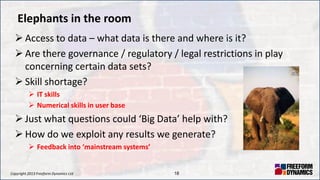
The document discusses the current state and future of big data and data centers, highlighting the challenges and opportunities organizations face in leveraging analytics. It emphasizes the need for effective governance, understanding of technology implications, and the shift towards unstructured data. Additionally, it explores the evolving IT landscape, including virtual infrastructure and hybrid cloud management, while addressing cultural and operational barriers to progress in modernizing IT systems.