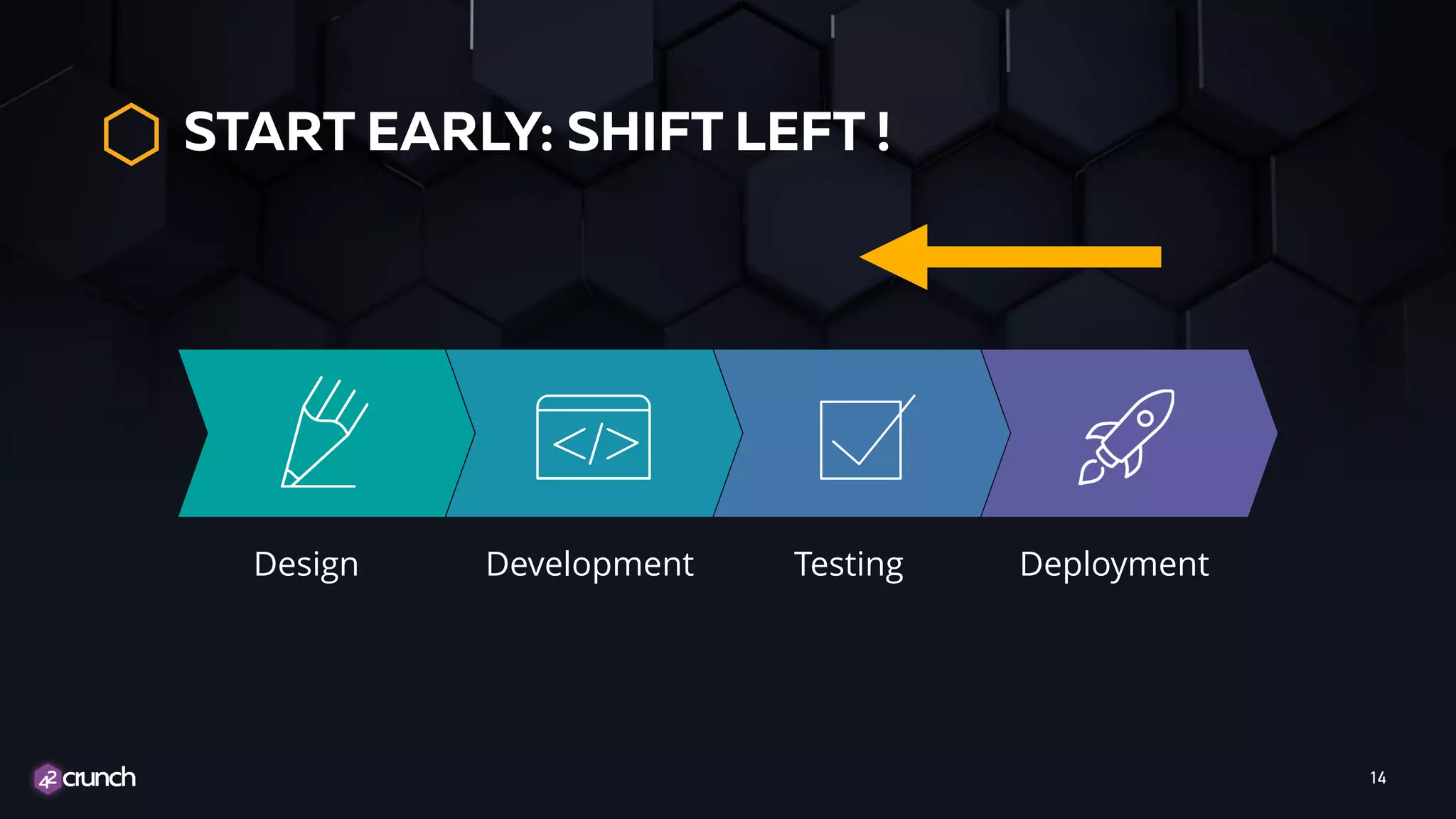
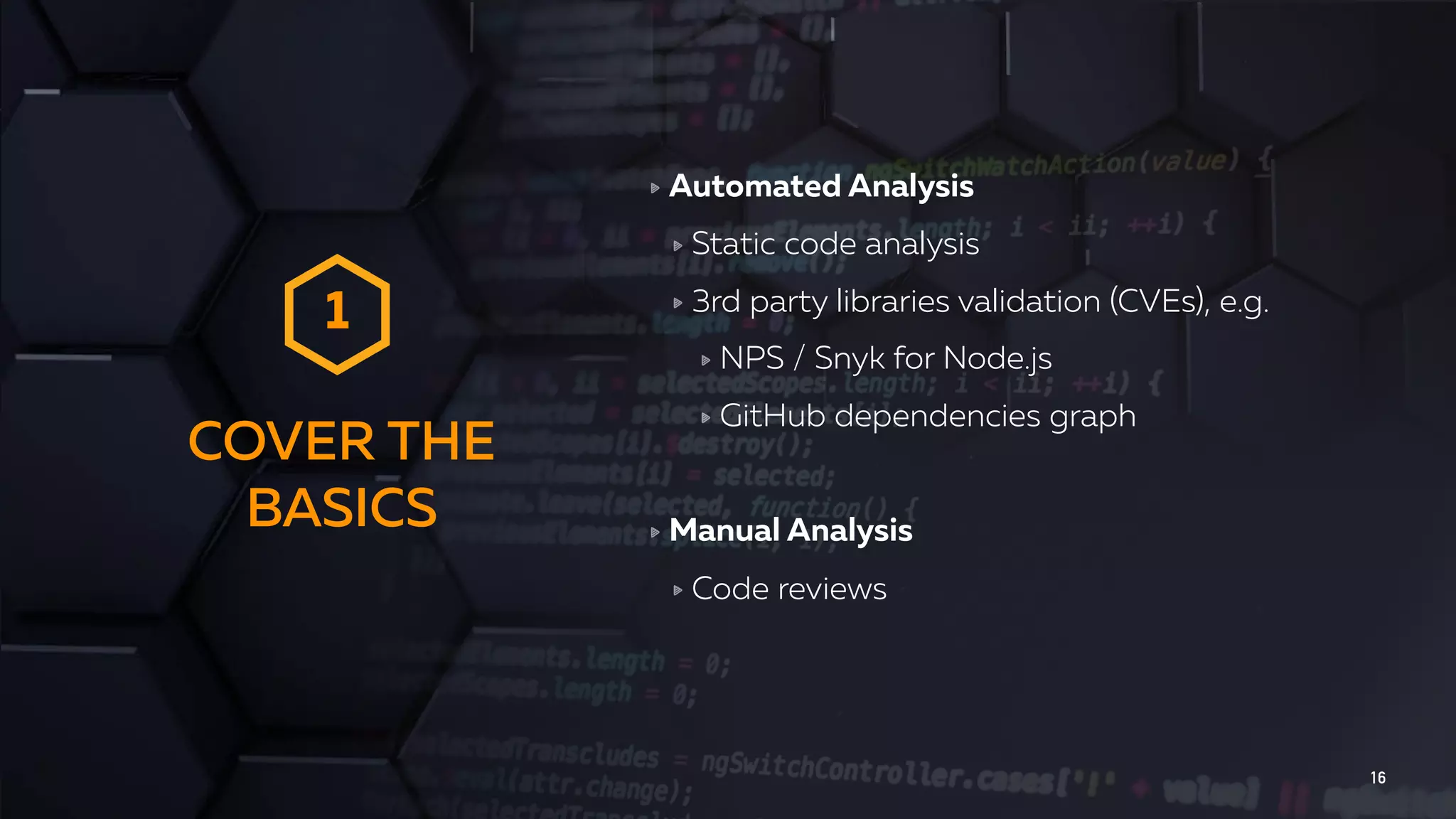
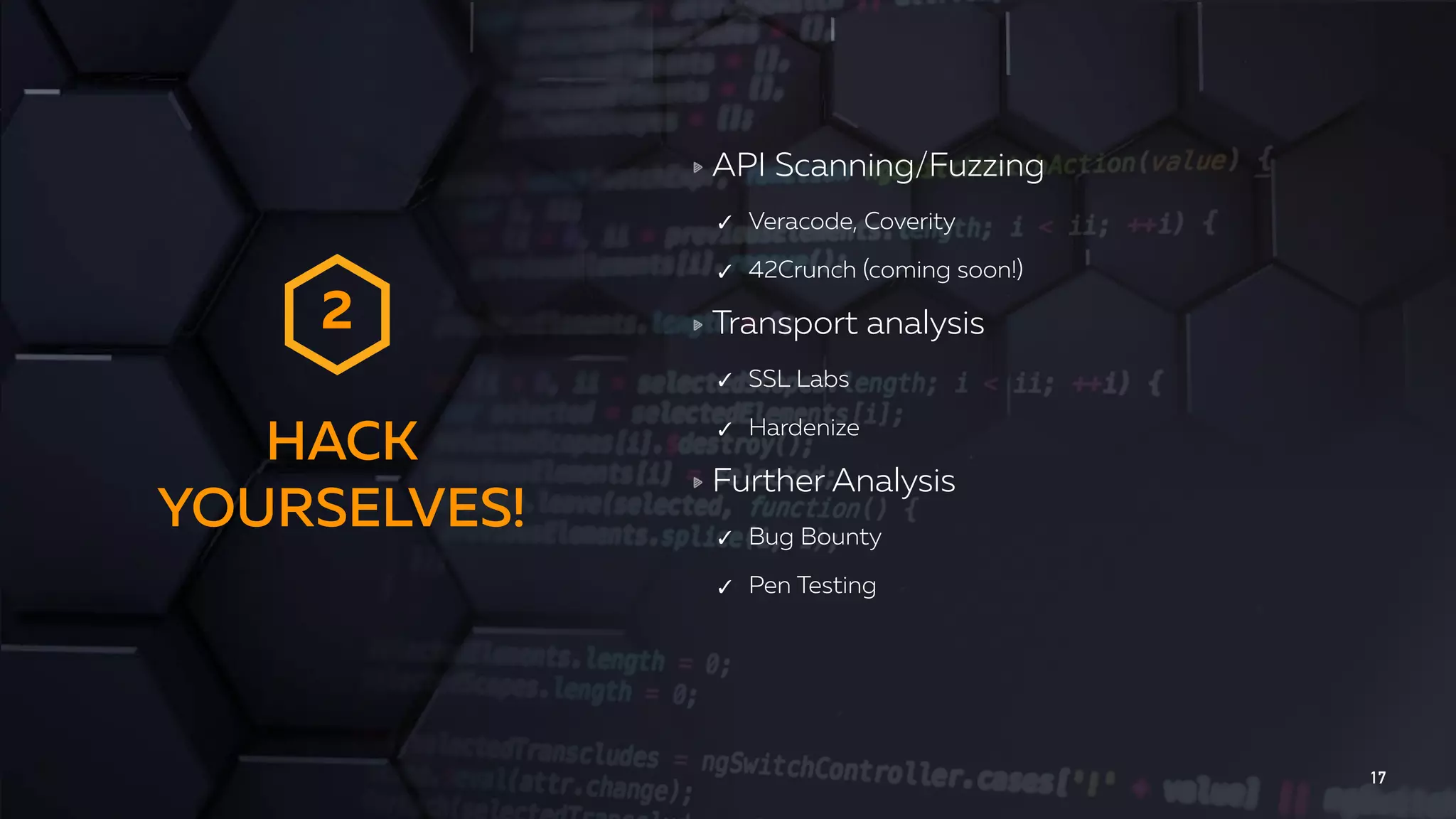
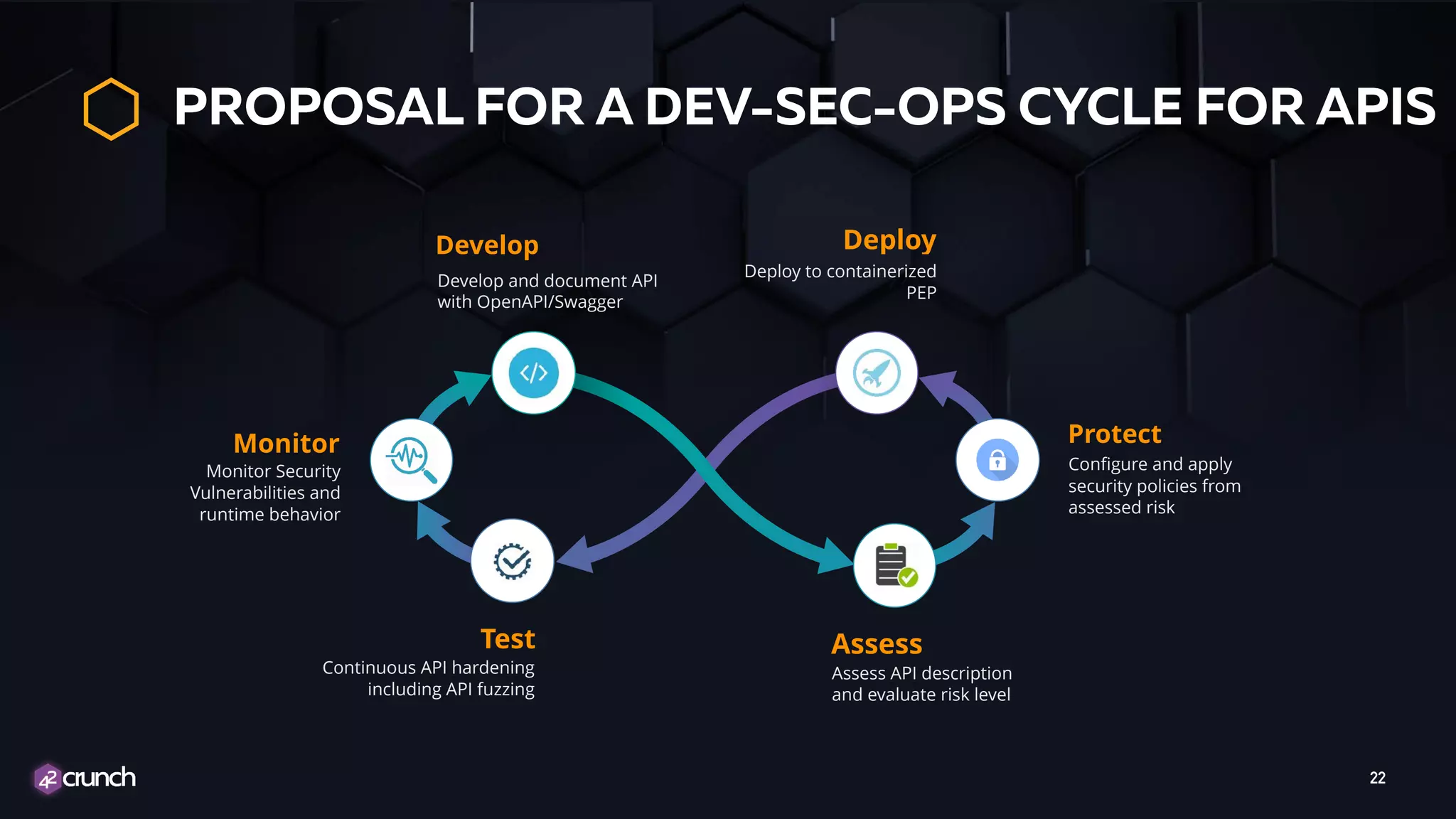
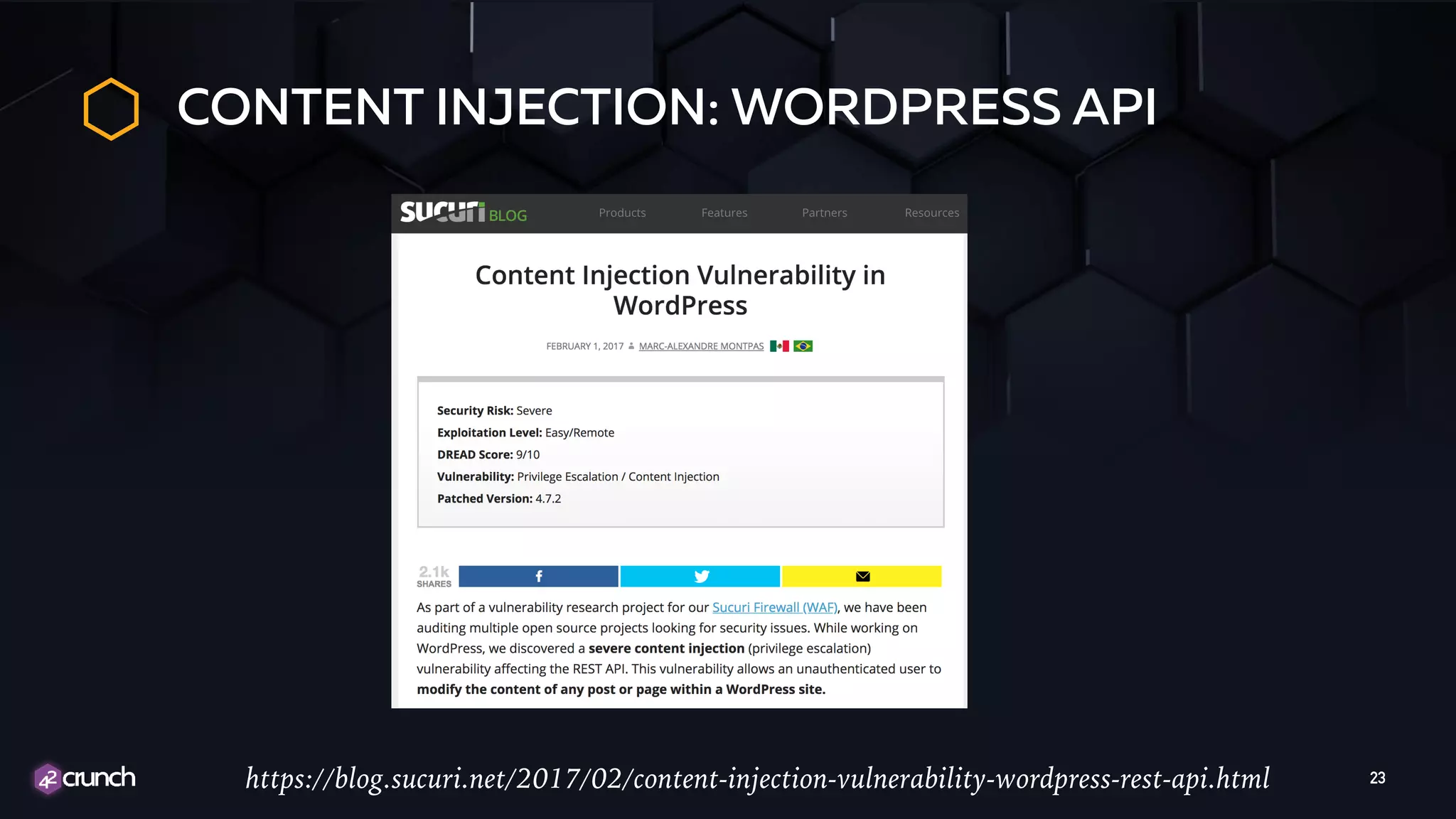
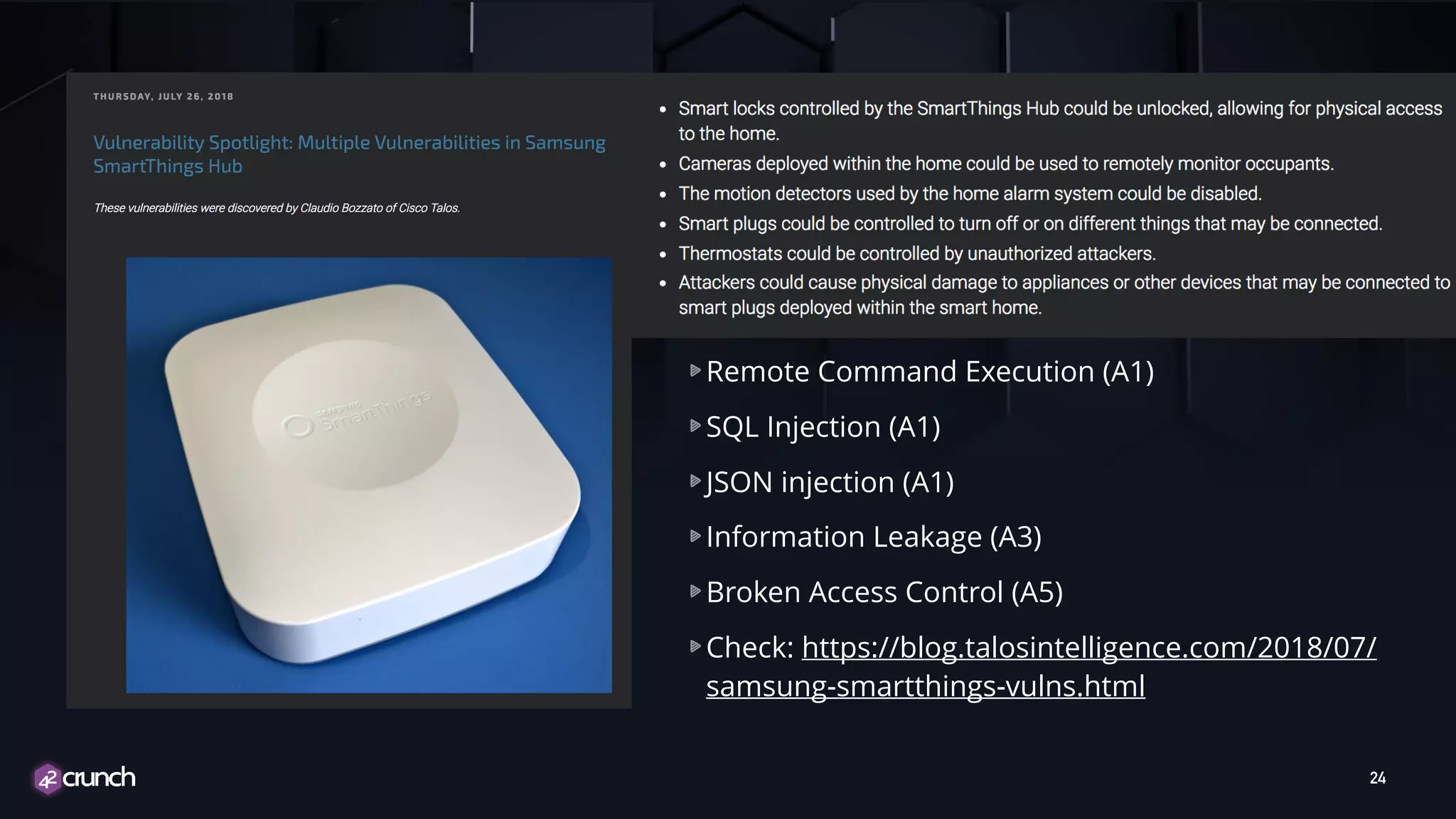
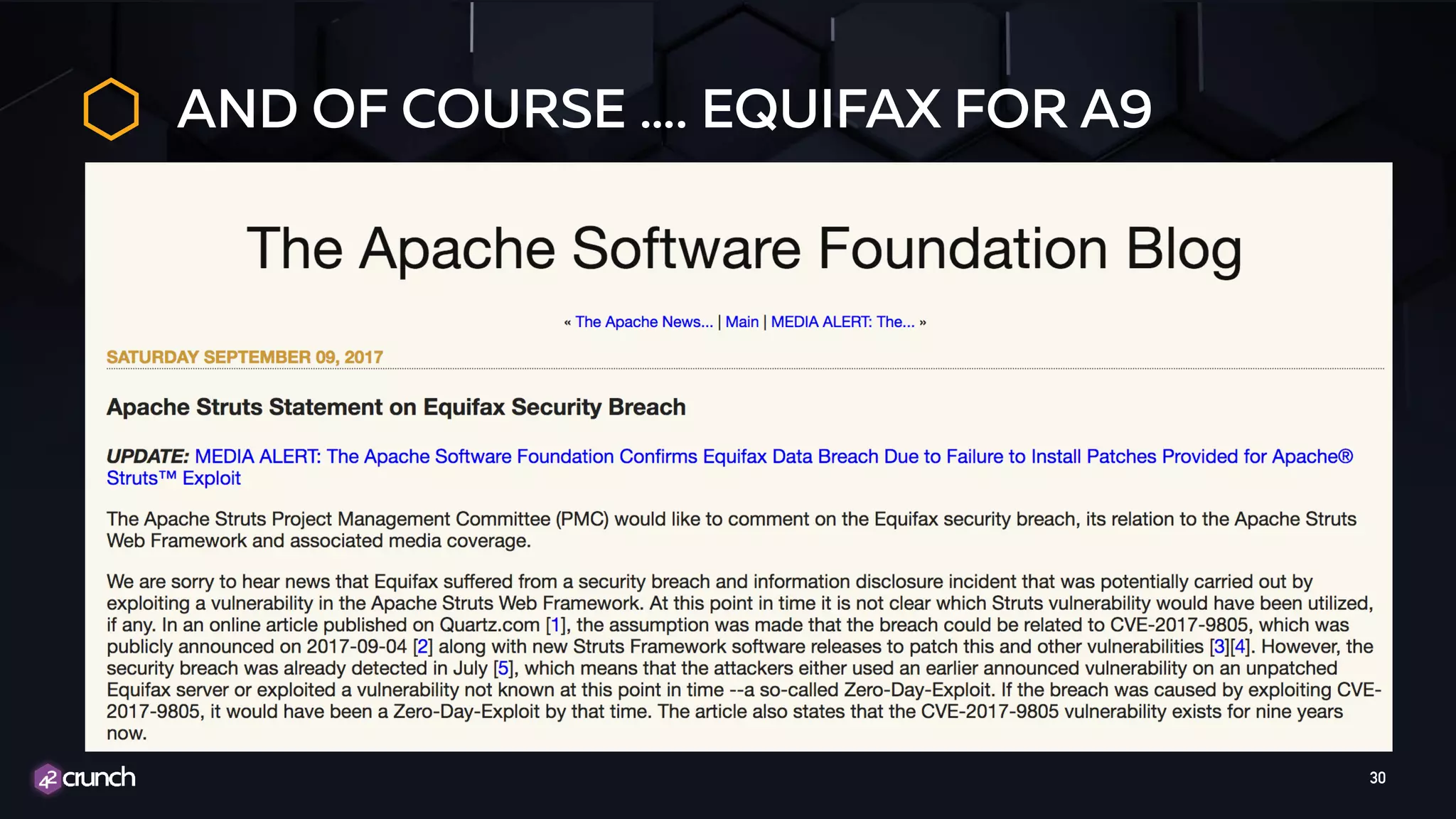
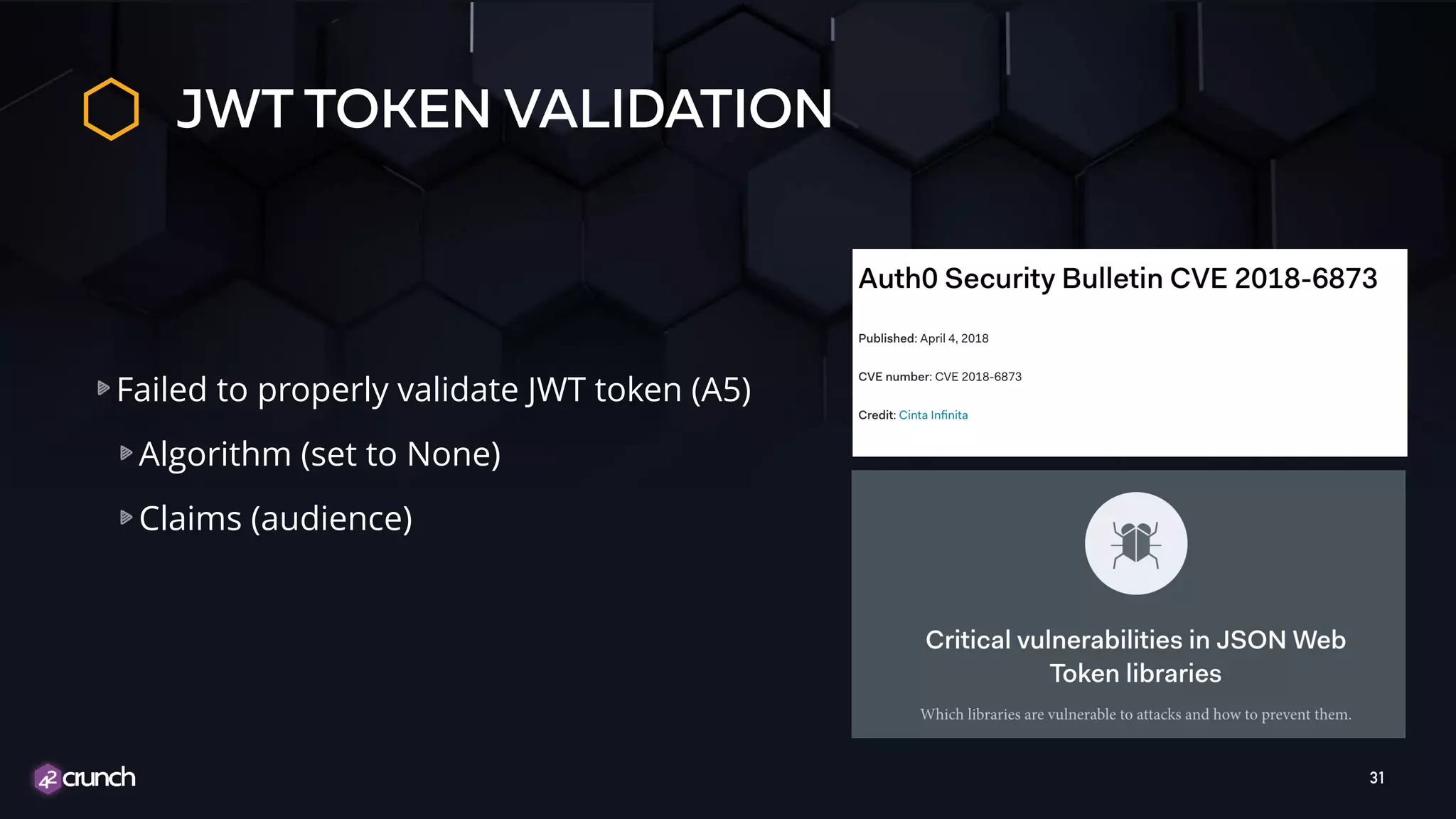
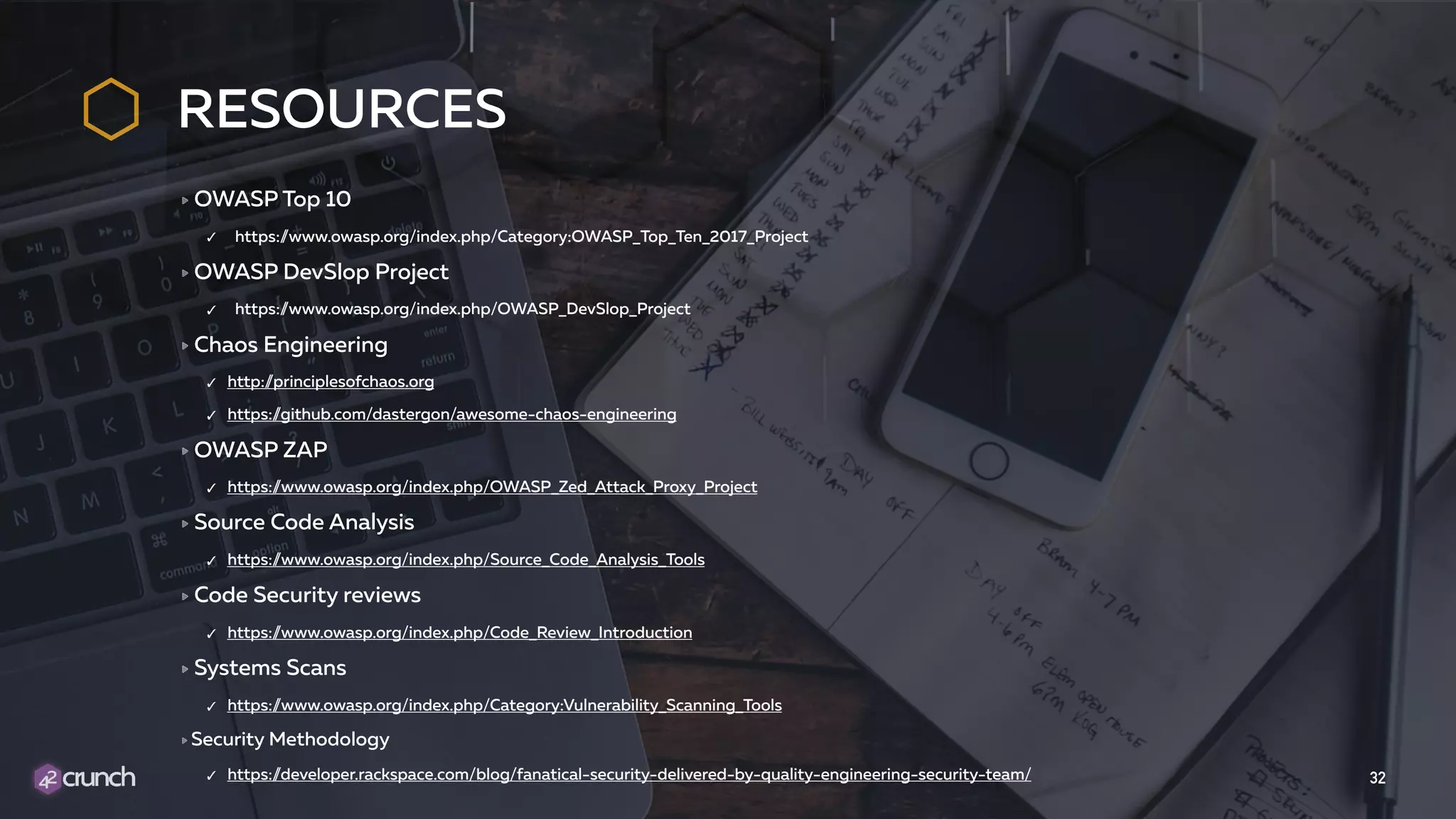
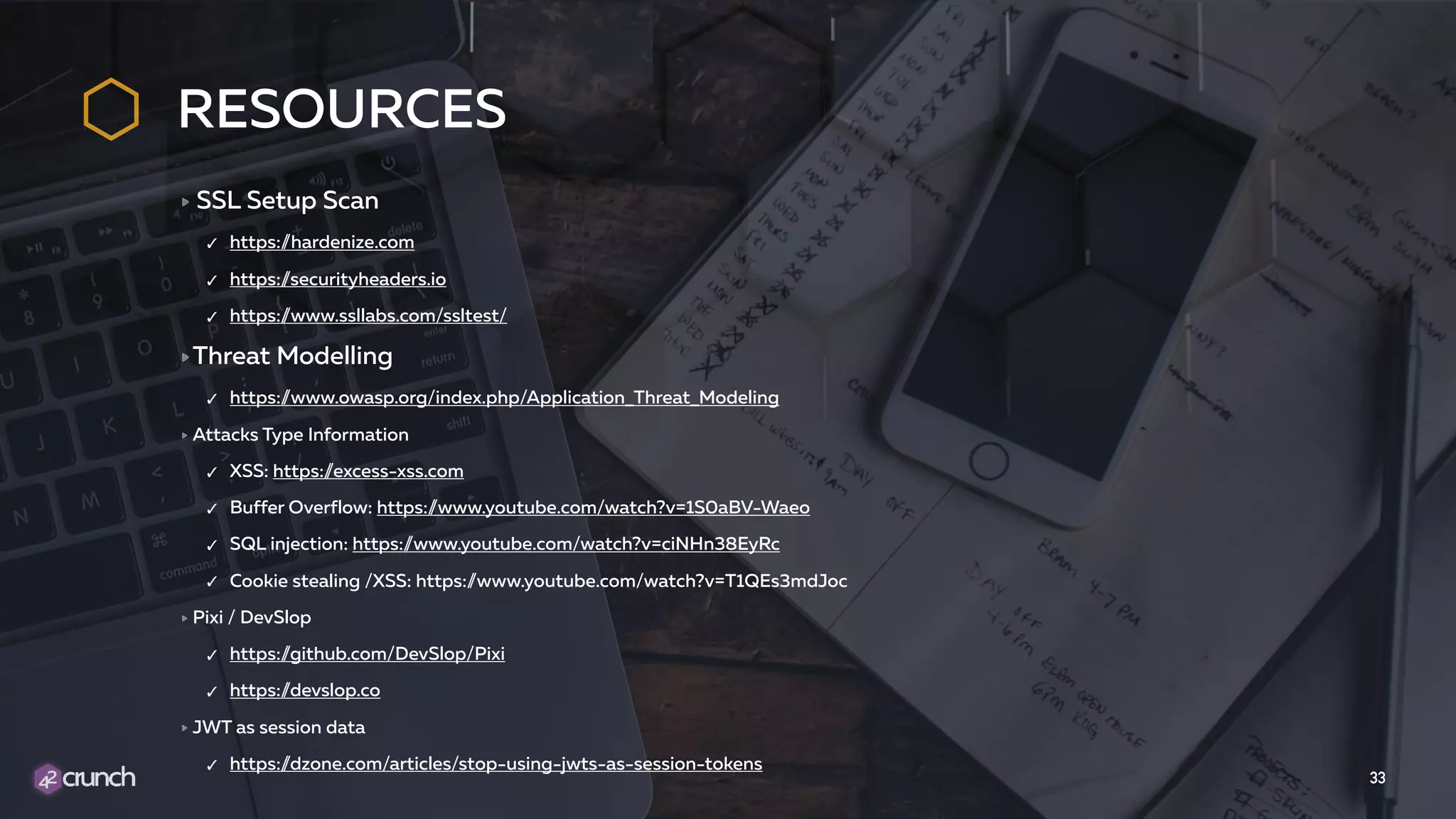
The document discusses API security, highlighting the evolution of common vulnerabilities as indicated by OWASP from 2010 to 2017, with a focus on the importance of automated security measures. It emphasizes the need for proper validation of inputs, JWT security, and protection of all APIs through various measures like rate limiting and monitoring. The document also outlines a proposal for a continuous Dev-Sec-Ops cycle to address API security concerns effectively.