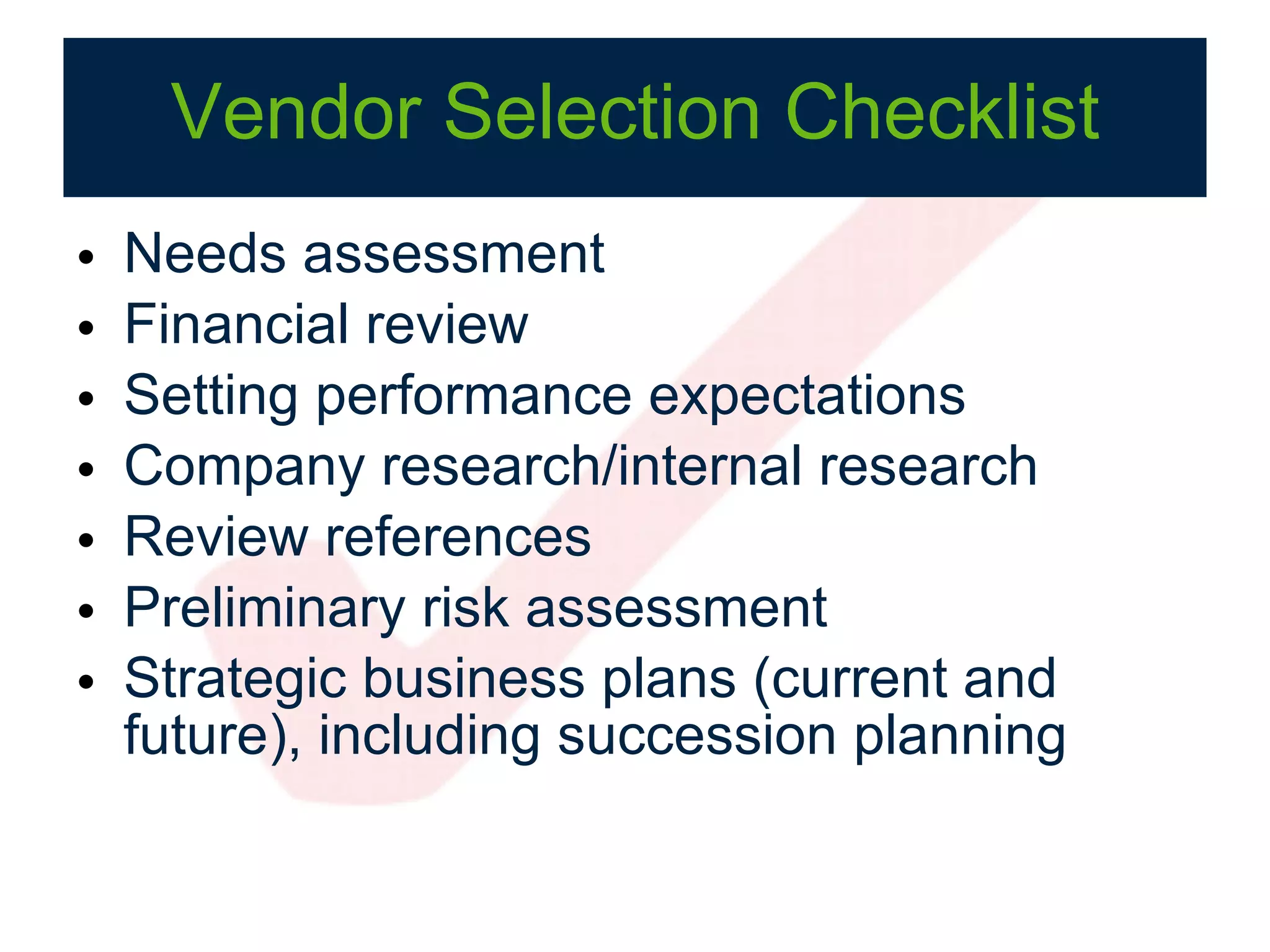
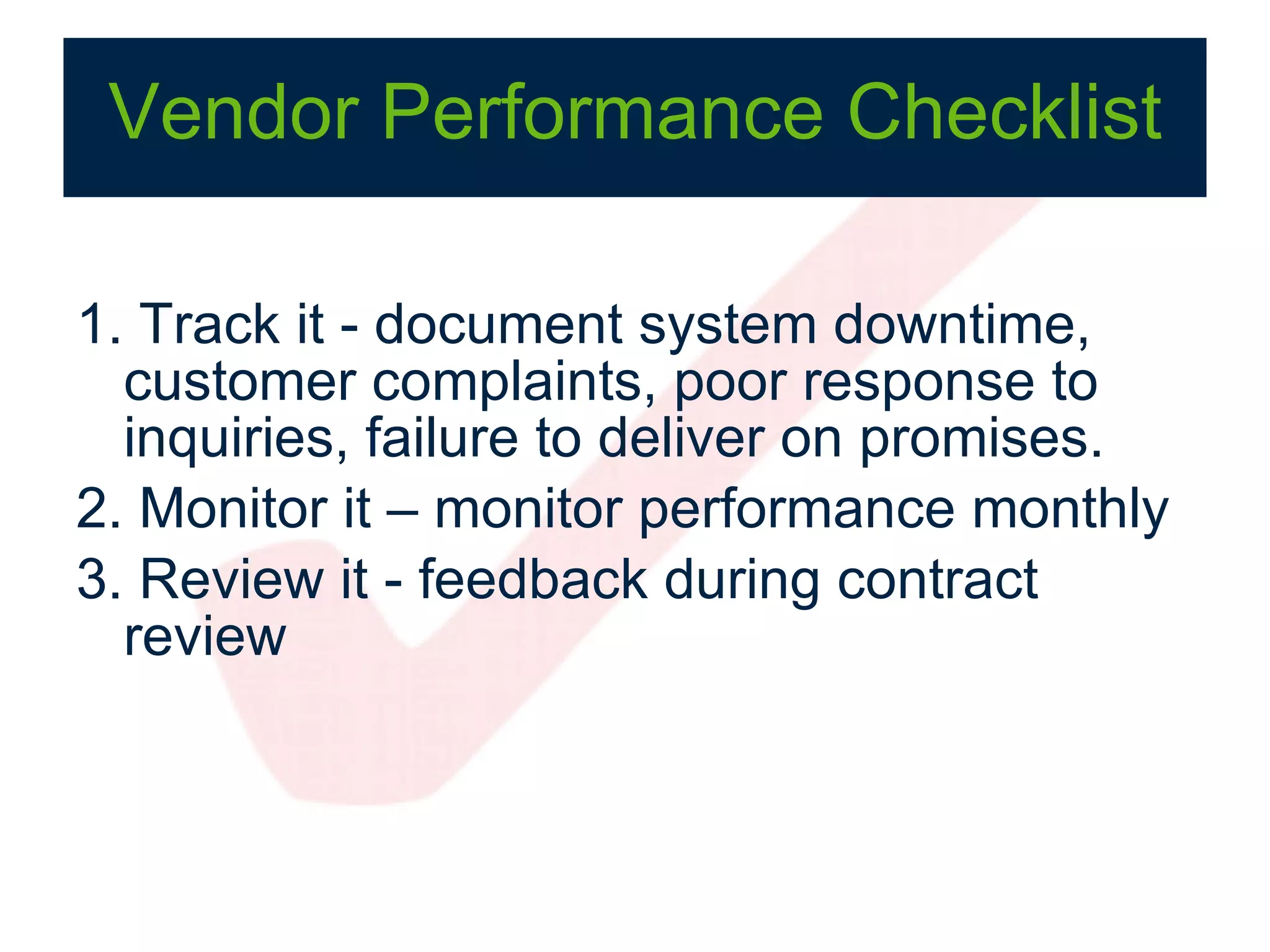
The document presents a comprehensive vendor management compliance checklist aimed at helping financial institutions meet regulatory requirements. It highlights the importance of vendor management programs, the concept of a compliance tax, and the effectiveness of checklists in reducing errors. Key components include risk assessment, due diligence, ongoing monitoring, and the roles of senior management in overseeing outsourced relationships.





























![Thank You! Contact info Susan Orr Susan Orr Consulting http://www.susanorrconsulting.com/ [email_address] Jim Kisch Continuity Control http://www.continuity.net [email_address]](https://image.slidesharecdn.com/compliancechecklistmanifestovendormanagement-100601165139-phpapp01/75/Vendor-Management-Compliance-Checklist-Manifesto-Series-32-2048.jpg)