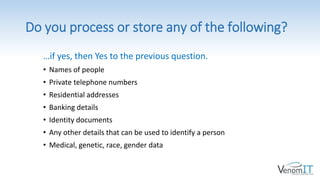
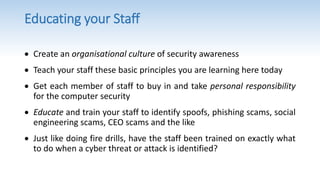
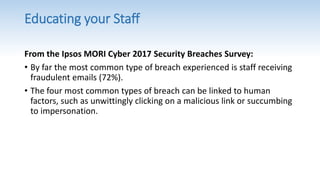
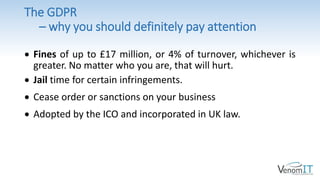
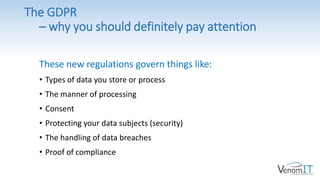
The presentation by Christoan Smit aims to provide insights into cyber security and GDPR, emphasizing their importance for businesses and how cloud services can support compliance and security. Key aspects discussed include the GDPR's regulations, the necessity of cyber security principles (CIA: confidentiality, integrity, availability), and various solutions for protecting data and ensuring staff training. The document concludes by promoting Venom IT's services, which include GDPR compliance assistance, network security, and cloud solutions.




![A Solution to the Problem…
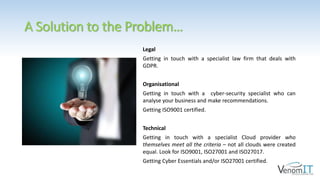
Regulation 18 of the GDPR states, in part:
“….when entrusting a processor
[subcontractor] with processing activities,
the …adherence of the processor to an
approved code of conduct or an approved
certification mechanism may be used as an
element to demonstrate compliance with
the obligations of the controller [you].”
In other words, the certificates and/or approved
codes of conduct of the data sub-contractor can be
used by you as proof (or part of your proof) of your
own GDPR compliance.](https://image.slidesharecdn.com/cybersecuritygdprcombinedslideshowlinkedinversion-190226143548/85/Cyber-Security-and-GDPR-Made-Easy-10-320.jpg)