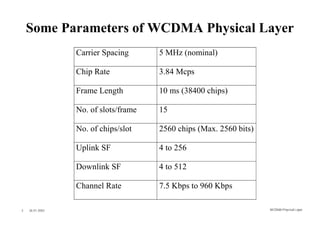
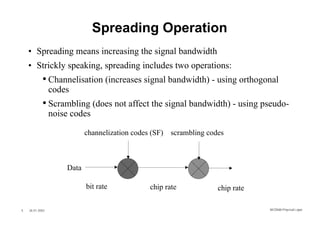
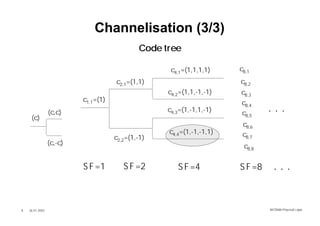
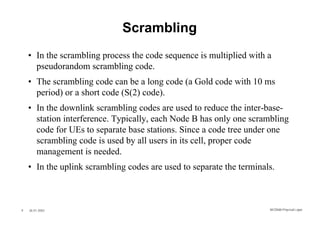
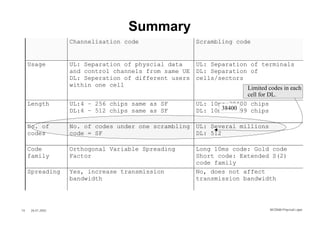
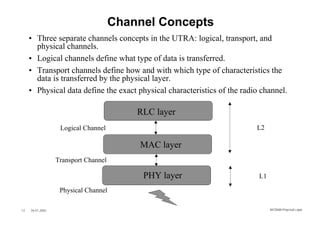
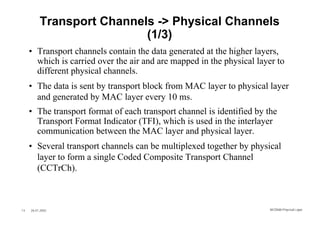
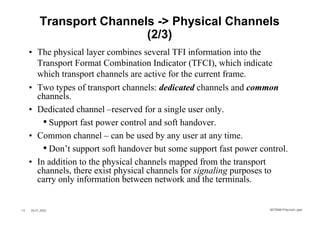
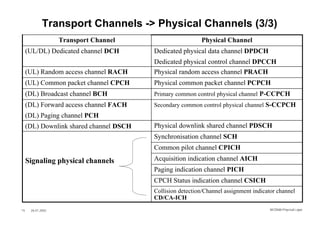
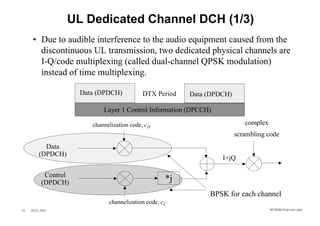
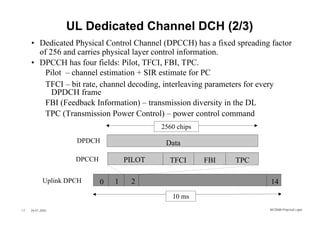
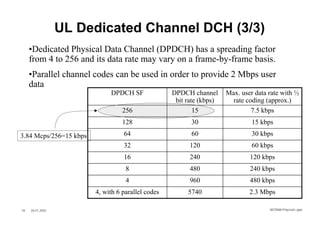
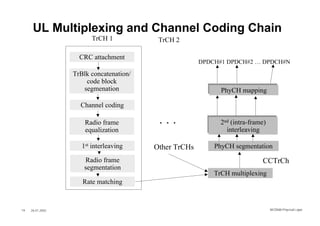
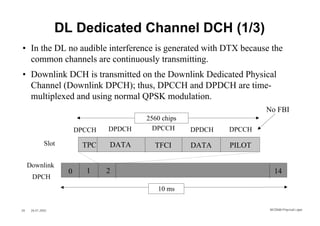
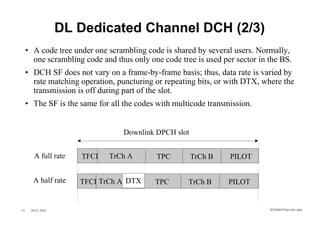
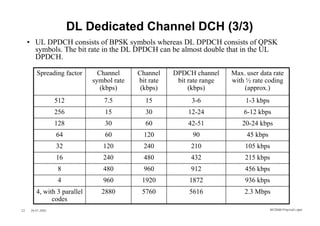
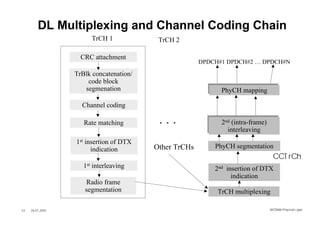
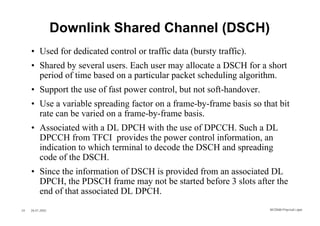
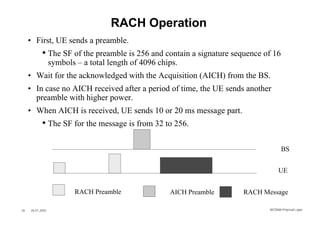
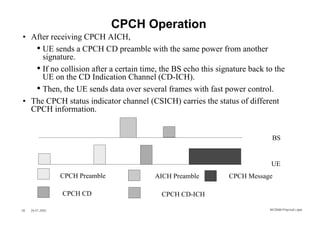
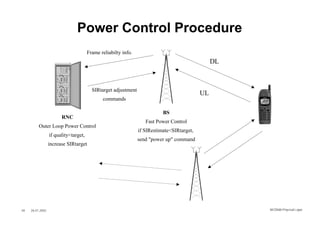
The document summarizes key aspects of the WCDMA physical layer. It discusses spreading and scrambling which increase signal bandwidth using channelization and scrambling codes. It describes transport channels which define how data is transferred physically, including dedicated and common channels. It also outlines physical channels such as the dedicated physical data and control channels for both uplink and downlink transmissions.