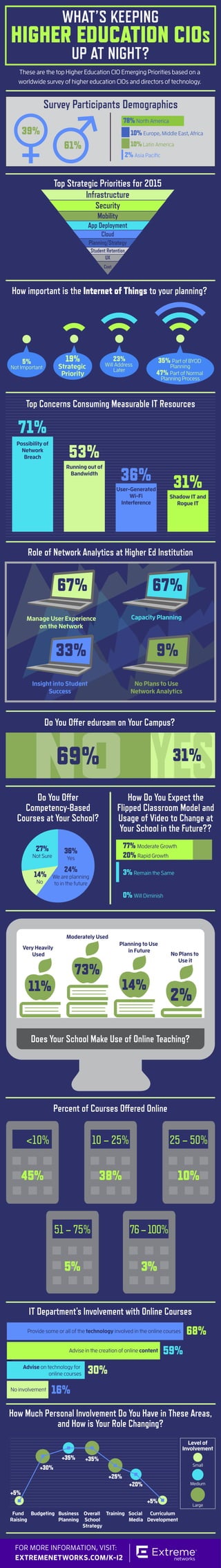
What's Keeping Higher Education CIOs Up at Night
•
3 likes•3,858 views
These are the top Higher Education CIO Emerging Priorities based on a worldwide survey of higher education CIOs and directors of technology.
Report
Share
Report
Share
Recommended
Gartner’s Top 10 Strategic Technologies Impacting Education in 2015

This document discusses 10 important technologies that Gartner recommends higher education CIOs plan for in 2015: 1) adaptive learning 2) adaptive e-textbooks 3) customer relationship management 4) big data 5) sourcing strategies 6) open exo-structure 7) open microcredentials 8) digital assessment 9) mobility solutions and 10) social learning. For each technology, the document provides examples of how Extreme Networks solutions can help address them and links to related blog posts for further information.
The Immediate Results of Purview - Application Analytics

Purview, from Extreme Networks, is a network-powered applications analytics solution that delivers business intelligence, optimized network management, and an improved security posture to any organization.
Leveraging Hospital Network Analytics

Purview is a network analytics solution from Extreme Networks that provides business intelligence, optimized network management, and improved security. It transforms the network into a strategic asset by extracting real-time insights without impacting performance. Purview gives organizations holistic visibility of application use across private and public clouds in a single dashboard, helps measure user experiences, enhances network architecture, accelerates troubleshooting, and assures security and compliance.
CompTIA Trends in Mobility

CompTIA’s 3rd Annual Trends in Enterprise Mobility study was conducted to build on previous CompTIA research in the mobility space and further explore mobility trends, challenges, and opportunities.
7 Best Practices to Protect Critical Business Information [Infographic]![7 Best Practices to Protect Critical Business Information [Infographic]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![7 Best Practices to Protect Critical Business Information [Infographic]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Is your organization ready for today’s security challenges? You need a policy-driven information security approach that you can enforce and monitor. Read this infographic and follow the 7 best practices to protect your company’s critical business information.
Student Mobile Workspaces Infographic

The rapid evolution of technology is changing the way we learn, work and educate. Mobile students need mobile workspaces with on-demand, secure access to the apps, data and services they require, expanding beyond traditional methods to promote independent and exploratory learning – without compromising security or compliance.
Learn more at: http://bit.ly/1vdmhJF
Cisco Cloud-Scale Innovation Infographic

Software innovations are needed to handle the increasing amounts of data being processed at the network edge. New technologies allow for more visibility and control over network traffic through real-time telemetry and segment routing. Automating configuration, policies, and software upgrades through standard-based data models helps networks run more efficiently and dependably to keep pace with growing mobility and data usage.
Application Strategies for the Connected Enterprise

Todd Bouman, VP, Product Marketing Samsung Enterprise Business Division, discusses application strategies for connected enterprises at Gartner Symposium/ITxpo 2014.
Recommended
Gartner’s Top 10 Strategic Technologies Impacting Education in 2015

This document discusses 10 important technologies that Gartner recommends higher education CIOs plan for in 2015: 1) adaptive learning 2) adaptive e-textbooks 3) customer relationship management 4) big data 5) sourcing strategies 6) open exo-structure 7) open microcredentials 8) digital assessment 9) mobility solutions and 10) social learning. For each technology, the document provides examples of how Extreme Networks solutions can help address them and links to related blog posts for further information.
The Immediate Results of Purview - Application Analytics

Purview, from Extreme Networks, is a network-powered applications analytics solution that delivers business intelligence, optimized network management, and an improved security posture to any organization.
Leveraging Hospital Network Analytics

Purview is a network analytics solution from Extreme Networks that provides business intelligence, optimized network management, and improved security. It transforms the network into a strategic asset by extracting real-time insights without impacting performance. Purview gives organizations holistic visibility of application use across private and public clouds in a single dashboard, helps measure user experiences, enhances network architecture, accelerates troubleshooting, and assures security and compliance.
CompTIA Trends in Mobility

CompTIA’s 3rd Annual Trends in Enterprise Mobility study was conducted to build on previous CompTIA research in the mobility space and further explore mobility trends, challenges, and opportunities.
7 Best Practices to Protect Critical Business Information [Infographic]![7 Best Practices to Protect Critical Business Information [Infographic]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![7 Best Practices to Protect Critical Business Information [Infographic]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Is your organization ready for today’s security challenges? You need a policy-driven information security approach that you can enforce and monitor. Read this infographic and follow the 7 best practices to protect your company’s critical business information.
Student Mobile Workspaces Infographic

The rapid evolution of technology is changing the way we learn, work and educate. Mobile students need mobile workspaces with on-demand, secure access to the apps, data and services they require, expanding beyond traditional methods to promote independent and exploratory learning – without compromising security or compliance.
Learn more at: http://bit.ly/1vdmhJF
Cisco Cloud-Scale Innovation Infographic

Software innovations are needed to handle the increasing amounts of data being processed at the network edge. New technologies allow for more visibility and control over network traffic through real-time telemetry and segment routing. Automating configuration, policies, and software upgrades through standard-based data models helps networks run more efficiently and dependably to keep pace with growing mobility and data usage.
Application Strategies for the Connected Enterprise

Todd Bouman, VP, Product Marketing Samsung Enterprise Business Division, discusses application strategies for connected enterprises at Gartner Symposium/ITxpo 2014.
Successful Strategies for Secure, Private and Reliable Wireless Networks

With the rise of mobile platforms, the increasing numbers of smartphones or tablet endpoints, and increasing needs for secure and private wireless connectivity, building and managing the networks that make it possible to control the mobile onslaught is key for any successful organization. This webinar will detail the course that leading organizations take in optimizing the performance of their wireless networks, securing both the network edge and core, accommodating the influx of tablets and smartphones (including the trend of BYOD or Bring Your Own Device), and smoothly integrating with next-generation wireless broadband LTE and 4G networks. We’ll also find out how one organization used Best-in-Class practices to implement and manage their own secure private wireless network.
Disruptive Technology

1. The document discusses how a new disruptive technology could impact organizations if employees begin using it and existing systems are not compatible.
2. Compatibility issues between the new technology and current software/systems could cause problems and potentially leave some organizations behind.
3. If the new technology becomes widely adopted, some existing software may become obsolete, which could create issues until compatibility is resolved.
The new tech wave of mission innovation

This document discusses Microsoft Azure and how it can help government agencies with cloud computing solutions. It mentions that Azure allows open and hybrid development that can be deployed both in the cloud and on-premises. It also discusses using data-driven intelligence from Azure to power decisions and applications. The document notes that Azure provides tools to protect missions and accelerate app innovation. It specifies that Azure Government supports the Defense Federal Acquisition Regulation Supplement. Finally, it briefly mentions using IoT solutions for public safety, justice and citizen services and that Azure Blueprints can help address FedRAMP security controls requirements.
The next tech wave of mission innovation

This document discusses Microsoft Azure and how it can help government agencies with open and hybrid cloud solutions, data-driven intelligence powered by insights, trust and security, accelerating app innovation, support for Defense Federal Acquisition Regulation Supplement, transforming government with IoT solutions in public safety and justice and citizen services, Azure Blueprints that provide templates and tools to focus on security over paperwork, and partnerships to help address FedRAMP controls requirements.
Extreme Networks SDN Innovation Challenge

The document discusses Extreme Networks' SDN Innovation Challenge. It provides details on Extreme's SDN platform and ecosystem including its network abstraction layer, southbound APIs to network elements, and northbound APIs. It outlines the timeline for the challenge and indicates there will be awards for winners. It encourages participants to register on the provided URL and contact email and use the provided hashtag on social media.
The Growing U.S. IT Productivity Gap

While investment in information technology has increased, productivity growth has slowed since the 1990s according to U.S. government data. This "productivity gap" is estimated to cost $2.7 trillion annually and is caused by older infrastructure struggling to handle newer mobile and cloud technologies, and over half of IT spending going to operations and maintenance rather than innovation. Closing the gap requires focusing spending on the "technology frontier" of innovative firms that are 3-4% more productive, and streamlining the use of technologies like cloud, mobile, and data management to improve business metrics and competitiveness.
Wireless Display 101 Lesson 2

This document discusses wireless display technology and its benefits over traditional wired display connections. It introduces the Miracast wireless display standard and explains how it simplifies displaying information in meeting rooms or classrooms by eliminating frustrations from connecting devices. While consumer media players also enable wireless display, the document notes that Miracast is better-suited for enterprise use as it supports security protocols, device management, and does not rely on an internet connection like consumer options. Miracast wireless display is also natively supported by many device types.
E itt i360 how to implementation

Some idea for implementing Insight 360.
Bill McIntosh
Authorized eInstruction by Turning Technologies Consultant
Phone :843-442-8888
Email : WKMcIntosh@Comcast.net
ARC Facilities - 5 FM Tech Tips Webinar

For video, check us out at https://youtu.be/mYrM5SPQVlg
You'll learn how to:
- Optimize your information for digital transformation.
- Leverage technology for improved emergency response.
- Instantly access information to enhance the workplace environment.
- Use technology to anticipate issues before they become a problem.
Expressworks Perspective on Human Behavior and Cyber Security

Want to understand how we incorporate behavior science and cyber security? Download the presentation we gave to the Center for Medicare and Medicaid Services’ Security Control Oversight & Update Training (CSCOUT) conference in August, 2015.
A Rise of Citizen Application Developers

A rise of citizen application developers poses data, security and integration challenges. Additionally, three out of four IT decision makers believe an enterprise low-code platform is the solution to mitigate risks.
Learn more about empowering Citizen Developers with low-code: http://ap.pn/2lbSmVF
GWAVACon 2015: GWAVA - Why Unified Archiving Pays Off…

This document summarizes a presentation about unified archiving. It discusses how employees communicate through a variety of platforms and locations. It notes that digital business data is growing 40-60% each year. The presentation outlines the value of unified archiving in improving productivity, ensuring compliance and reducing costs. It provides details on how unified archiving can retain email, mobile data, and social media content. It emphasizes that managing data efficiently has become essential.
ePlus Enabling a Total Healthcare IT Transformation to Deliver the Future of ...

ePlus can help healthcare organizations design and deploy a full suite of IT solutions to address key concerns in patient care like improving clinical outcomes, data interoperability, and patient safety. This includes implementing an electronic medical record system, developing strategies for data management and sharing, enabling personalized medicine through genomic data, and providing mobility and remote access for patients and physicians. ePlus offers consulting, managed services, and flexible consumption-based funding models to support healthcare organizations with their IT transformations.
Cloud Security for Dummies Webinar — The Identity Edition

Join "Cloud Security for Dummies" authors Ravi Ithal and Krishna Narayanaswamy, along with Patrick Harding, CTO from Ping Identity for this special “Identity Edition” of the Cloud Security for Dummies webinar series.
In this panel-style discussion, the experts will compare notes, debate approaches, and share stories from the cloud security and identity and access management front lines. IT security professionals will walk away with best practices on:
- Finding and assessing risk of all cloud apps running in your enterprise
- Onboarding new apps and bringing them into the secure Single Sign On fold
- Using identity to enable access and enforce usage and content policies
- Dealing with security issues such as poor reputation users and compromised accounts
- Communicating and coaching users
Three Keys to Building a Secure Mobile Infrastructure in Government Environments

Companies today have distributed mobile workforces and employees who are connecting to the corporate network via a large number of devices. These employees are located all over the globe, and they need seamless access to their information.
This creates pressure on IT to figure out how to deliver the right business services and data to users, and to deliver these in a way that is efficient, secure and auditable for IT. Moreover, the experience must be productive for users no matter what device they are using to connect from.
Horizon Workspace 1.5 is uniquely positioned to deliver on these objectives.
5 Steps to Successful BYOD Implementation

We discuss five steps your organization can take to assure BYOD's productivity and make your business move faster while remaining secure.
Making Cloud Security Part of Your DNA Webinar Slides

To watch the full Making Cloud Security Part of Your DNA webinar video, please go to: https://resources.netskope.com/h/i/65967799-making-cloud-security-part-of-your-dna
Summary:
As Chief Security Officer for leading cancer diagnostic company Genomic Health, Craig Guinasso makes cloud a strategic advantage while solving some of today’s most complex security challenges.
Join Craig, along with Sanjay Beri, CEO of Netskope, Missy Krasner, Managing Director of Healthcare at Box, and David Baker, CSO of Okta, for a webinar on the top five strategies that healthcare technology leaders should adopt to get the most out of the cloud while also protecting patient health data and keeping their organizations compliant.
In this powerpoint, you will get a glimpse into the webinar where we discussed how to:
- Think about cloud services in relation to business objectives
- Triage Shadow IT and consolidate on the most enterprise-ready cloud services
- Create checks and policies to identify and prevent PHI leaks
- Turn their business stakeholders into security champions
Securing medical apps in the age of covid final

The COVID-19 pandemic has drastically altered the connected healthcare landscape, accelerating the usage of telemedicine and other remote healthcare delivery systems by as much as 11,000% for some populations. How has this unprecedented push affected healthcare and medical device application security? The security team at Intertrust recently analyzed 100 Android and iOS medical apps to find out.
In this webinar, we'll discuss:
Medical application and device threat trends
The top mHealth security vulnerabilities uncovered in our analysis
Strategies to keep your mHealth apps safe
Future advances in digital healthcare and how your security can evolve with it
Implementing next generation mobile app strategies with Seqrite MDM

This document discusses implementing mobile device management strategies using Seqrite MDM. It introduces mobile device management and its need in today's enterprise scenarios. Seqrite MDM provides centralized control over apps, monitoring of data usage and recommended apps. It allows blocking access to certain apps either fully or partially based on categories. Case studies show how Seqrite MDM helped organizations control data usage on mobile devices by restricting unnecessary apps and streaming. Upcoming features will include policy changes based on location, WiFi network and time zones.
Why Extreme - Be Part of Something BIG

The document is a recruitment advertisement for Extreme Networks that highlights the company's culture, products, customers, growth, and opportunities. It summarizes that Extreme Networks encourages transparency and teamwork which leads to great products, has over 20,000 delighted customers and 1600 employees, and experienced 130% stock growth in the past year. It invites candidates to visit their careers page and join their growing company in shaping the future of networking technology.
Mobility Trends Impacting Healthcare

Extreme's Mike Leibovitz explains how tomorrow's mobility trends are impacting technology in healthcare.
#HIMSS16
8 Technologies and Trends to Inspire Creativity and Enhance Teaching

This document discusses virtual reality and augmented reality. It provides examples of how VR and AR are currently being used in various fields such as education, medicine, tourism, and more. Key information includes definitions of VR and AR, descriptions of technologies like Google Cardboard and zSpace, and specific applications in areas like virtual tours, therapy, and more immersive learning experiences. Overall, the document outlines the growing potential for VR and AR across many industries including opportunities for interactive and engaging education.
More Related Content
What's hot
Successful Strategies for Secure, Private and Reliable Wireless Networks

With the rise of mobile platforms, the increasing numbers of smartphones or tablet endpoints, and increasing needs for secure and private wireless connectivity, building and managing the networks that make it possible to control the mobile onslaught is key for any successful organization. This webinar will detail the course that leading organizations take in optimizing the performance of their wireless networks, securing both the network edge and core, accommodating the influx of tablets and smartphones (including the trend of BYOD or Bring Your Own Device), and smoothly integrating with next-generation wireless broadband LTE and 4G networks. We’ll also find out how one organization used Best-in-Class practices to implement and manage their own secure private wireless network.
Disruptive Technology

1. The document discusses how a new disruptive technology could impact organizations if employees begin using it and existing systems are not compatible.
2. Compatibility issues between the new technology and current software/systems could cause problems and potentially leave some organizations behind.
3. If the new technology becomes widely adopted, some existing software may become obsolete, which could create issues until compatibility is resolved.
The new tech wave of mission innovation

This document discusses Microsoft Azure and how it can help government agencies with cloud computing solutions. It mentions that Azure allows open and hybrid development that can be deployed both in the cloud and on-premises. It also discusses using data-driven intelligence from Azure to power decisions and applications. The document notes that Azure provides tools to protect missions and accelerate app innovation. It specifies that Azure Government supports the Defense Federal Acquisition Regulation Supplement. Finally, it briefly mentions using IoT solutions for public safety, justice and citizen services and that Azure Blueprints can help address FedRAMP security controls requirements.
The next tech wave of mission innovation

This document discusses Microsoft Azure and how it can help government agencies with open and hybrid cloud solutions, data-driven intelligence powered by insights, trust and security, accelerating app innovation, support for Defense Federal Acquisition Regulation Supplement, transforming government with IoT solutions in public safety and justice and citizen services, Azure Blueprints that provide templates and tools to focus on security over paperwork, and partnerships to help address FedRAMP controls requirements.
Extreme Networks SDN Innovation Challenge

The document discusses Extreme Networks' SDN Innovation Challenge. It provides details on Extreme's SDN platform and ecosystem including its network abstraction layer, southbound APIs to network elements, and northbound APIs. It outlines the timeline for the challenge and indicates there will be awards for winners. It encourages participants to register on the provided URL and contact email and use the provided hashtag on social media.
The Growing U.S. IT Productivity Gap

While investment in information technology has increased, productivity growth has slowed since the 1990s according to U.S. government data. This "productivity gap" is estimated to cost $2.7 trillion annually and is caused by older infrastructure struggling to handle newer mobile and cloud technologies, and over half of IT spending going to operations and maintenance rather than innovation. Closing the gap requires focusing spending on the "technology frontier" of innovative firms that are 3-4% more productive, and streamlining the use of technologies like cloud, mobile, and data management to improve business metrics and competitiveness.
Wireless Display 101 Lesson 2

This document discusses wireless display technology and its benefits over traditional wired display connections. It introduces the Miracast wireless display standard and explains how it simplifies displaying information in meeting rooms or classrooms by eliminating frustrations from connecting devices. While consumer media players also enable wireless display, the document notes that Miracast is better-suited for enterprise use as it supports security protocols, device management, and does not rely on an internet connection like consumer options. Miracast wireless display is also natively supported by many device types.
E itt i360 how to implementation

Some idea for implementing Insight 360.
Bill McIntosh
Authorized eInstruction by Turning Technologies Consultant
Phone :843-442-8888
Email : WKMcIntosh@Comcast.net
ARC Facilities - 5 FM Tech Tips Webinar

For video, check us out at https://youtu.be/mYrM5SPQVlg
You'll learn how to:
- Optimize your information for digital transformation.
- Leverage technology for improved emergency response.
- Instantly access information to enhance the workplace environment.
- Use technology to anticipate issues before they become a problem.
Expressworks Perspective on Human Behavior and Cyber Security

Want to understand how we incorporate behavior science and cyber security? Download the presentation we gave to the Center for Medicare and Medicaid Services’ Security Control Oversight & Update Training (CSCOUT) conference in August, 2015.
A Rise of Citizen Application Developers

A rise of citizen application developers poses data, security and integration challenges. Additionally, three out of four IT decision makers believe an enterprise low-code platform is the solution to mitigate risks.
Learn more about empowering Citizen Developers with low-code: http://ap.pn/2lbSmVF
GWAVACon 2015: GWAVA - Why Unified Archiving Pays Off…

This document summarizes a presentation about unified archiving. It discusses how employees communicate through a variety of platforms and locations. It notes that digital business data is growing 40-60% each year. The presentation outlines the value of unified archiving in improving productivity, ensuring compliance and reducing costs. It provides details on how unified archiving can retain email, mobile data, and social media content. It emphasizes that managing data efficiently has become essential.
ePlus Enabling a Total Healthcare IT Transformation to Deliver the Future of ...

ePlus can help healthcare organizations design and deploy a full suite of IT solutions to address key concerns in patient care like improving clinical outcomes, data interoperability, and patient safety. This includes implementing an electronic medical record system, developing strategies for data management and sharing, enabling personalized medicine through genomic data, and providing mobility and remote access for patients and physicians. ePlus offers consulting, managed services, and flexible consumption-based funding models to support healthcare organizations with their IT transformations.
Cloud Security for Dummies Webinar — The Identity Edition

Join "Cloud Security for Dummies" authors Ravi Ithal and Krishna Narayanaswamy, along with Patrick Harding, CTO from Ping Identity for this special “Identity Edition” of the Cloud Security for Dummies webinar series.
In this panel-style discussion, the experts will compare notes, debate approaches, and share stories from the cloud security and identity and access management front lines. IT security professionals will walk away with best practices on:
- Finding and assessing risk of all cloud apps running in your enterprise
- Onboarding new apps and bringing them into the secure Single Sign On fold
- Using identity to enable access and enforce usage and content policies
- Dealing with security issues such as poor reputation users and compromised accounts
- Communicating and coaching users
Three Keys to Building a Secure Mobile Infrastructure in Government Environments

Companies today have distributed mobile workforces and employees who are connecting to the corporate network via a large number of devices. These employees are located all over the globe, and they need seamless access to their information.
This creates pressure on IT to figure out how to deliver the right business services and data to users, and to deliver these in a way that is efficient, secure and auditable for IT. Moreover, the experience must be productive for users no matter what device they are using to connect from.
Horizon Workspace 1.5 is uniquely positioned to deliver on these objectives.
5 Steps to Successful BYOD Implementation

We discuss five steps your organization can take to assure BYOD's productivity and make your business move faster while remaining secure.
Making Cloud Security Part of Your DNA Webinar Slides

To watch the full Making Cloud Security Part of Your DNA webinar video, please go to: https://resources.netskope.com/h/i/65967799-making-cloud-security-part-of-your-dna
Summary:
As Chief Security Officer for leading cancer diagnostic company Genomic Health, Craig Guinasso makes cloud a strategic advantage while solving some of today’s most complex security challenges.
Join Craig, along with Sanjay Beri, CEO of Netskope, Missy Krasner, Managing Director of Healthcare at Box, and David Baker, CSO of Okta, for a webinar on the top five strategies that healthcare technology leaders should adopt to get the most out of the cloud while also protecting patient health data and keeping their organizations compliant.
In this powerpoint, you will get a glimpse into the webinar where we discussed how to:
- Think about cloud services in relation to business objectives
- Triage Shadow IT and consolidate on the most enterprise-ready cloud services
- Create checks and policies to identify and prevent PHI leaks
- Turn their business stakeholders into security champions
Securing medical apps in the age of covid final

The COVID-19 pandemic has drastically altered the connected healthcare landscape, accelerating the usage of telemedicine and other remote healthcare delivery systems by as much as 11,000% for some populations. How has this unprecedented push affected healthcare and medical device application security? The security team at Intertrust recently analyzed 100 Android and iOS medical apps to find out.
In this webinar, we'll discuss:
Medical application and device threat trends
The top mHealth security vulnerabilities uncovered in our analysis
Strategies to keep your mHealth apps safe
Future advances in digital healthcare and how your security can evolve with it
Implementing next generation mobile app strategies with Seqrite MDM

This document discusses implementing mobile device management strategies using Seqrite MDM. It introduces mobile device management and its need in today's enterprise scenarios. Seqrite MDM provides centralized control over apps, monitoring of data usage and recommended apps. It allows blocking access to certain apps either fully or partially based on categories. Case studies show how Seqrite MDM helped organizations control data usage on mobile devices by restricting unnecessary apps and streaming. Upcoming features will include policy changes based on location, WiFi network and time zones.
What's hot (19)
Successful Strategies for Secure, Private and Reliable Wireless Networks

Successful Strategies for Secure, Private and Reliable Wireless Networks
Expressworks Perspective on Human Behavior and Cyber Security

Expressworks Perspective on Human Behavior and Cyber Security
GWAVACon 2015: GWAVA - Why Unified Archiving Pays Off…

GWAVACon 2015: GWAVA - Why Unified Archiving Pays Off…
ePlus Enabling a Total Healthcare IT Transformation to Deliver the Future of ...

ePlus Enabling a Total Healthcare IT Transformation to Deliver the Future of ...
Cloud Security for Dummies Webinar — The Identity Edition

Cloud Security for Dummies Webinar — The Identity Edition
Three Keys to Building a Secure Mobile Infrastructure in Government Environments

Three Keys to Building a Secure Mobile Infrastructure in Government Environments
Making Cloud Security Part of Your DNA Webinar Slides

Making Cloud Security Part of Your DNA Webinar Slides
Implementing next generation mobile app strategies with Seqrite MDM

Implementing next generation mobile app strategies with Seqrite MDM
Viewers also liked
Why Extreme - Be Part of Something BIG

The document is a recruitment advertisement for Extreme Networks that highlights the company's culture, products, customers, growth, and opportunities. It summarizes that Extreme Networks encourages transparency and teamwork which leads to great products, has over 20,000 delighted customers and 1600 employees, and experienced 130% stock growth in the past year. It invites candidates to visit their careers page and join their growing company in shaping the future of networking technology.
Mobility Trends Impacting Healthcare

Extreme's Mike Leibovitz explains how tomorrow's mobility trends are impacting technology in healthcare.
#HIMSS16
8 Technologies and Trends to Inspire Creativity and Enhance Teaching

This document discusses virtual reality and augmented reality. It provides examples of how VR and AR are currently being used in various fields such as education, medicine, tourism, and more. Key information includes definitions of VR and AR, descriptions of technologies like Google Cardboard and zSpace, and specific applications in areas like virtual tours, therapy, and more immersive learning experiences. Overall, the document outlines the growing potential for VR and AR across many industries including opportunities for interactive and engaging education.
The Future of Network Management

Cloud-managed networking delivers a platform of engagement that dynamically adjusts to business transformation and growth.
Comunicación Punto de Venta y Digitalización en sector Deportivo (Marcas y Re...

El documento describe cómo la experiencia de compra en el punto de venta se está digitalizando. Los compradores de hoy están más informados y buscan inspiración e interacción personalizada. La digitalización permite ofrecer estas experiencias a través de señalización digital, aplicaciones móviles y más. Esto ayuda a las marcas a comunicarse mejor con los compradores y aumentar las ventas.
Registros Personales de Salud

Este documento describe el sistema de Registros Personales de Salud implementado en el Hospital Universitario Quirón Dexeus. El sistema tiene como objetivos empoderar al paciente dándole acceso a su información médica de forma ubicua y segura, mejorar la adherencia a tratamientos, y reducir costes. Las funcionalidades incluyen ver el perfil, carpeta de salud con documentos médicos, solicitar citas y documentos, ver el equipo médico, y nuevas funcionalidades como integración con videoconferencia. Los pacientes opinan positivamente sobre la
Wi fi runners retail smart wifi

This document discusses how smart Wi-Fi solutions for retail businesses can help boost sales and customer engagement. It outlines features like separate guest and business networks for security, content filtering for families, and compliance with regulations. Providing free Wi-Fi is shown to increase customer spending and time in venues. The solution allows businesses to collect customer data and profiles to send targeted marketing emails and texts. It also integrates with social media to boost brand awareness and engage customers' social networks. A range of tools are available for understanding customers, managing marketing campaigns, and driving repeat visits through loyalty programs.
IdRetail – Migración Mobile a Smart Device con PXTools

Este documento presenta los objetivos y conceptos clave de la migración de la aplicación IdRetail de dispositivos móviles a dispositivos inteligentes utilizando la herramienta PXTools. Los objetivos incluyen migrar la aplicación móvil a dispositivos inteligentes, potenciar PXTools y aprovechar las nuevas funciones de GeneXus Evolution 2. Se destacan consideraciones como el rediseño operativo para aprovechar mejor las capacidades táctiles y las limitaciones de eventos y código en dispositivos inteligentes.
Samsung Techwing. Business sales vertical solution retail

This document discusses Techwin's retail solution for security and video surveillance. The solution provides business insights through people counting, demographic analysis, heatmaps of foot traffic, electronic article surveillance (EAS) integration with alarms, and point of sale (POS) system integration. It also outlines the system architecture involving cameras, EAS, POS, monitoring center, and storage devices like network video recorders. Example scenarios described include people counting, searching video by POS keywords, and EAS alarm notifications. Finally, it introduces some of Techwin's network camera and recorder products that could enable this retail solution.
Presentación Soluciones DS Digital Screens

DS DIGITAL SCREENS es uno de los líderes tecnológicos mundiales dentro de los soportes de señalización digital. Creamos soluciones de última generación para las necesidades más exigentes de comunicación digital.
Carlos Martinez - PAMEM: Redisseny de rols emergents, funcions i serveis infe...

Carlos Martinez - PAMEM: Redisseny de rols emergents, funcions i serveis infe...Fòrum Català d’Informació i Salut
Carlos Martinez - PAMEM: Redisseny de rols emergents, funcions i serveis infermers Atenció PrimàriaSmart retail getting to uk brands and existing partners mike cornwell 

Smart retail getting to uk brands and existing partners. Mike Cornwell, Digital Marketing Institute. Export Finland Smart Retail UK seminar, Helsinki June 4th 2015.
Elisa Videra Smart Retail

This document discusses the concept of smart retail and how digital technologies can enhance the customer experience. It provides examples of how interactive digital displays, signage, and applications can be used at various touchpoints in the retail process to improve branding, provide product information, enable self-service options for customers, and generate analytics. Case studies are presented of companies that have implemented these smart retail solutions, such as Mobistar which saw improved customer experiences and cost savings, and Elisa Shopit which offered more versatile product testing for customers. The overall benefits highlighted include a richer digital customer experience, better brand communication and customer service, and more efficient retail operations.
Adaptación del Retail físico al shopper digital

El documento habla sobre la adaptación de los puntos de venta físicos al entorno del e-commerce. Explica que los consumidores ahora tienen más información antes de ir a la tienda y buscan una experiencia de marca. Las tiendas deben convertirse en showrooms que ofrezcan valor añadido o almacenes que faciliten el servicio. También debe haber una integración completa entre canales online y offline a través de la digitalización del espacio físico y el uso de tecnologías como beacons.
Key Insights from the 2016 Seahawks Mobility Summit

IT leaders gathered in Seattle to talk about the future of Wi-Fi and Mobility. Here, we've gathered some of their best information.
Evolución de los registros personales de salud: los casos de Noruega, Suecia ...

Evolución de los registros personales de salud: los casos de Noruega, Suecia ...Fòrum Català d’Informació i Salut
Joan rodón sesión técnica uoc-forum cis
helsenorge.no:
- Mapeo de los servicios/sistemas ya existentes (nacional, regional, proveedor)
- Ofrecer al ciudadano acceso unificado a información de alta de ingreso, informes de urgencias, diagnósticos, derivaciones, informes de pruebas de laboratorio, radiología, etc.RANDOM: La Digitalizacion de los Centros Comerciales en España. Informe ejecu...

“La Digitalización de los Centros Comerciales en España”. El informe de la consultora RANDOM basado en las opiniones y percepciones de los directivos entrevistados, pone foco en la presencia y prospectiva del Sector de los Centros Comerciales.
Destaca la rápida transformación que ya está empezando a experimentar el sector en España. Las nuevas tecnologías, ocuparán una parte importante en la experiencia del cliente y su relación con los Centros Comerciales. El estudio de RANDOM, incluye además un apartado específico con las opiniones de los directivos en relación a 12 Soluciones Digitales, un amplio abanico de innovaciones que llegan para dar respuesta a los cambios en el comportamiento del consumidor SOLOMO (Social, Local & Mobile).
Smart Lighting: LED & Sistemas de Control by Miguel Ángel Ramos

SMART ENERGY. El papel fundamental de la eficiencia energética dentro del concepto de las ciudades inteligentes.
Debido a que las ciudades son las principales emisoras de CO2 especialmente en Europa, América y Asia, esta sesión se centra en analizar los desafíos futuros que se presentan para la mejora de la eficiencia energética con el objetivo de cumplir con los compromisos adquiridos por los estados de cara al 2020 . Dentro de esta sesión se analizarán los últimos proyectos que se están implementando de cara a la producción energética mediante energías renovables , el desarrollo de nuevos modelos de gestión de las redes eléctricas existentes y la apuesta por una tecnología que reduzca la necesidad de consumo eléctrico de las ciudades con el objetivo de reducir su impacto medioambiental . Por ello , proponemos los siguientes objetivos para la sesión:
Exponer nuevas fuentes de energía no convencionales que sean respetuosas con el medio ambiente.
Dar a conocer vehículos eléctricos que se producen en serie adaptados a las necesidades de los usuarios residentes en ciudades.
Presentar las novedades en el campo de las Smart Grids y las nuevas posibilidades de almacenamiento energético que ofrecen.
Dar a conocer el impacto que tienen las nuevas tecnologías en materia energética sobre las instalaciones en las que son aplicadas así como sobre la economía de las ciudades.
Exponer las nuevas regulaciones en materia energética tanto a nivel europeo como estatal.
Infografia farmacia- pharma healthcare digital marketing (Spain)

Uso de Internet por el farmacéutico en España, Presencia Digital de la Farmacia en España.
Interacción Digital del Farmacéutico con el paciente
Interacción Digital del Farmacéutico con Laboratorio (Pharma). Retos y oportunidades
IBM Smarter Process

George Chast of IBM's Smarter Process Leadership Team presented on reinventing business operations for greater customer centricity and top-line growth using mobile, social and cloud technologies. IBM's approach focuses on enabling greater customer centricity in an age of new technologies while driving efficiency. Chast discussed how knowledge worker empowerment is vital for success and customer centricity. He outlined IBM's Smarter Process capabilities including operational decision management, business process management, and case management. Chast proposed identifying business challenges, starting with an initial project, and establishing a program to build a roadmap for process excellence.
Viewers also liked (20)
8 Technologies and Trends to Inspire Creativity and Enhance Teaching

8 Technologies and Trends to Inspire Creativity and Enhance Teaching
Comunicación Punto de Venta y Digitalización en sector Deportivo (Marcas y Re...

Comunicación Punto de Venta y Digitalización en sector Deportivo (Marcas y Re...
IdRetail – Migración Mobile a Smart Device con PXTools

IdRetail – Migración Mobile a Smart Device con PXTools
Samsung Techwing. Business sales vertical solution retail

Samsung Techwing. Business sales vertical solution retail
Carlos Martinez - PAMEM: Redisseny de rols emergents, funcions i serveis infe...

Carlos Martinez - PAMEM: Redisseny de rols emergents, funcions i serveis infe...
Smart retail getting to uk brands and existing partners mike cornwell 

Smart retail getting to uk brands and existing partners mike cornwell
Key Insights from the 2016 Seahawks Mobility Summit

Key Insights from the 2016 Seahawks Mobility Summit
Evolución de los registros personales de salud: los casos de Noruega, Suecia ...

Evolución de los registros personales de salud: los casos de Noruega, Suecia ...
RANDOM: La Digitalizacion de los Centros Comerciales en España. Informe ejecu...

RANDOM: La Digitalizacion de los Centros Comerciales en España. Informe ejecu...
Smart Lighting: LED & Sistemas de Control by Miguel Ángel Ramos

Smart Lighting: LED & Sistemas de Control by Miguel Ángel Ramos
Infografia farmacia- pharma healthcare digital marketing (Spain)

Infografia farmacia- pharma healthcare digital marketing (Spain)
Similar to What's Keeping Higher Education CIOs Up at Night
CIO Tech Poll: Tech Priorities 2018

This document summarizes the results of a survey of 186 IT leaders about their technology priorities and budgets for 2018. It found that security-related projects, like business continuity and disaster recovery, were the most important initiatives. Most respondents expected their overall IT budgets to increase in the next year. Emerging technologies like analytics, cloud computing, and IoT were areas where organizations were most open to partnering with newer vendors. The document provides details on the survey methodology and breakdown of responses by industry, job role, and technology category.
2015 Strategic Directions: Smart Utility Report

The 2015 Black & Veatch Strategic Directions: Smart Utility report explores how advances in telecommunications, automation and data analytics are changing the relationship between utilities and their customers. The report provides an analysis of important planning, investment, and security challenges and opportunities along with insights on how utilities and cities can achieve their service, resiliency and, ultimately, smart city goals.
Learn more: http://bv.com/reports/smart-utility
Logicalis Global CIO Survey 2016

Digital enablers: the challenges facing CIOs in an age of digital transformation. Research from Logicalis based on a global study of CIO pressures and priorities.
[Webinar Slides] Capture Leaders & Their Projects: We Asked, They Answered. D...![[Webinar Slides] Capture Leaders & Their Projects: We Asked, They Answered. D...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] Capture Leaders & Their Projects: We Asked, They Answered. D...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
In this webinar, exclusively for BPOs and Outsourced Service Providers, we share with you the results of our recent survey from the leaders of capture projects. Find out how Parascript works with its partners to ensure that customers improve and update their capture platform and processes.
Want to follow along with the webinar replay? Download it here for FREE: https://info.aiim.org/capture-leaders-and-their-projects-2019
The new CIO-CMO relationship in Higher Education

Extreme Networks interviewed CIOs and conducted research to find how Higher Education CIOs can work with their CMOs to lead campus digital transformation.
The Accenture CIO Mobility Survey 2012

1) The document discusses keeping up with mobility strategies and priorities for CIOs. It highlights challenges around developing a cohesive mobility strategy while balancing issues like security, costs, and fragmentation across devices and platforms.
2) According to surveys, CIOs see mobility as a high priority but face challenges developing strategies. Emerging markets see it as more of a priority likely due to fewer legacy systems.
3) To develop effective strategies, the document recommends understanding where apps are being created, integrating them cohesively, and using the strategy competitively. Process improvements and dedicated resources are also important.
Accenture CIO Mobility Survey

To gauge the perceptions of mobility among IT professionals, Accenture Research surveyed several hundred CIOs and several thousand application developers in North America, Europe, Asia and South America in January 2012. The results were startling. When asked to tally their priorities, 78 percent of CIOs placed mobility in their top five.
International Technology Adoption & Workforce Issues Study - Middle East Summary

International Technology Adoption and Workforce Issues Study for the Middle East
The study explored technology adoption, IT priorities, skills gaps, and training practices in the Middle East. Key findings include:
1) Top IT priorities for Middle Eastern businesses are IT security, updating aging computers/software, and automating business processes.
2) Over half of Middle Eastern businesses have adopted cloud computing to some degree, but face hurdles like unreliable internet access.
3) 85% of businesses believe the cybersecurity threat level is increasing due to factors like more internet-based applications.
4) Most IT staff received training in the past year, and certifications are expected to increase in importance.
2014 Software Development Survey Results 

To better understand America’s software development talent shortage and devise solutions, the nonprofit TECNA (Technology Councils of North America) partnered with the global learning leader, Apollo Education Group, and its subsidiary, University of Phoenix, to conduct a research study on software development talent acquisition, skills gaps, and educational requirements. The findings can help employers, higher education institutions, and regional technology councils improve the size, quality, and sustainability of the software development workforce. View this presentation for the full report and findings.
International Technology Adoption & Workforce Issues Study - Canadian Summary

90% of Canadian executives indicate at least some degree of gaps in IT skills at their business exists. 59% of UK executives believe the cybersecurity threat level is increasing. Find out more on how companies are adopting new technology and how it's impacting their workforce.
CompTIA 11th Annual Information Security Trends

Organizations are overwhelmingly confident in their readiness to combat security threats, but may not be prepared for dangers linked to new technology models and increasingly sophisticated threats, according to a new study released by CompTIA, the non-profit association for the information technology industry.
CompTIA's 5 Trends Shaping the Tech-Driven Workforce

Disruptive technologies and business models continue to force organizations to assess how they do business, manage staff and engage with customers. This CompTIA presentation explores five keys trends shaping the tech-driven workforce of the future.
Clarkston Consulting CIO - 2022 Survey Summary Report.pdf

The 2022 CIO Survey Summary Report provides insight into the priorities, challenges, and opportunities facing IT leaders in the consumer products, retail, and life sciences industries this year. Businesses across the world continue to face talent and labor shortages as a result of the COVID-19 pandemic, and companies within the tech industry are no different. These shortages, combined with changes to the “normal” workplace environment, have resulted in many companies rethinking and assessing their current and future challenges, opportunities, and priorities within their IT departments. In late 2021, Clarkston Consulting conducted a CIO Market Study, aiming to better understand the current priorities and challenges of upper or C-Suite level IT professionals (CIO/CISO/CTO/VP) at large companies ($350M+ revenue) in the retail, CPG, manufacturing, or life science industries. The four key objectives for the 2022 CIO Survey were to:
Understand the overall relationship between IT and other departments within the company.
Understand current IT budget distribution, technologies/platforms used, and sources for technology-specific learning and development.
Identify attributes that are important in selecting outsourcing or managed services partners, a professional services provider, or a technology platform/vendor.
Determine priorities for the coming year and understand how COVID-19 has changed priorities in recent years.
Market Study Results
Through this CIO Market Study, Clarkston was able to gain valuable insight on the current status and perceptions of IT departments, including budget, ERP usage, investments, outsourced activities, and department health; department expectations, priorities, and plans for the upcoming year; and important attributes in outsourcing and managed services, among other key findings.
The results of this survey provide a detailed view of many of the challenges that IT departments across the consumer products, retail, and life sciences industries continue to face, particularly as they navigate the ongoing effects of the COVID-19 pandemic in the workplace.
Education Strategy Forum: Research Report

This report is based on survey findings of the delegates for the Education Strategy Forum on the 26th and 27th February 2019, comprising of 308 Vice Chancellors, Directors and Heads of Department from UK Higher Education. To deepen our insights, we interviewed the highest decision makers in face-to-face and telephone interviews to discuss trends and issues being tackled by university leaders.
Information technology research trends: The future vision 

This lecture delivered by Professor Mohamed Fahmy Tolba at the monthly meeting of the Scientific Research Group in Egypt (SRGE) on Saturday 6 June 2015 at DAR ELDEYAFA - Ain Shams university
CompTIA International Trends in Cybersecurity

A CompTIA research summary overview of the behaviors, techniques, and opportunities associated with cyberecurity across 12 countries.
CIO Tech Priorities 2023_Sample Slides.pdf

The document summarizes the results of a survey of 276 IT leaders on their technology priorities for the next 12 months. Key findings include:
- 51% of respondents expect their IT budgets to increase over the next year.
- Top technologies being researched/piloted include IoT, multi-cloud management, and SDN. Least interesting are blockchain, AR/VR, and open source technologies.
- The most important project for many is cybersecurity, followed by cloud infrastructure and enterprise apps.
- Challenges to deploying new technologies include lack of skills/staff and disconnect between IT and business leadership.
2019 Intelligent Technology Index 

Organizations today are discovering new realities around the cloud and data center, IT supply chain management, the modern workplace and digital transformation. For the 2019 Insight Intelligent Technnology™ Index, we surveyed 400 IT professionals to assess how they’re optimizing technology to unlock these growth opportunities. Explore the key takeaways.
ELearning trends 2015: #2 Mobile learning

Millennials now make up over 35% of the global workforce and prefer mobile devices and more interactive learning. As they will form 50% of the workforce by 2020, organizations need to incorporate mobile learning to engage millennial employees. Mobile learning is not yet widely used in Australian businesses, but 63% plan to implement it in the future. This has implications for online learning, including responsive design, flexible delivery across devices, and content optimized for mobile.
Econsultancy, in association with Adobe - Digital Trends

The presentation is based on a survey of 12,500 marketing, creative, design and technology professionals across EMEA, North America and Asia Pacific.
Similar to What's Keeping Higher Education CIOs Up at Night (20)
[Webinar Slides] Capture Leaders & Their Projects: We Asked, They Answered. D...![[Webinar Slides] Capture Leaders & Their Projects: We Asked, They Answered. D...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] Capture Leaders & Their Projects: We Asked, They Answered. D...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Webinar Slides] Capture Leaders & Their Projects: We Asked, They Answered. D...
International Technology Adoption & Workforce Issues Study - Middle East Summary

International Technology Adoption & Workforce Issues Study - Middle East Summary
International Technology Adoption & Workforce Issues Study - Canadian Summary

International Technology Adoption & Workforce Issues Study - Canadian Summary
CompTIA's 5 Trends Shaping the Tech-Driven Workforce

CompTIA's 5 Trends Shaping the Tech-Driven Workforce
Clarkston Consulting CIO - 2022 Survey Summary Report.pdf

Clarkston Consulting CIO - 2022 Survey Summary Report.pdf
Information technology research trends: The future vision 

Information technology research trends: The future vision
Econsultancy, in association with Adobe - Digital Trends

Econsultancy, in association with Adobe - Digital Trends
More from Extreme Networks
Employee Spotlight: Anu Gade

Anu Gade is the Senior Director of Product Management at Extreme Networks. She is responsible for defining the overall switching strategy and increasing cloud adoption for Extreme switches. She enjoys engineering because it allows her to solve problems creatively by exploring new ideas, testing them out, and iterating until satisfied. The best career advice she received was that networking is essential and having sponsors advocate for you is important for advancement.
Employee Spotlight: Indhu Balraj

Indhu Balraj is the Senior Engineering Director at Extreme Networks. She oversees product security compliance and certifications, enabling products in the federal market, manages global engineering labs for service provider and enterprise switching products, and manages engineering operations for the service provider organization. She loves engineering because it allows her to be creative in solving problems and make a difference in the world. The best advice she received was to break barriers, focus on strengths, and commit fully. Her advice for young engineers is to find a mentor and develop strong soft skills in addition to technical skills.
Employee Spotlight: Uma Parthasarathy

Uma Parthasarathy is the Senior Director of QA Engineering at Extreme Networks. She is responsible for quality assurance of EXOS products and functional testing of ExtremeCloud IQ NOS features. She also heads the Diversity and Inclusion Council for the India team. She enjoys engineering because it involves finding simple solutions to complex problems through logical problem-breaking and solution-building. Her best advice is to have a "Can Do" attitude and good working relationships. For young engineers, she advises that with hard work and determination, anything can be achieved.
Extreme Networks Wi-Fi Timeline

The document summarizes the history of Wi-Fi from 1971 to 2020, including key milestones such as the establishment of the IEEE 802.11 standards committee in 1997, the release of the 802.11b standard in 1999 allowing speeds up to 11 Mbps, and the introduction of Wi-Fi 6 in 2019 providing faster speeds and increased capacity. It discusses the evolution of Wi-Fi technologies and standards over time as well as the growing reliance on Wi-Fi connectivity during the 2020 coronavirus pandemic.
Extreme Networks Timeline 2021

Extreme Networks has a history of many technology firsts, including being the first to market with Gigabit Ethernet switches, 10 Gigabit Ethernet switches, and 802.11ax Wi-Fi 6 access points. It has grown through acquisitions of companies like Enterasys, Zebra's WLAN business, Avaya's networking business, and Brocade's data center networking business. Today, Extreme Networks provides end-to-end wired and wireless networking solutions and cloud services to enterprises and venues like NFL stadiums and MLB ballparks.
Teenage Vaping is on the Rise: Vape Sensor Solutions SlideShare

This document discusses solutions to combat vaping in schools. It describes a new smart sensor product called HALO that can detect vaping and THC and is being used by school districts to address the youth vaping epidemic. It also outlines how Extreme Networks provides integrated networking solutions including secure sensor onboarding, management, and reporting capabilities to support the HALO sensors.
Esports and Extreme Networks

This document discusses esports and networking technology from Extreme Networks' perspective. It begins with an introduction of Extreme Networks, describing their history, customers, and industry recognition. It then presents a case study of SUNY Canton's esports program, including how their arena was set up and how esports has increased enrollment in related programs. The document concludes by discussing the current state and future predictions of the esports industry, and emphasizes the importance of infrastructure and computing technology to esports.
Introducing and and Implementing eSports at SUNY Canton

Today 20% of schools have implemented an eSports program and another 50% are considering adding one. This presentation shares how it’s done, directly from SUNY Canton, the first SUNY college to offer varsity eSports in 2018. The leaders of this program take you through SUNY Canton’s eSports journey and how their innovative investment has aided recruitment and retention. Along the way, they created one of the largest dedicated gaming installations in the Northeast: a 1,800 square-foot space with 25 high-end gaming rigs.
Wi-Fi Engagement Insights from Super Bowl LIII

As the Official Wi-Fi Solutions Provider of the NFL, Extreme Networks has powered the previous 6 Super Bowls with Wi-Fi analytics from connected fans.
Take Your Automated Campus to the Next Level

This document discusses Extreme Automated Campus and new enhancements from Extreme Networks. It provides 10 top automated campus enhancements, including: 1) expanded management and automation capabilities, 2) new IoT security features, 3) application telemetry and analytics, 4) extending policy and insights into multi-cloud networks, 5) high performance 100G core/aggregation networking, 6) next-generation edge switching, 7) scalable and unified wired/wireless solutions, 8) high performance border routing, 9) fast and simple guest/IoT onboarding, and 10) simplified migrations from heritage switches. Additional details and benefits are described for each enhancement area.
Hazardous & Challenging Wi-Fi Deployments

This document discusses deploying Wi-Fi in challenging environments and provides examples of how Extreme Networks solutions have addressed Wi-Fi needs in various industries. It describes common challenges in harsh environments like large and open spaces, device density, and changing environmental conditions. It then highlights Extreme Networks' differentiated solutions for indoor and outdoor deployments. Finally, it provides case studies of Extreme Networks deployments on retail/warehouses, public venues, ports/shipping, buses, trains, mining facilities, and sports venues.
Retail’s Digital Pain Points and How the Network Can Solve Them

How to transform your network from a cost center to a business asset by learning customer behavior and buying habits with network analytics.
Extreme Secure Automated Smart Factory

This document discusses Extreme Networks' Secure Automated Smart Factory (SASF) solution. It provides an example of how SASF was implemented for a US car manufacturer to achieve fully automated operations, network robustness, flexible network topology, and highly secure segmentation. The SASF architecture provides infrastructure switching, network services automation, endpoint access automation, and distributed security policies. It allows for rapid service provisioning, reduced change windows, and isolation of network segments.
Top 12 Reasons Our Healthcare Networks Deliver Better Patient Care

Here’s a quick scan of the top ways the best network for healthcare helps you deliver better patient outcomes. You’ll recognize challenges like balancing the Facebook and Netflix needs of patients and visitors with the guarantee of privacy for patient medical records. And how do you insure the best possible doctor and patient experience, while safe-guarding the network from outside attack? Here are the top challenges of healthcare IT, and how to solve them painlessly.
Extreme Networks and Avaya IP Networking Strategy

Extreme Networks is acquiring Avaya's networking business and Brocade's data center technologies. The acquisition will make Extreme the largest company focused on software-driven wired and wireless networking solutions. Extreme is committed to maintaining service continuity and preserving customers' investments for both Avaya and Extreme customers. Over the next year, Extreme will focus on delivering an expanded portfolio while maintaining existing purchase and support models.
Take Your K-12 IT Management From Pain to Bliss in 12 steps

EdTech is rapidly expanding and bringing intimidating new challenges to primary/secondary and k-12 IT departments. Today’s classrooms are providing virtual and augmented reality for students. Entire classes often simultaneously participate in online assessments or final exams. The Internet of Things is introducing new sensors and devices to schools.
The Connected Guest Experience

The document discusses how ExtremeWireless provides connectivity solutions for the hospitality industry that deliver a quality guest experience through ubiquitous WiFi coverage both indoors and outdoors. Their solutions ease the burden on small IT staffs through unified management, allow properties to understand how guests use the network, securely onboard guests, prioritize bandwidth to critical applications, and offer flexible solutions for new or existing properties regardless of costs or timing constraints.
Higher Education and The Digital Connected Experience

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive functioning. Exercise boosts blood flow and levels of neurotransmitters and endorphins that elevate and stabilize mood.
Record-Breaking Wi-Fi Usage at Super Bowl LI

For Super Bowl LI, the NFL trusted Extreme Networks to provide the Wi-Fi infrastructure and network analytics for their always-connected fans.
Extreme Networks Retail Guest Analytics Solution

The document discusses Extreme Networks' Retail Guest Analytics Solution. It provides centralized, integrated, scalable, easy to use, powerful, and customizable wireless access and analytics for retail stores. The solution allows retailers to gain insights into customer engagement through wireless usage data and social media/SMS login information. It provides customizable dashboards and reports with metrics such as device types, applications used, dwell times, and more to understand customer behavior.
More from Extreme Networks (20)
Teenage Vaping is on the Rise: Vape Sensor Solutions SlideShare

Teenage Vaping is on the Rise: Vape Sensor Solutions SlideShare
Introducing and and Implementing eSports at SUNY Canton

Introducing and and Implementing eSports at SUNY Canton
Retail’s Digital Pain Points and How the Network Can Solve Them

Retail’s Digital Pain Points and How the Network Can Solve Them
Top 12 Reasons Our Healthcare Networks Deliver Better Patient Care

Top 12 Reasons Our Healthcare Networks Deliver Better Patient Care
Take Your K-12 IT Management From Pain to Bliss in 12 steps

Take Your K-12 IT Management From Pain to Bliss in 12 steps
Higher Education and The Digital Connected Experience

Higher Education and The Digital Connected Experience
Recently uploaded
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

ABSTRACT: A prima vista, un mattoncino Lego e la backdoor XZ potrebbero avere in comune il fatto di essere entrambi blocchi di costruzione, o dipendenze di progetti creativi e software. La realtà è che un mattoncino Lego e il caso della backdoor XZ hanno molto di più di tutto ciò in comune.
Partecipate alla presentazione per immergervi in una storia di interoperabilità, standard e formati aperti, per poi discutere del ruolo importante che i contributori hanno in una comunità open source sostenibile.
BIO: Sostenitrice del software libero e dei formati standard e aperti. È stata un membro attivo dei progetti Fedora e openSUSE e ha co-fondato l'Associazione LibreItalia dove è stata coinvolta in diversi eventi, migrazioni e formazione relativi a LibreOffice. In precedenza ha lavorato a migrazioni e corsi di formazione su LibreOffice per diverse amministrazioni pubbliche e privati. Da gennaio 2020 lavora in SUSE come Software Release Engineer per Uyuni e SUSE Manager e quando non segue la sua passione per i computer e per Geeko coltiva la sua curiosità per l'astronomia (da cui deriva il suo nickname deneb_alpha).
Best 20 SEO Techniques To Improve Website Visibility In SERP

Boost your website's visibility with proven SEO techniques! Our latest blog dives into essential strategies to enhance your online presence, increase traffic, and rank higher on search engines. From keyword optimization to quality content creation, learn how to make your site stand out in the crowded digital landscape. Discover actionable tips and expert insights to elevate your SEO game.
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on integration of Salesforce with Bonterra Impact Management.
Interested in deploying an integration with Salesforce for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/building-and-scaling-ai-applications-with-the-nx-ai-manager-a-presentation-from-network-optix/
Robin van Emden, Senior Director of Data Science at Network Optix, presents the “Building and Scaling AI Applications with the Nx AI Manager,” tutorial at the May 2024 Embedded Vision Summit.
In this presentation, van Emden covers the basics of scaling edge AI solutions using the Nx tool kit. He emphasizes the process of developing AI models and deploying them globally. He also showcases the conversion of AI models and the creation of effective edge AI pipelines, with a focus on pre-processing, model conversion, selecting the appropriate inference engine for the target hardware and post-processing.
van Emden shows how Nx can simplify the developer’s life and facilitate a rapid transition from concept to production-ready applications.He provides valuable insights into developing scalable and efficient edge AI solutions, with a strong focus on practical implementation.Webinar: Designing a schema for a Data Warehouse

Are you new to data warehouses (DWH)? Do you need to check whether your data warehouse follows the best practices for a good design? In both cases, this webinar is for you.
A data warehouse is a central relational database that contains all measurements about a business or an organisation. This data comes from a variety of heterogeneous data sources, which includes databases of any type that back the applications used by the company, data files exported by some applications, or APIs provided by internal or external services.
But designing a data warehouse correctly is a hard task, which requires gathering information about the business processes that need to be analysed in the first place. These processes must be translated into so-called star schemas, which means, denormalised databases where each table represents a dimension or facts.
We will discuss these topics:
- How to gather information about a business;
- Understanding dictionaries and how to identify business entities;
- Dimensions and facts;
- Setting a table granularity;
- Types of facts;
- Types of dimensions;
- Snowflakes and how to avoid them;
- Expanding existing dimensions and facts.
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
Recently uploaded (20)
Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...

Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

Cosa hanno in comune un mattoncino Lego e la backdoor XZ?
Best 20 SEO Techniques To Improve Website Visibility In SERP

Best 20 SEO Techniques To Improve Website Visibility In SERP
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
What's Keeping Higher Education CIOs Up at Night
- 1. These are the top Higher Education CIO Emerging Priorities based on a worldwide survey of higher education CIOs and directors of technology. WHAT’S KEEPING HIGHER EDUCATION CIOS UP AT NIGHT? 39% 61% 78% North America 10%Latin America 10% Europe, Middle East, Africa 2% Asia Pacific Survey Participants Demographics How important is the Internet of Things to your planning? Top Concerns Consuming Measurable IT Resources Role of Network Analytics at Higher Ed Institution Do You Offer eduroam on Your Campus? Do You Offer Competency-Based Courses at Your School? How Do You Expect the Flipped Classroom Model and Usage of Video to Change at Your School in the Future?? Top Strategic Priorities for 2015 Infrastructure Security Mobility App Deployment Cloud Planning/Strategy Student Retention UX Cost 5% Not Important 19% Strategic Priority 23% Will Address Later 35% Part of BYOD Planning 47% Part of Normal Planning Process Possibility of Network Breach 71% Running out of Bandwidth 53% User-Generated Wi-Fi Interference 36% Shadow IT and Rogue IT 31% 67% Manage User Experience on the Network 67% Capacity Planning 33% Insight into Student Success 9% No Plans to Use Network Analytics NO69% YES31% 27% Not Sure 14% No 36% Yes 24% We are planning to in the future 3% Remain the Same 0% Will Diminish 73% 77% Moderate Growth 20% Rapid Growth Moderately Used Planning to Use in Future No Plans to Use it Does Your School Make Use of Online Teaching? Percent of Courses Offered Online IT Department’s Involvement with Online Courses How Much Personal Involvement Do You Have in These Areas, and How is Your Role Changing? 11% 14% 2% Very Heavily Used <10% 45% 51 – 75% 5% 76–100% 3% 10 – 25% 38% 25 – 50% 10% Provide some or all of the technology involved in the online courses Advise in the creation of online content Advise on technology for online courses Level of Involvement No involvement 68% 59% 30% 16% Small Medium Large FOR MORE INFORMATION, VISIT: EXTREMENETWORKS.COM/K-12 Fund Raising Overall School Strategy +5% +5% +35% Budgeting +30% Business Planning +35% Training +25% Curriculum Development Social Media +20%
