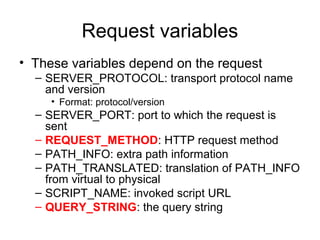
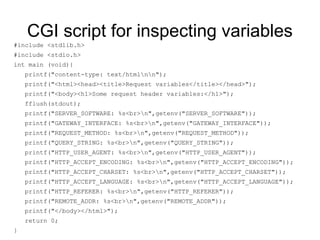
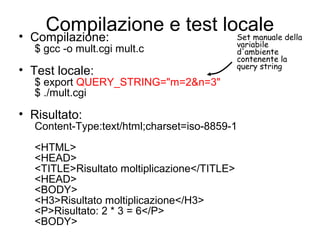
CGI (Common Gateway Interface) is an interface that allows a web server to launch external applications dynamically in response to requests. It defines standard communication variables between the web server and CGI programs. CGI programs can be written in any programming language and are executed by the web server to generate dynamic web page content on the fly based on request parameters and structured data. However, CGI has performance and security limitations due to creating new processes for each request.