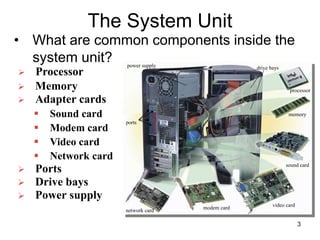
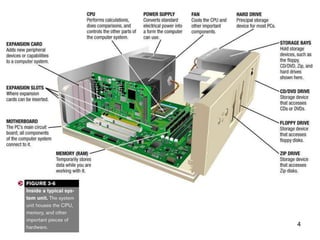
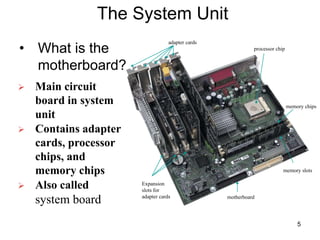
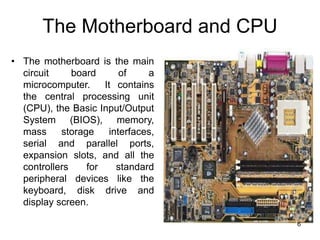
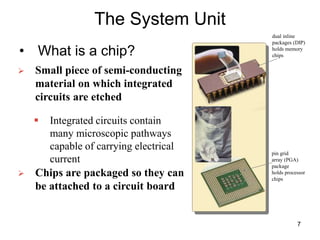
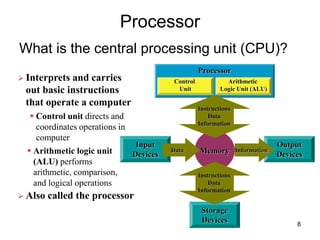
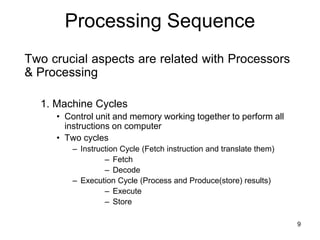
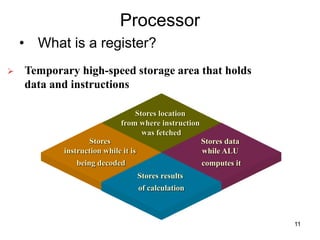
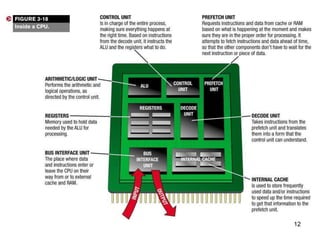
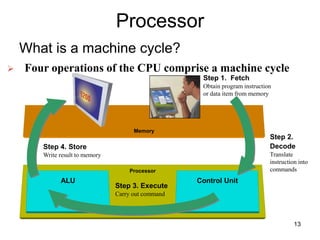
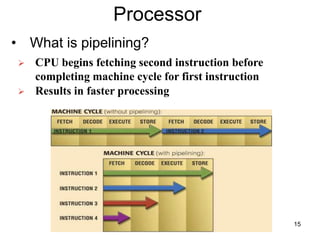
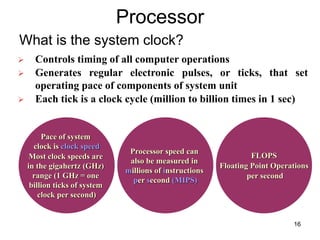
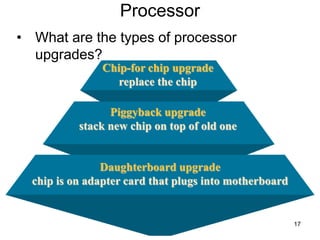
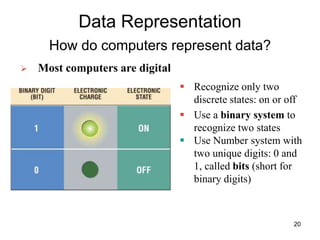
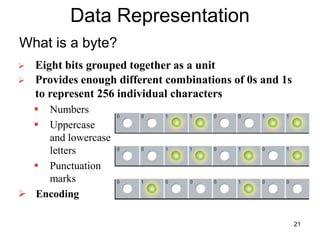
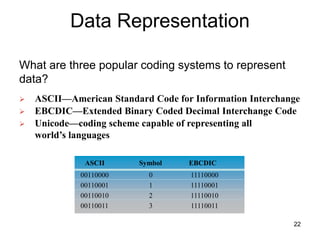
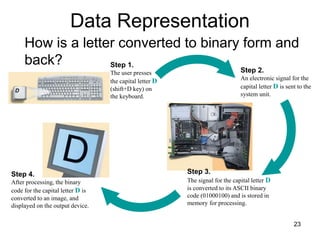
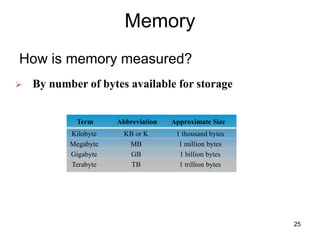
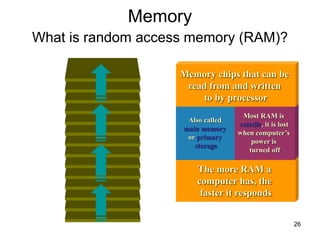
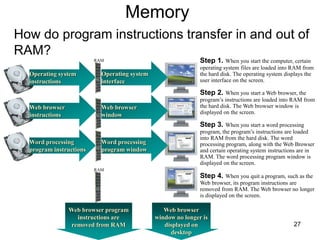
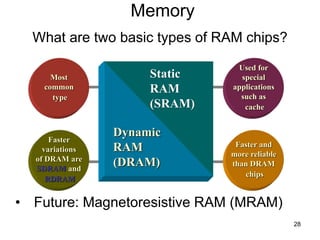
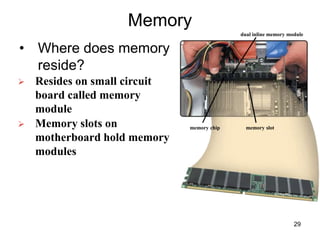
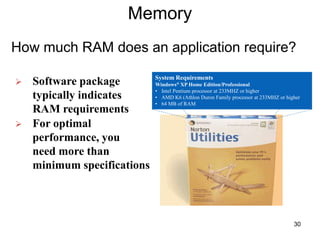
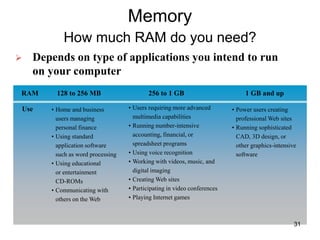
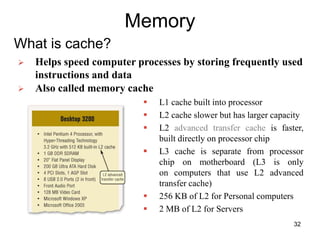
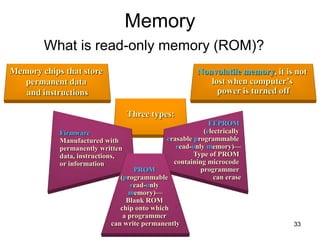
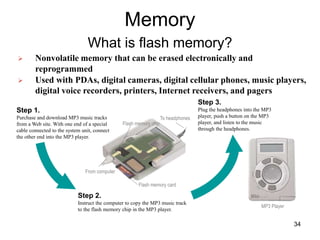
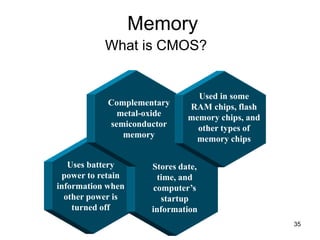
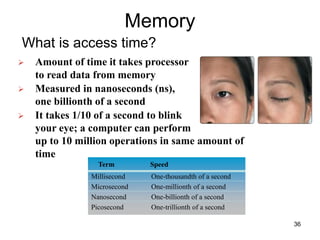
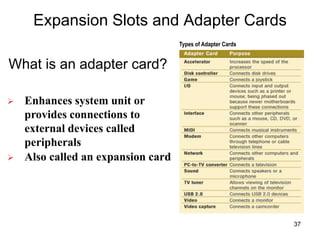
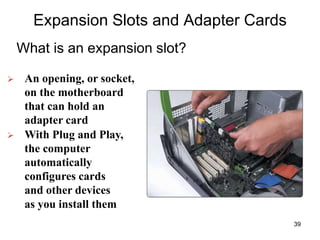
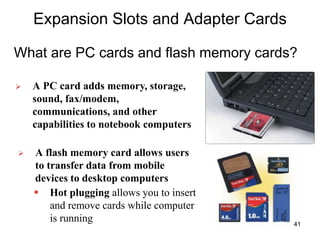
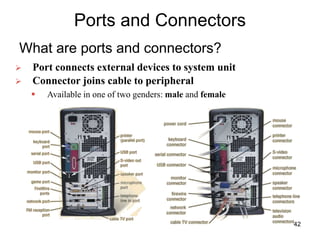
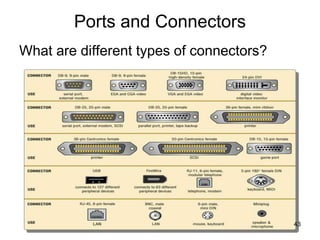
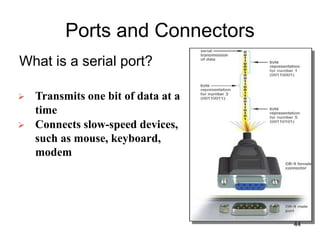
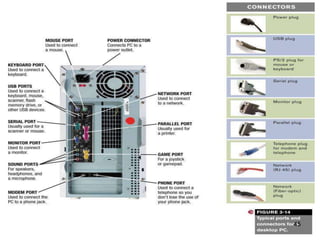
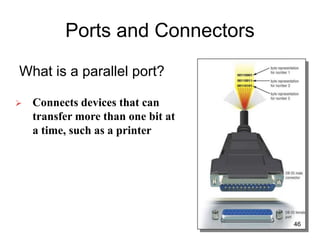
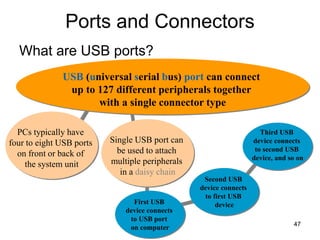
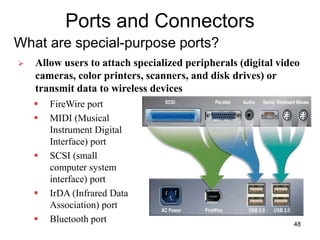
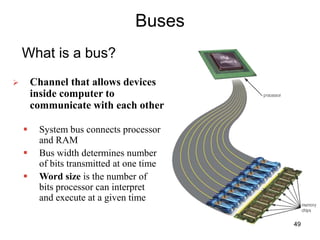
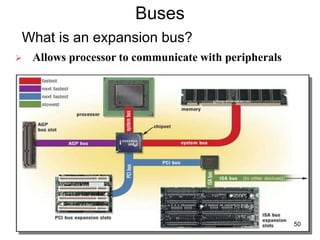
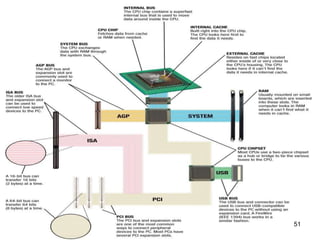
The document describes the components of a computer system unit, focusing on the motherboard, central processing unit (CPU), memory types, and data representation. It explains the functions of key components such as chips, machine cycles, registers, and various types of memory (e.g., RAM, ROM, flash). Additionally, it covers expansion slots, adapter cards, and different ports for connecting external devices.