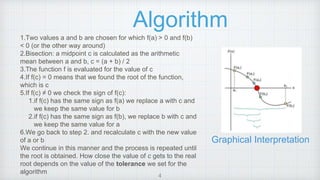
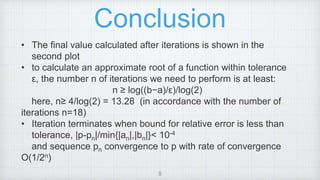
The document describes the implementation of the bisection method for root-finding in numerical analysis, outlining its theoretical basis and algorithmic steps. It includes a script for executing the method in MATLAB, detailing the iterative process for narrowing down to the root of a continuous function. The conclusion emphasizes the method’s simplicity and robustness, while also noting its relative slowness compared to other root-finding methods.

![Theory
Root-finding problem: Bisection Method is also called the interval
halving method, the binary search method, or the dichotomy method. is
based on the Bolzano’s theorem for continuous functions.
Intermediate value theorem states that if f is a continuous
function whose domain contains the interval [a, b], then it takes on any
given value between f(a) and f(b) at some point within the interval.
This has two corollaries:
1.If a continuous function has values of opposite sign inside an interval,
then it has a root in that interval (Bolzano's theorem).
2.The image of a continuous function over an interval is itself an interval
3](https://image.slidesharecdn.com/20463985-230523145656-2b7a86a0/85/Bisection-Method-3-320.jpg)