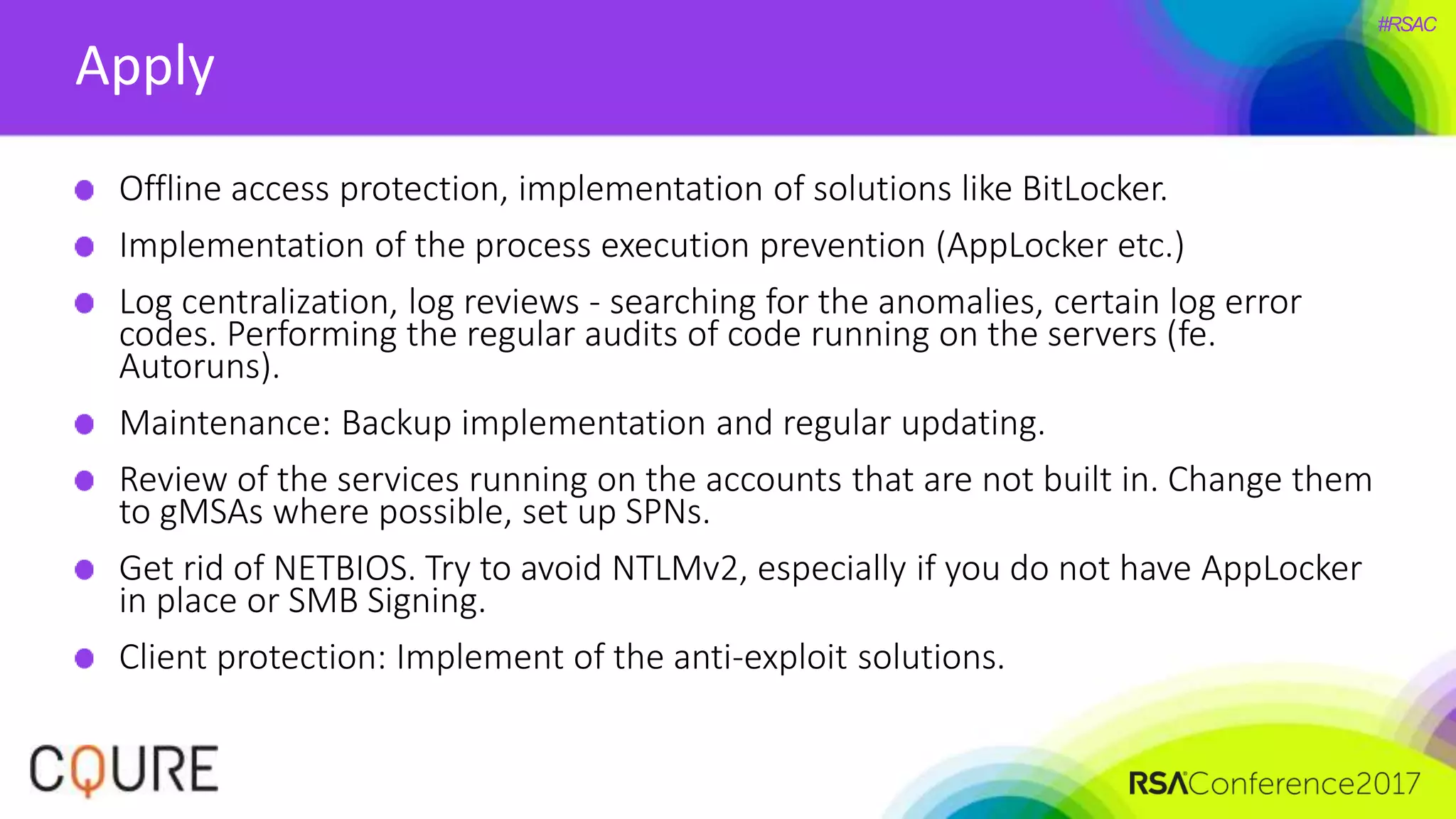
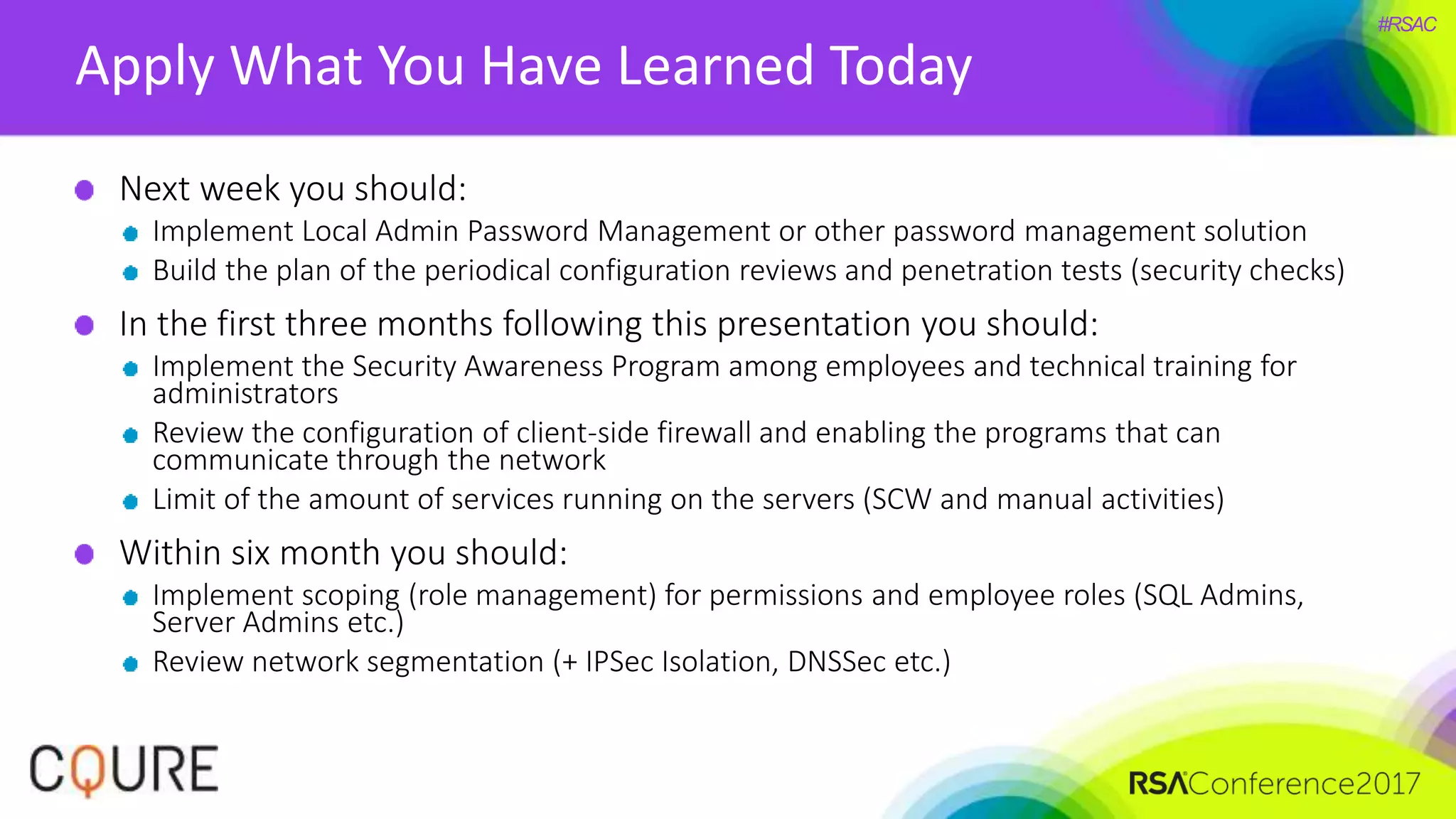
The document discusses cybersecurity best practices for Windows infrastructure, emphasizing the importance of understanding potential vulnerabilities and hacker tactics. Key recommendations include implementing password management, regular audits, security awareness training, and proper network segmentation to mitigate risks. The session aims to equip attendees with practical measures to enhance their security posture against potential attacks.