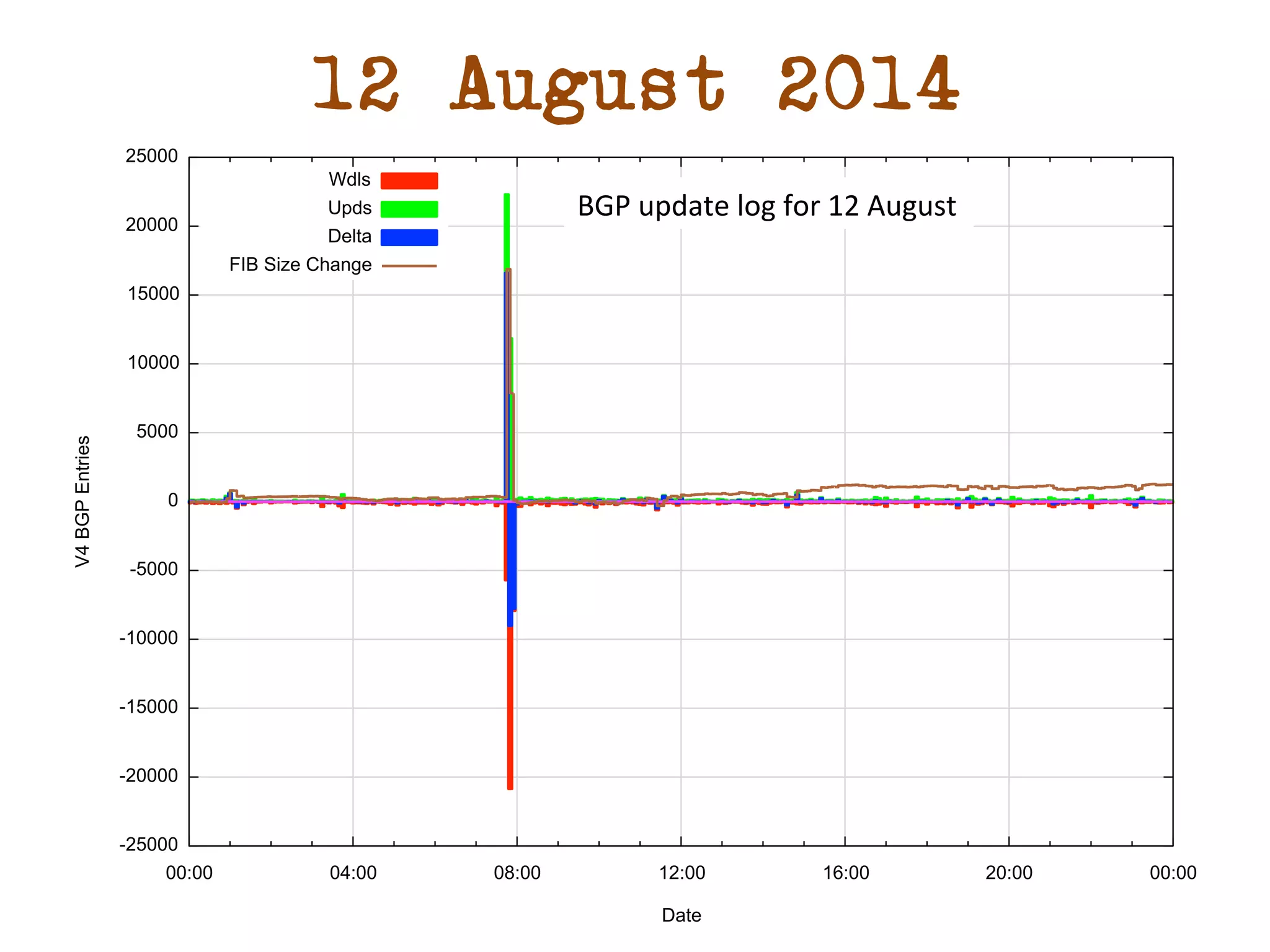
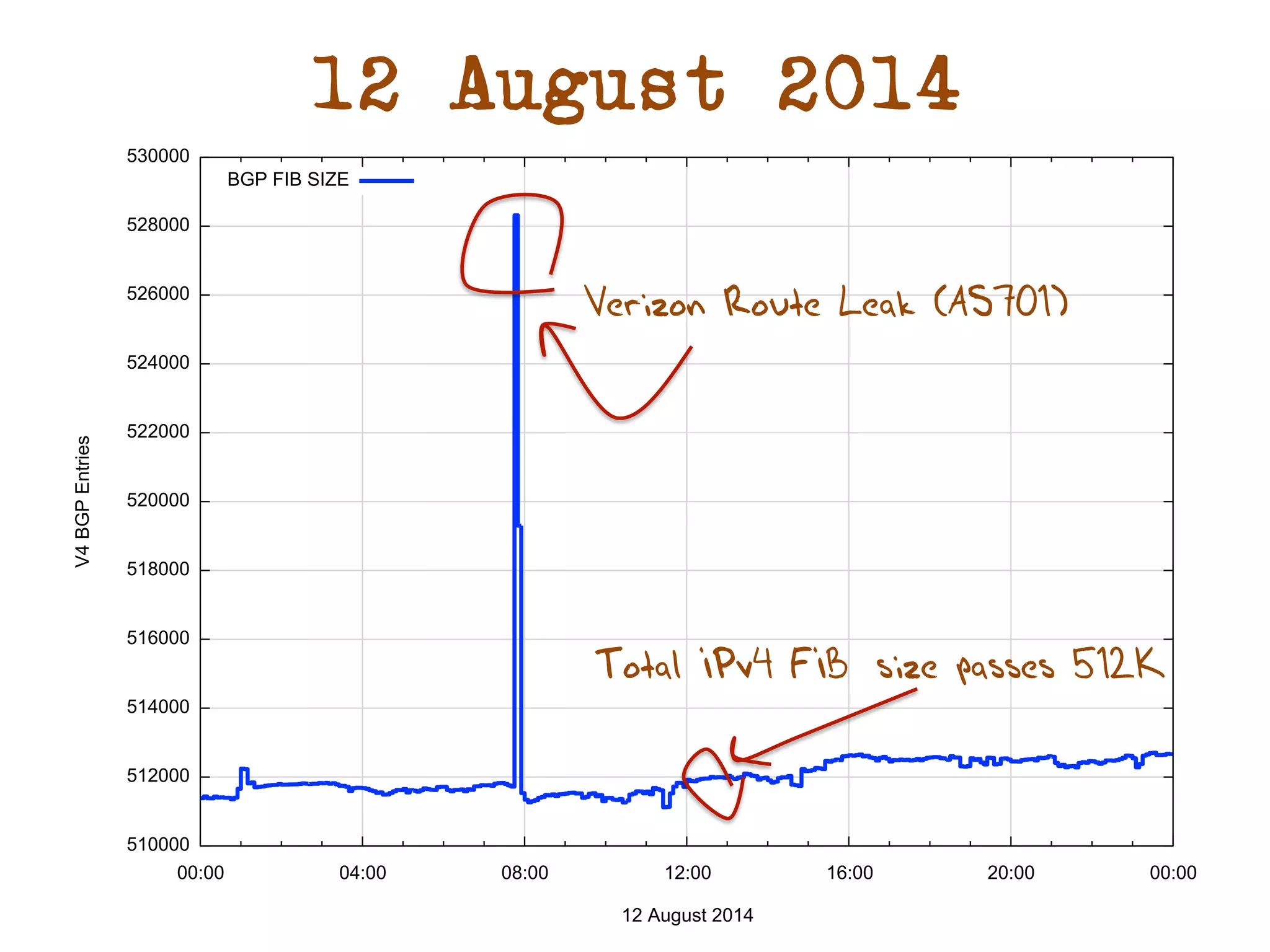
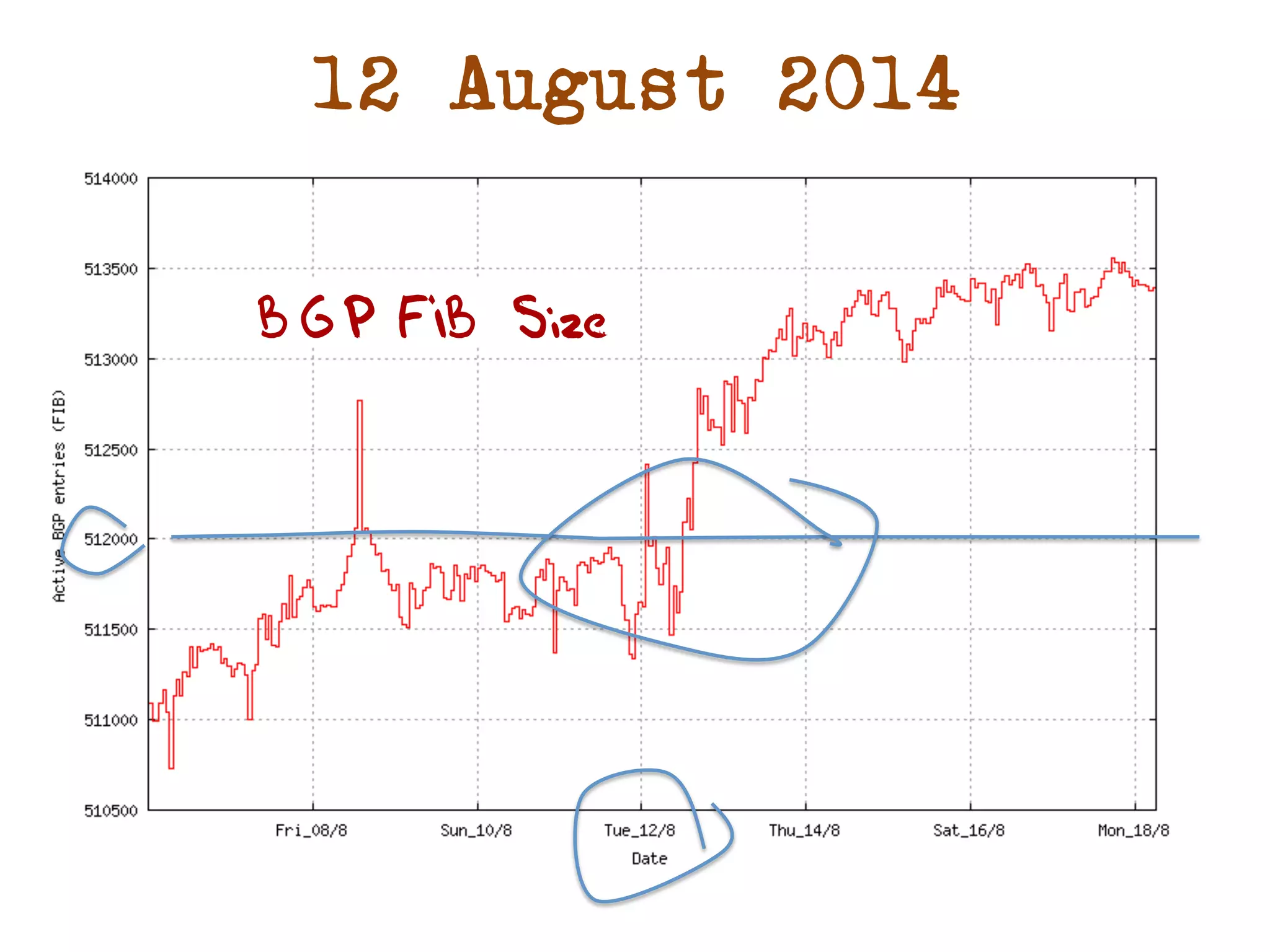
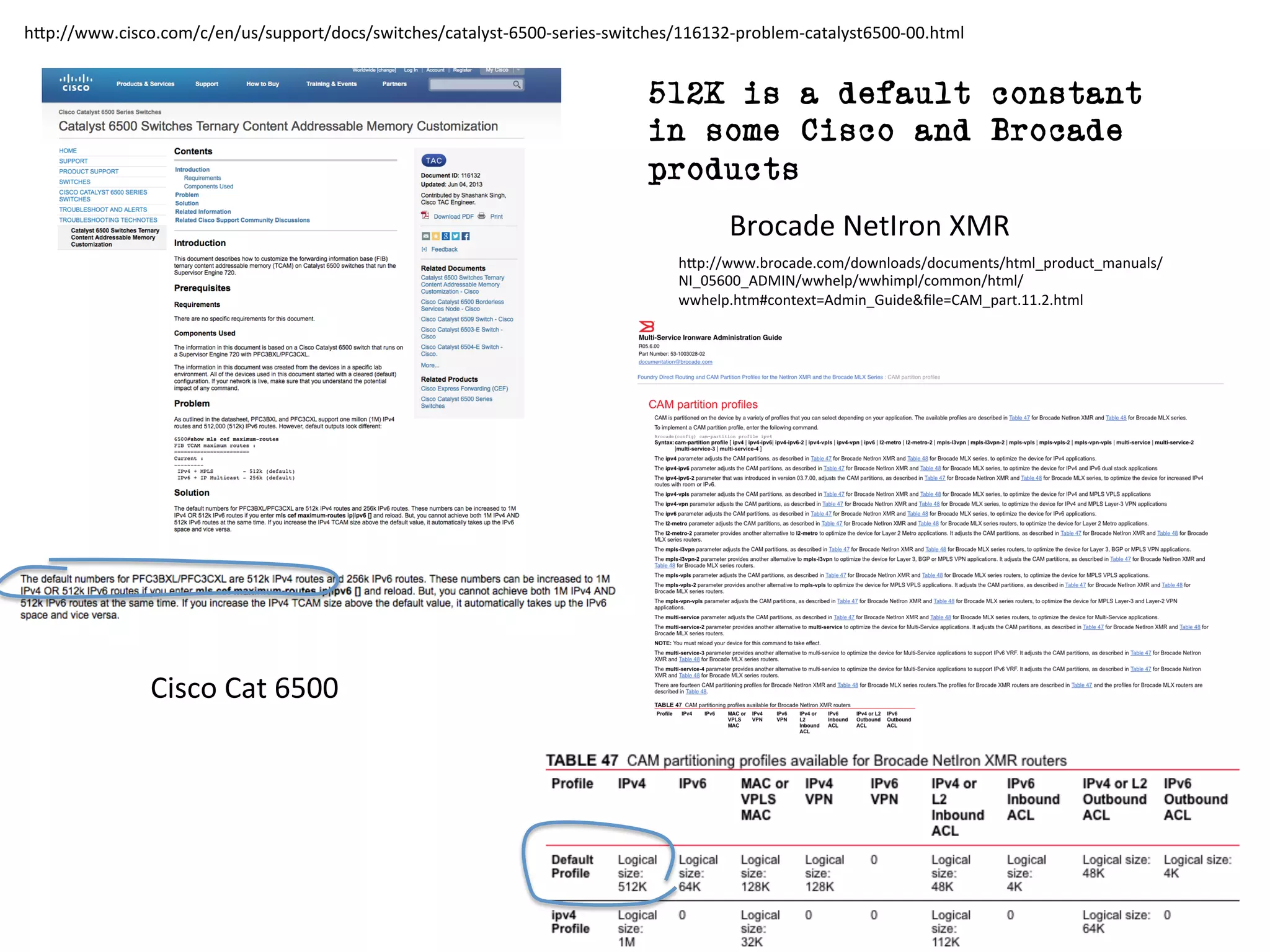
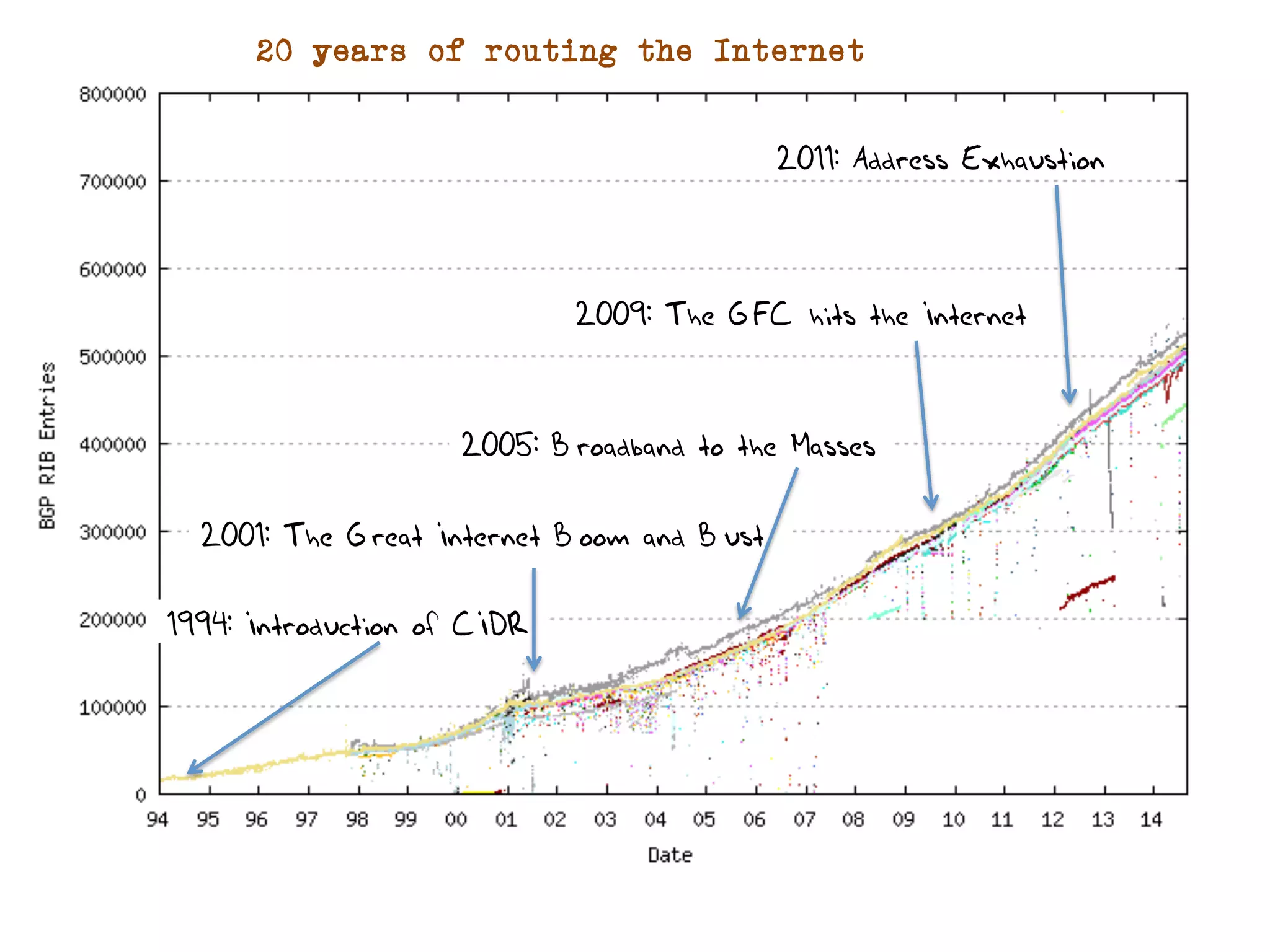
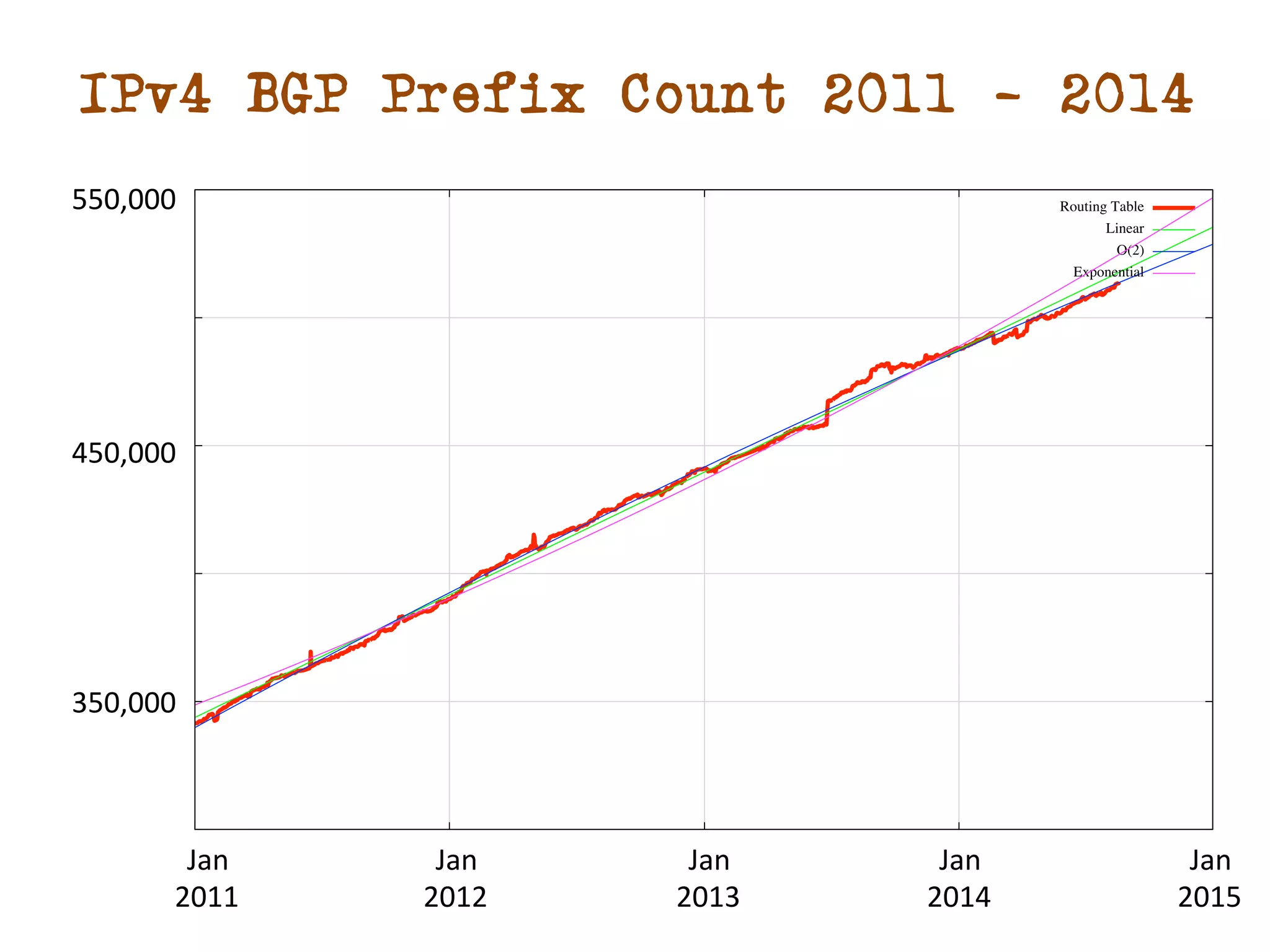
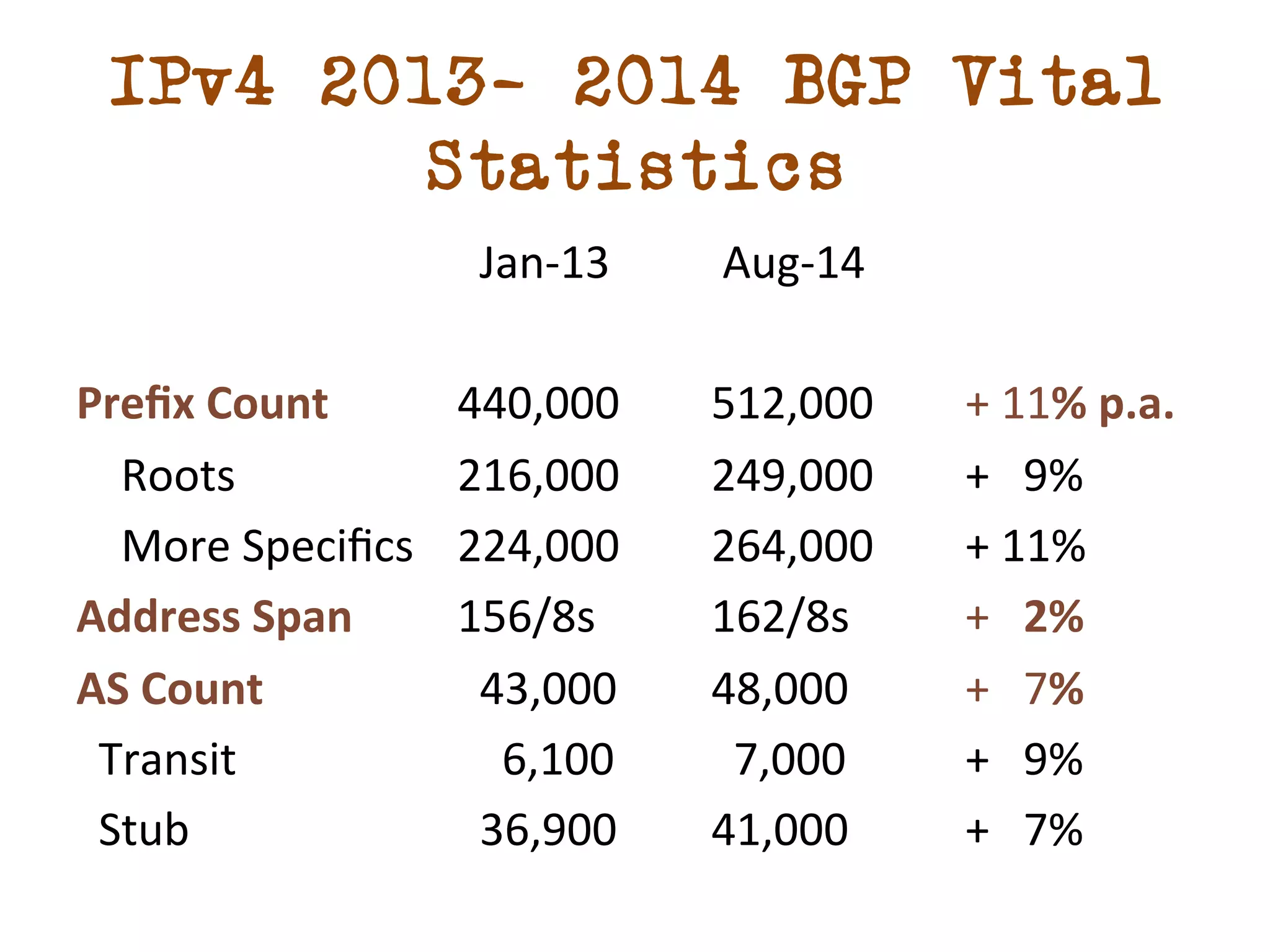
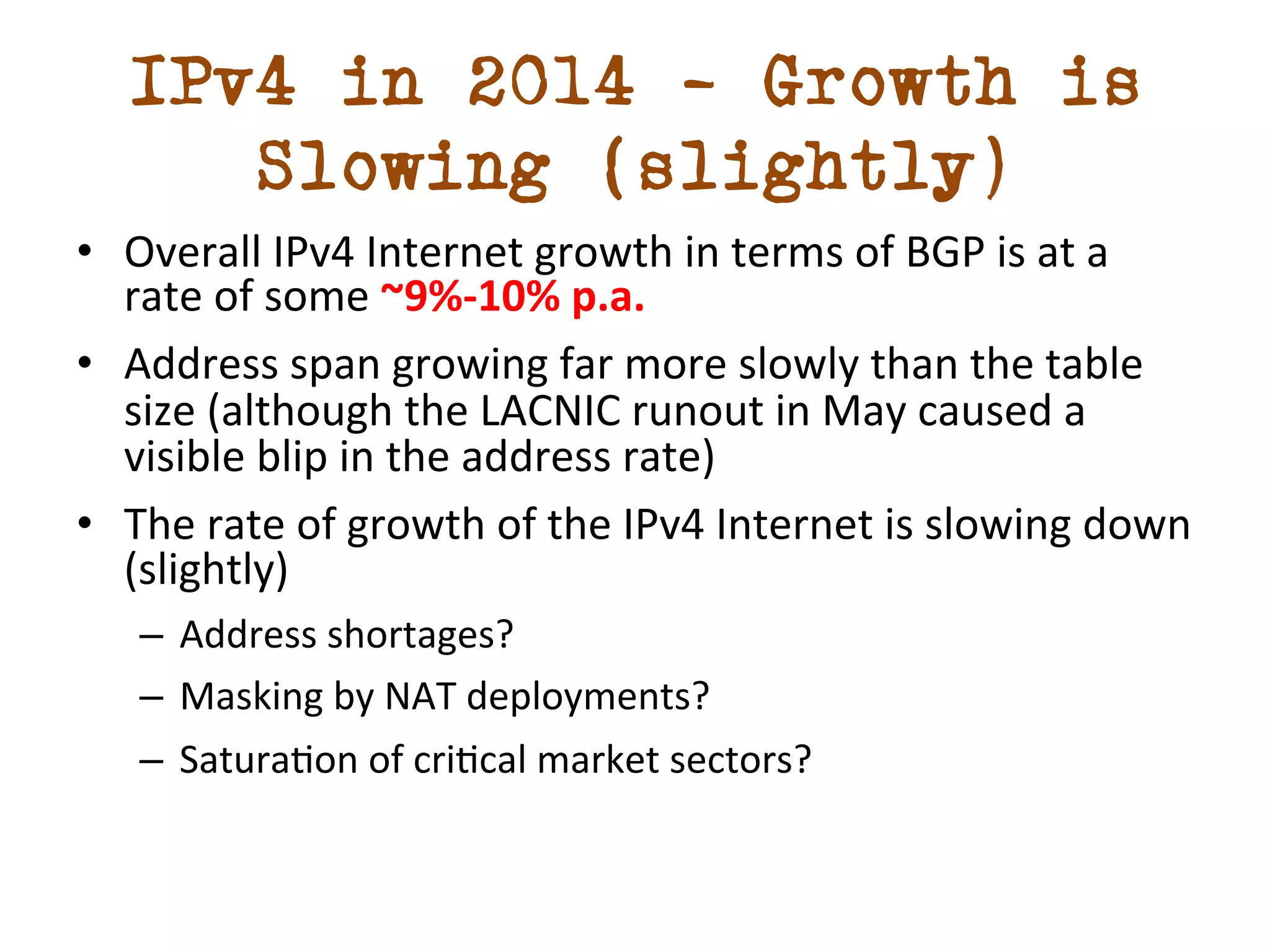
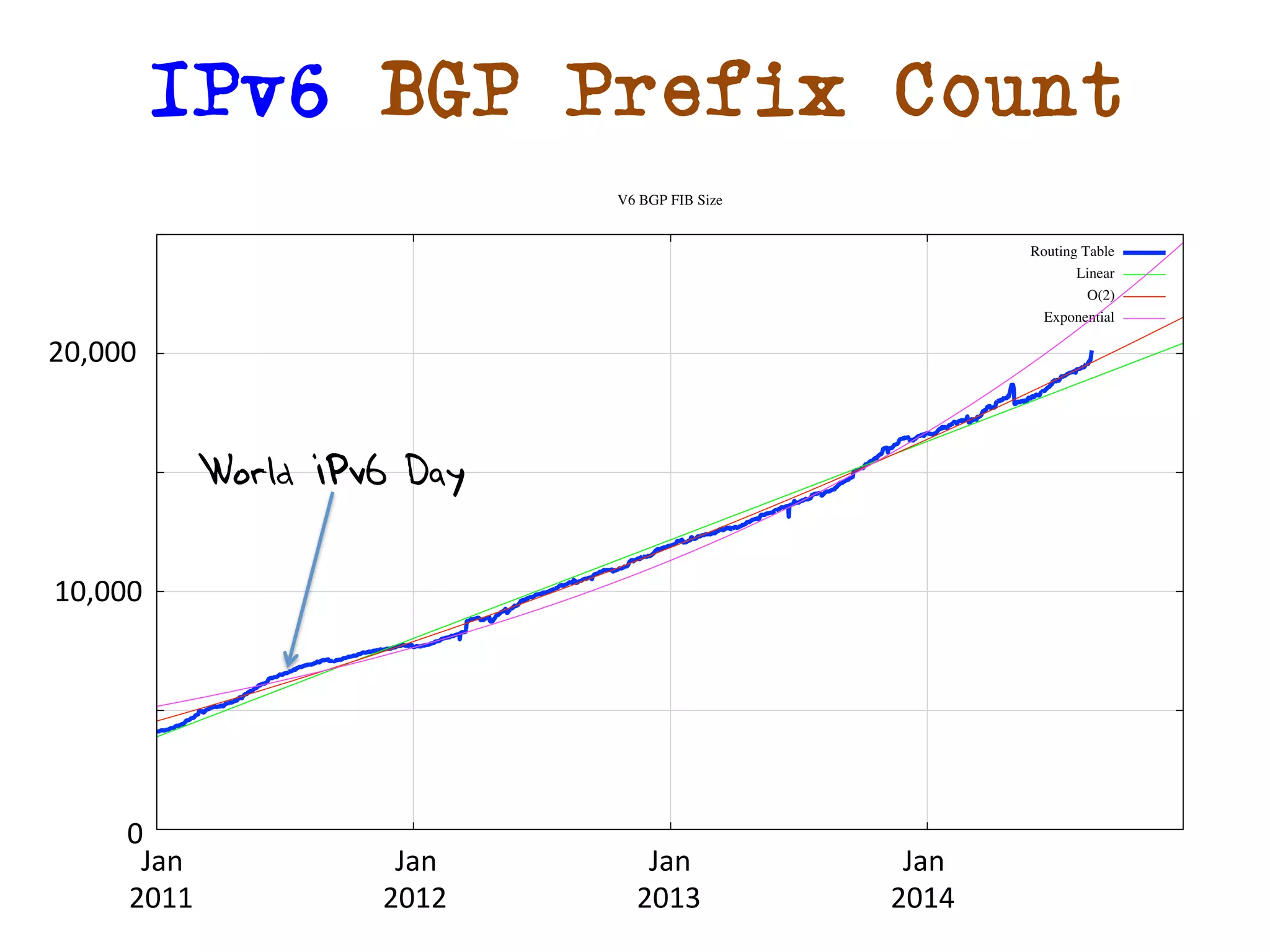
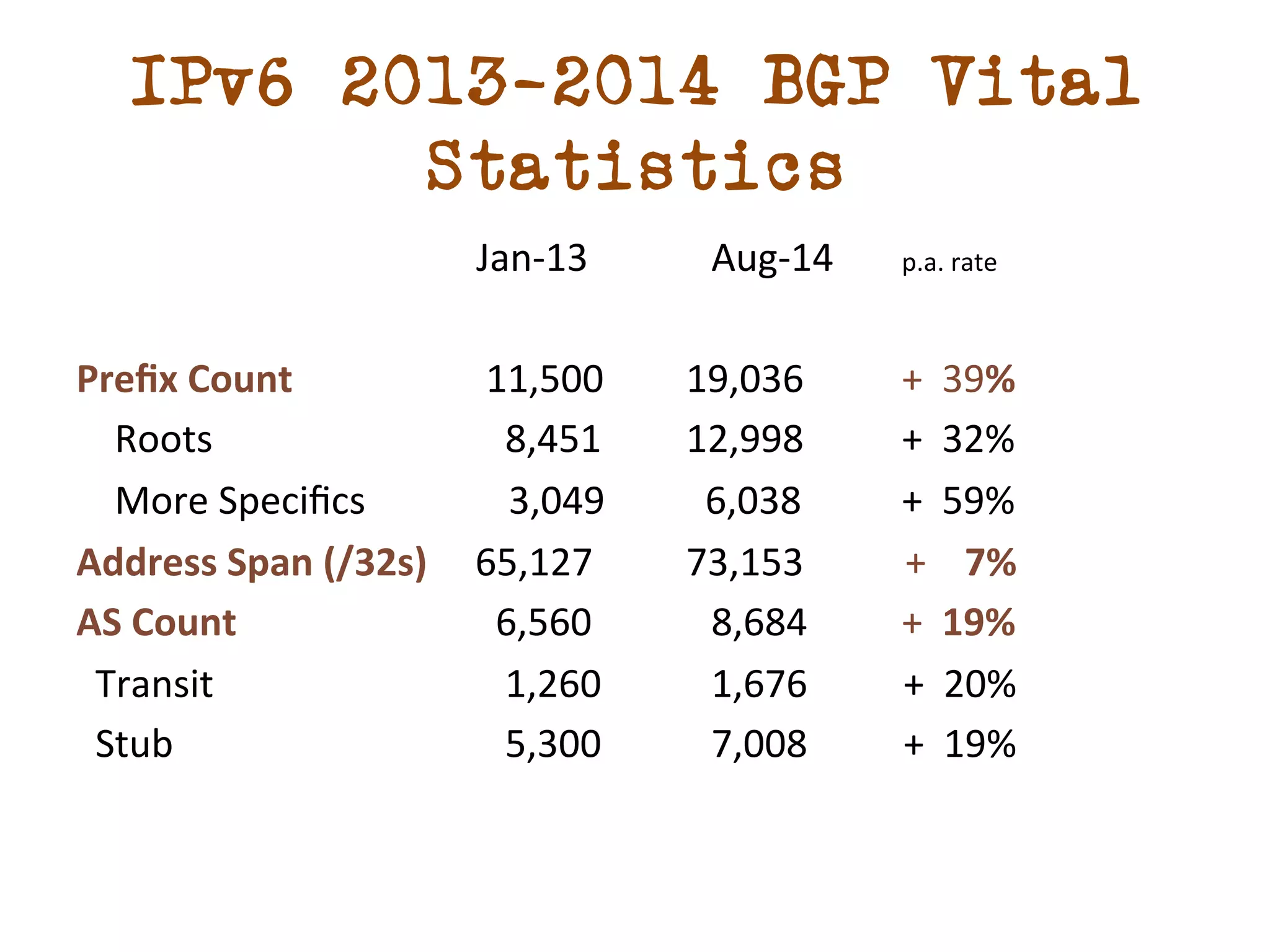
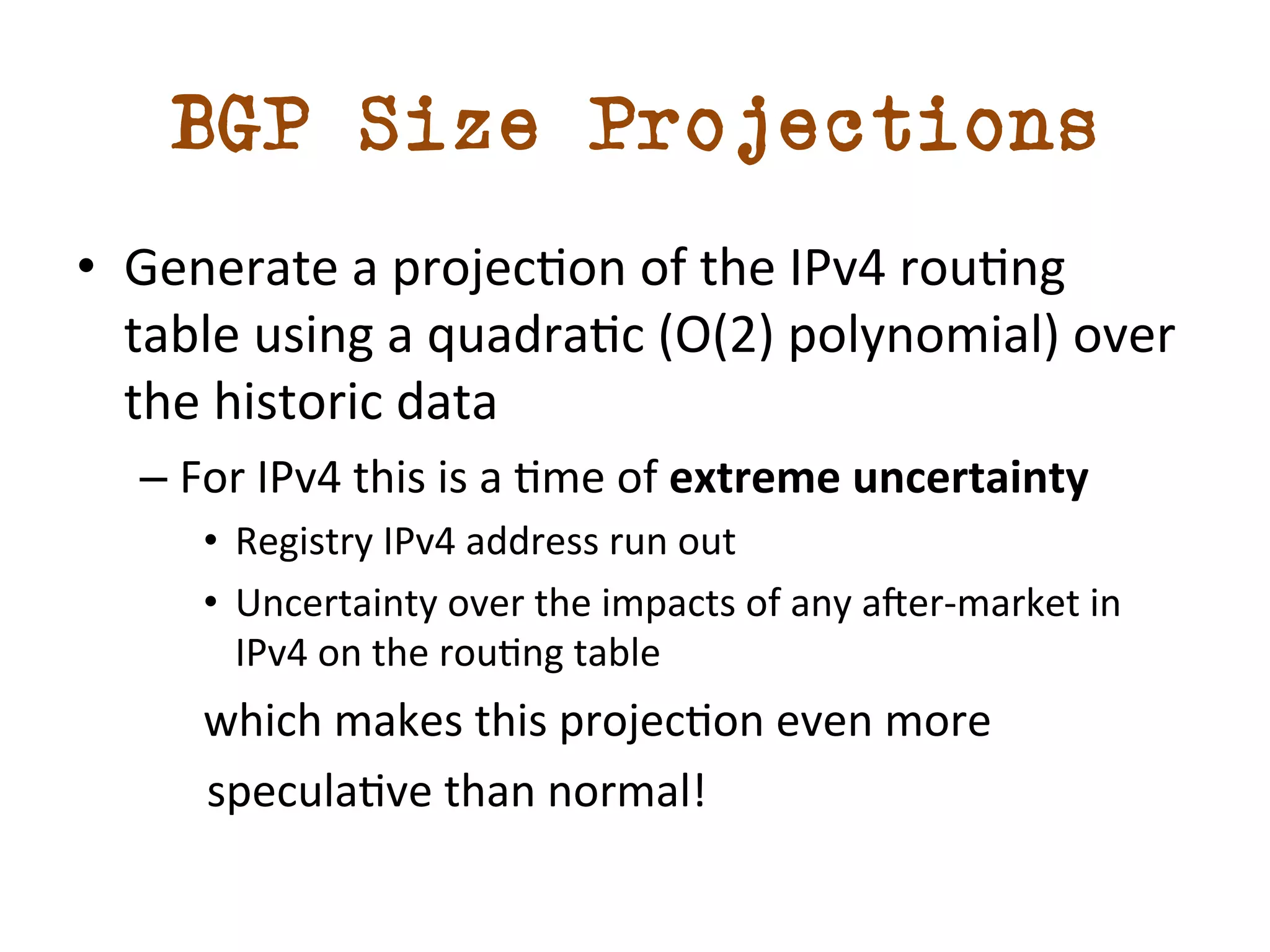
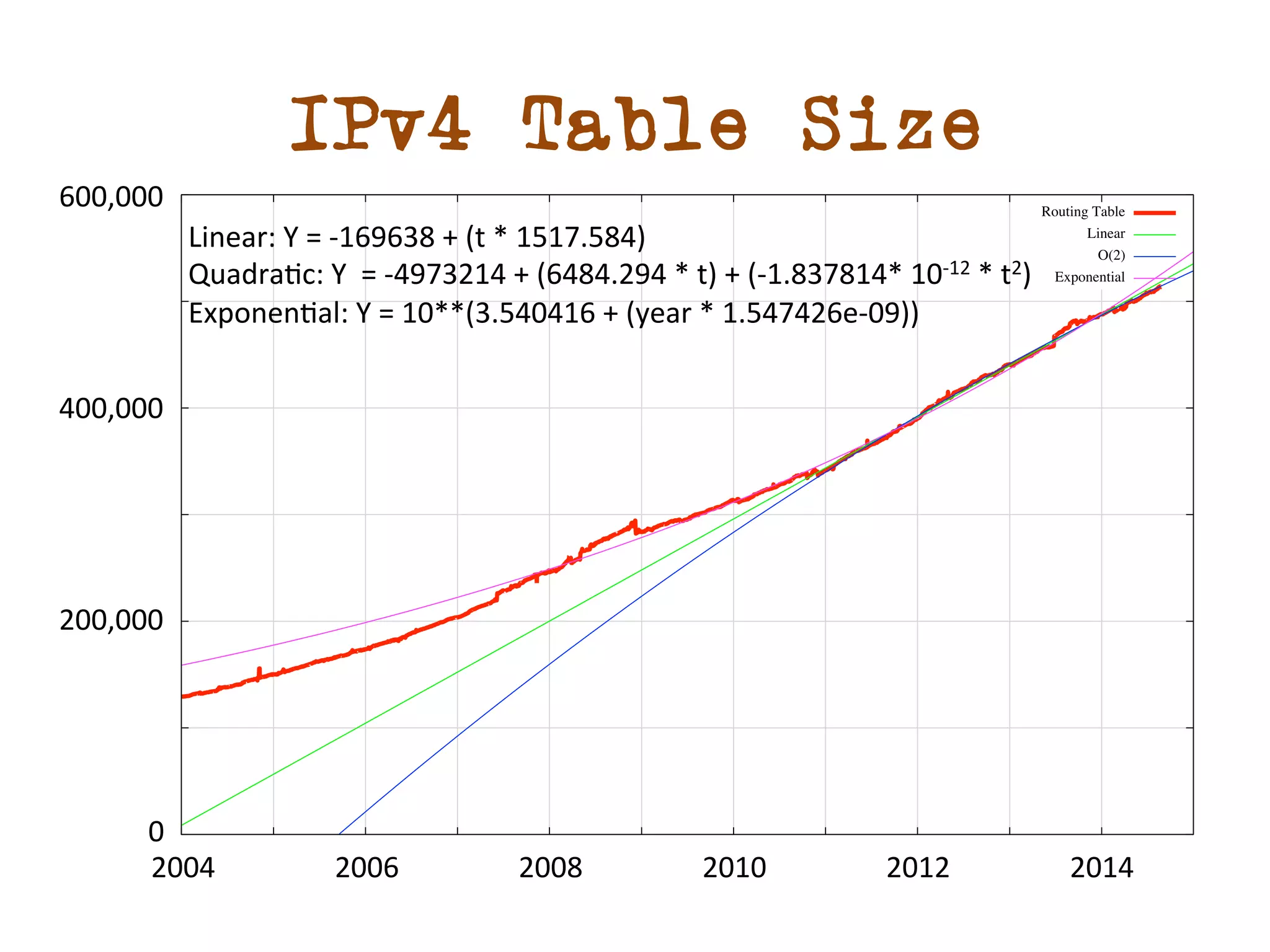
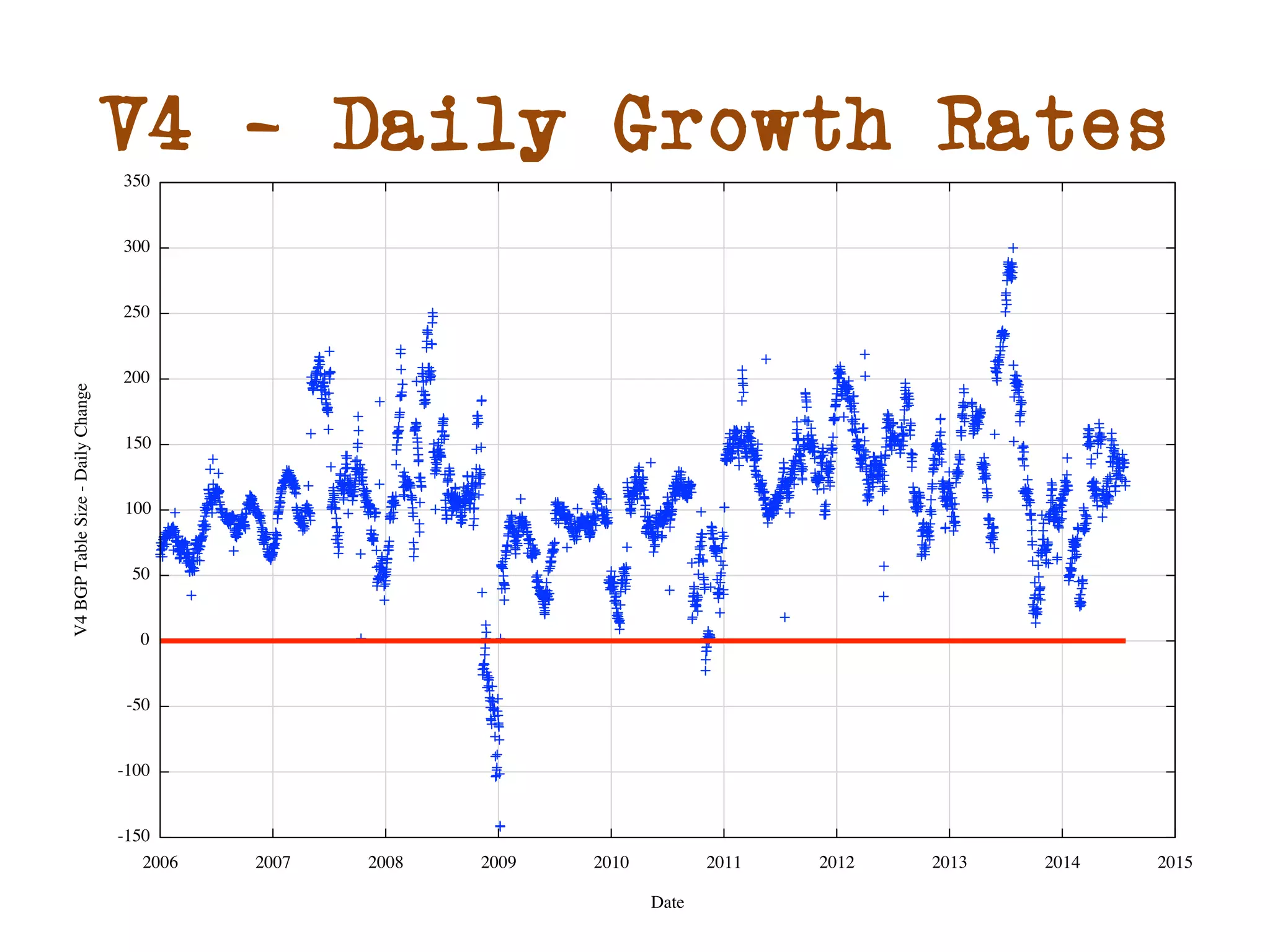
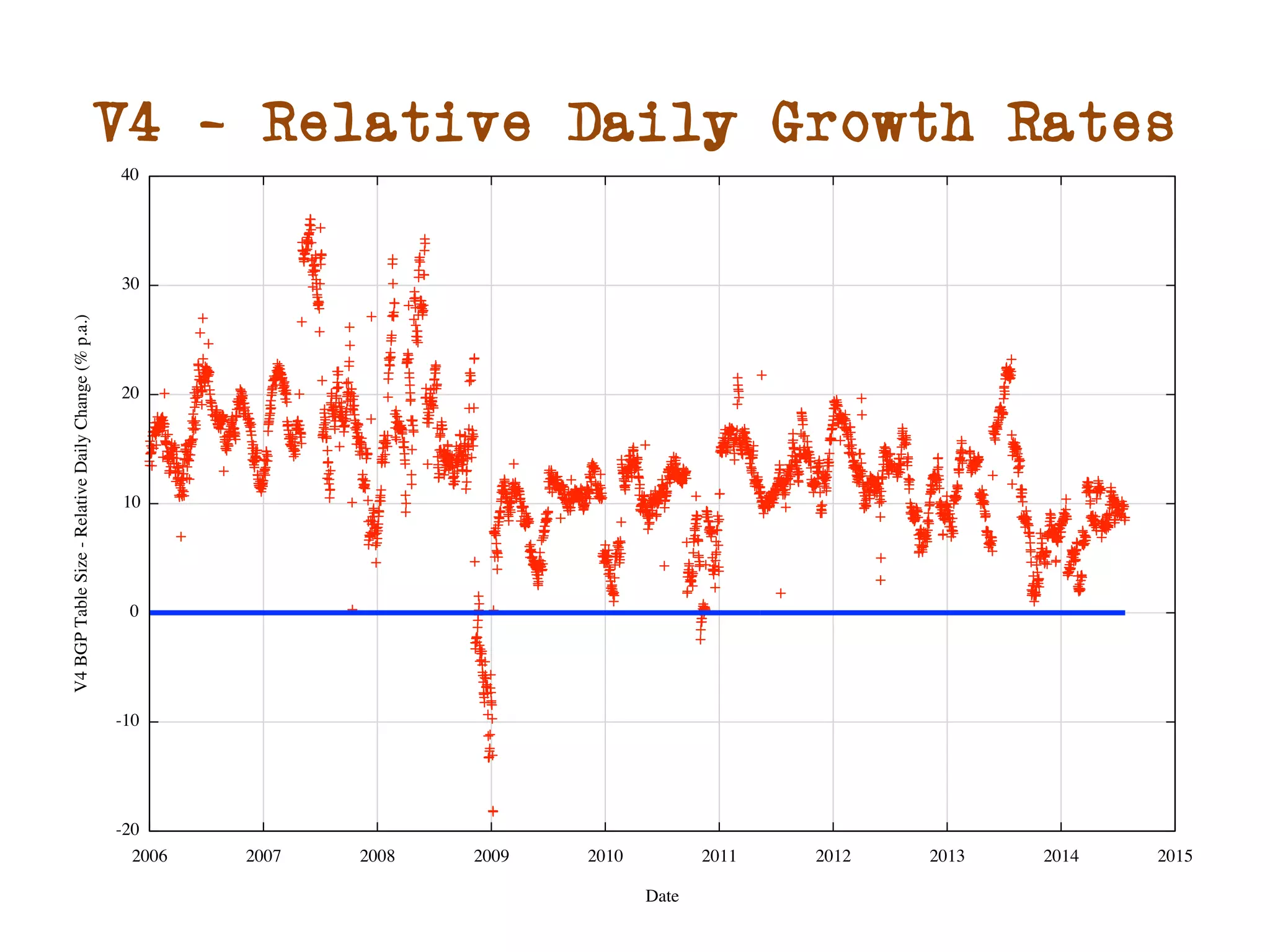
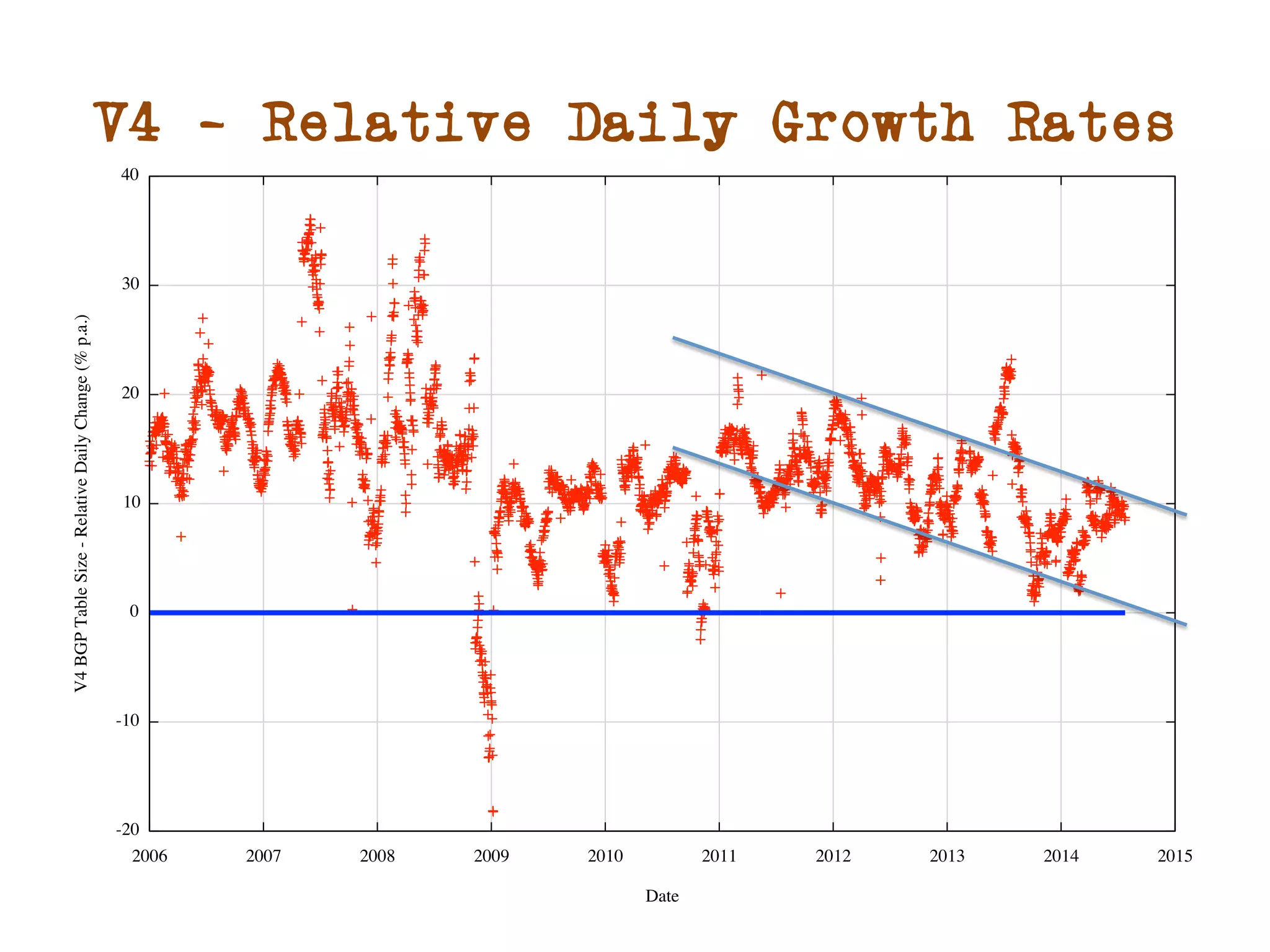
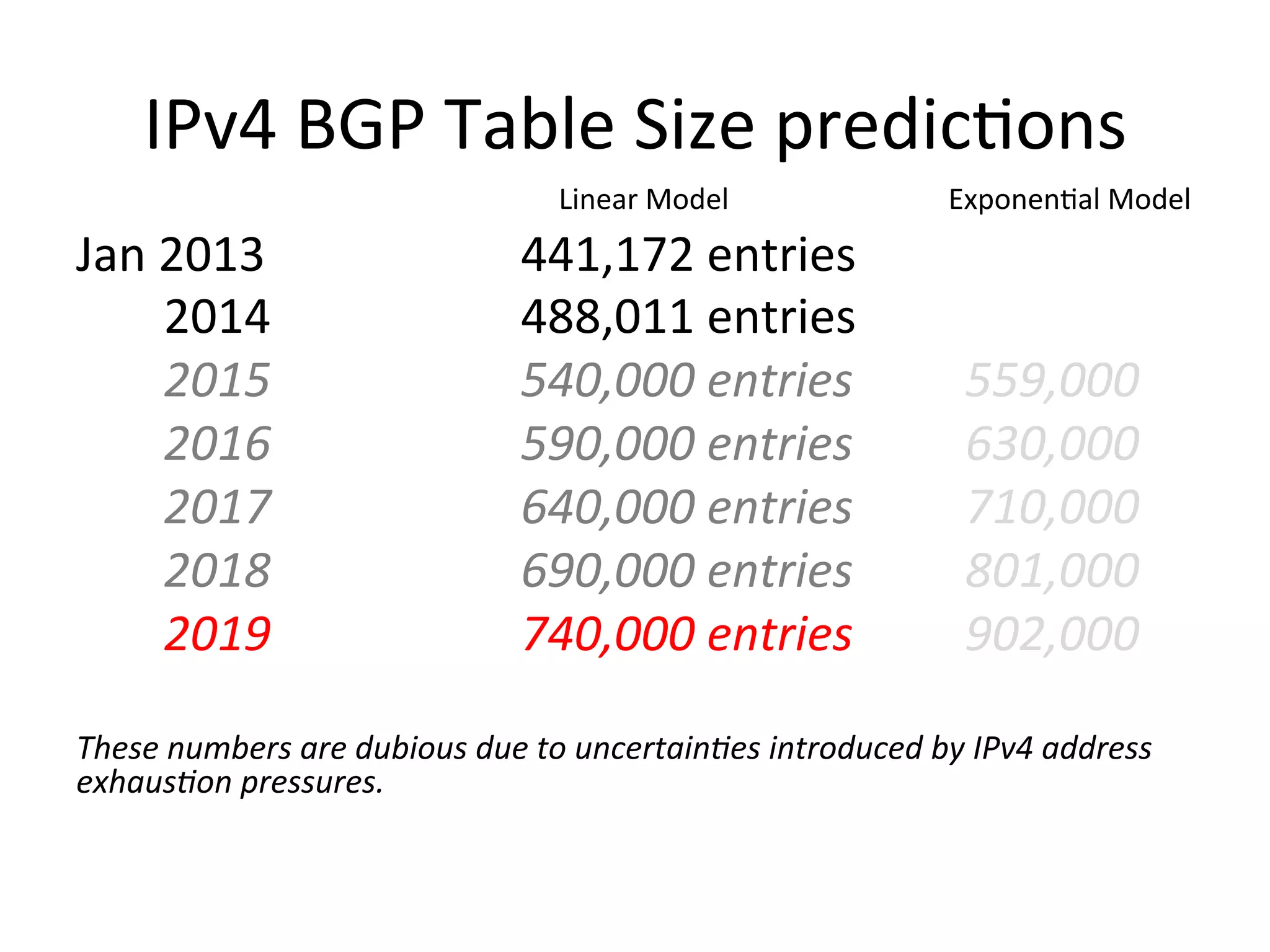
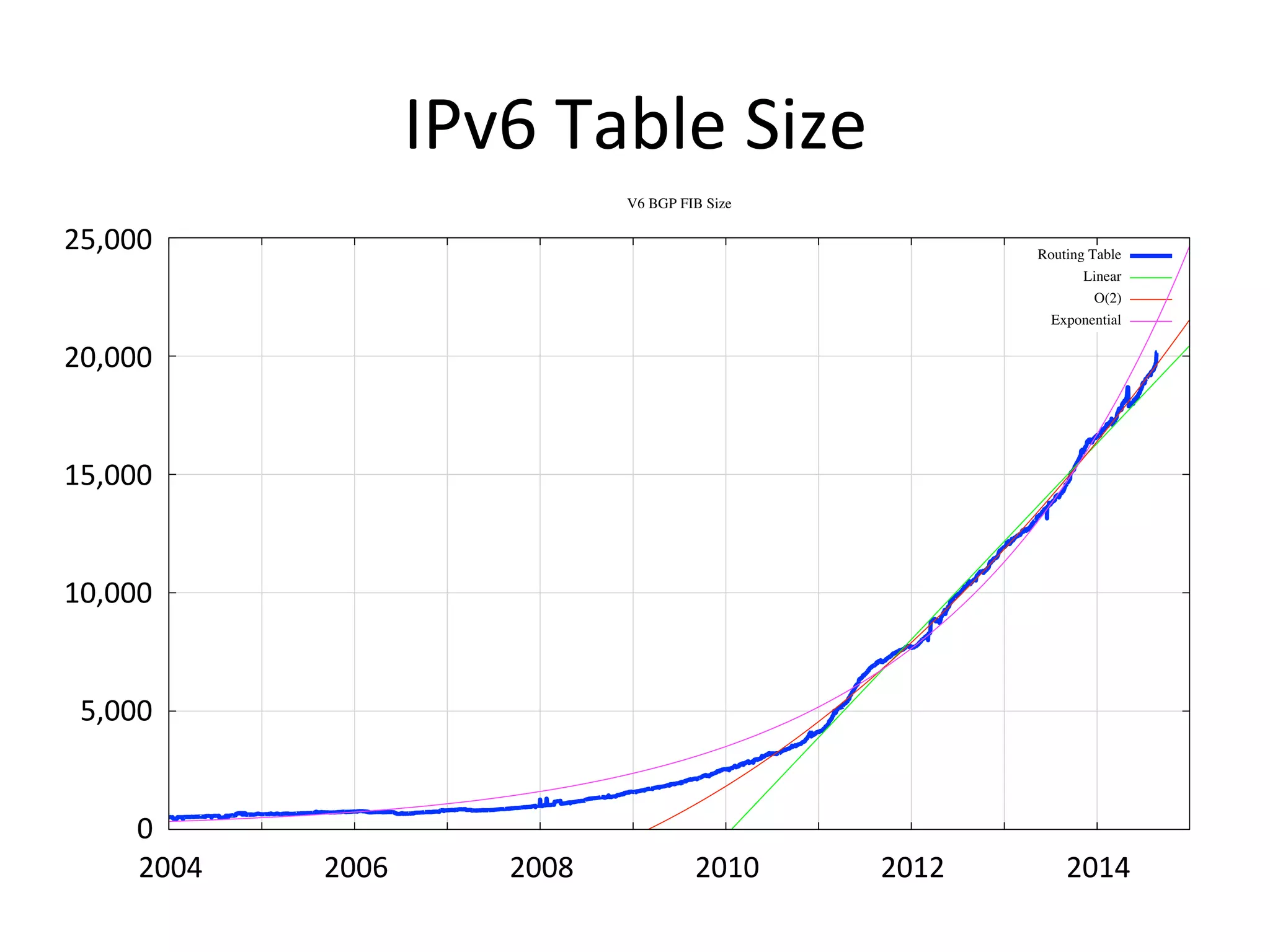
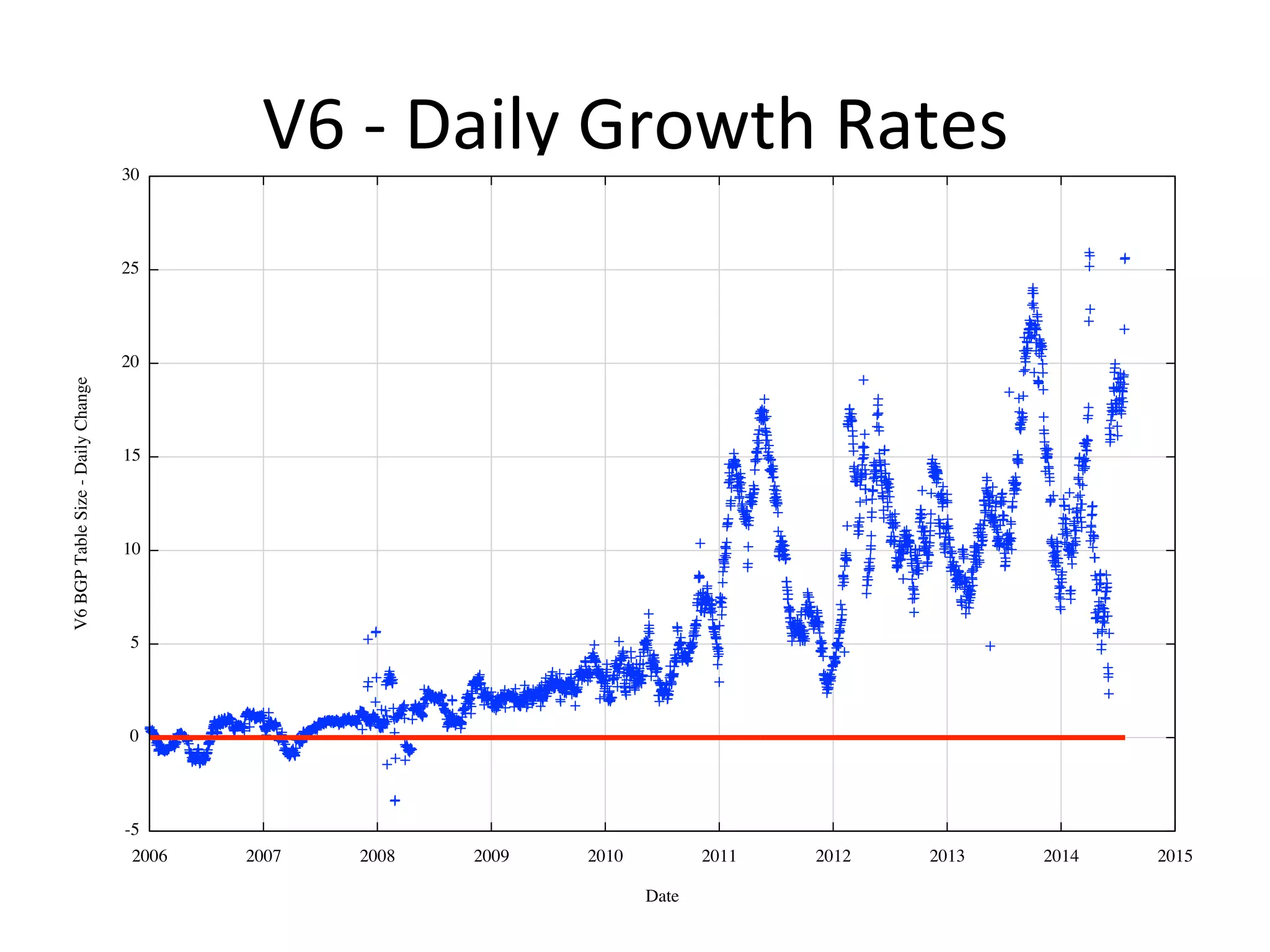
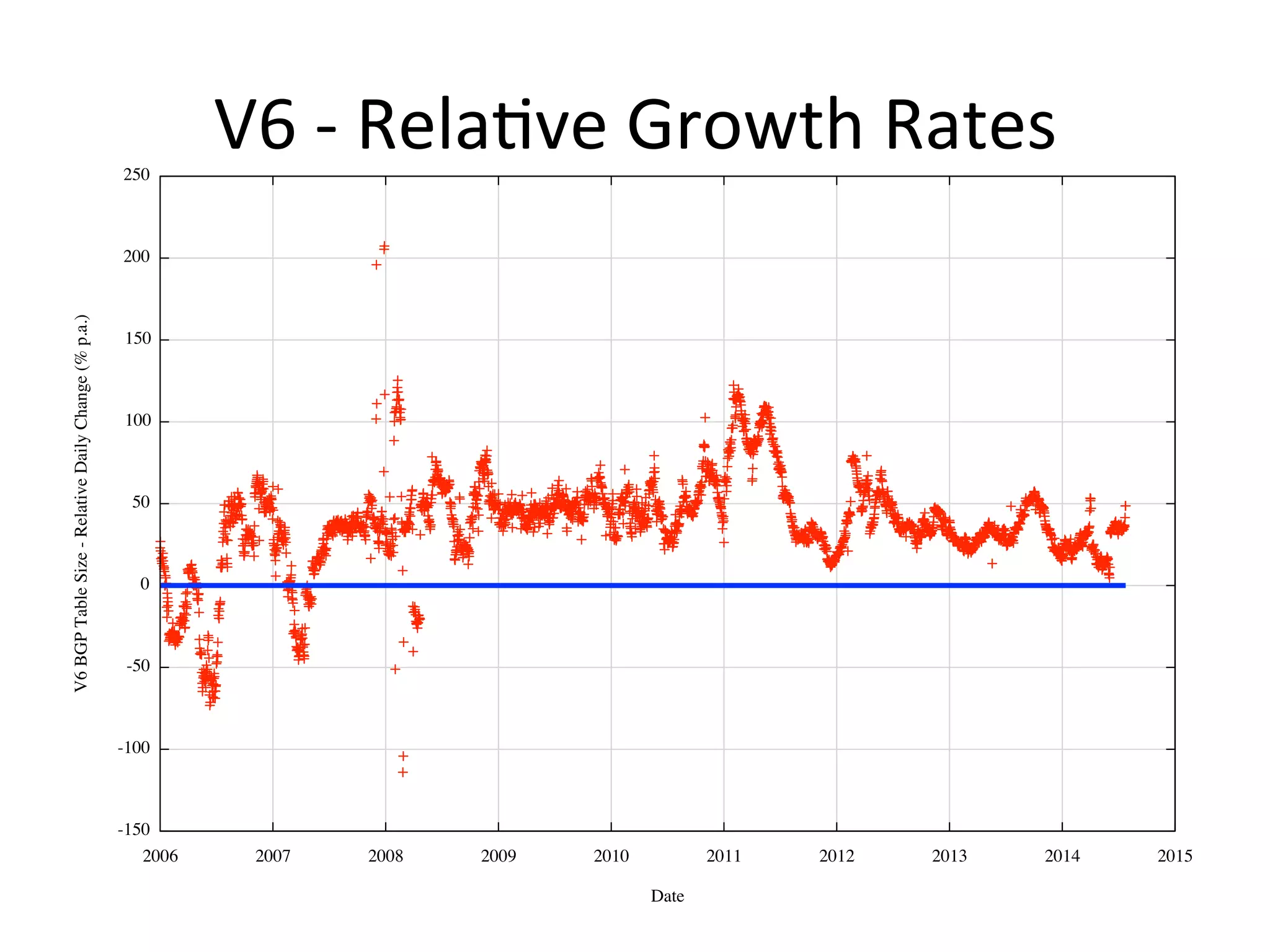
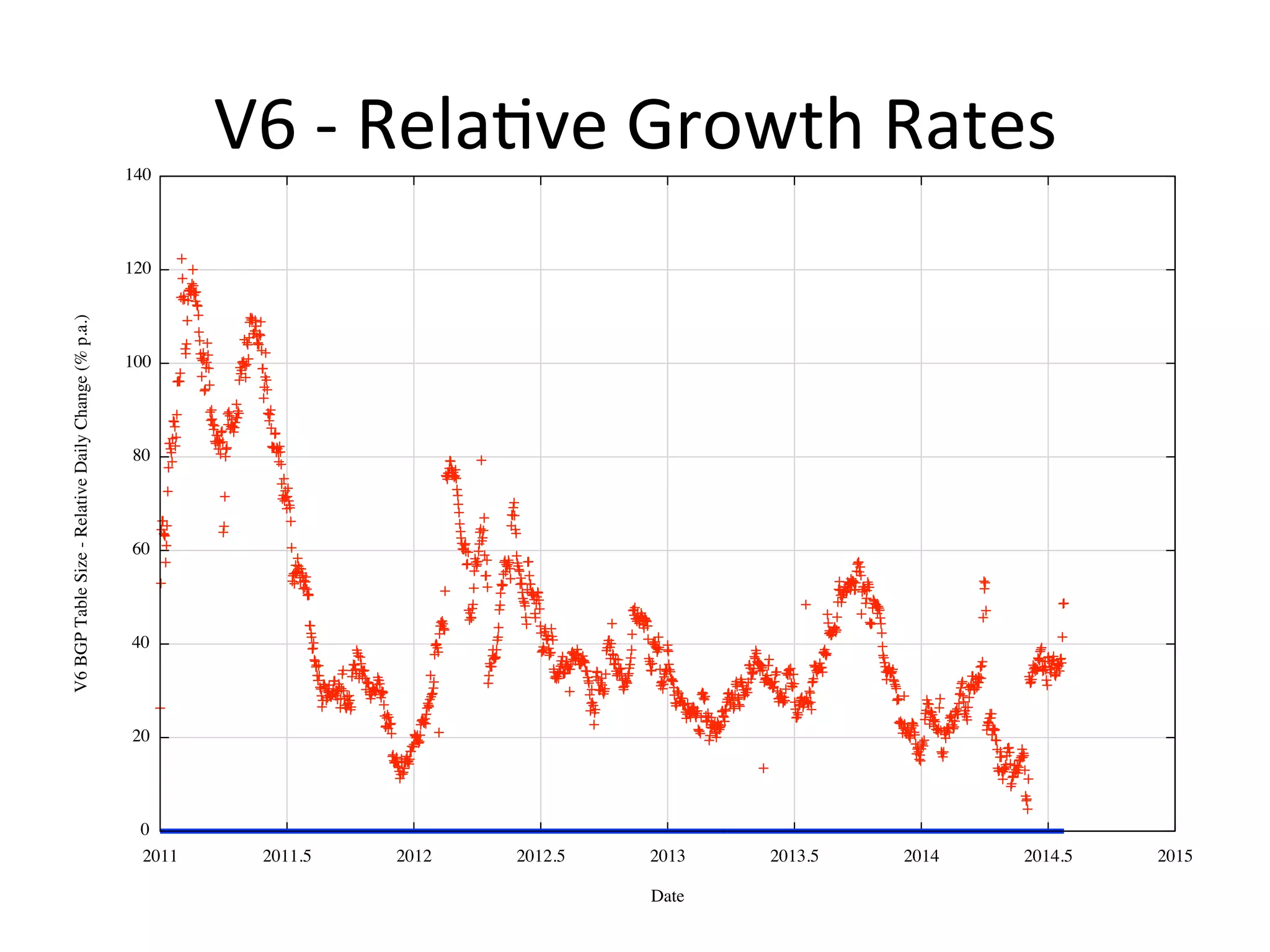
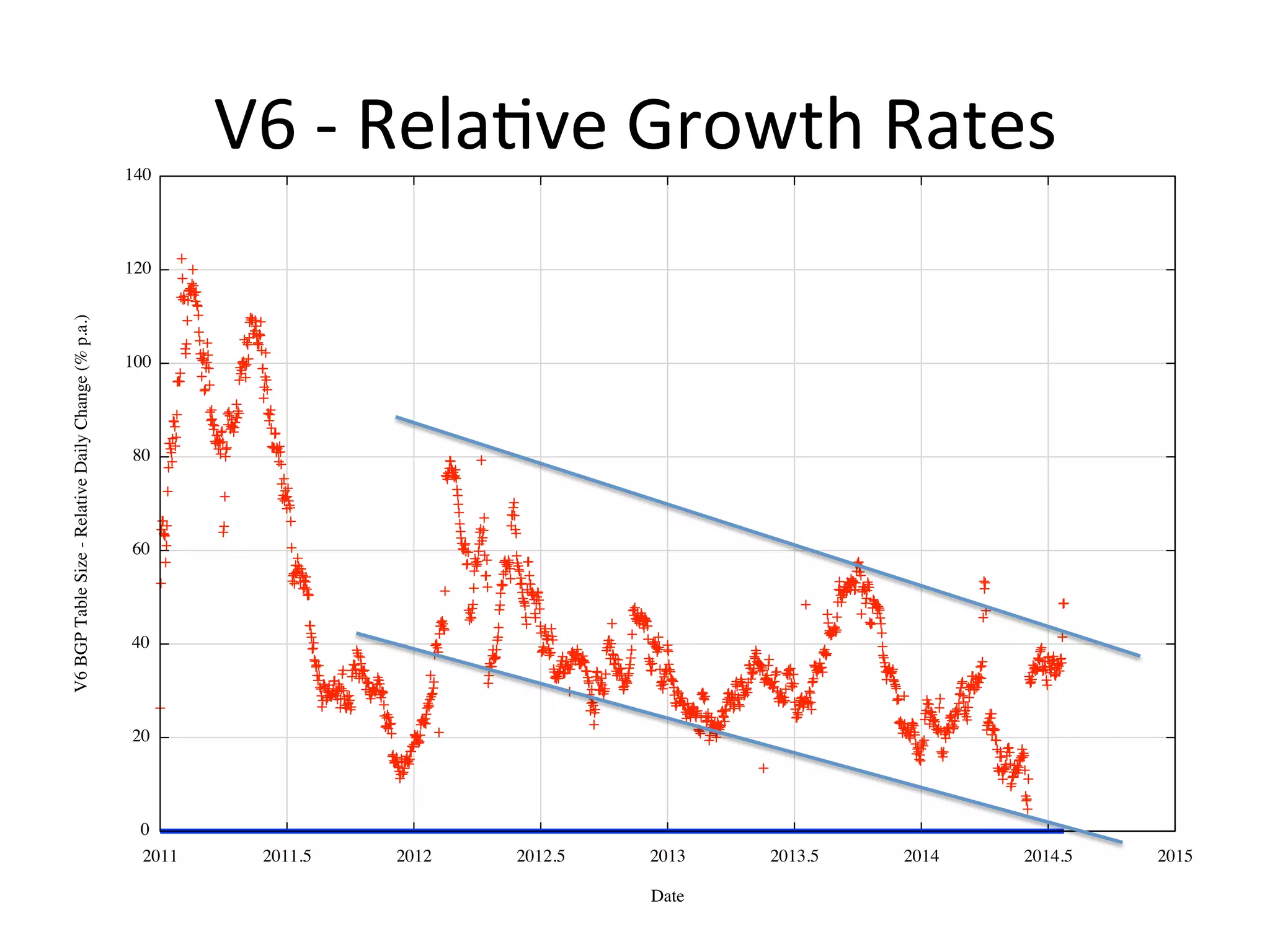
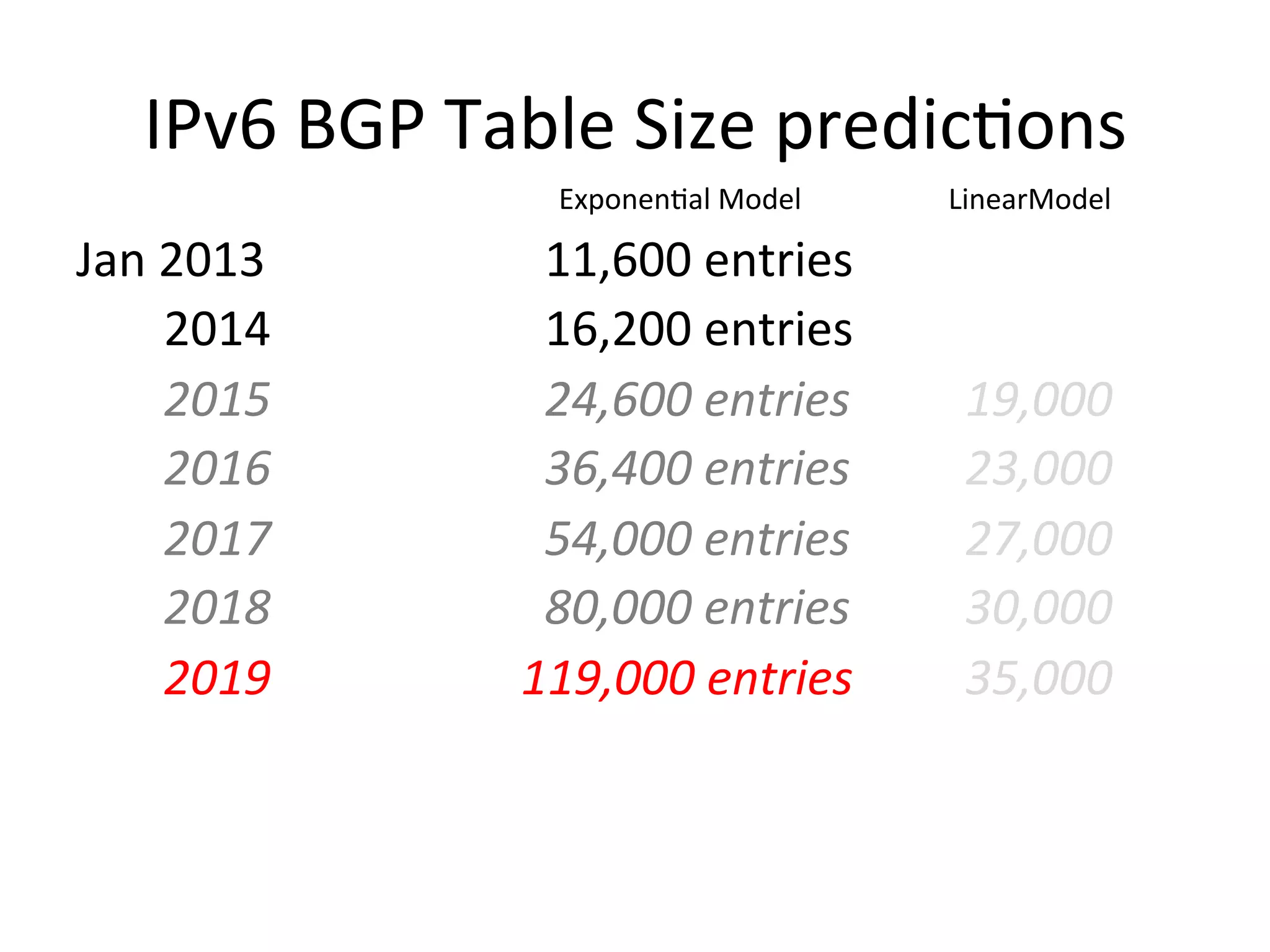
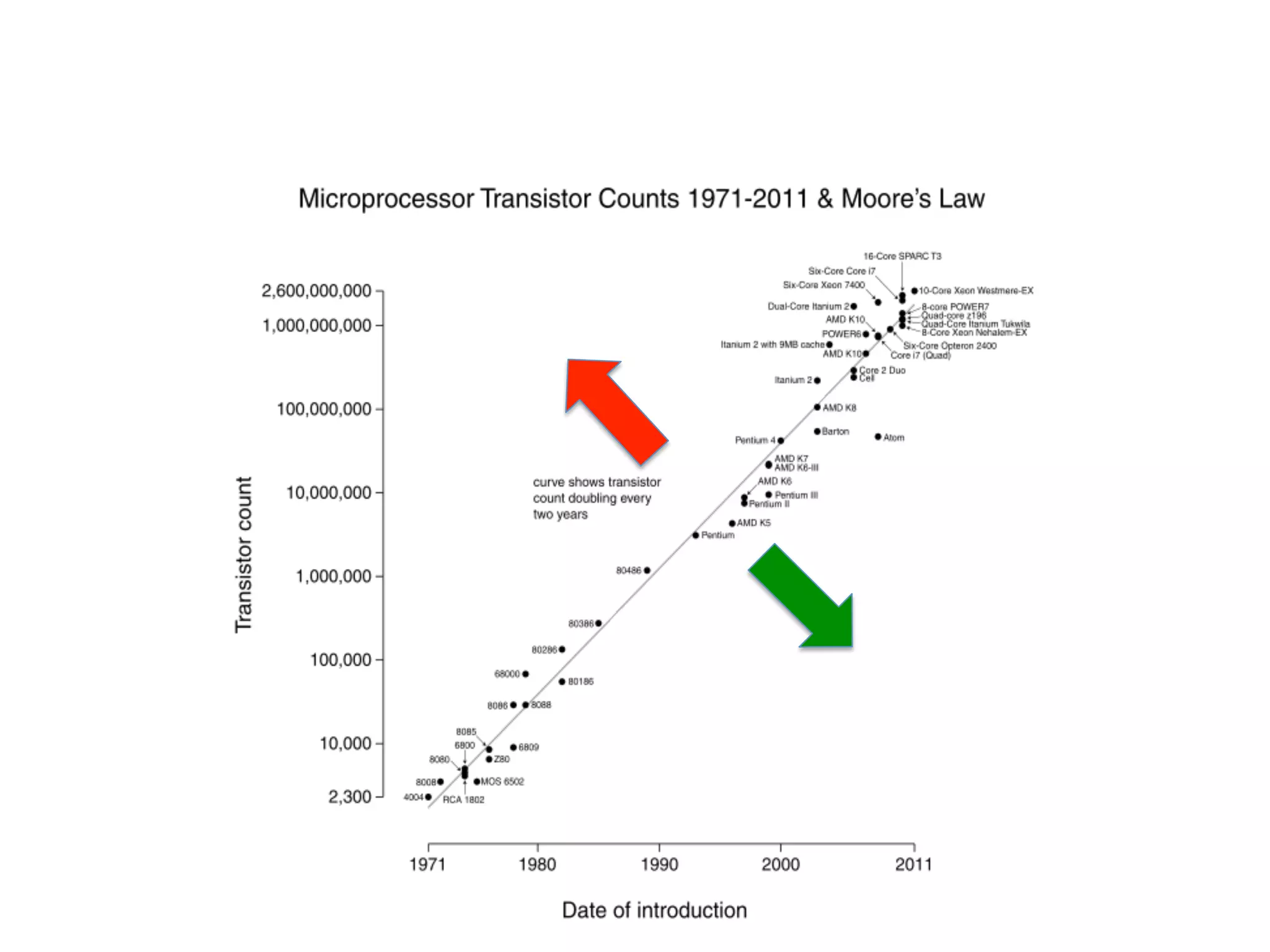
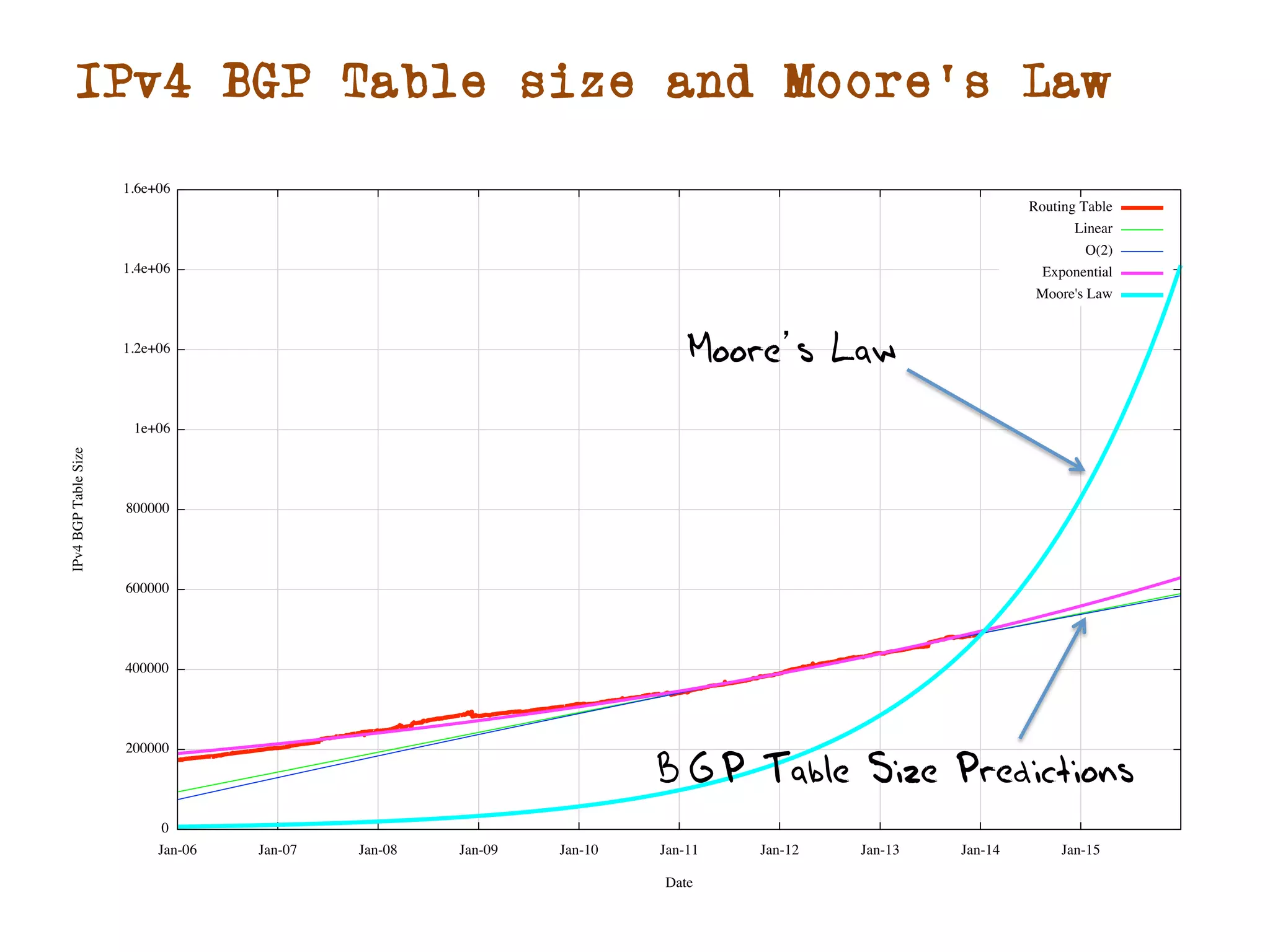
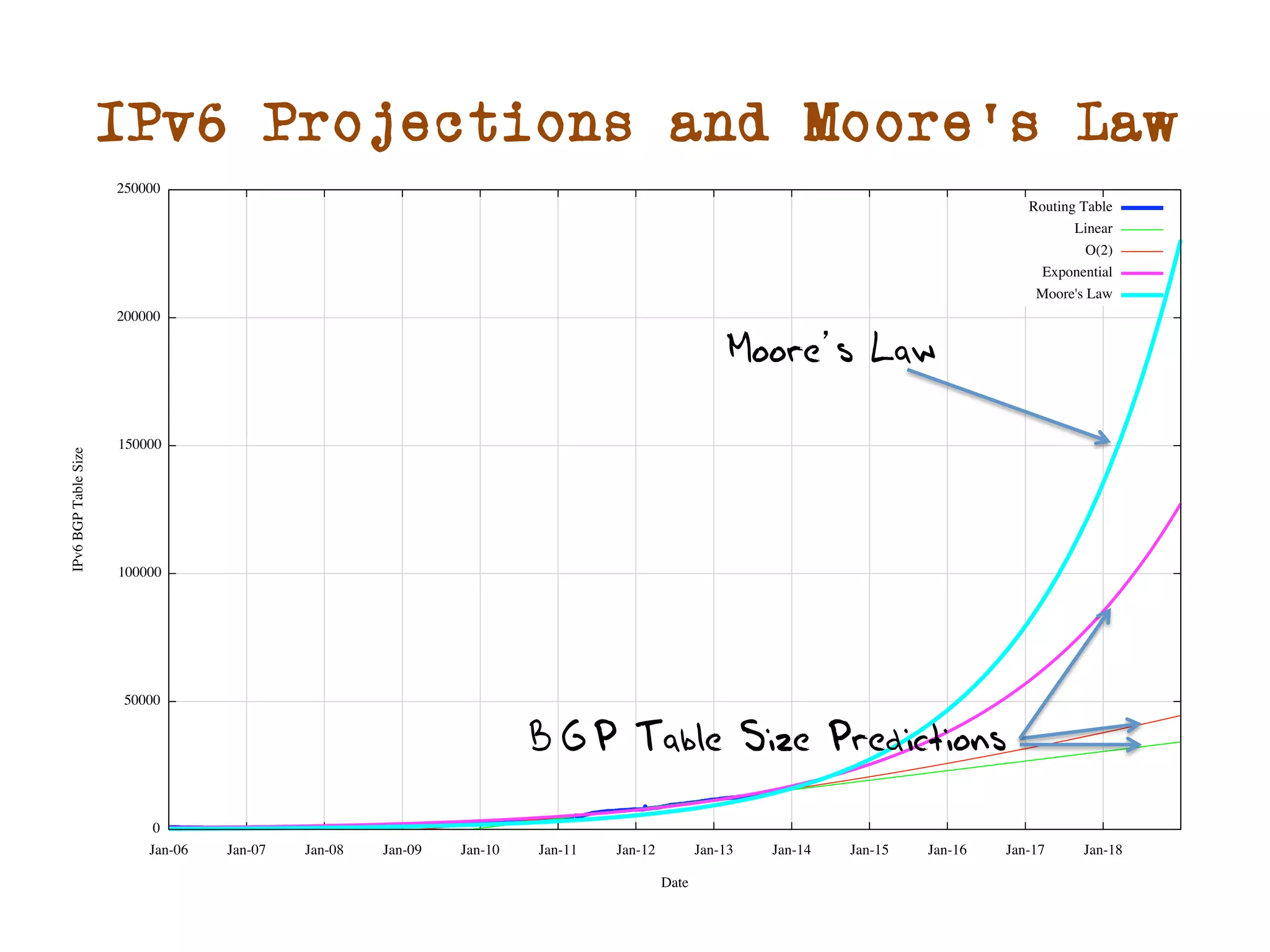
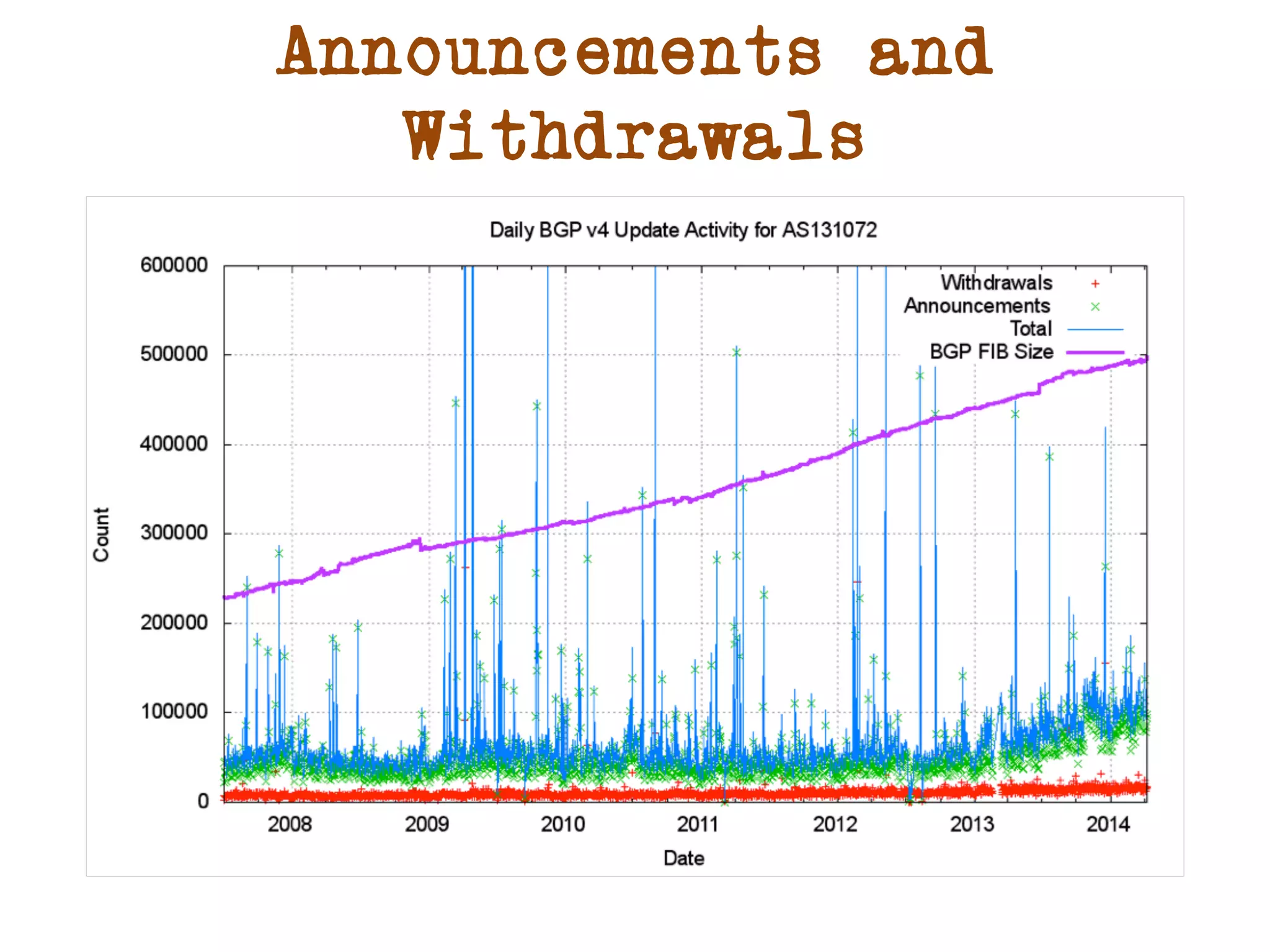
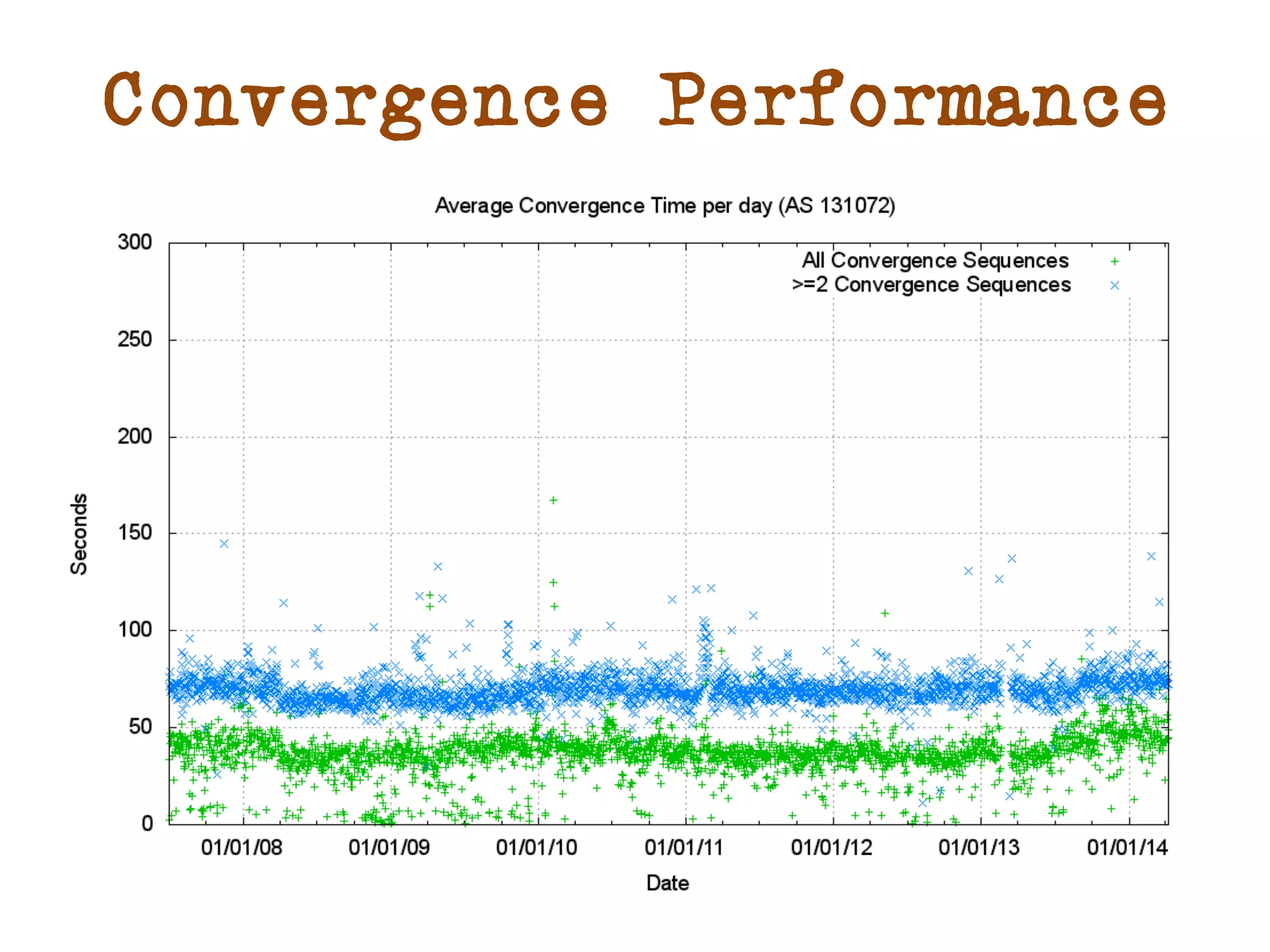
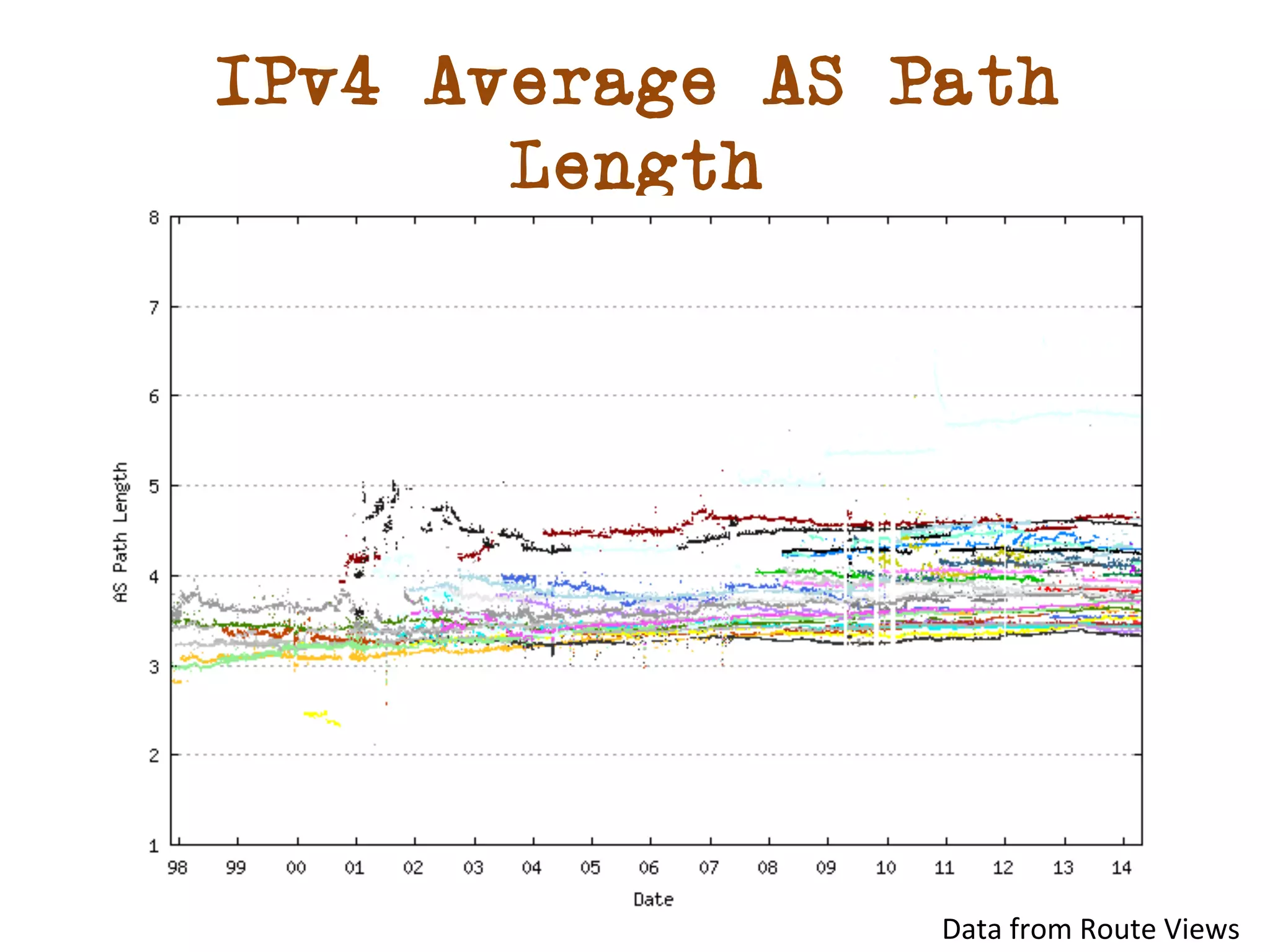
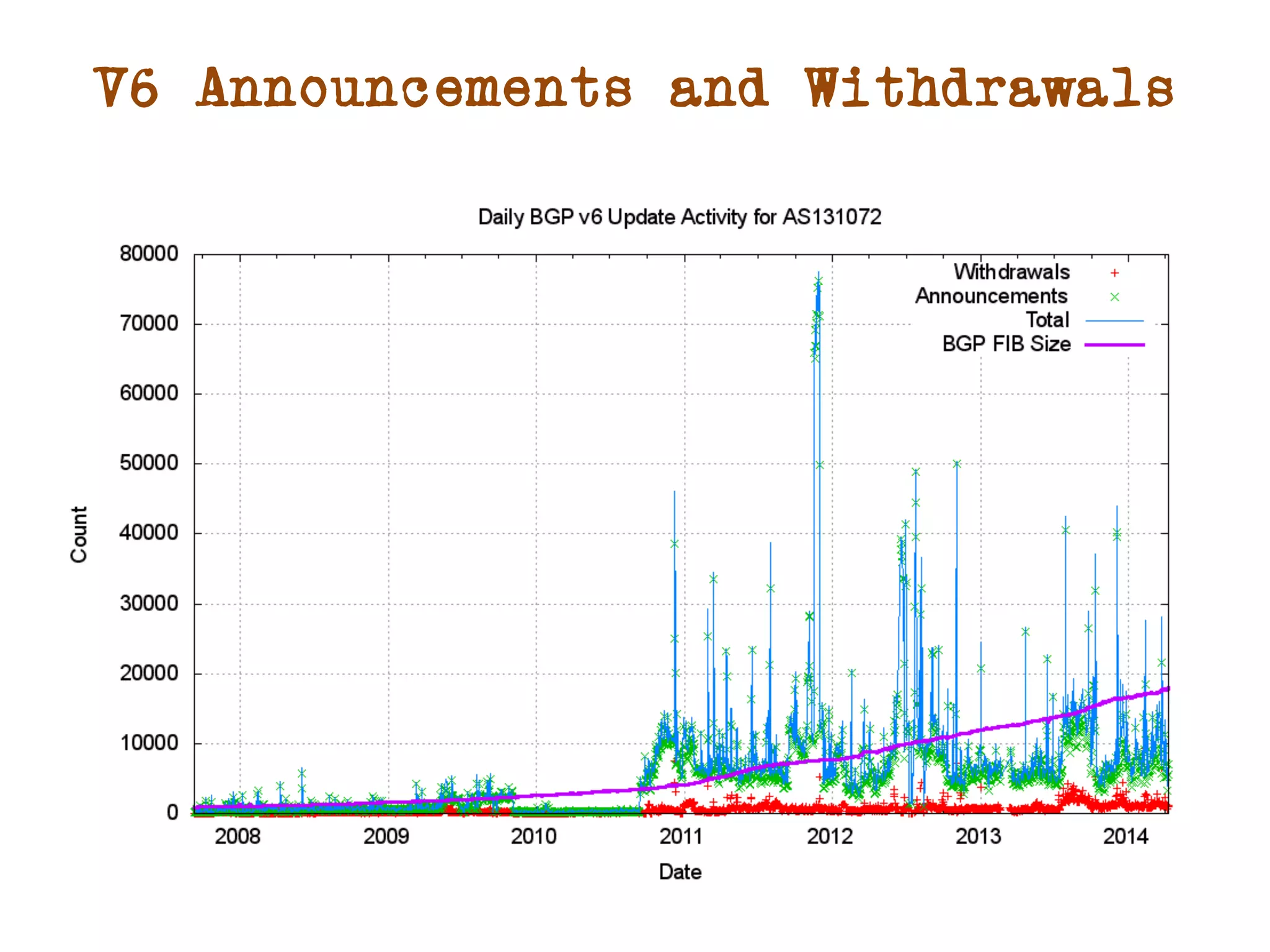
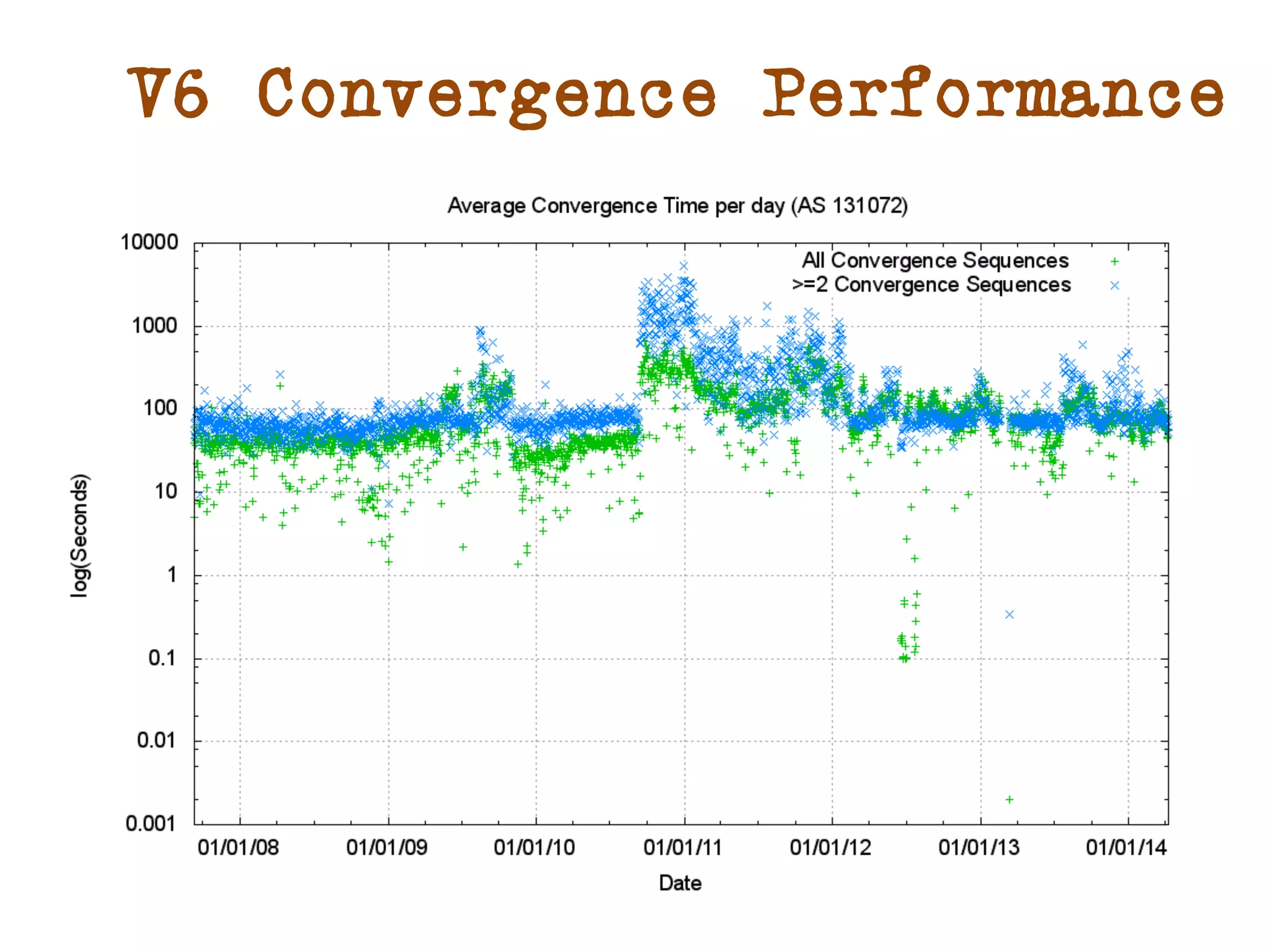
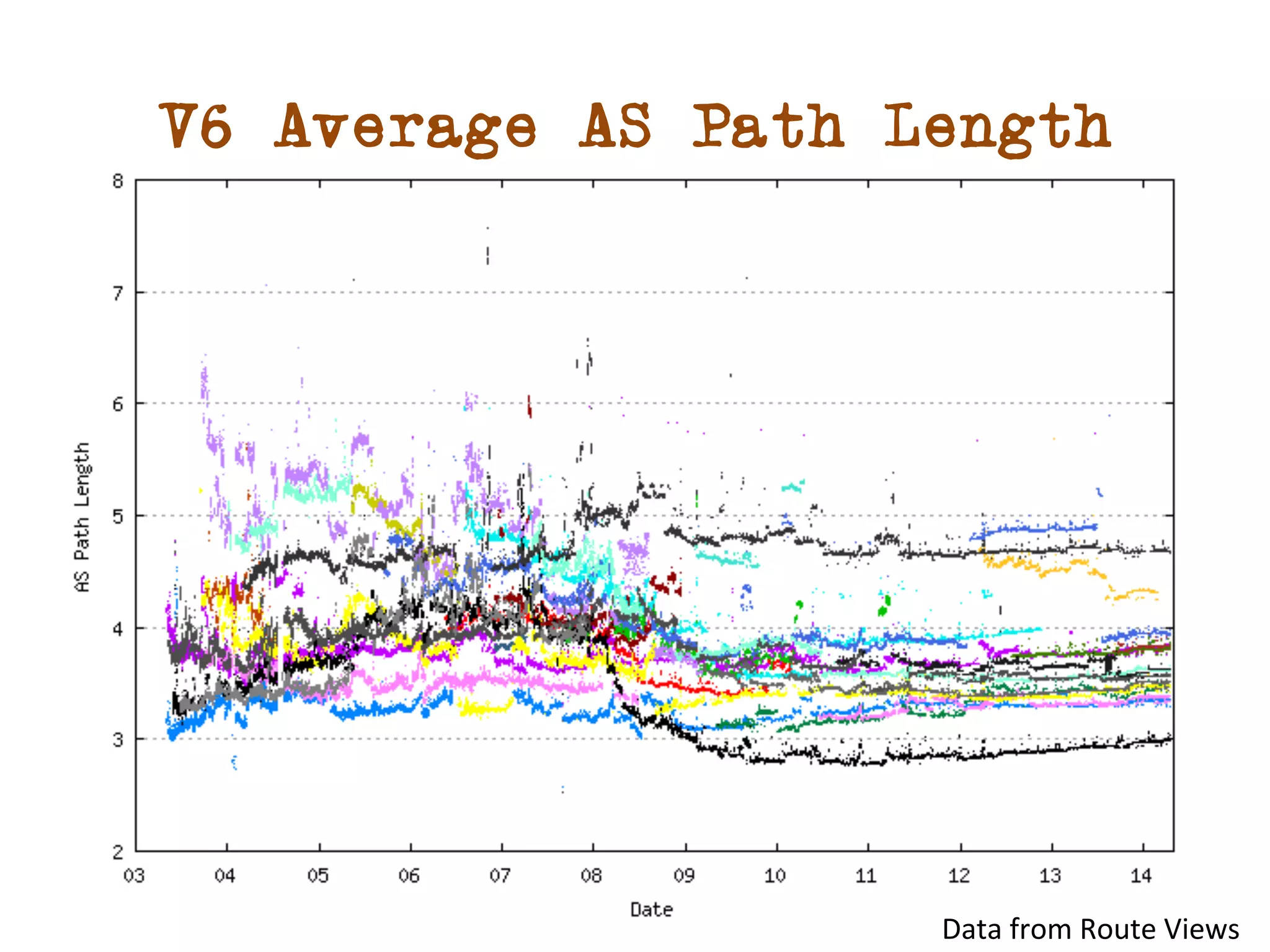
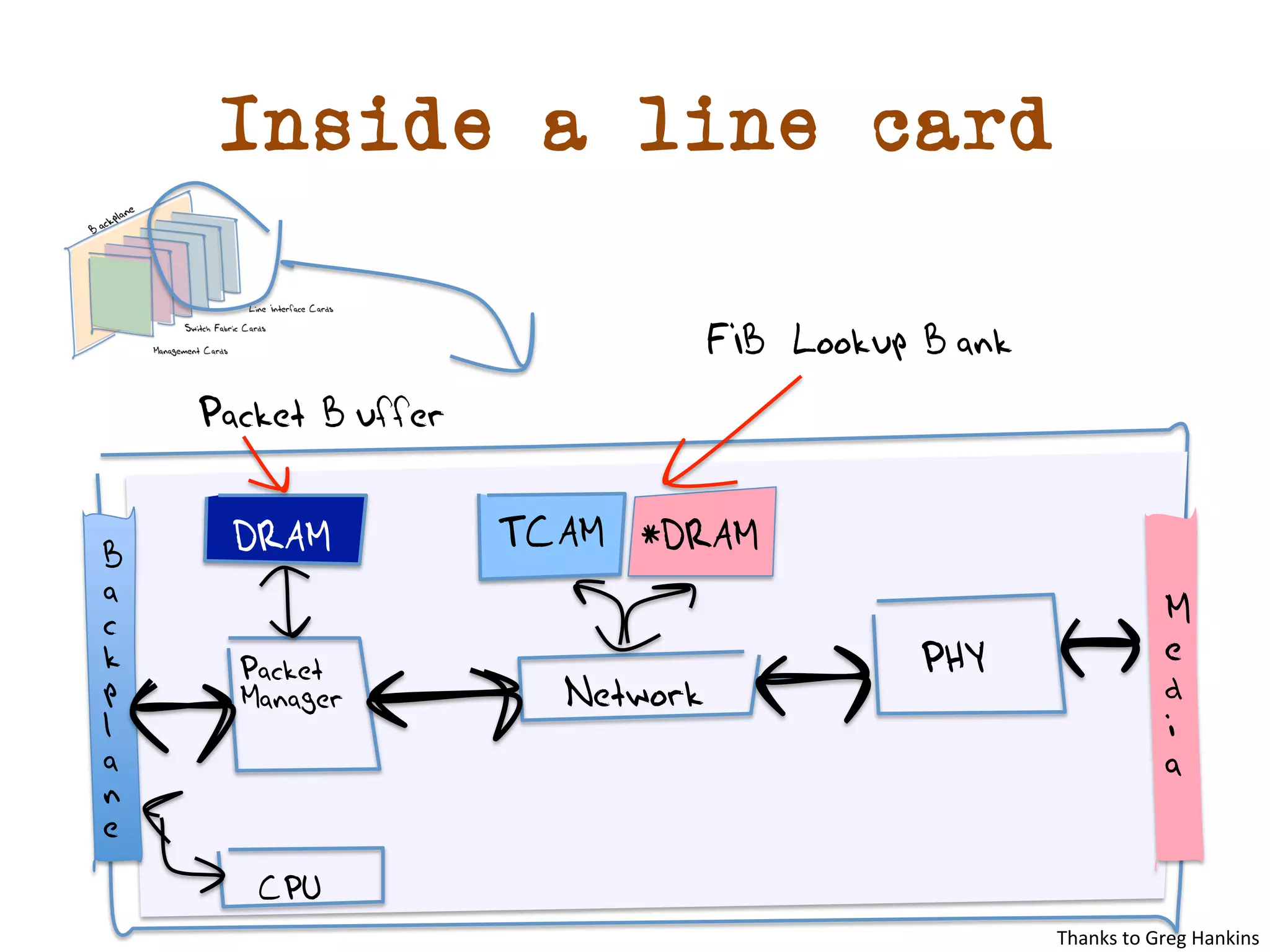
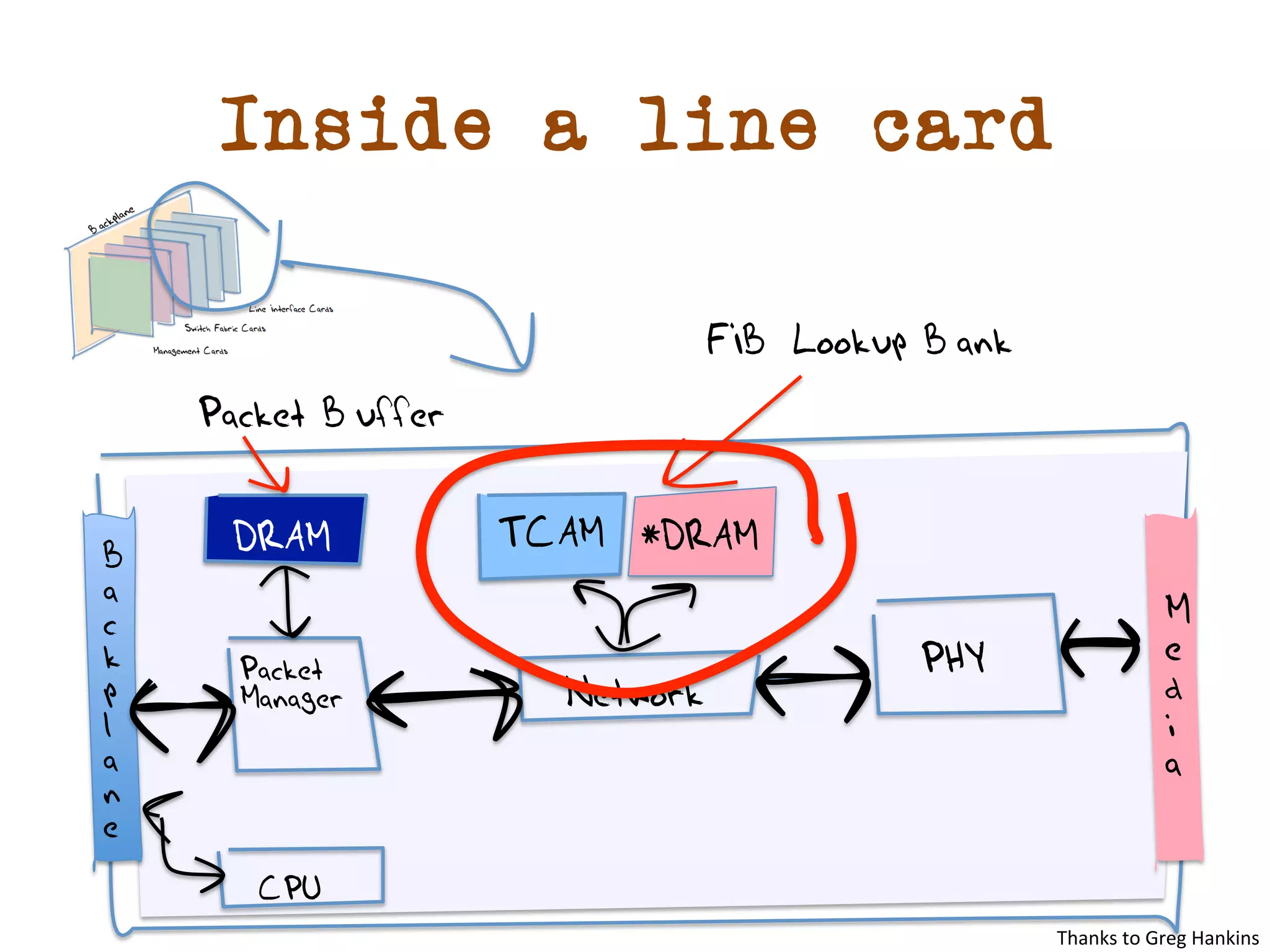
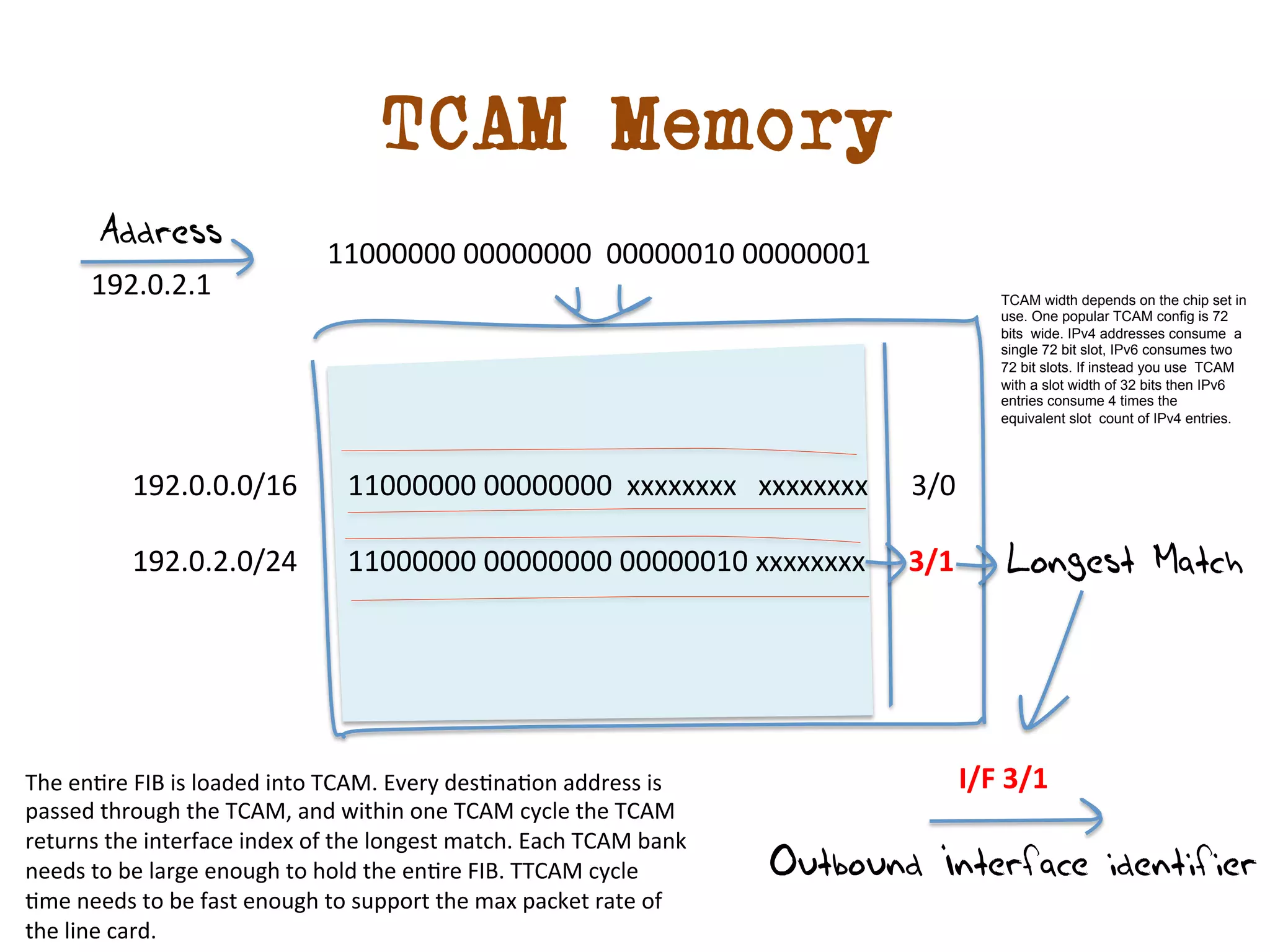
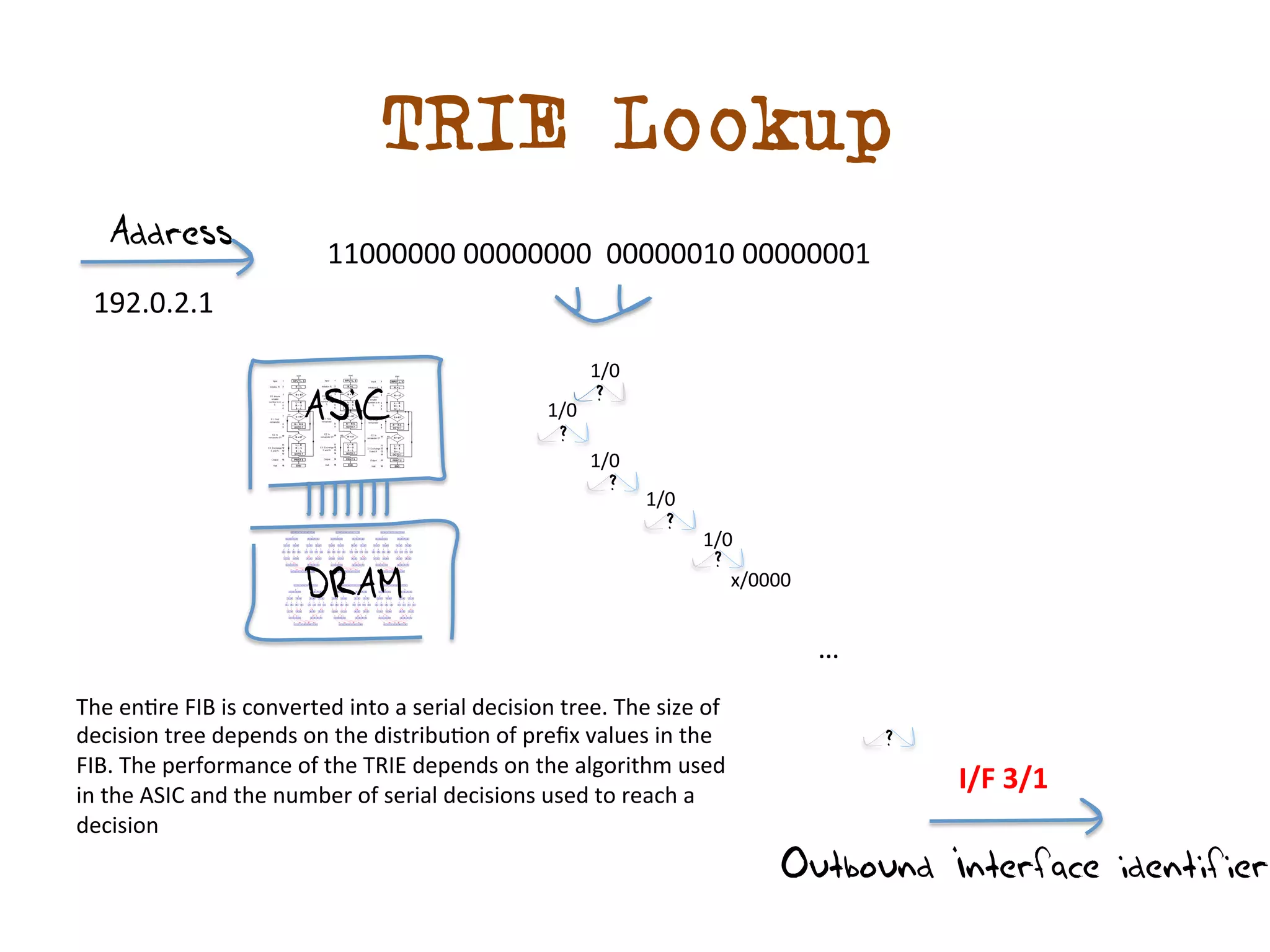
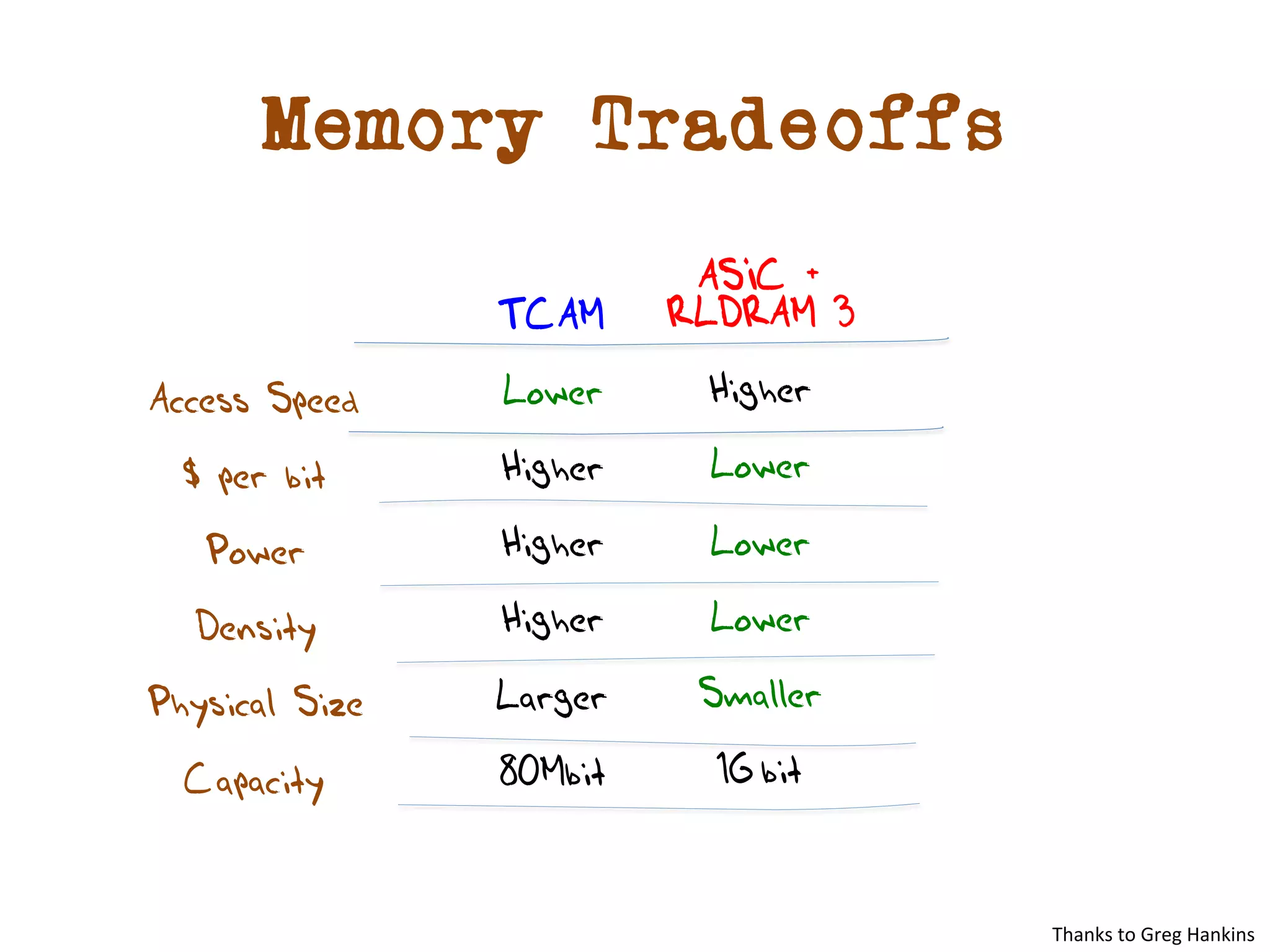
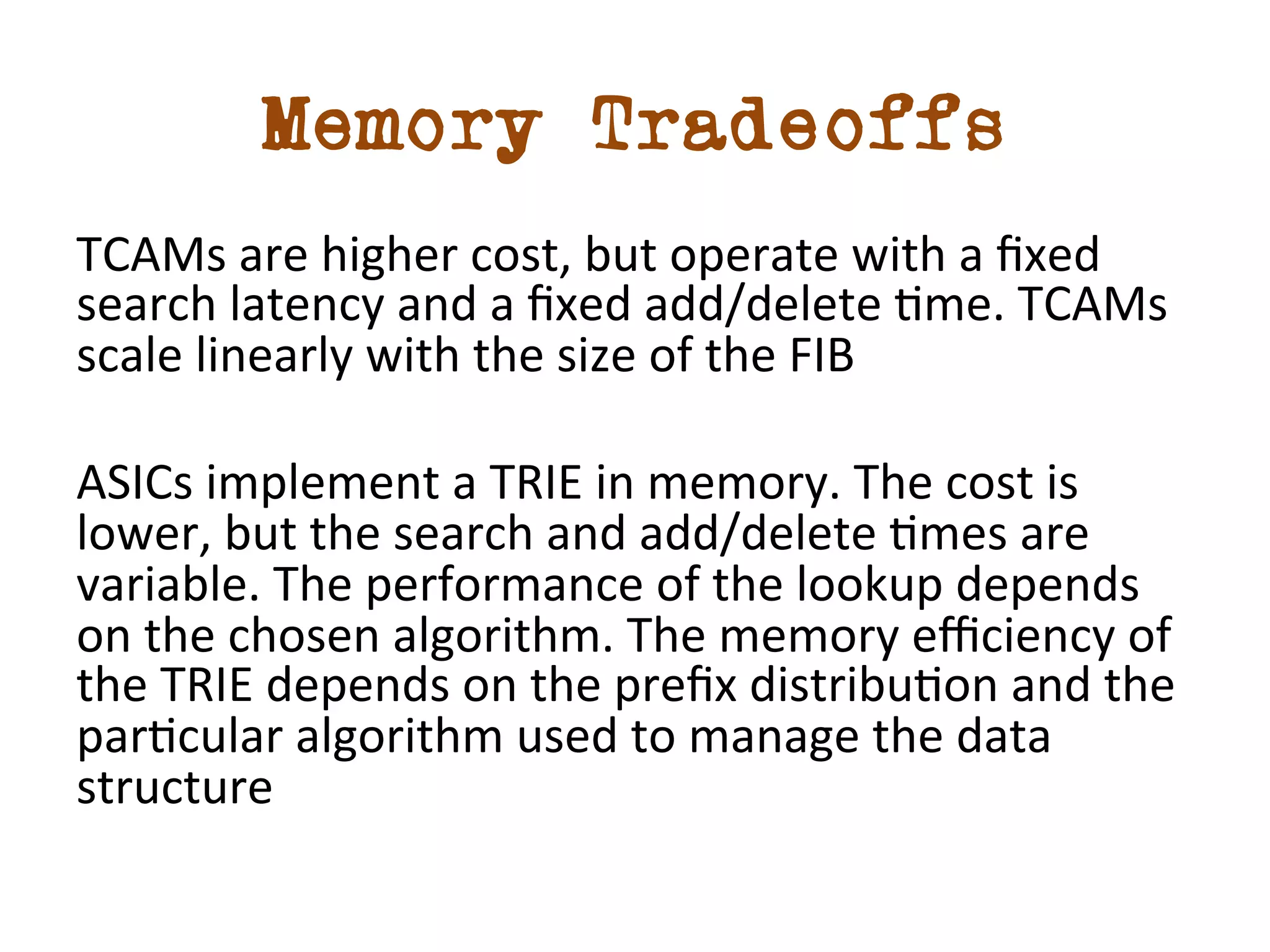
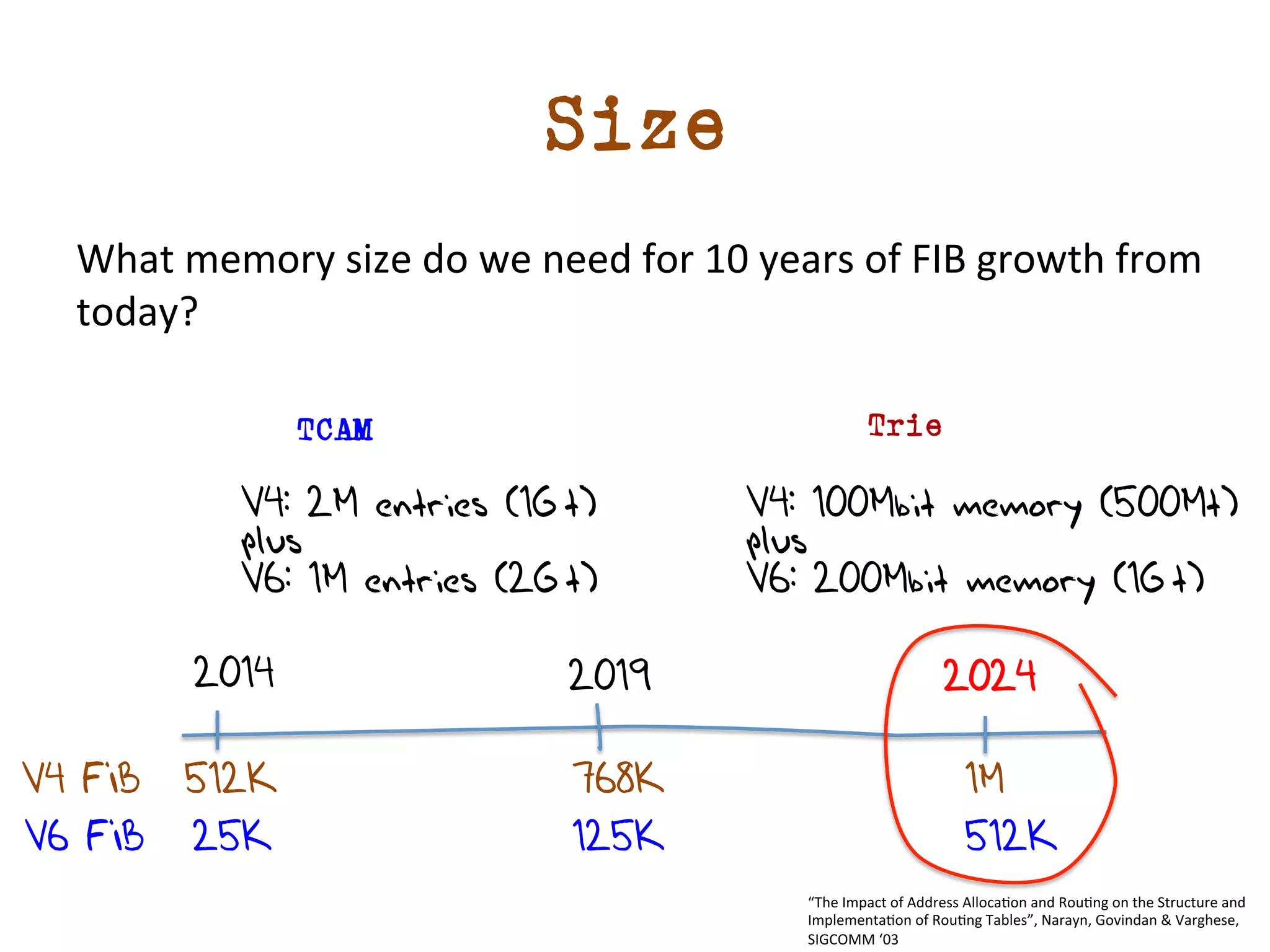
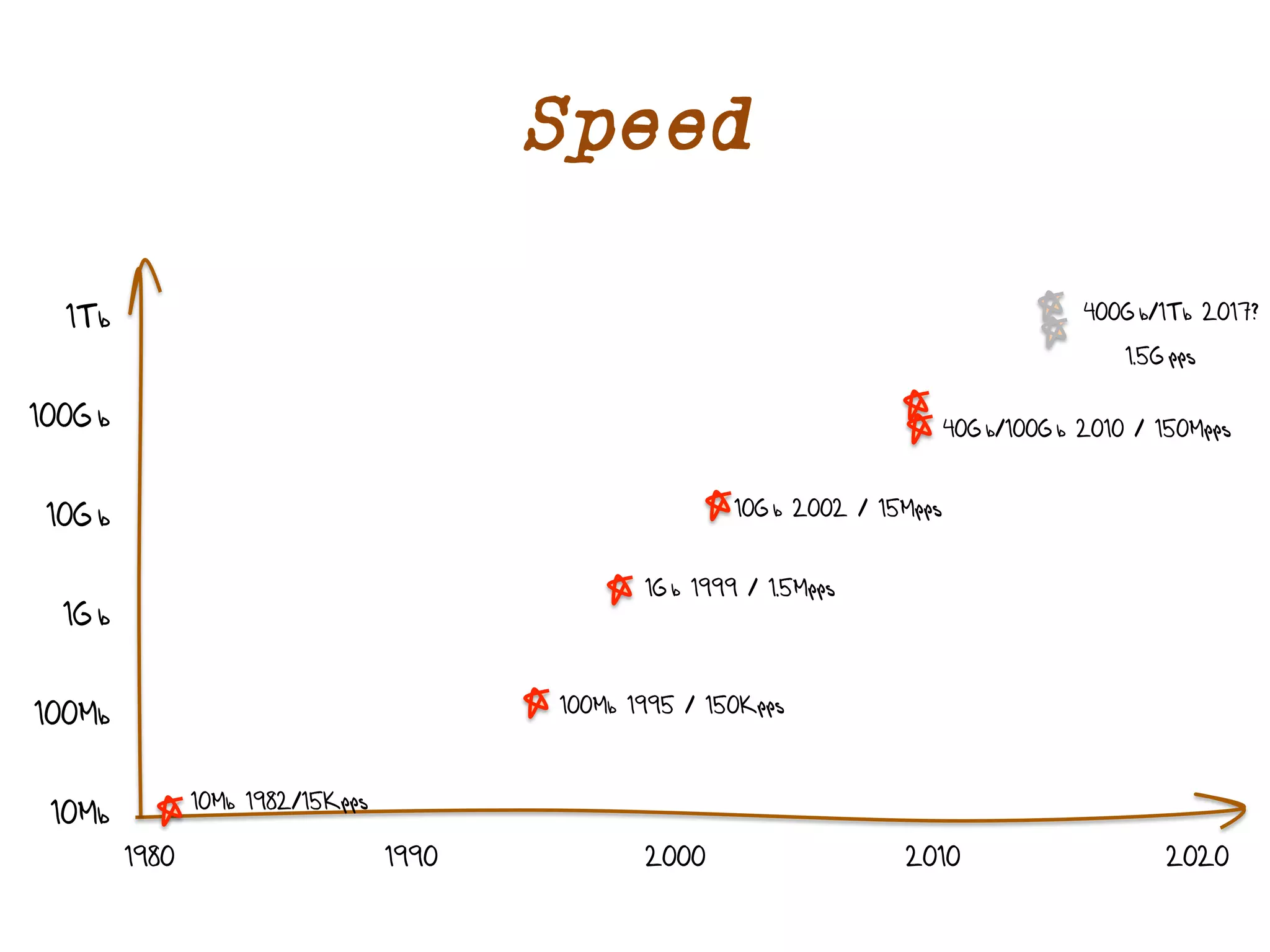
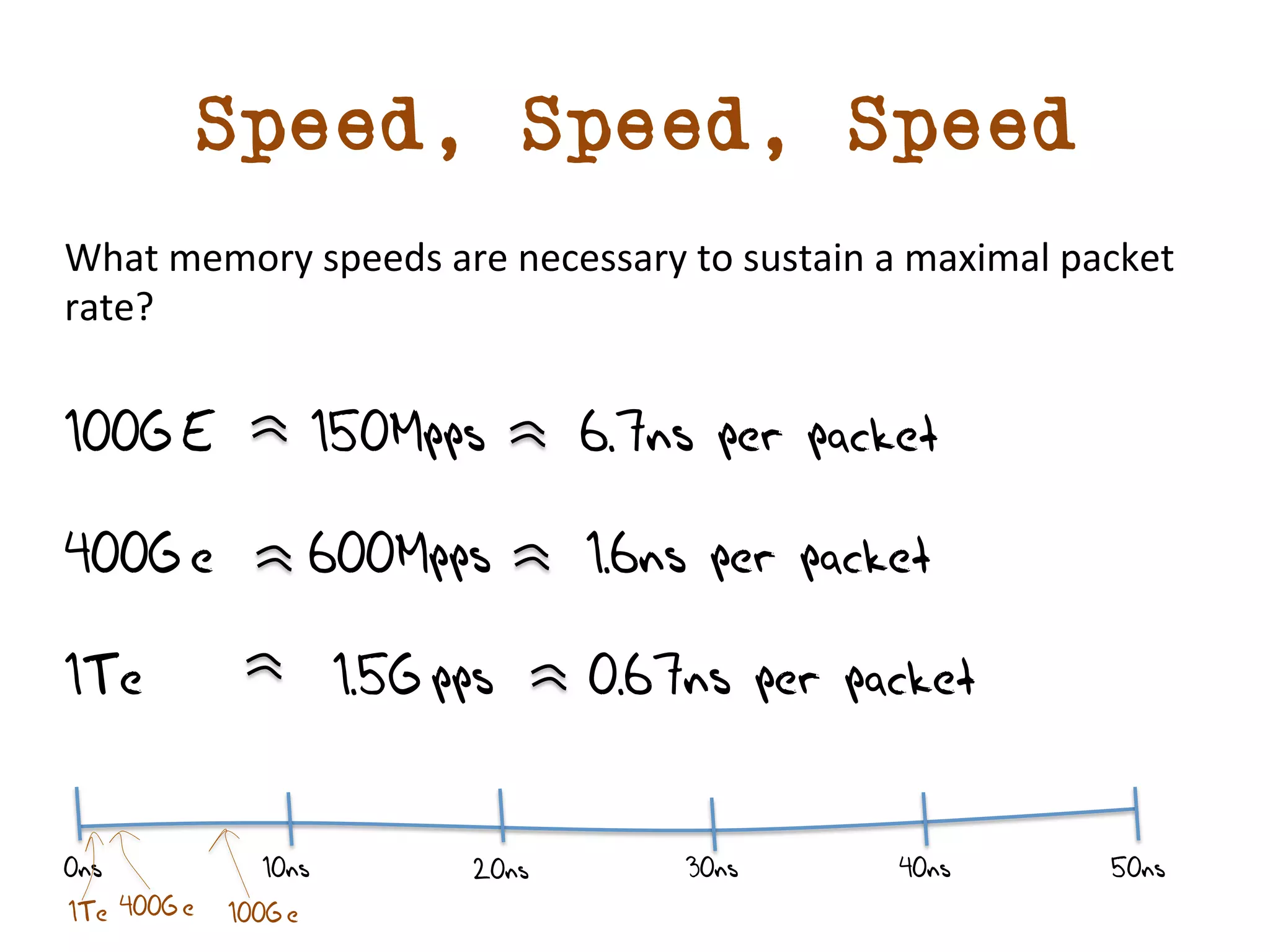
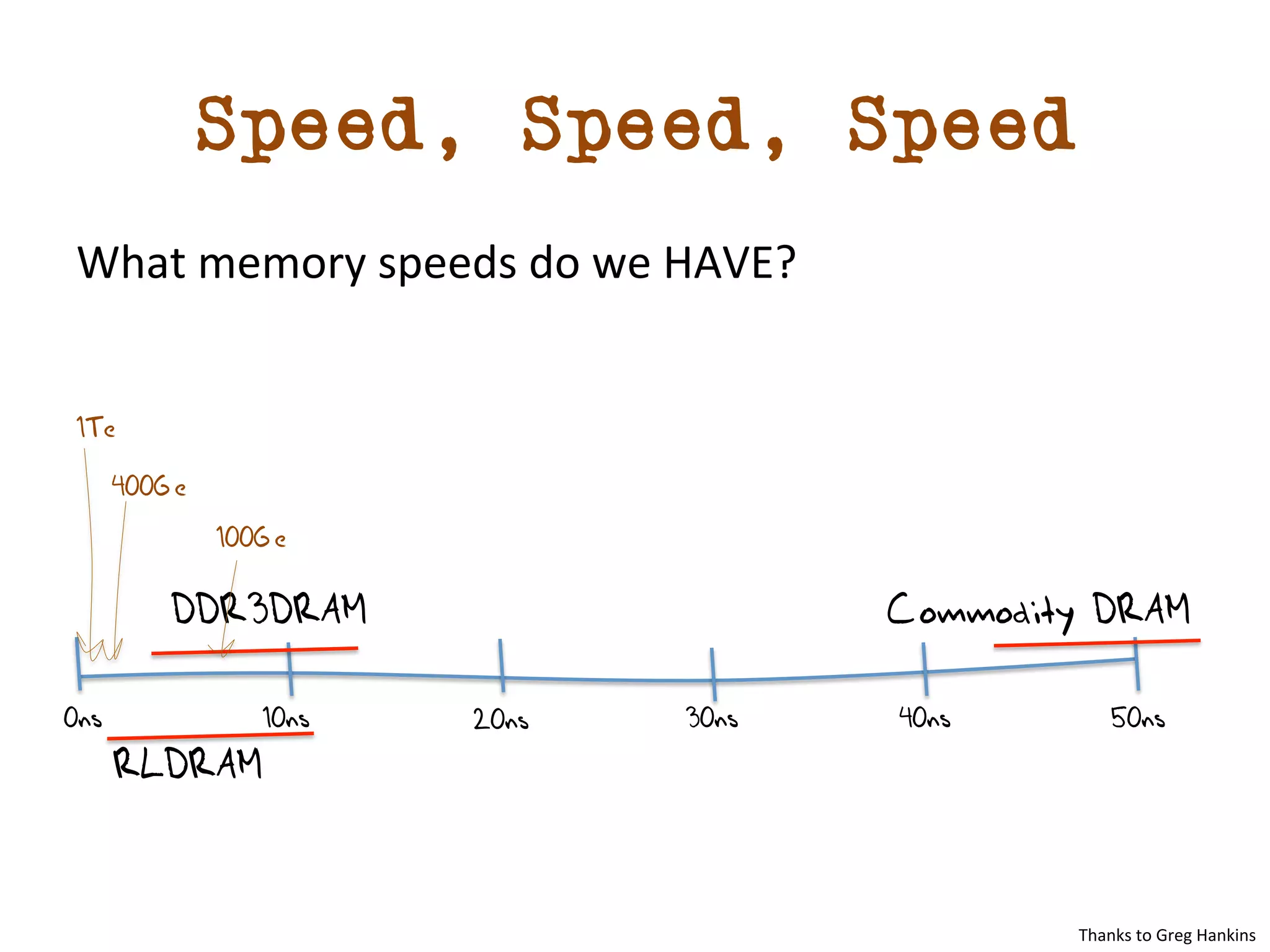
The document discusses the implications of the number 512 in the context of BGP routing table growth, specifically focusing on the total IPv4 FIB size surpassing 512k entries and its default significance in routing systems. It analyzes historical and projected trends in both IPv4 and IPv6 prefix counts, highlighting a slowdown in IPv4 growth while IPv6 experiences rapid increases. Additionally, it covers the technical challenges and memory requirements for sustaining future network speeds and the importance of BGP updates in the routing environment.