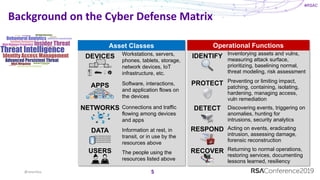
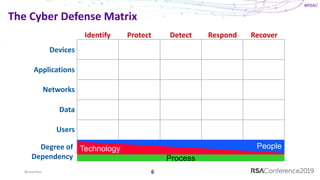
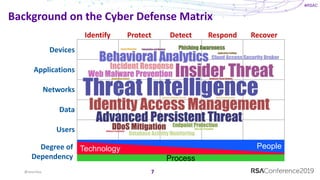
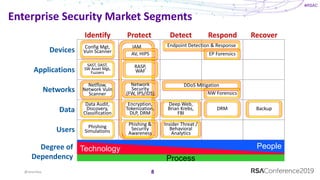
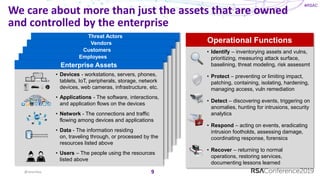
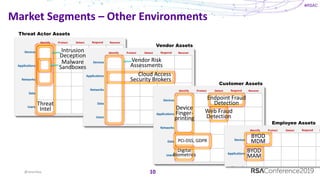
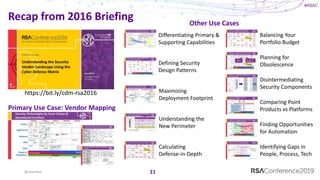
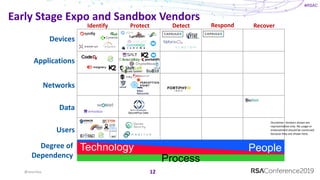
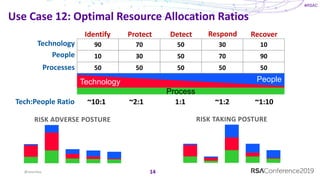
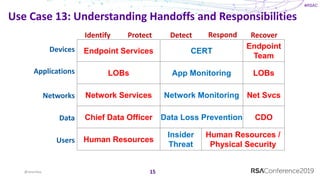
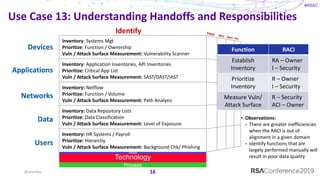
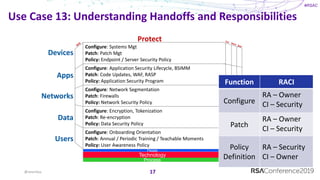
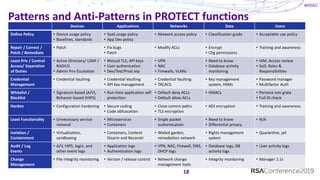
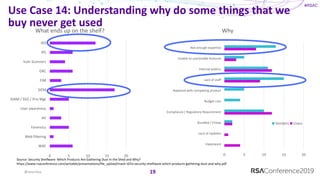
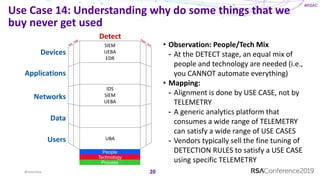
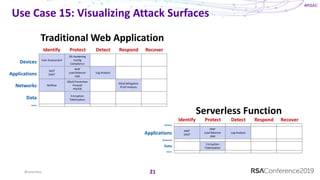
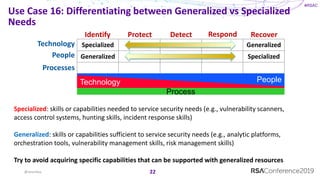
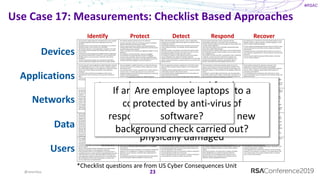
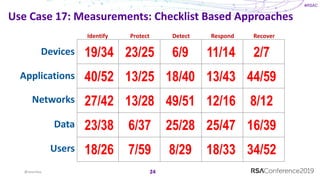
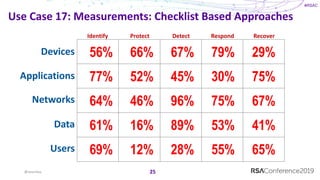
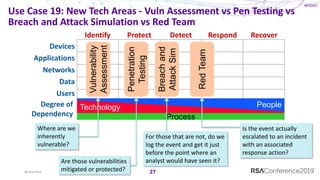
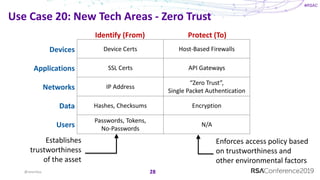
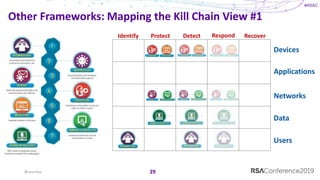
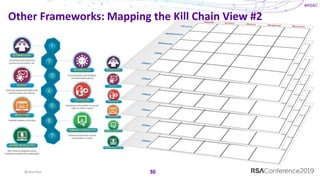
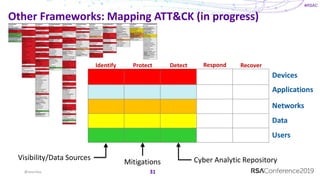
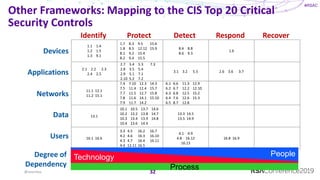
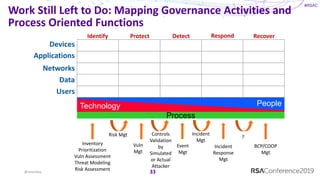
The document discusses the Cyber Defense Matrix, emphasizing its operational functions such as identifying, protecting, detecting, responding, and recovering from security threats. It outlines various asset classes and the functions necessary for effective cybersecurity management, including inventorying vulnerabilities and assessing risks. Additionally, it highlights the importance of balancing technology, people, and processes to enhance security capabilities within organizations.