as data privacy compliance, the European Union’s General Data Protection Regulations (EU GDPR) went from being threatening to manageable, thanks in part to the Gigya implementation team’s guidance. Within the last year alone, DCT Media saw a five-fold increase in registrations through Gigya’s platform. Around 40% of those new readers signed up for accounts via marketing emails, becoming DCT Media’s second most valuable type of customer in terms of page views, increasing this KPI by 16%, especially when linked to delivered personalised content. By enabling Gigya’s SSO functionality throughout their e-commerce platforms, affiliate websites, magazine and newspaper websites, DCT Media now understands how readers consume content across multiple properties, can easily track their behaviour across sites, and develop valuable new products based on that underlying data. GIGYA WAS THE ‘SILVER BULLET’ THAT RESOLVED THIS ISSUE AND ALLOWED US TO BUILD OUT OUR OWN MINI-NETWORK, CREATING IN EFFECT A MULTI-SITE ENVIRONMENT OF SHOPS AND WEBSITES WITH A SINGLE LOGIN AND PREFERENCE CENTRE. Kirsten Morrison Head of Digital, DC Thomson Media
