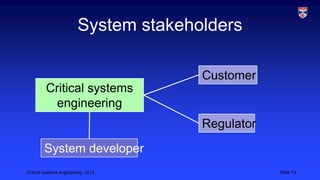
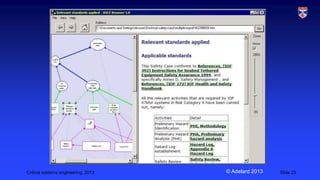
Critical systems engineering focuses on developing dependable and secure systems for applications where failure could result in loss of life, injury, or significant economic damage. These systems often require certification by regulators to demonstrate compliance with safety and dependability standards before use. The development process for critical systems uses rigorous, plan-driven methodologies and techniques like formal methods, fault detection tools, and redundancy to reduce risk of failure, which may involve higher costs than for other systems due to the potentially severe consequences of errors.