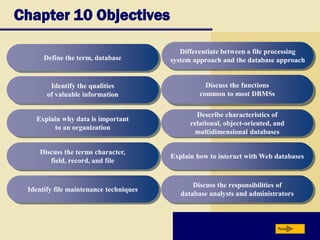
This chapter discusses database management and discusses key concepts such as:
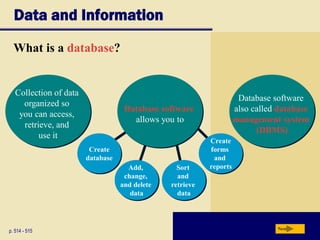
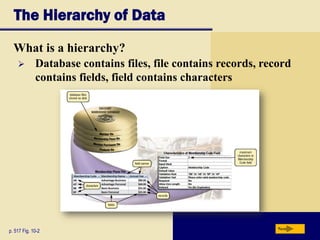
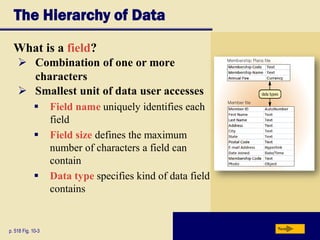
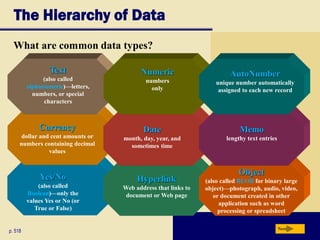
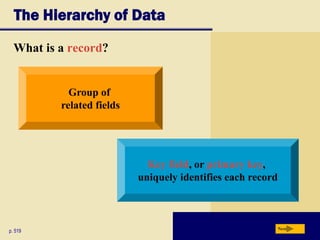
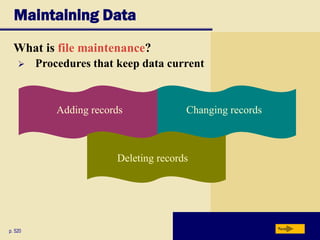
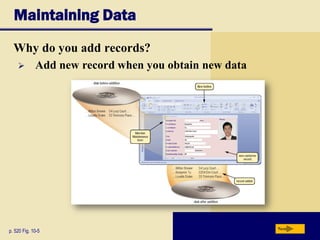
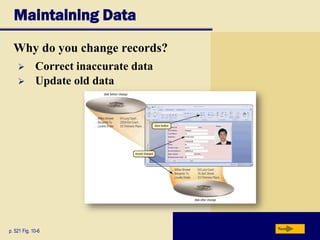
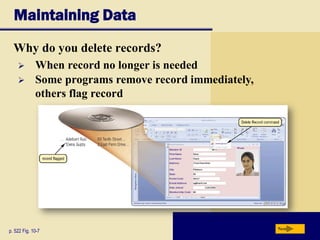
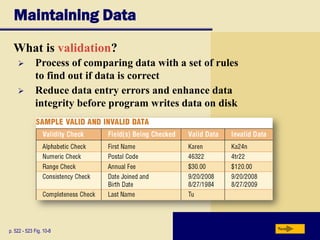
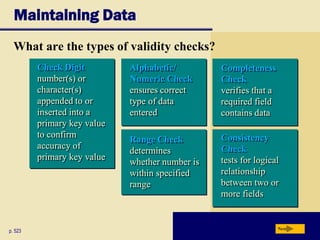
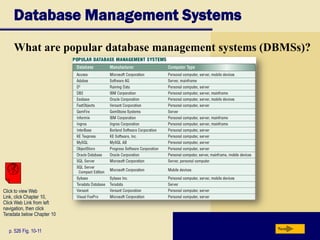
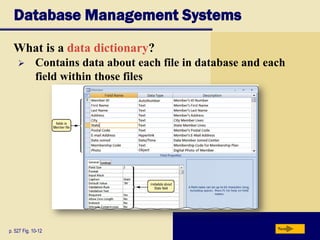
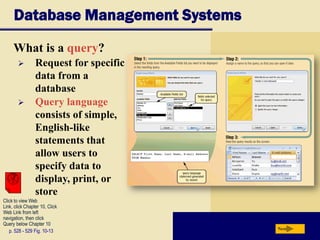
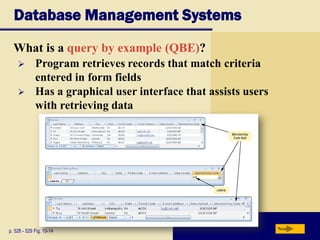
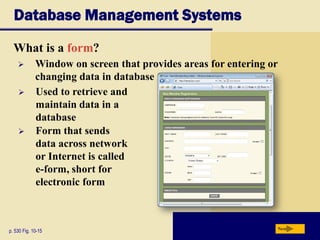
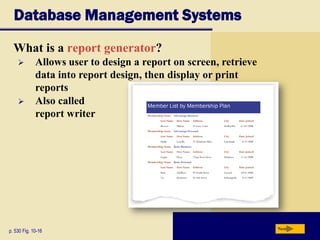
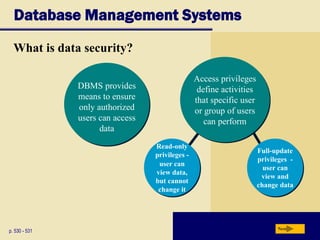
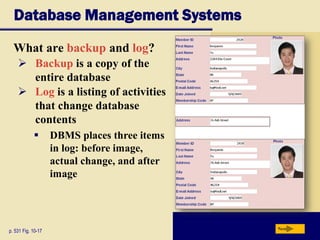
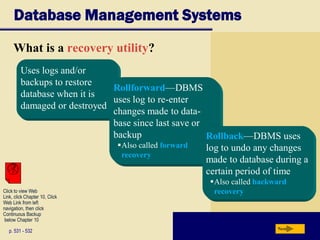
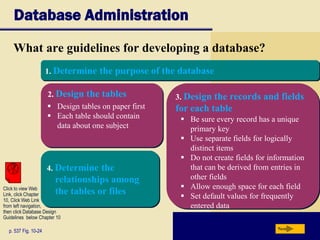
1. The functions of database management systems including adding, changing, deleting, sorting and retrieving data.
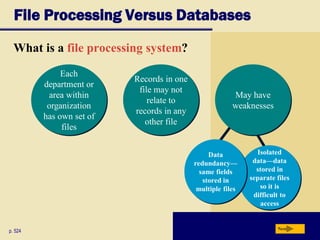
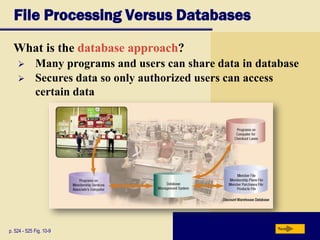
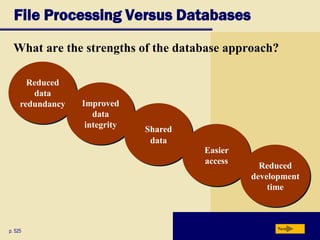
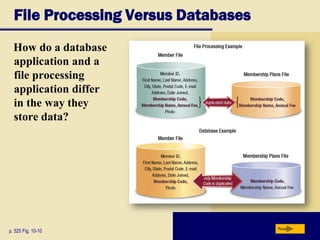
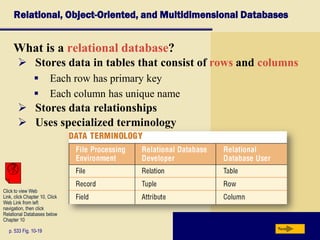
2. The differences between file processing systems and database approaches, with databases allowing for shared data access and reduced data redundancy.
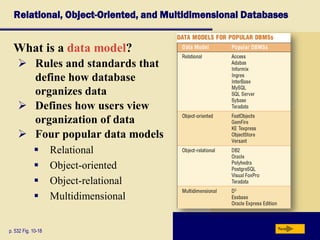
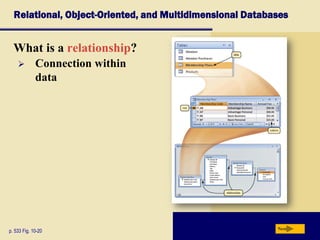
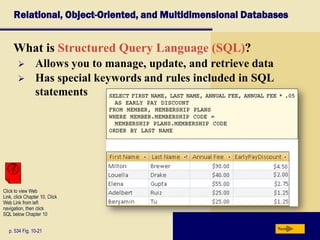
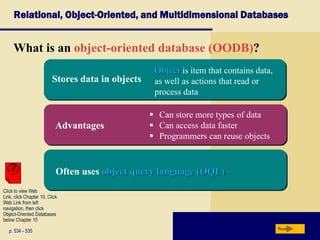
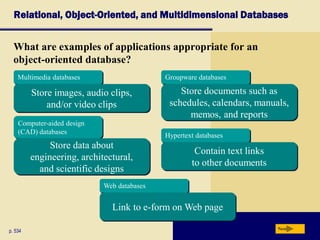
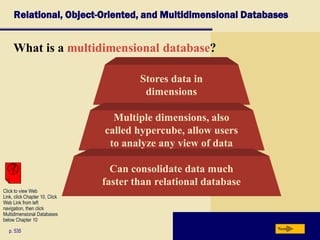
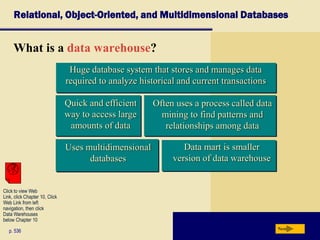
3. Popular database models including relational, object-oriented and multidimensional databases and how each organizes and stores data differently.