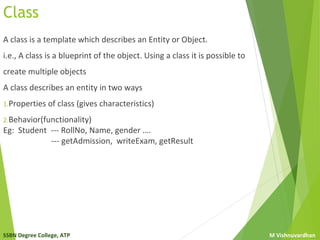
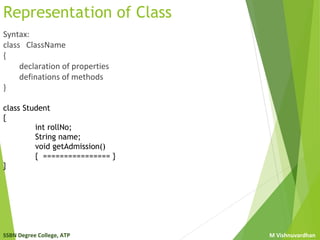
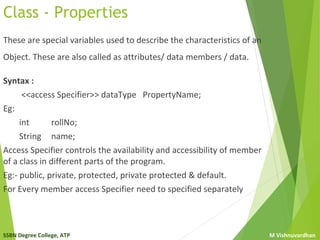
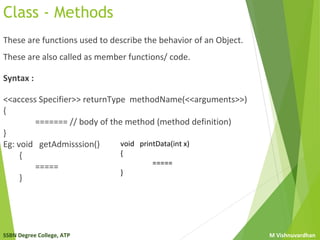
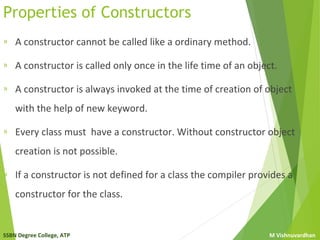
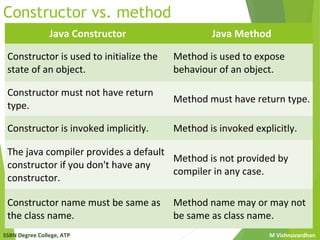
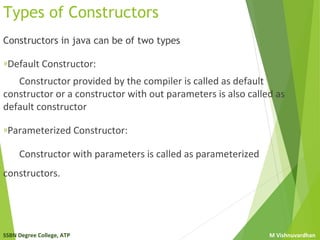
The document explains the concepts of classes and objects in Java, illustrating that a class serves as a template or blueprint describing the properties and behaviors of objects in the software. It defines key elements such as class syntax, properties, methods, and constructors, highlighting their roles and differences. Additionally, it distinguishes between default and parameterized constructors, emphasizing their importance in object creation.