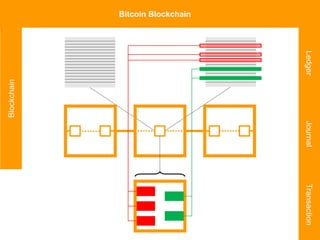
This document provides an overview of key blockchain and distributed ledger concepts including Bitcoin, Ethereum, Hyperledger, smart contracts, and related technologies like IoT and AI. It discusses the blockchain layers of immutability, authorization, and consensus for Bitcoin and Ethereum. It also summarizes the consensus approaches of proof of work, proof of stake, and PBFT used by different platforms.



















































![Ethereum Solidity – Token Contract
pragma solidity ^0.4.8;
contract MyToken {
...
event Transfer(
address indexed from,
address indexed to,
uint256 value);
/* Initializes contract with initial supply tokens */
function MyToken(
uint256 initialSupply,
string tokenName,
uint8 decimalUnits,
string tokenSymbol ) {
balanceOf[msg.sender] = initialSupply;
...](https://image.slidesharecdn.com/20171025blockchainiotnight-171025100757/85/Blockchain-IoT-Night-25th-Oct-2017-54-320.jpg)