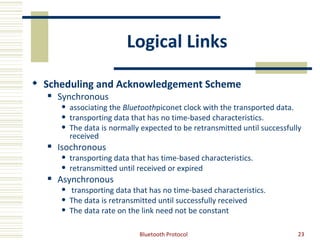
The document discusses the Bluetooth protocol. It provides details on Bluetooth properties like short-range wireless communication in the 2.4GHz band using frequency hopping. It describes Bluetooth profiles, usage cases, architecture including layers like L2CAP and protocols like LMP. Pairing, networks, testing qualifications are also summarized.