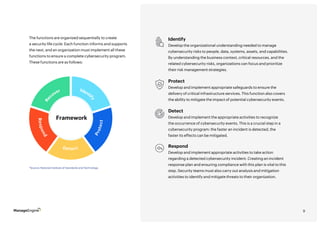
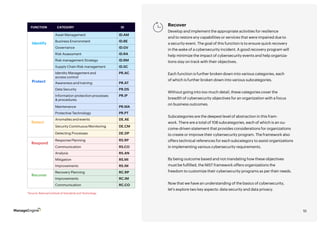
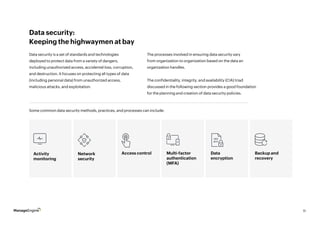
The document provides an overview of cybersecurity, explaining why it is important for businesses to implement security measures to protect their data, networks, and systems from cyber threats in order to avoid economic losses, reputational damage, and regulatory penalties. It discusses the components of cybersecurity including identity and access management, security information and event management, endpoint security, network security, and data security. The document also covers cybersecurity compliance regulations and best practices organizations should follow.