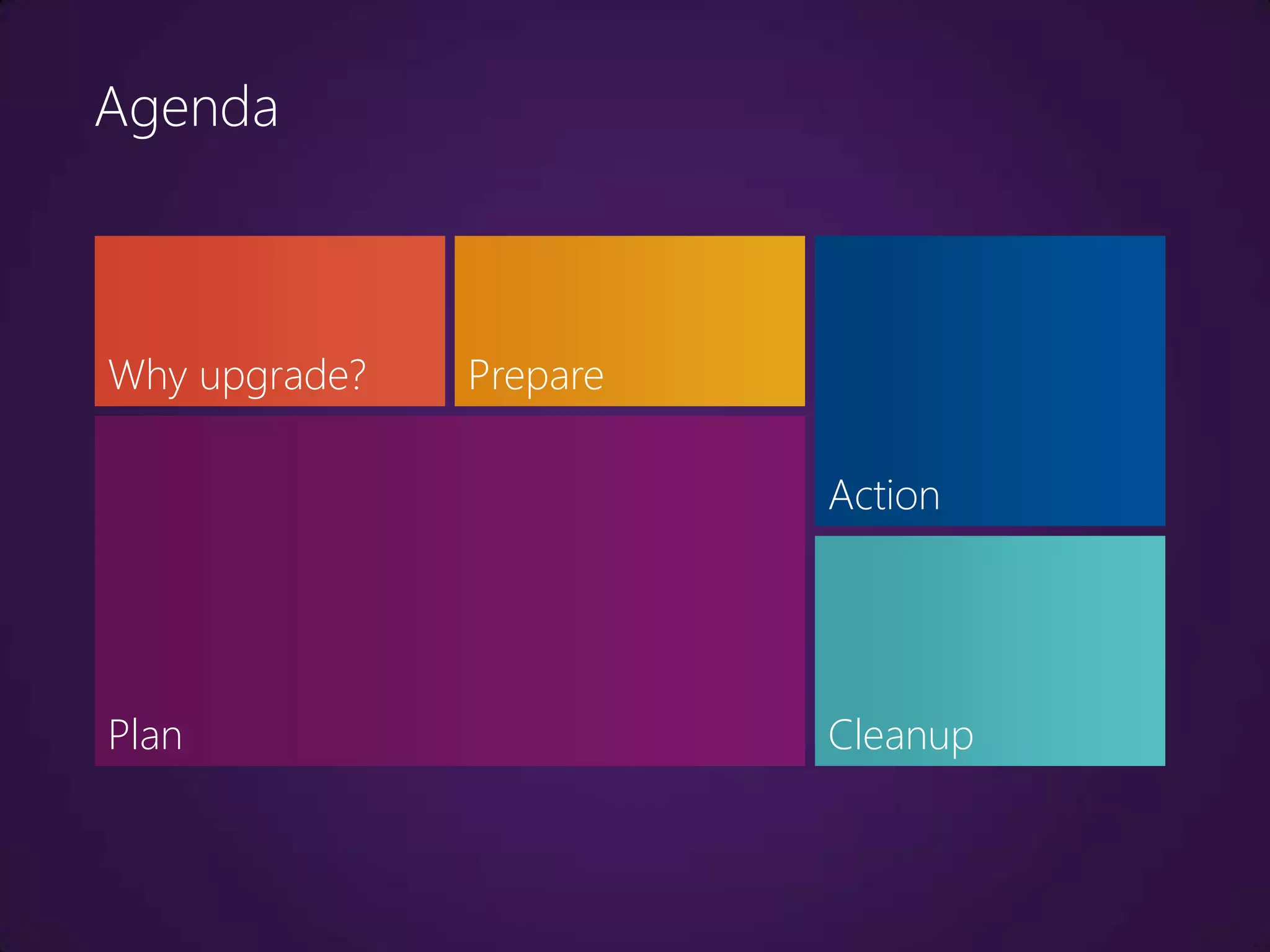
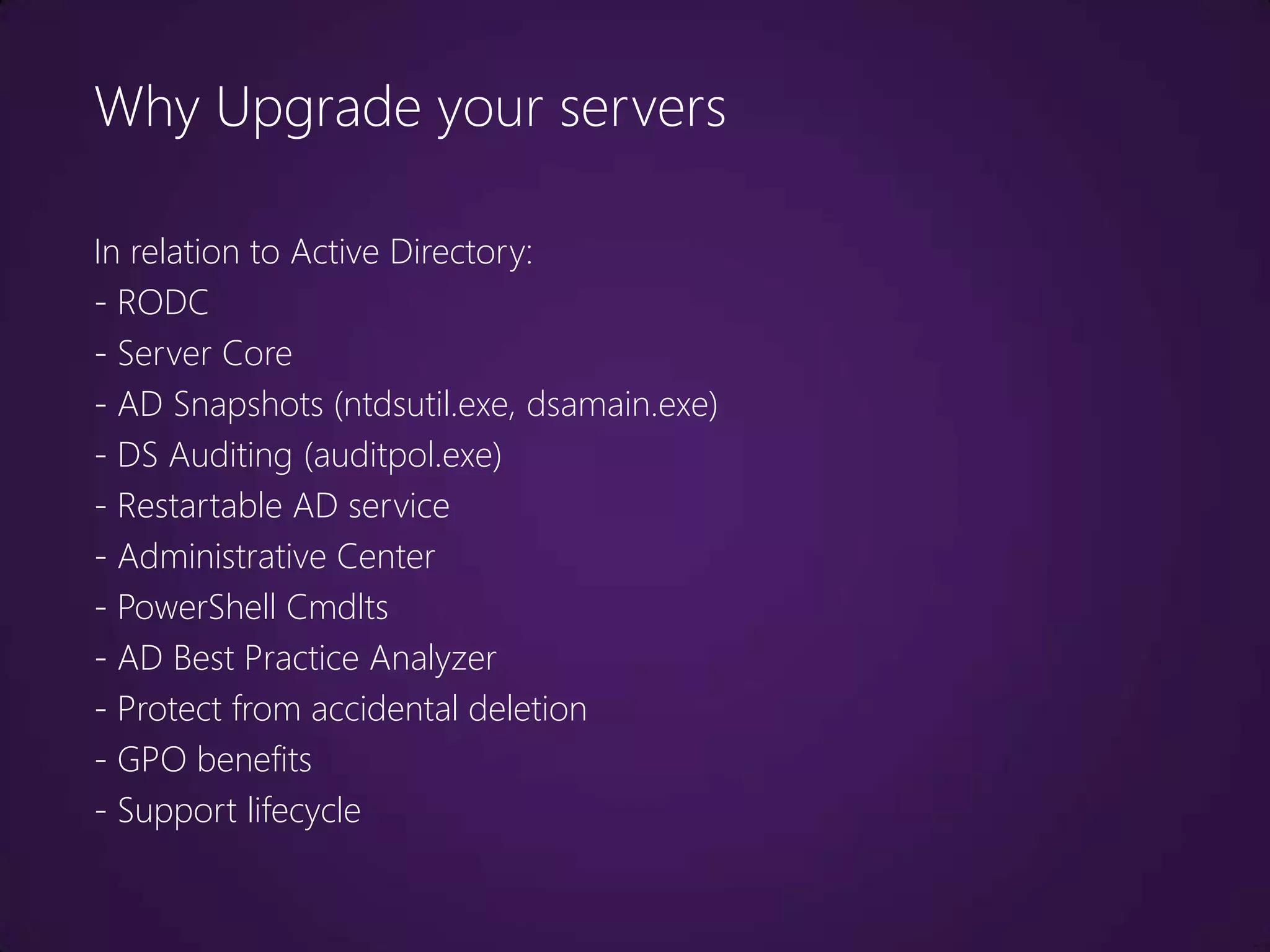
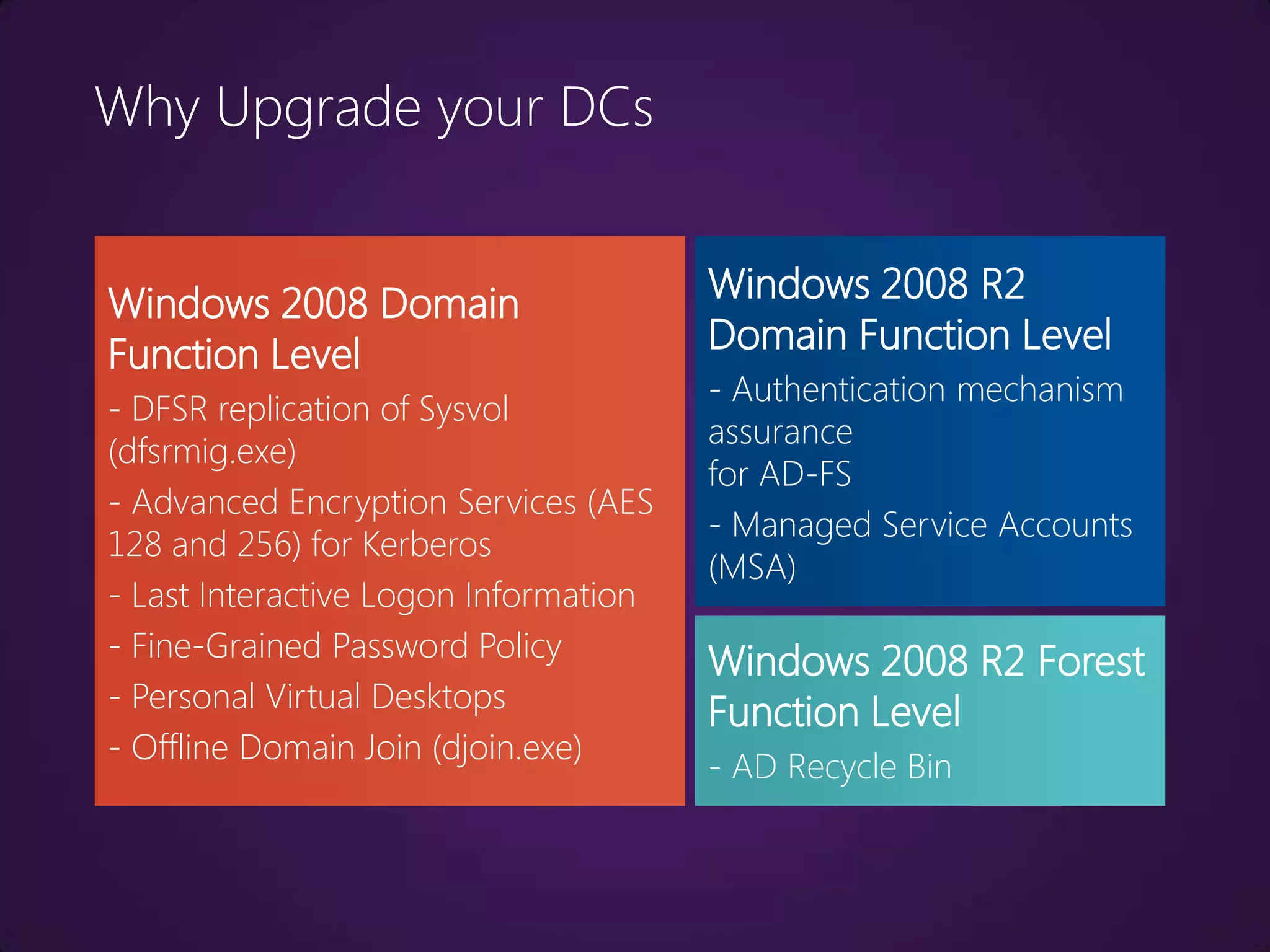
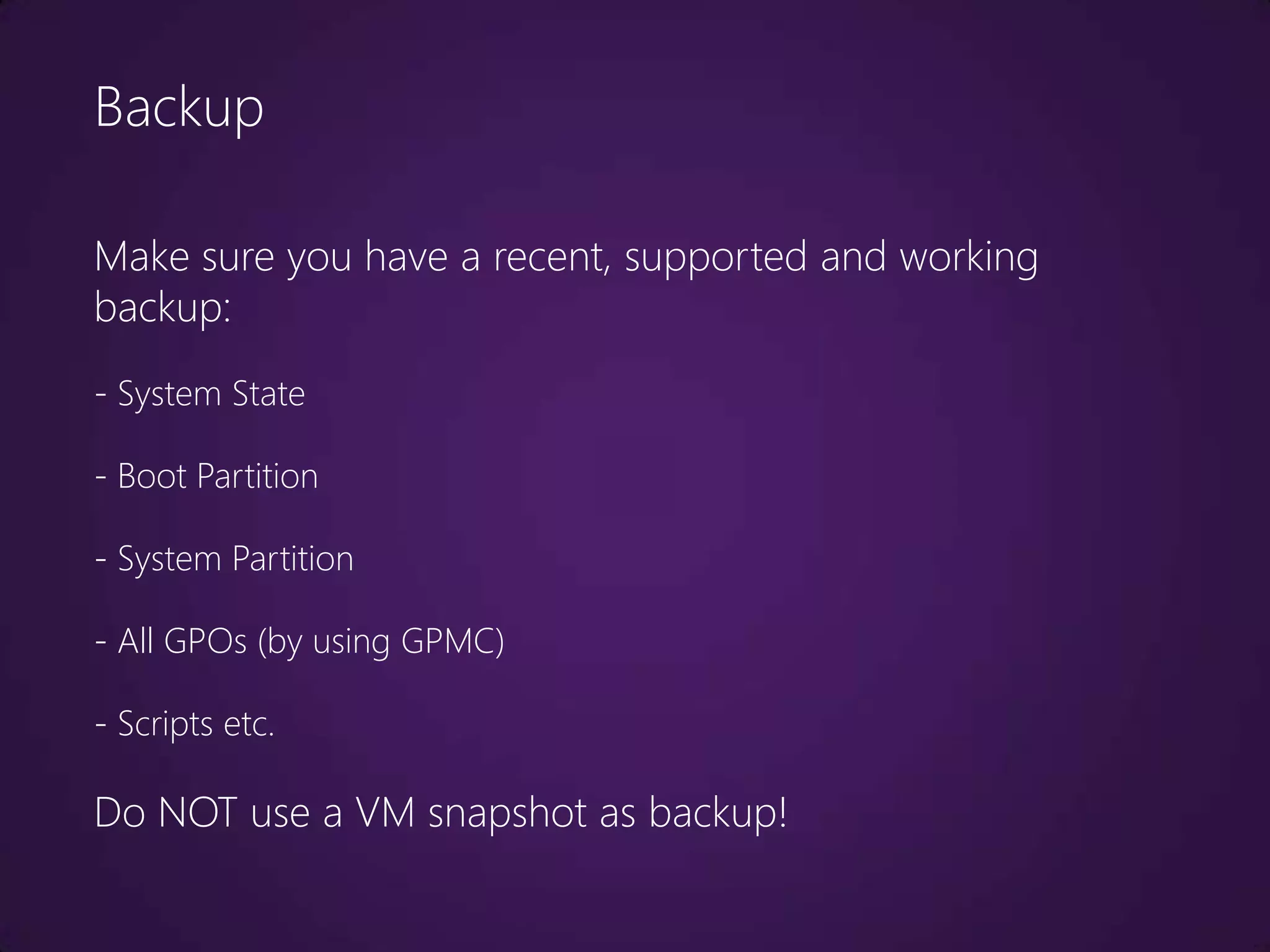
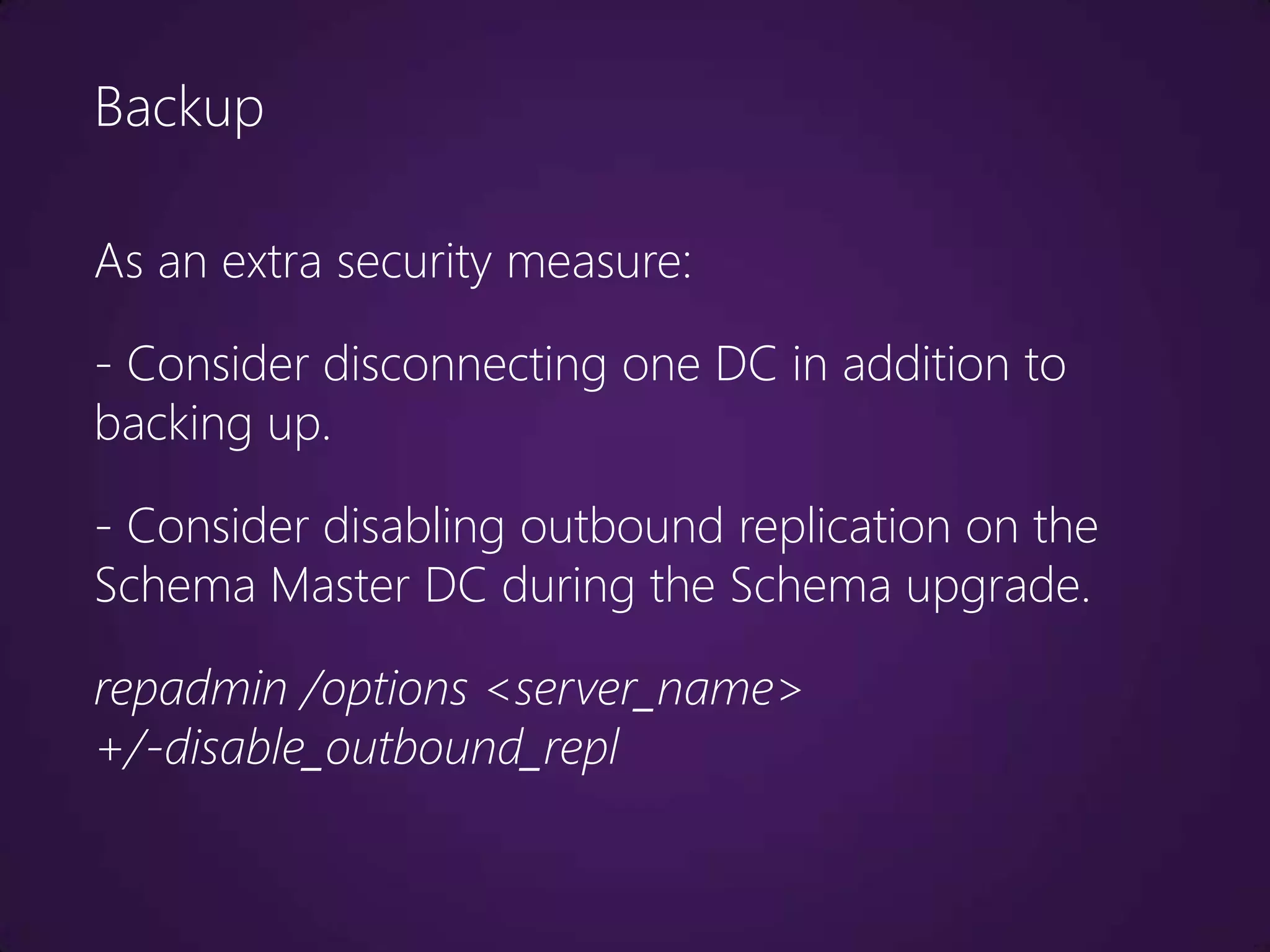
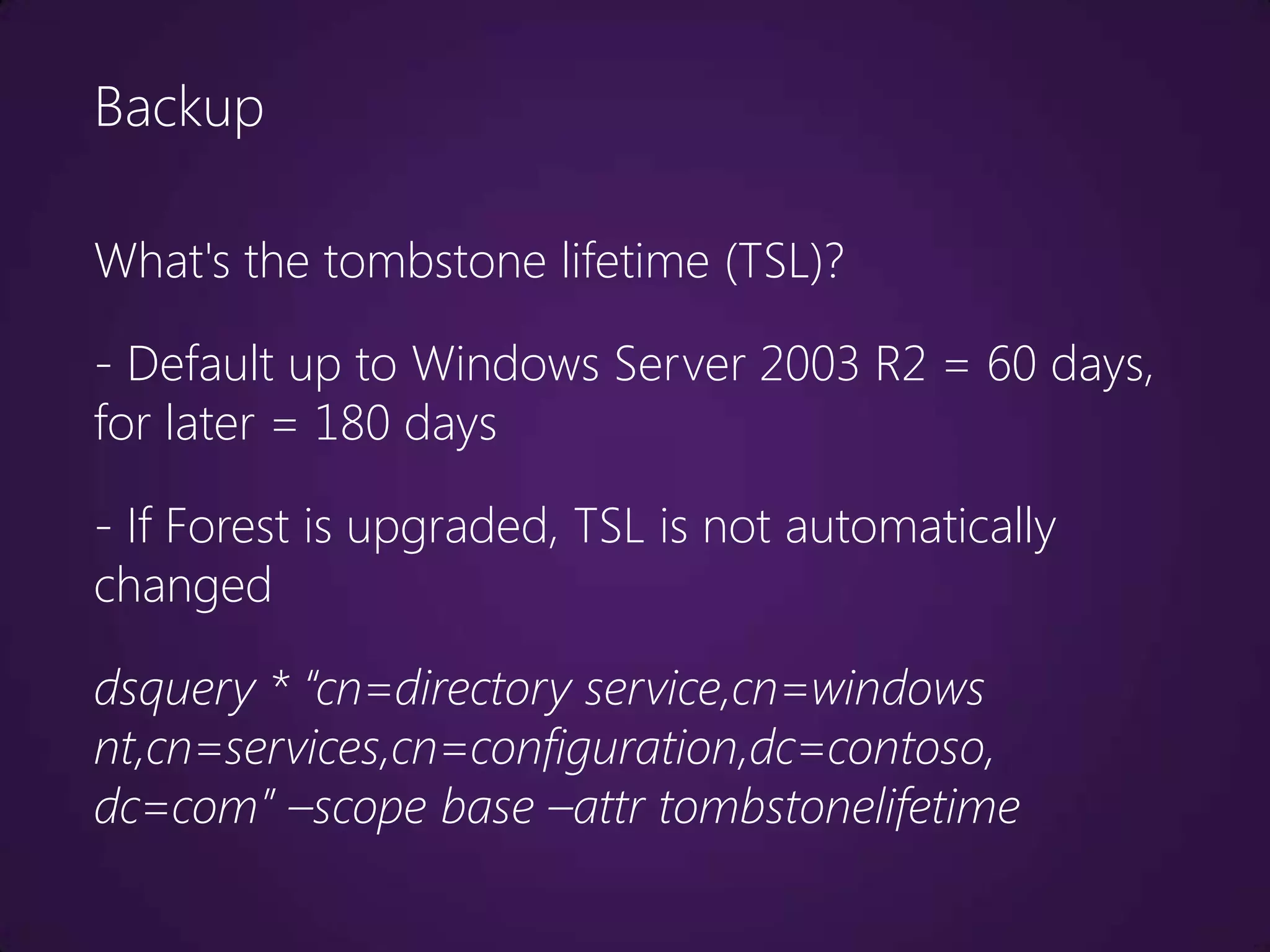
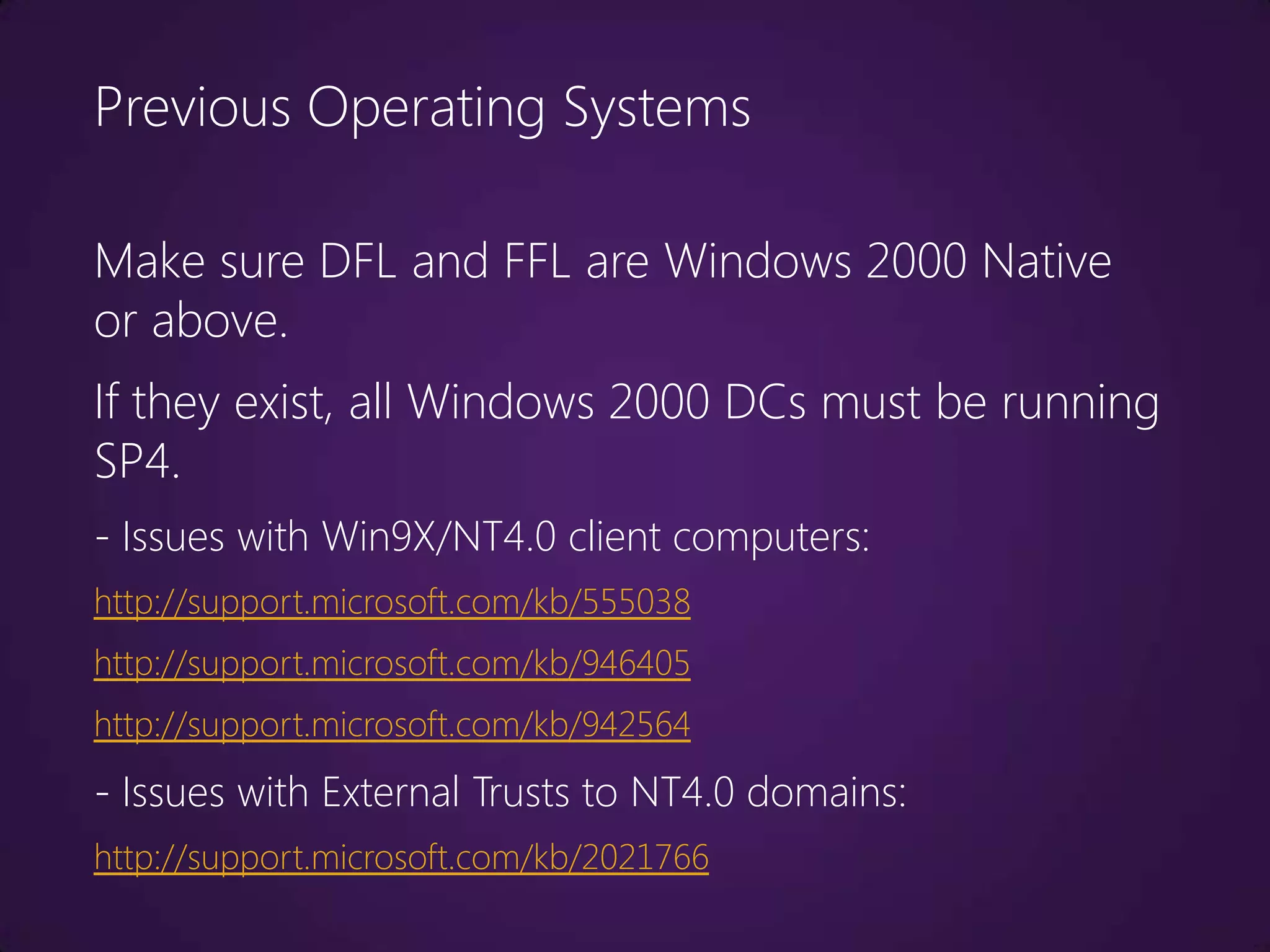
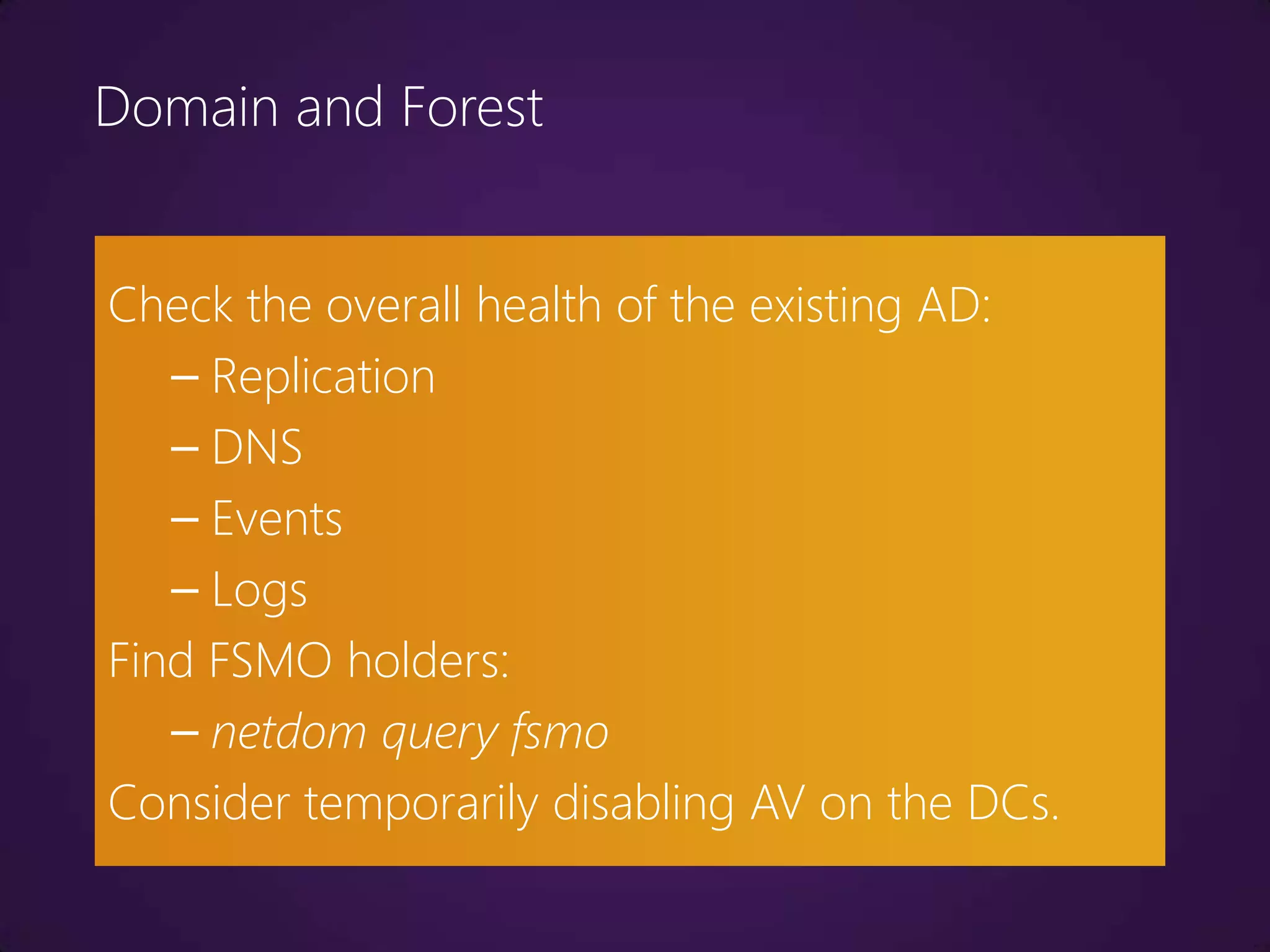
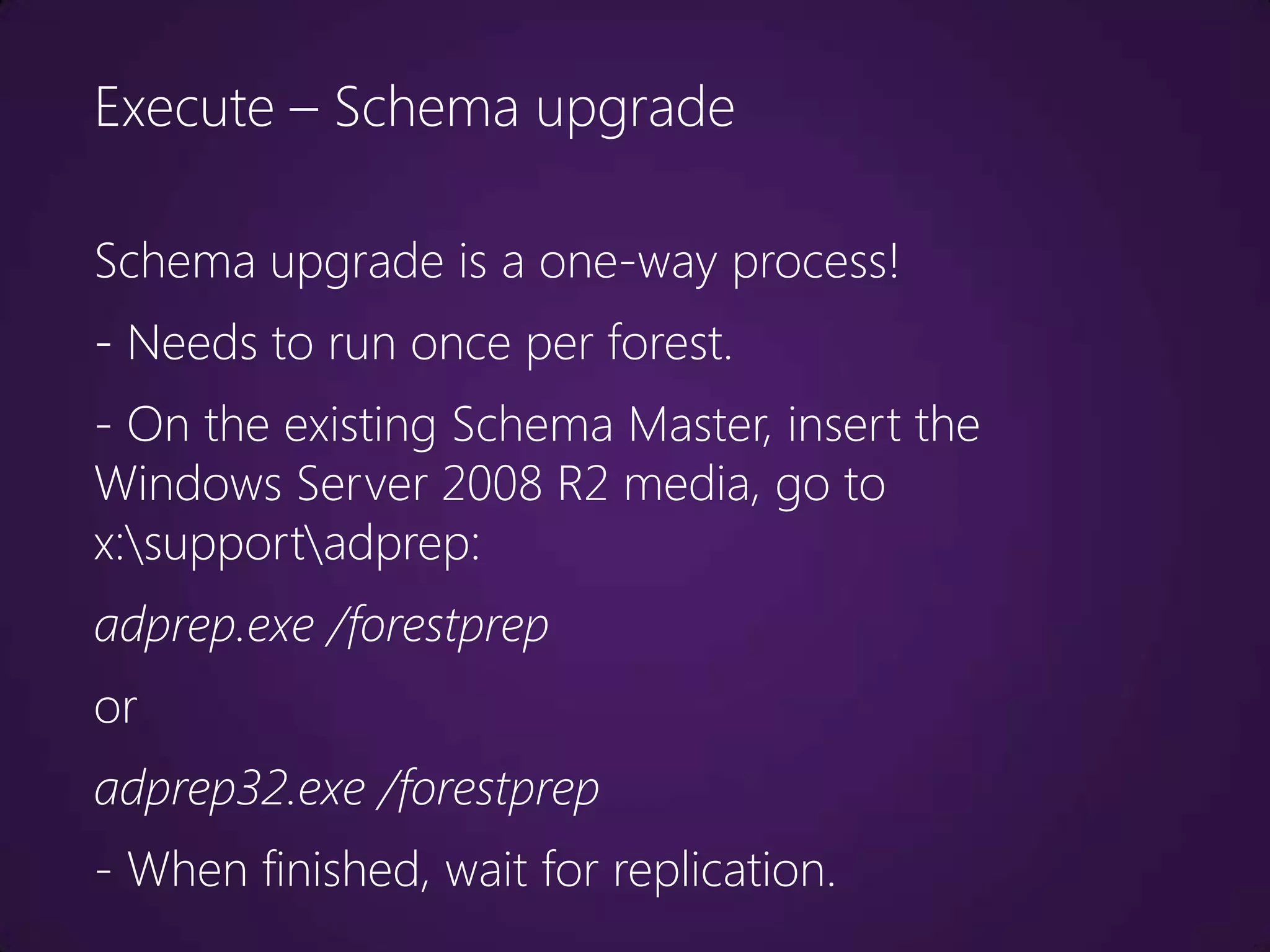
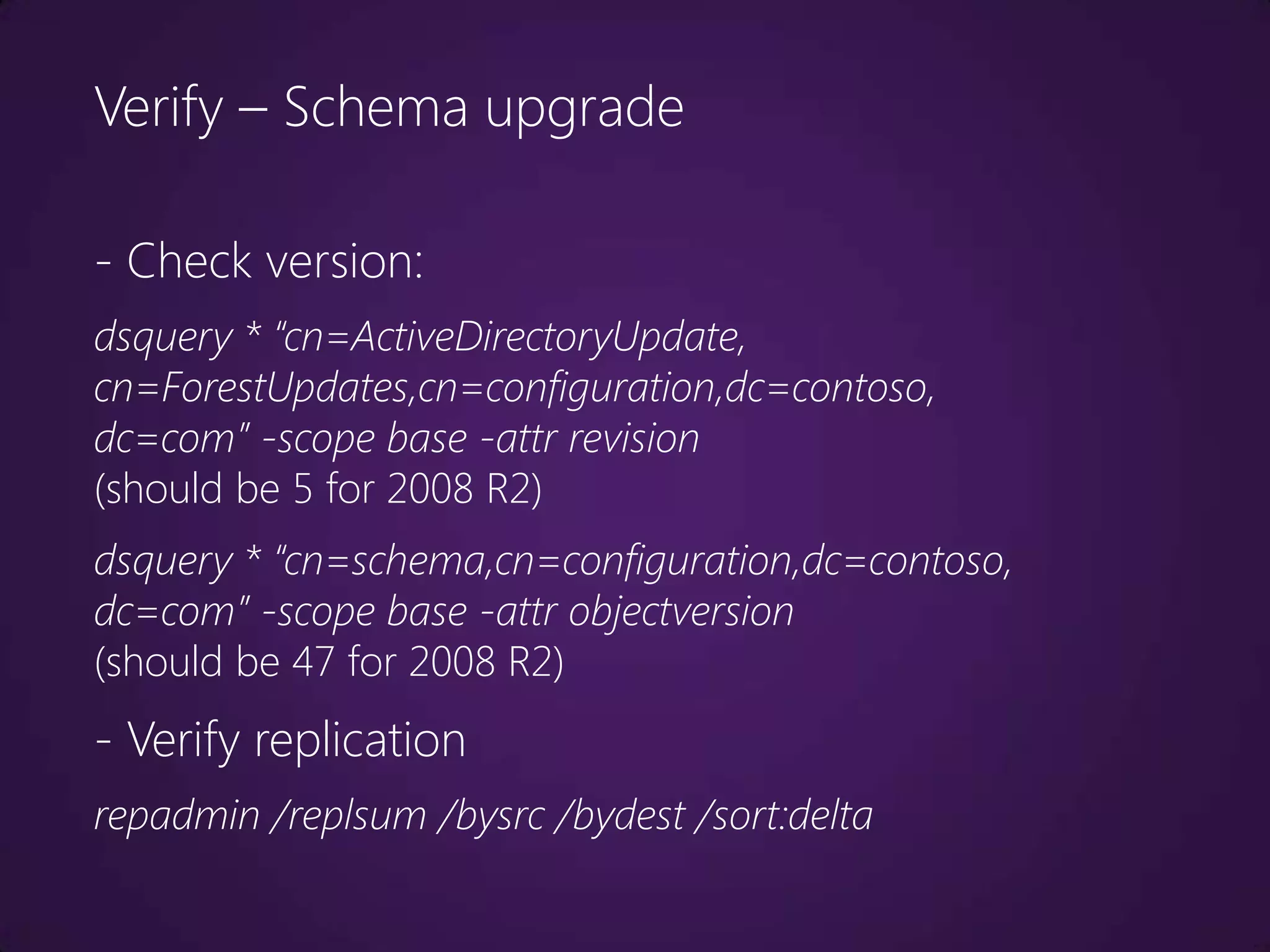
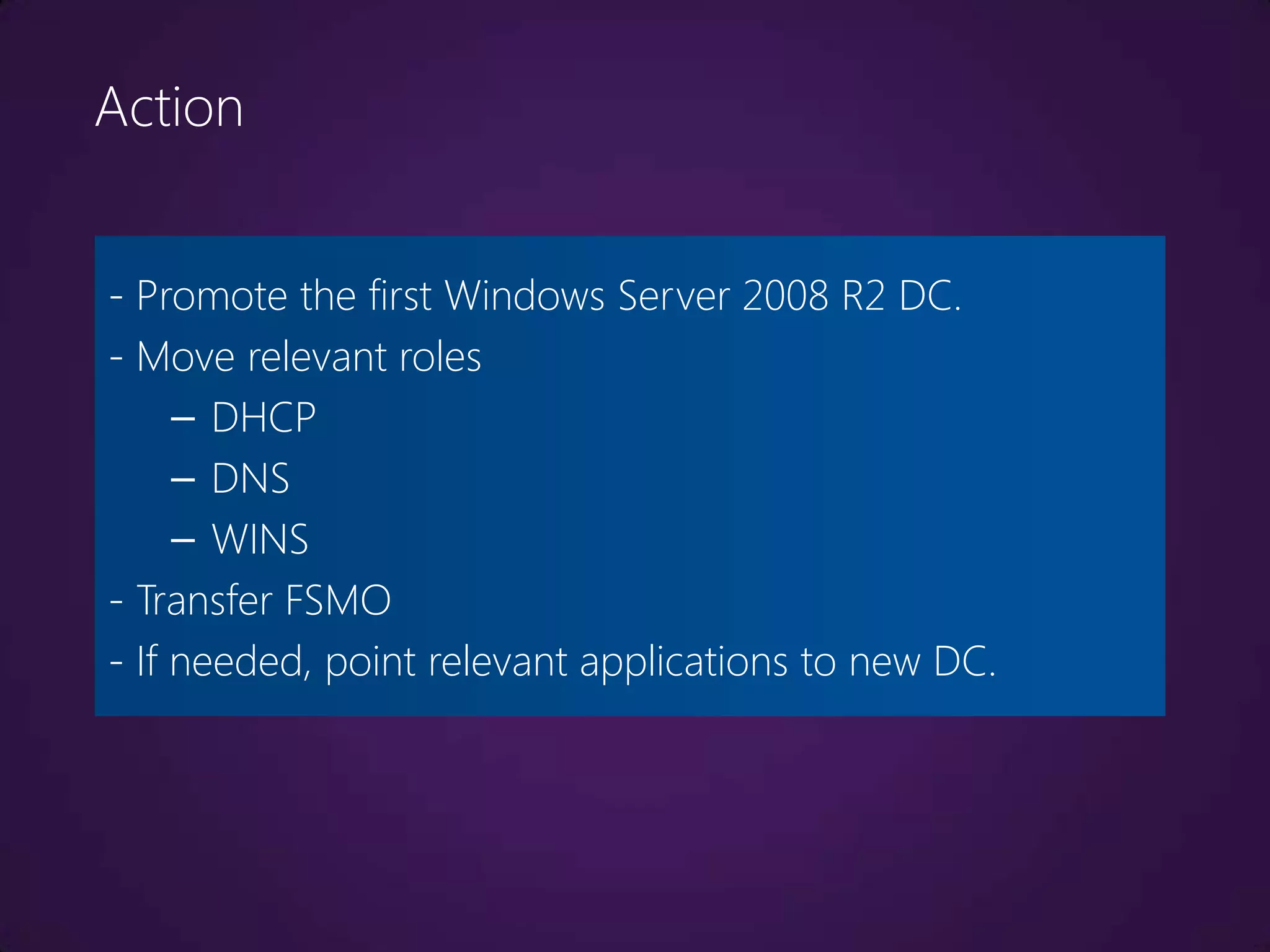
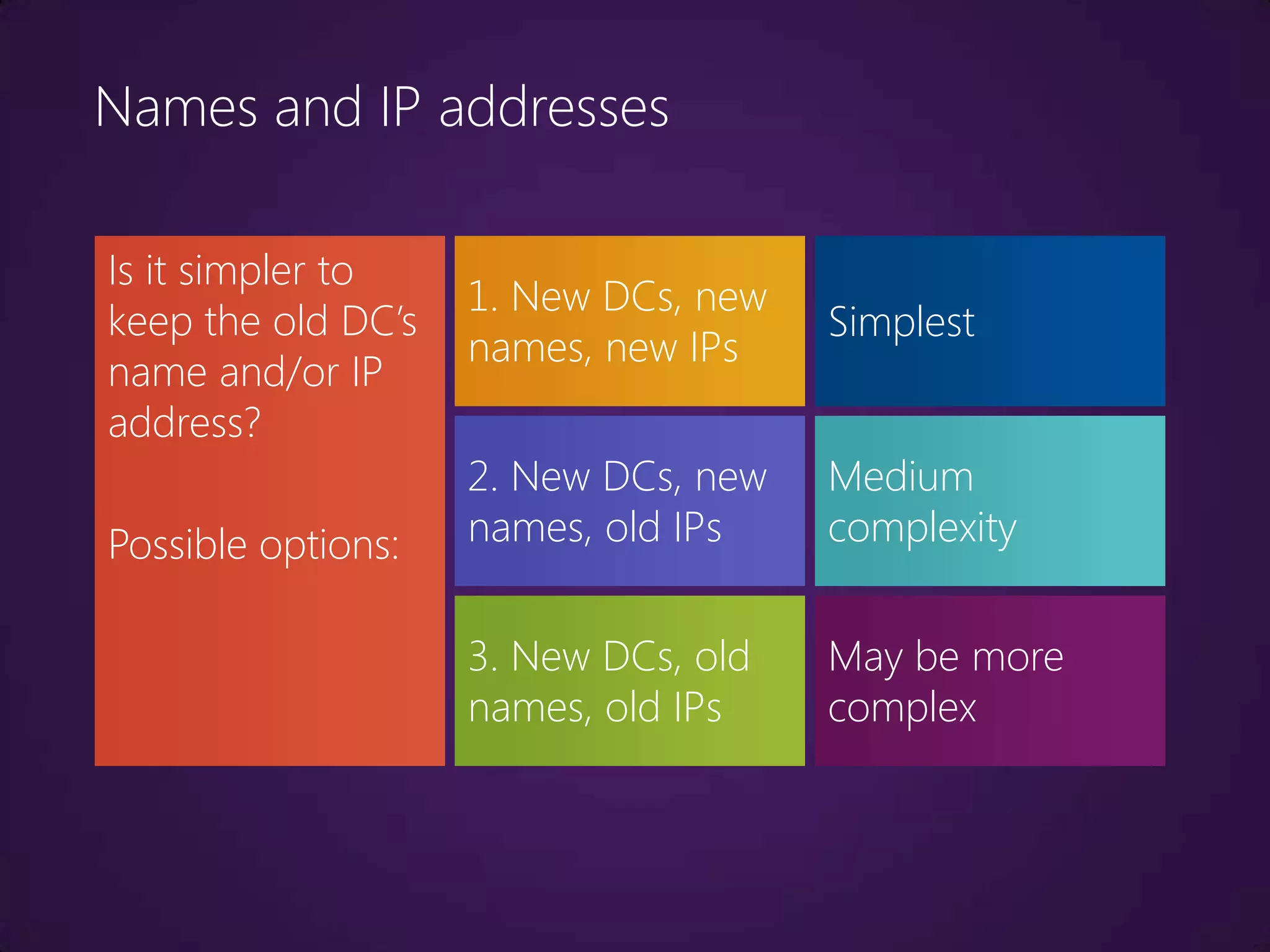
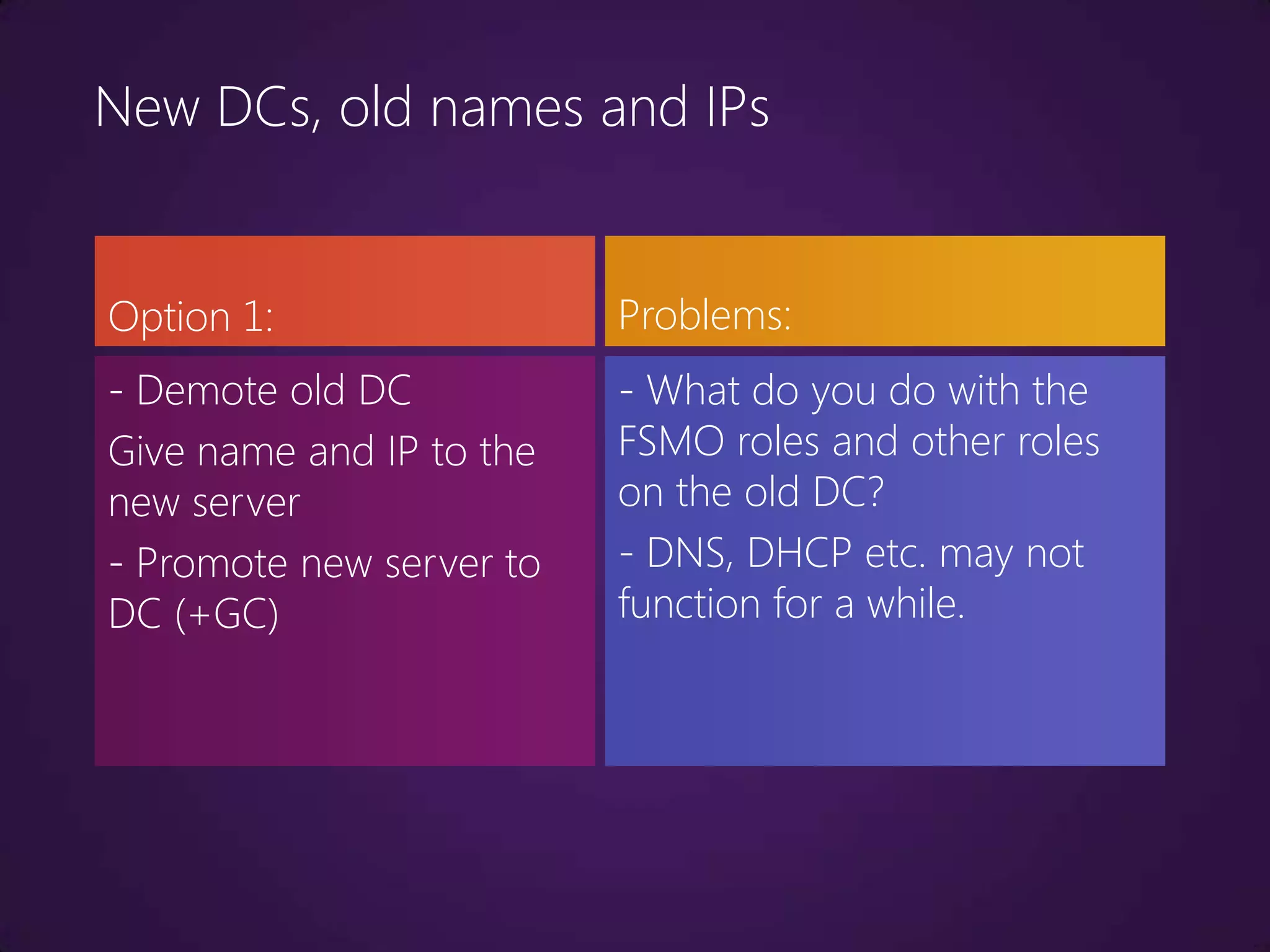
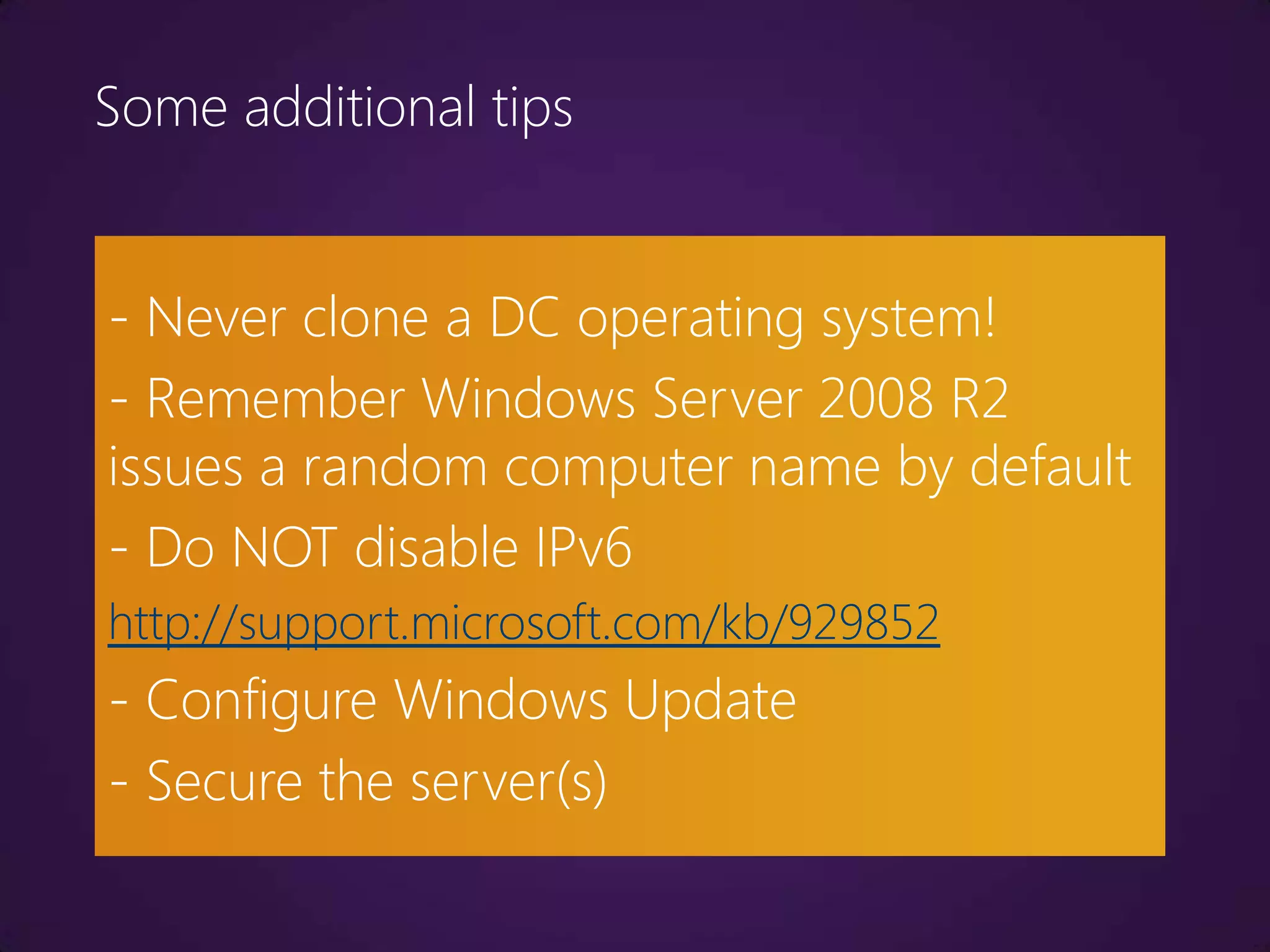
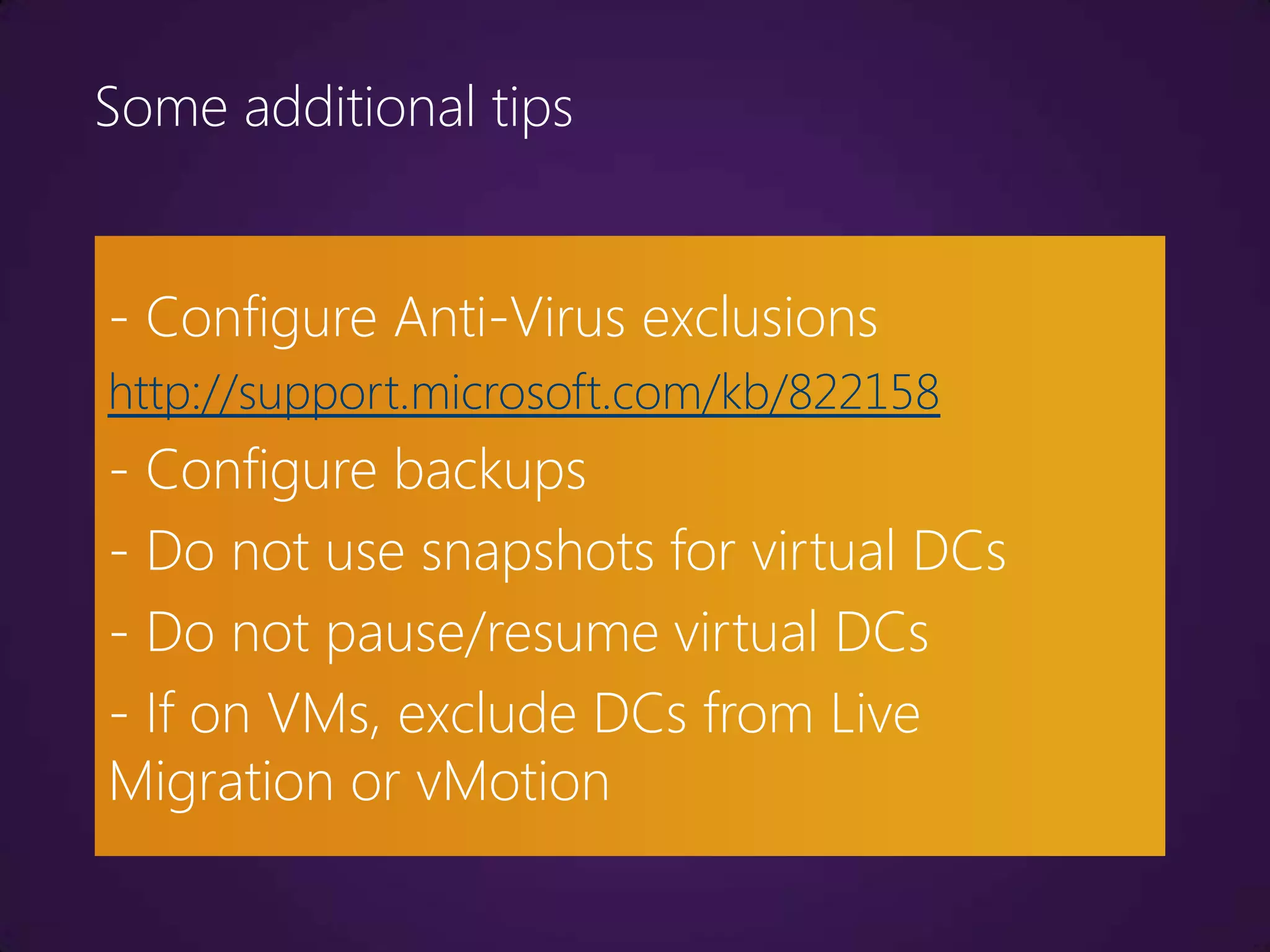
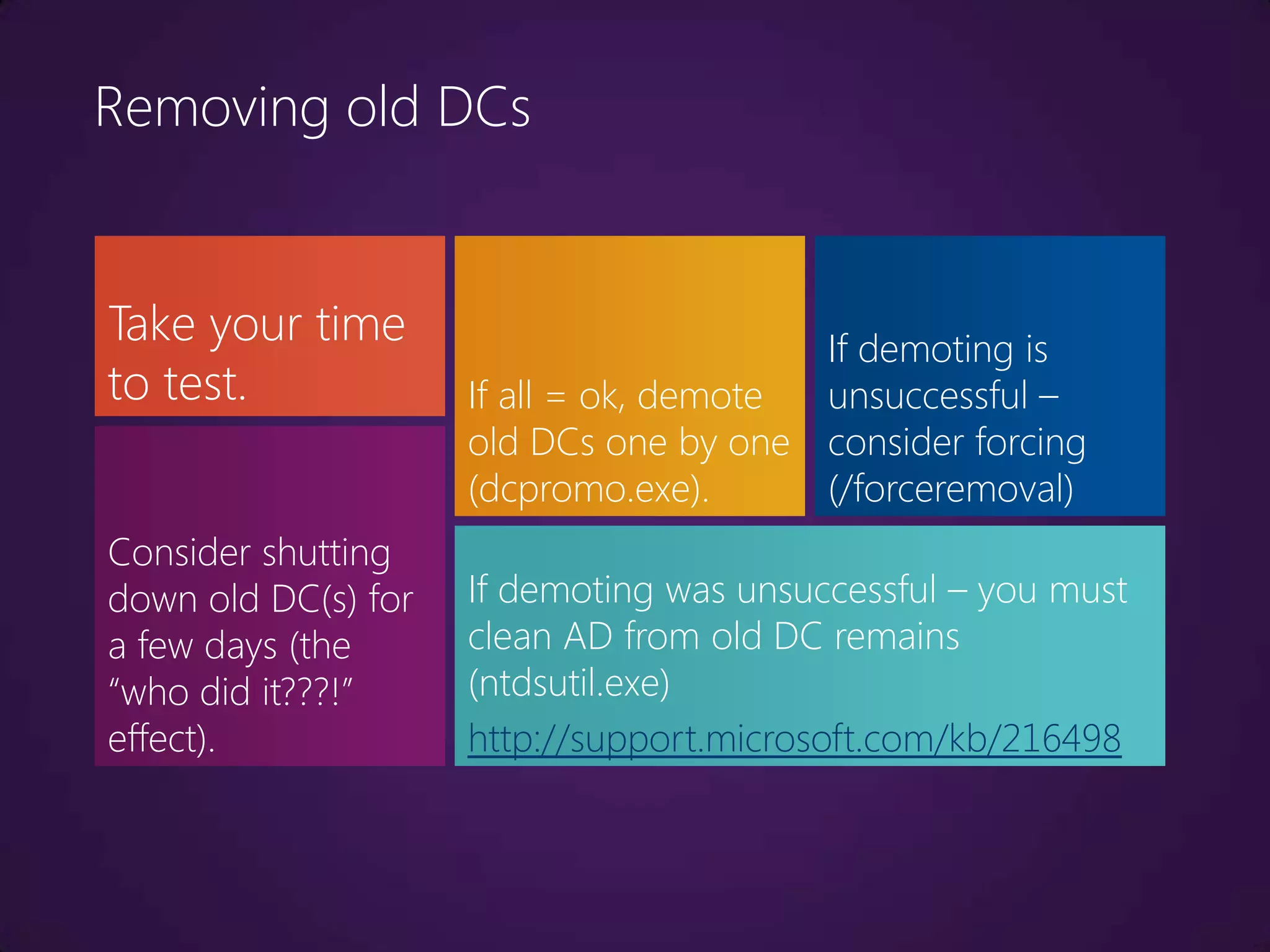
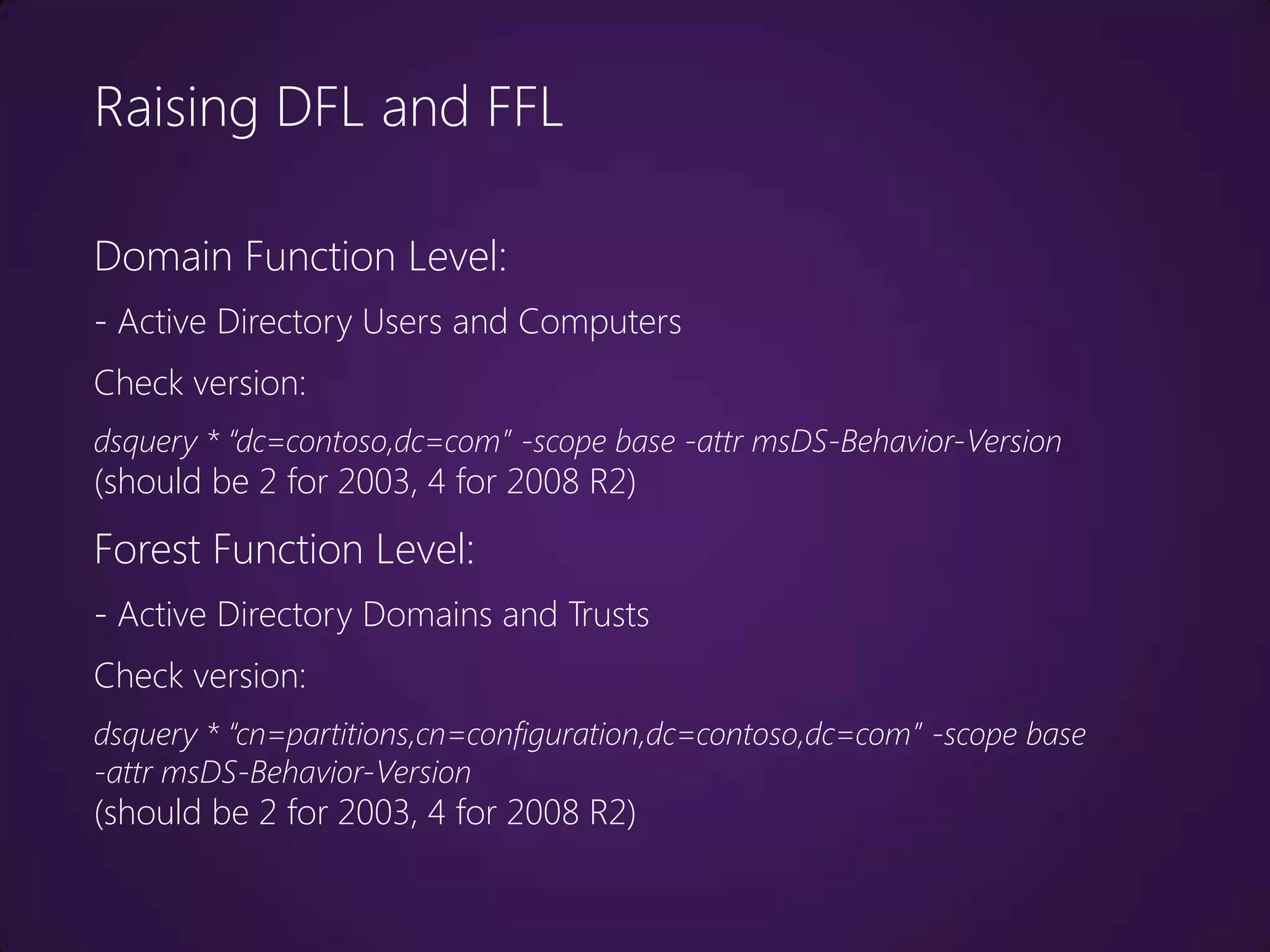
This document outlines the process of upgrading from Windows Server 2003 to Windows Server 2008 R2, focusing on the importance of planning, testing, and performing backups prior to the upgrade. It covers various factors such as Active Directory enhancements, schema upgrades, and potential issues that may arise, as well as best practices for ensuring a smooth transition. The document emphasizes the need for thorough preparation and caution when demoting old domain controllers and raising domain and forest function levels.